Time limit: 0
Quiz-summary
0 of 109 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
Information
Good luck For You!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 109 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- Answered
- Review
-
Question 1 of 109
1. Question
1 pointsWhich of the following are the address ranges of the private IP addresses? (Choose three.)Correct
Incorrect
-
Question 2 of 109
2. Question
1 pointsWhich two functions of the OSI model occur at layer two? (Choose two.)Correct
Incorrect
-
Question 3 of 109
3. Question
1 pointsRefer to the exhibit. What function does router RT_A need to provide to allow Internet access for hosts in this network?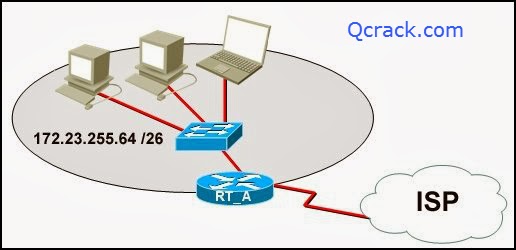 Correct
Correct
Incorrect
-
Question 4 of 109
4. Question
1 pointsWhat is true regarding network layer addressing? (Choose three.)Correct
Incorrect
-
Question 5 of 109
5. Question
1 pointsRefer to the exhibit. Host A attempts to establish a TCP/IP session with host C. During this attempt, a frame was captured with the source MAC address 0050.7320.D632 and the destination MAC address 0030.8517.44C4. The packet inside the captured frame has an IP source address 192.168.7.5, and the destination IP address is 192.168.219.24. At which point in the network was this packet captured?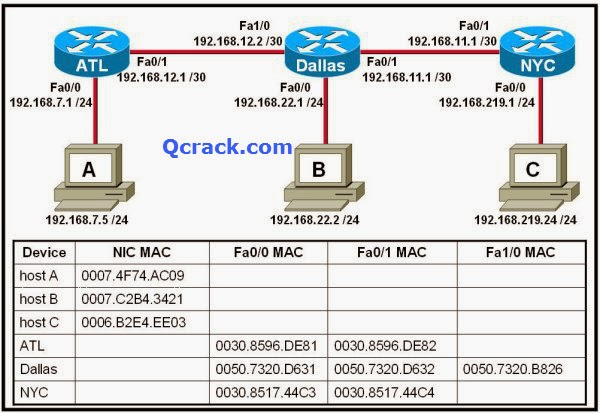 Correct
Correct
Incorrect
-
Question 6 of 109
6. Question
1 pointsRefer to the exhibit. Assume all devices are using default configurations. How many subnets are required to address the topology that is shown? Correct
Correct
Incorrect
-
Question 7 of 109
7. Question
1 pointsA technician is asked to secure the privileged EXEC mode of a switch by requiring a password. Which type of password would require this login and be considered the most secure?Correct
Incorrect
-
Question 8 of 109
8. Question
1 pointsRefer to the exhibit. A technician is working on a network problem that requires verification of the router LAN interface. What address should be pinged from this host to confirm that the router interface is operational?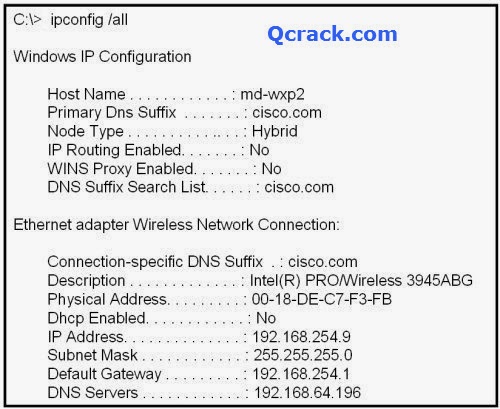 Correct
Correct
Incorrect
-
Question 9 of 109
9. Question
1 pointsWhich OSI layer does IP rely on to determine whether packets have been lost and to request retransmission?Correct
Incorrect
-
Question 10 of 109
10. Question
1 pointsWhen connectionless protocols are implemented at the lower layers of the OSI model, what is usually used to acknowledge that the data was received and to request the retransmission of missing data?Correct
Incorrect
-
Question 11 of 109
11. Question
1 pointsRefer to the exhibit. Host C is able to ping 127.0.0.1 successfully, but is unable to communicate with hosts A and B in the organization. What is the likely cause of the problem?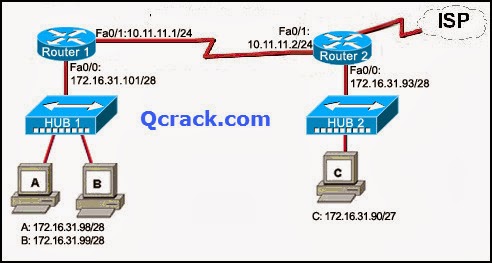 Correct
Correct
Incorrect
-
Question 12 of 109
12. Question
1 pointsRefer to the exhibit. Which list refers only to end devices?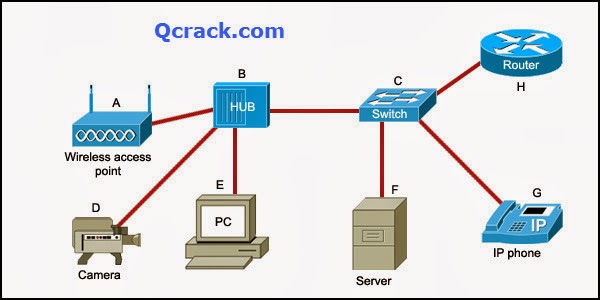 Correct
Correct
Incorrect
-
Question 13 of 109
13. Question
1 pointsRefer to the exhibit. Host A sends a frame with the destination MAC address as FFFF.FFFF.FFFF. What action will the switch take for this frame?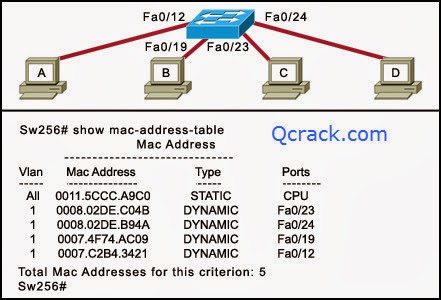 Correct
Correct
Incorrect
-
Question 14 of 109
14. Question
1 pointsWhich subnet mask will allow 2040 hosts per subnet on the IP network 10.0.0.0?Correct
Incorrect
-
Question 15 of 109
15. Question
