Author: IT Administrator
SRWE Final Skills Exam (Equipment) Your exam may be different Topology Assessment Objectives Part 1: Initialize, Reload and Configure Basic Device Settings (45 points, 45 minutes) Part 2: Configure Network Infrastructure Settings (VLANs, Trunking, Etherchannel) (30 points, 25 minutes) Part 3: Configure Host Support (20 points, 25 minutes) …
Lab – Initialize and Reload a Router and Switch (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Topology Objectives Part 1: Set Up Devices in the Network as Shown in the Topology Part 2: Initialize the Router …
3.0.3 Class Activity – Design a Communications System (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Explain the role of protocols and standards organizations in facilitating interoperability in network communications. Background / Scenario You have just …
CyberOps Associate (Version 1.0) – CyberOps Associate 1.0 Final exam answers 1. Which two statements are characteristics of a virus? (Choose two.) A virus typically requires end-user activation. A virus can be dormant and then activate at a specific time or date. A virus replicates itself by independently …
CyberOps Associate (Version 1.0) – CyberOps Associate 1.0 Practice Final exam answers 1. What are two problems that can be caused by a large number of ARP request and reply messages? (Choose two.) All ARP request messages must be processed by all nodes on the local network. A …
CyberOps Associates v1.0 – Skills Assessment Introduction You have been hired as a junior security analyst. As part of your training, you were tasked to determine any malicious activity associated with the Pushdo trojan. You will have access to the internet to learn more about the events. You …
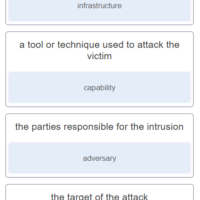
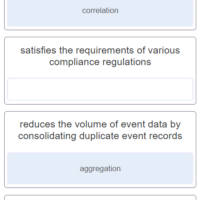
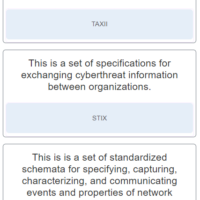
CyberOps Associate (Version 1.0) – Modules 26 – 28: Analyzing Security Data Group Exam 1. Match the intrusion event defined in the Diamond Model of intrusion to the description. network path used to establish and maintain command and control : infrastructure a tool or technique used to attack …
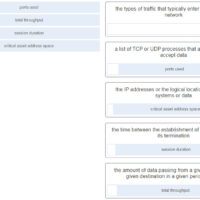
CyberOps Associate (Version 1.0) – Modules 24 – 25: Protocols and Log Files Group Exam 1. Which ICMP message type should be stopped inbound? source quench echo-reply echo unreachable 2. How can IMAP be a security threat to a company? Someone inadvertently clicks on a hidden iFrame. Encrypted …
CyberOps Associate (Version 1.0) – Modules 21 – 23: Cryptography and Endpoint Protection Group Exam 1. Which type of attack does the use of HMACs protect against? brute force DDoS DoS man-in-the-middle 2. Which objective of secure communications is achieved by encrypting data? confidentiality integrity availability authentication 3. …
CyberOps Associate (Version 1.0) – Modules 18 – 20: Network Defense Group Exam 1. Why is asset management a critical function of a growing organization against security threats? It identifies the ever increasing attack surface to threats. It allows for a build of a comprehensive AUP. It serves …