Time limit: 0
Quiz-summary
0 of 100 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
Information
Good luck for you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 100 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- Answered
- Review
-
Question 1 of 100
1. Question
1 pointsRefer to the exhibit. Router RA receives a packet with a source address of 192.168.1.65 and a destination address of 192.168.1.161. What will the router do with this packet?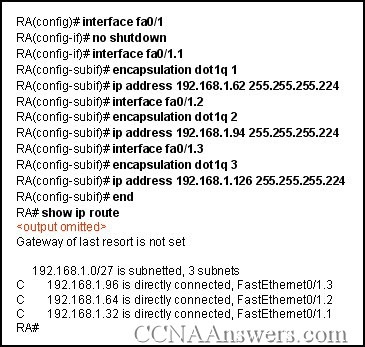 Correct
Correct
Incorrect
-
Question 2 of 100
2. Question
1 pointsWhich value determines if a switch becomes the central point of reference in the spanning tree topology?Correct
Incorrect
-
Question 3 of 100
3. Question
1 pointsAn administrator is troubleshooting a PC on the network which is suffering from slow and intermittent connectivity. The PC has a ping success rate to the default gateway of less than half the ping attempts. Other PCs on the switch can consistently ping the default gateway. The switch port is configured for auto duplex and the PC is configured for full duplex. What will commonly cause this problem?Correct
Incorrect
-
Question 4 of 100
4. Question
1 pointsWhat is the purpose of the switch command switchport access vlan 99?Correct
Incorrect
-
Question 5 of 100
5. Question
1 pointsWhat three tasks should be performed before moving a Catalyst switch to another VTP management domain? (Choose three.)Correct
Incorrect
-
Question 6 of 100
6. Question
1 pointsWhich method establishes an administrative connection for configuring the Linksys WRT300N wireless access point?Correct
Incorrect
-
Question 7 of 100
7. Question
1 pointsHow does a switch that is configured for 802.1Q trunking handle untagged frames that are received on a trunk port?Correct
Incorrect
-
Question 8 of 100
8. Question
1 pointsIn which mode is a VTP switch operating if it has been configured to only forward VTP advertisements?Correct
Incorrect
-
Question 9 of 100
9. Question
1 pointsWhy is it important that the network administrator consider the spanning-tree network diameter when choosing the root bridge?Correct
Incorrect
-
Question 10 of 100
10. Question
1 pointsWhich feature is uniquely found in an access layer switch within a hierarchical network model?Correct
Incorrect
-
Question 11 of 100
11. Question
1 pointsWhile configuring a new switch, a network administrator configures the switch as an HTTP server. What benefits does this configuration provide?Correct
Incorrect
-
Question 12 of 100
12. Question
1 pointsUsing the command copy tftp:backup.cfg startup-config, an administrator downloaded a saved configuration from a TFTP server to a switch. Why does the administrator not detect any changes in the switch configuration after the download completes?Correct
Incorrect
-
Question 13 of 100
13. Question
1 pointsWhy is it advisable that a network administrator use SSH instead of Telnet when managing switches?Correct
Incorrect
-
Question 14 of 100
14. Question
1 pointsRefer to the exhibit. A network has already been configured with VTP, using DLS1 as the VTP server for the VTP domain Cisco. What will happen when the DLS2 switch is connected to the DLS1 switch via a trunk link?Correct
Incorrect
-
Question 15 of 100
15. Question
1 pointsWhat information in an Ethernet frame is used by a Layer 2 switch to build its address table?Correct
Incorrect
-
Question 16 of 100
16. Question
1 pointsA wireless LAN access point will convert traffic between which two frame encapsulation types?Correct
Incorrect
-
Question 17 of 100
17. Question