1 pointsRefer to the exhibit. RouterB is configured properly. The Ethernet interface Fa0/0 of RouterA is configured with the use of the commands that are shown. However, a ping from the Fa0/0 interface of RouterA to the Fa0/0 interface of RouterB is unsuccessful. What action should be taken on RouterA to solve this problem?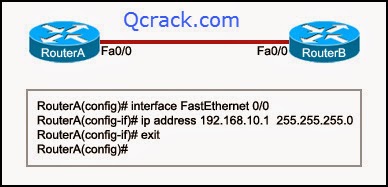 Correct
Correct
Incorrect
-
Question 16 of 109
16. Question
1 pointsTo send data through a network, what two flags are used to establish a session? (Choose two.)Correct
Incorrect
-
Question 17 of 109
17. Question
1 pointsWhich statement is true about the TTL value of an IPv4 packet?Correct
Incorrect
-
Question 18 of 109
18. Question
1 pointsRefer to the exhibit. Communication for hosts X and Y is restricted to the local network. What is the reason for this?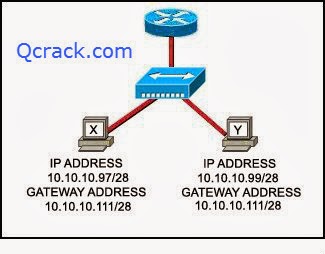 Correct
Correct
Incorrect
-
Question 19 of 109
19. Question
1 pointsWhat type of network is maintained if a server takes no dedicated role in the network?Correct
Incorrect
-
Question 20 of 109
20. Question
1 pointsA routing issue has occurred in your internetwork. Which of the following type of devices should be examined to isolate this error?Correct
Incorrect
-
Question 21 of 109
21. Question
1 pointsA user sees the command prompt: Router(config-if)# . What task can be performed at this mode?Correct
Incorrect
-
Question 22 of 109
22. Question
1 pointsWhat information can be gathered by using the command netstat?Correct
Incorrect
-
Question 23 of 109
23. Question
1 pointsHow can ARP be used to help document the network?Correct
Incorrect
-
Question 24 of 109
24. Question
1 pointsWhat is the protocol data unit that is associated with the data link layer of the OSI reference model?Correct
Incorrect
-
Question 25 of 109
25. Question
1 pointsWhich application layer protocol allows administrators to log into a server from remote locations and control a server as though logged in locally?Correct
Incorrect
-
Question 26 of 109
26. Question
1 pointsWhich statement identifies the DNS protocol?Correct
Incorrect
-
Question 27 of 109
27. Question
1 pointsWhich password would allow a user to establish a Telnet session with a Cisco device?Correct
Incorrect
-
Question 28 of 109
28. Question
1 pointsWhich identifier is contained in the header of the Layer 2 Ethernet frame?Correct
Incorrect
-
Question 29 of 109
29. Question
1 pointsWhat happens when a node on an Ethernet network is creating a frame and it does not have the destination MAC address?Correct
Incorrect
-
Question 30 of 109
30. Question
1 pointsAn administrator makes changes to the default configuration of a router and saves them to NVRAM. After testing, it is discovered that the configurations did not have the desired effect and must be removed. What steps must be taken to remove the changes and return the router to the default configuration?Correct
Incorrect
-
Question 31 of 109
31. Question
1 pointsA network administrator is tasked with connecting two workgroups that are configured to use different subnets. Which device should be selected to allow connectivity between users on the two networks?Correct
Incorrect
-
Question 32 of 109
32. Question
1 pointsWhich two programs can be used to accomplish terminal emulation for configuring a router from the CLI through the console port? (Choose two.)Correct
Incorrect
-
Question 33 of 109
33. Question
1 pointsWhich statement accurately describes file sharing in a peer-to-peer network?Correct
Incorrect
-
Question 34 of 109
34. Question
1 pointsWhat are two primary responsibilities of the Ethernet MAC sublayer? (Choose two.)Correct
Incorrect
-
Question 35 of 109
35. Question
1 pointsWhich router configuration mode would an administrator use to configure the router for SSH or Telnet login access?Correct
Incorrect
-
Question 36 of 109
36. Question
1 pointsRefer to the exhibit. Which device should be included in the network topology to provide Layer 2 connectivity for all LAN devices, provide multiple collision domains, and also provide a connection to the rest of the network?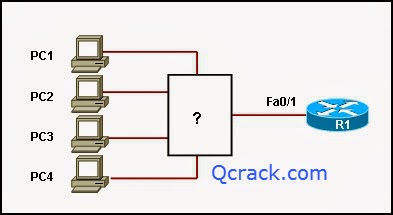 Correct
Correct
Incorrect
-
Question 37 of 109
37. Question
1 pointsWhat purpose does a hostname serve on a router?Correct
Incorrect
-
Question 38 of 109
38. Question
1 pointsWhich prompt is associated with the privileged exec mode?Correct
Incorrect
-
Question 39 of 109
39. Question
1 pointsA technician wishes to connect two computers to move data from one to the other before reloading the operating system. The NICs on both PCs do not support autosensing feature. Which procedure will satisfy the requirement?Correct
Incorrect
-
Question 40 of 109
40. Question
1 pointsRefer to the exhibit. Interface Fa0/0 on router A is generating excessive broadcast traffic. Which LAN segments will affected by the excessive broadcasts?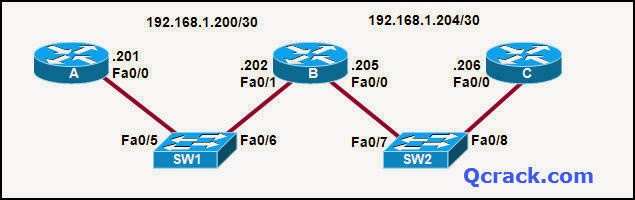 Correct
Correct
Incorrect
-
Question 41 of 109
41. Question
1 pointsTwo routers are connected via their serial ports in a lab environment. The routers are configured with valid IP addresses, but they cannot ping each other. The show interface serial0/0 command shows that the serial0/0 interface is up but the line protocol is down. What could be the cause of this problem?Correct
Incorrect
-
Question 42 of 109
42. Question
1 pointsRefer to the exhibit. Which layered network model is shown in the diagram?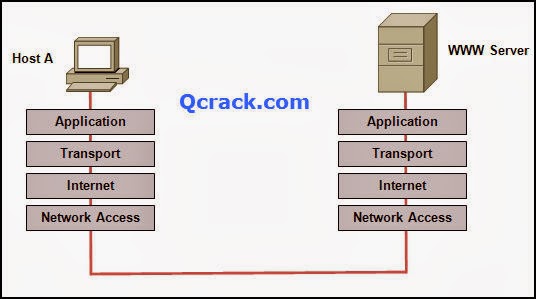 Correct
Correct
Incorrect
-
Question 43 of 109
43. Question
1 pointsRefer to the exhibit. Host A is unable to reach host B on the remote network. A technician attempted to ping the local gateway and the ping was successful. To verify the host configuration, the technician issued the ipconfig command. What is the likely cause of the problem?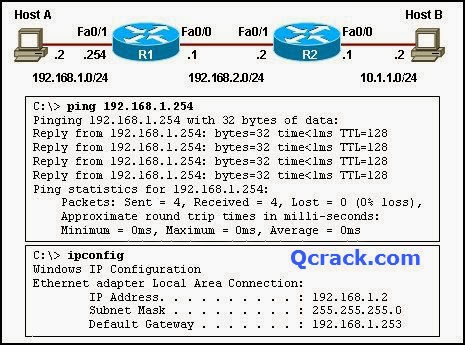 Correct
Correct
Incorrect
-
Question 44 of 109
44. Question
1 pointsAn organization has been assigned network ID 10.10.128.0 and subnet mask 255.255.224.0. Which IP address range can be used for this organization?Correct
Incorrect
-
Question 45 of 109
45. Question
1 pointsWhen must a router serial interface be configured with the clock rate command?Correct
Incorrect
-
Question 46 of 109
46. Question
1 pointsDue to a security violation, the router passwords must be changed. What information can be learned from the following configuration entries? (Choose two.)Correct
Incorrect
-
Question 47 of 109
47. Question
1 pointsWhich password is automatically encrypted when it is created?Correct
Incorrect
-
Question 48 of 109
48. Question
1 pointsWhich prompt represents the appropriate mode used for the copy running-config startup-config command ?Correct
Incorrect
-
Question 49 of 109
49. Question
1 pointsWhich information is used by the router to determine the path between the source and destination hosts?Correct
Incorrect
-
Question 50 of 109
50. Question
1 pointsWell-known services and applications use which range of TCP/UDP port numbers?Correct
Incorrect
-
Question 51 of 109
51. Question
1 pointsWhich three IPv4 addresses represent subnet broadcast addresses? (Choose three.)Correct
Incorrect
-
Question 52 of 109
52. Question
1 pointsWhich three statements are true about network layer addressing? (Choose three.)Correct
Incorrect
-
Question 53 of 109
53. Question
1 pointsWhich OSI layer addressing is required to route packets between two networks?Correct
Incorrect
-
Question 54 of 109
54. Question
1 pointsHow many host addresses may be assigned when using the 128.107.0.0 network address with a subnet mask of 255.255.248.0?Correct
Incorrect
-
Question 55 of 109
55. Question
1 pointsDuring the encapsulation process, what is the PDU of the internet layer?Correct
Incorrect
-
Question 56 of 109
56. Question
1 pointsWhich service is used when the nslookup command is issued on a computer?Correct
Incorrect
-
Question 57 of 109
57. Question
1 pointsWhat are the default terminal emulation software settings when configuring a Cisco device through a console port?Correct
Incorrect
-
Question 58 of 109
58. Question
1 pointsIn a packet-switched data network, what is used to reassemble the packets in the correct order at the destination device?Correct
Incorrect
-
Question 59 of 109
59. Question
1 pointsWhich router configuration mode will require user authentication if an administrator issues the enable secret command?Correct
Incorrect
-
Question 60 of 109
60. Question
1 pointsWhich location of router memory is cleared with the erase startup-config command?Correct
Incorrect
-
Question 61 of 109
61. Question
1 pointsWhich subnet mask should be used for a Class B network that is divided into subnets and will accommodate between 800 hosts and 1000 hosts?Correct
Incorrect
-
Question 62 of 109
62. Question
1 pointsWhich prompt is associated with the privileged exec mode?Correct
Incorrect
-
Question 63 of 109
63. Question
1 pointsWhat is the effect of using the Router# copy running-config startup-config command on a router?Correct
Incorrect
-
Question 64 of 109
64. Question
1 pointsIn a network design project, a network designer needs to select a device to provide collision free connections to 40 hosts on the LAN. Which device should be selected?Correct
Incorrect
-
Question 65 of 109
65. Question
1 pointsWhich communication tool allows real-time collaboration?Correct
Incorrect
-
Question 66 of 109
66. Question
1 pointsWhich range of port numbers are reserved for services that are commonly used by applications that run on servers?Correct
Incorrect
-
Question 67 of 109
67. Question
1 pointsWhich OSI layer manages data segments?Correct
Incorrect
-
Question 68 of 109
68. Question
1 pointsWhich two types of media can provide bandwidth up to 1 Gb/s? (Choose two.)Correct
Incorrect
-
Question 69 of 109
69. Question
1 pointsTo enhance security in a network, the network administrator uses these commands:- Router(config)# (line console 0) Router(config-line)# (password j1mdi2) Router(config-line)# (login)
Correct
Incorrect
-
Question 70 of 109
70. Question
1 pointsWhat two conclusions are evident from these commands? (Choose two.)Correct
Incorrect
-
Question 71 of 109
71. Question
1 pointsA user enters http://www.cisco.com/web1.htm in the address line of a browser. Which statement is true about this transaction?Correct
Incorrect
-
Question 72 of 109
72. Question
1 pointsWhat can the user do from the command prompt, Router(config-line)# ?Correct
Incorrect
-
Question 73 of 109
73. Question
1 pointsA technician is setting up a workgroup for six users and wants to allow users to share files without setting up a server. Which application layer protocol will provide for peer-to-peer file sharing in a workgroup?Correct
Incorrect
-
Question 74 of 109
74. Question
1 pointsWhich router component will have contents erased when the command erase startup-config is issued?Correct
Incorrect
-
Question 75 of 109
75. Question
1 pointsWhat is described by the network access layer of the TCP/IP model?Correct
Incorrect
-
Question 76 of 109
76. Question
1 pointsWhich two factors contribute to the increased throughput when all nodes of a LAN are connected to a switch instead of a hub? (Choose two.)Correct
Incorrect
-
Question 77 of 109
77. Question
1 pointsA network technician has made a UTP cable that is terminated as T568A on one end and T568B on the opposite end. What type of cable has been constructed?Correct
Incorrect
-
Question 78 of 109
78. Question
1 pointsWhich application belongs to the category of the client/server model?Correct
Incorrect
-
Question 79 of 109
79. Question
1 pointsWhat command can be used to troubleshoot domain name resolution issues?Correct
Incorrect
-
Question 80 of 109
80. Question
1 pointsWhich three addresses belong to the category of public IP addresses? (Choose three.)Correct
Incorrect
-
Question 81 of 109
81. Question
1 pointsWhat is the effect of the command copy running-config tftp?Correct
Incorrect
-
Question 82 of 109
82. Question
1 pointsRefer to the exhibit. A network technician wants to connect host A to the console of a Cisco switch to initialize the configuration. What type of cable is required for this connection?Correct
Incorrect
-
Question 83 of 109
83. Question
1 pointsRefer to the exhibit. The network administrator for a small advertising company has chosen to use the 192.168.5.96/27 network for internal LAN addressing. As shown in the exhibit, a static IP address is assigned to the company web server. However, the web server cannot access the Internet. The administrator verifies that local workstations with IP addresses that are assigned by a DHCP server can access the Internet, and the web server is able to ping local workstations. Which component is incorrectly configured?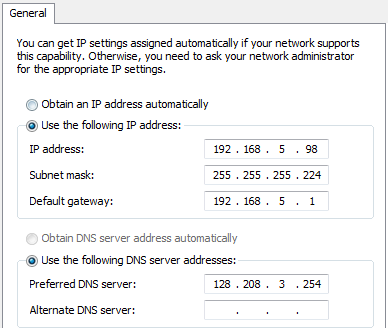 Correct
Correct
Incorrect
-
Question 84 of 109
84. Question
1 pointsA technician makes several changes to the running configuration on a router, but the desired results are not achieved. The technician issues the reload command. What action will be taken by the router?Correct
Incorrect
-
Question 85 of 109
85. Question
1 pointsRefer to the exhibit. Each media link is labeled. What type of cable should be used to connect the different devices?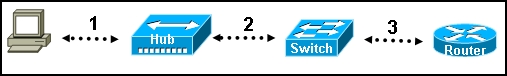 Correct
Correct
Incorrect
-
Question 86 of 109
86. Question
1 pointsWhich scenario describes a typical peer-to-peer network environment?Correct
Incorrect
-
Question 87 of 109
87. Question
1 pointsWhat type of cable is being used if a network administrator is connecting two Cisco routers and uses the 100BaseTX standard?Correct
Incorrect
-
Question 88 of 109
88. Question
1 pointsA PC can not connect to any remote websites, ping its default gateway, or ping a printer that is functioning properly on the local network segment. Which action will verify that the TCP/IP stack is functioning correctly on this PC?Correct
Incorrect
-
Question 89 of 109
89. Question
1 pointsWhat are two purposes for configuring a banner on a router? (Choose two.)Correct
Incorrect
-
Question 90 of 109
90. Question
1 pointsAn administrator needs management access to a switch from a remote offsite location. Which three configurations are required on the switch to allow the administrator to have remote access using either SSH or Telnet? (Choose three.)Correct
Incorrect
-
Question 91 of 109
91. Question
1 pointsWhich three commands will change the current configuration mode of a router? (Choose three.)Correct
Incorrect
-
Question 92 of 109
92. Question
1 pointsWhich device should be used for enabling a host to communicate with another host on a different network?Correct
Incorrect
-
Question 93 of 109
93. Question
1 pointsDuring the encapsulation process, what identifiers are added at the transport layer?Correct
Incorrect
-
Question 94 of 109
94. Question
1 pointsWhat action is taken by a host on an Ethernet network when the host attempts to contact a remote host on another network?Correct
Incorrect
-
Question 95 of 109
95. Question
1 pointsWhich three addresses are private IP addresses? (Choose three.)Correct
Incorrect
-
Question 96 of 109
96. Question
1 pointsA network administrator needs to provide administrative access for certain users. Which mode will allow users access to both the show and debug commands?Correct
Incorrect
-
Question 97 of 109
97. Question
1 pointsA network has grown too large for technicians to configure network addresses and hosts files for name resolution. Which two application layer services should be added to the server to allow these needs to be satisfied dynamically? (Choose two.)Correct
Incorrect
-
Question 98 of 109
98. Question
1 pointsWhich statement is true about Layer 3 addresses?Correct
Incorrect
-
Question 99 of 109
99. Question
1 pointsA network technician wants to configure an IP address on a router interface by using the ip address 192.168.1.1 255.255.255.0 command. Which prompt should the technician see when entering this command?Correct
Incorrect
-
Question 100 of 109
100. Question
1 pointsUDP is the transport layer protocol for which application?Correct
Incorrect
-
Question 101 of 109
101. Question
1 pointsWhat is the Cisco IOS?Correct
Incorrect
-
Question 102 of 109
102. Question
1 pointsRefer to the exhibit. What is the total amount of RAM on the router?Correct
Incorrect
-
Question 103 of 109
103. Question
1 pointsWhich physical component is used to access and perform the initial configuration on a new unconfigured router?Correct
Incorrect
-
Question 104 of 109
104. Question
1 pointsWhich option shows how a router will route packets to a remote network?Correct
Incorrect
-
Question 105 of 109
105. Question
1 pointsRefer to the exhibit. A network technician is trying to determine the correct IP address configuration for Host A. What is a valid configuration for Host A?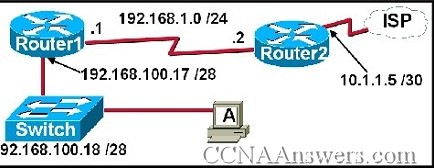 Correct
Correct
Incorrect
-
Question 106 of 109
106. Question
1 pointsRefer to the exhibit. A PC is communicating with another PC on a remote network. The two networks are connected by three routers. Which action will help to identify the path between the hosts? Correct
Correct
Incorrect
-
Question 107 of 109
107. Question
1 pointsRefer to the exhibit. Host A and B are unable to communicate with each other. What is the reason for this?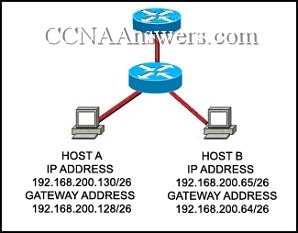 Correct
Correct
Incorrect
-
Question 108 of 109
108. Question
1 pointsRefer to the exhibit. While configuring a network, a technician wired each end of a Category 5e cable as shown. Which two statements are true about this setup? (Choose two.)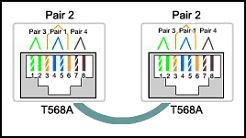 Correct
Correct
Incorrect
-
Question 109 of 109
109. Question
1 pointsRefer to the exhibit. Host A is configured with the correct IP address for the default gateway of the router R1 FastEthernet0/1 interface. How will a packet that is sent from host A to host B be handled by the devices on the network?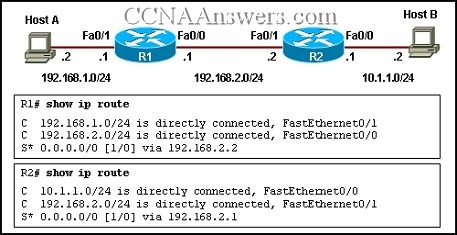 Correct
Correct
Incorrect