1 pointsA network administrator is asked to connect four switches that are each configured with eight VLANs. Routers that have two FastEthernet ports each that support trunking are available. What is the minimum number of routers needed to interconnect traffic from all of the VLANs if trunking is allowed?Correct
Incorrect
-
Question 18 of 100
18. Question
1 pointsWhat are two characteristics of normal range VLANs? (Choose two.)Correct
Incorrect
-
Question 19 of 100
19. Question
1 pointsWhat is the benefit of the auto-MDIX feature on a Cisco Catalyst switch?Correct
Incorrect
-
Question 20 of 100
20. Question
1 pointsWhat benefit does 802.1x provide to a wireless network?Correct
Incorrect
-
Question 21 of 100
21. Question
1 pointsWhich configuration changes will increment the configuration revision number on the VTP server?Correct
Incorrect
-
Question 22 of 100
22. Question
1 pointsA wireless client is attempting to establish a connection with a wireless access point. What process does the client use to discover the access points which are available to it?Correct
Incorrect
-
Question 23 of 100
23. Question
1 pointsRefer to the exhibit. Each switch is shown with its MAC address. Which switch will be elected as the spanning-tree root bridge if the switches are configured with their default priority values?Correct
Incorrect
-
Question 24 of 100
24. Question
1 pointsWhat is a function or characteristic of the native VLAN?Correct
Incorrect
-
Question 25 of 100
25. Question
1 pointsA network administrator must purchase new access layer switches to deploy across an existing hierarchical network that supports voice and data traffic. At a minimum, which two features should the new access layer switches support? (Choose two.)Correct
Incorrect
-
Question 26 of 100
26. Question
1 pointsWhich combination is required to establish a connection to initially configure the Linksys WRT300N wireless access device?Correct
Incorrect
-
Question 27 of 100
27. Question
1 pointsRefer to the exhibit. SW-T has been configured with a single trunking interface. Which VLANs will be allowed across the trunk?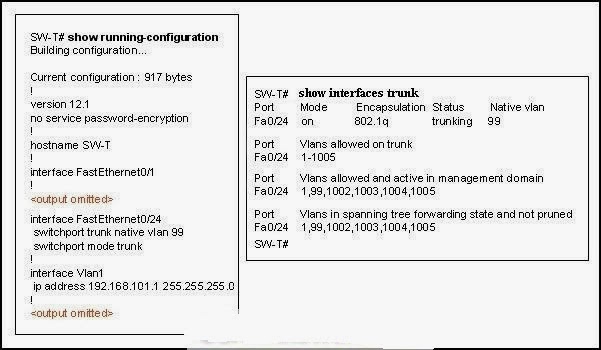 Correct
Correct
Incorrect
-
Question 28 of 100
28. Question
1 pointsRefer to the exhibit. Hosts B and C attempt to transmit a frame at the same time, but a collision occurs. Which hosts will receive the collision jamming signal?Correct
Incorrect
-
Question 29 of 100
29. Question
1 pointsRefer to the exhibit. The switch VTY lines have been properly configured, but PC1 is unable to remotely manage the switch. How can this problem be resolved?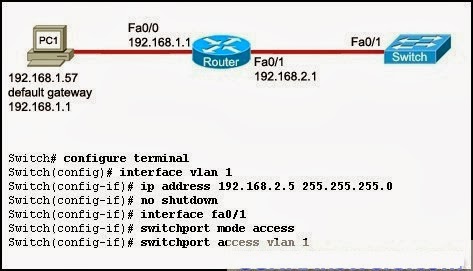 Correct
Correct
Incorrect
-
Question 30 of 100
30. Question
1 pointsRefer to the exhibit. The network administrator is planning five additional VLANs to be shared throughout the VTP domain on S3. What action should the administrator take before creating the additional VLANs?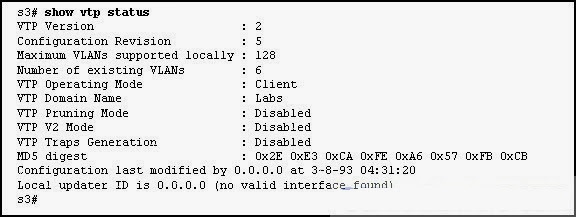 Correct
Correct
Incorrect
-
Question 31 of 100
31. Question
1 pointsWhich switching method provides error-free data transmission?Correct
Incorrect
-
Question 32 of 100
32. Question
1 pointsWhich wireless topology supports roaming from one access point to another?Correct
Incorrect
-
Question 33 of 100
33. Question
1 pointsA wireless access point is configured for WPA2. Which encryption algorithm will all devices that connect to the access point be required to use?Correct
Incorrect
-
Question 34 of 100
34. Question
1 pointsWhere is the information of newly created VLANs stored on a switch?Correct
Incorrect
-
Question 35 of 100
35. Question
1 pointsRefer to the exhibit. The configuration steps that are listed in the exhibit have been entered in switch S1 via the console. Subsequent attempts to telnet to the switch are not successful. What is causing the problem?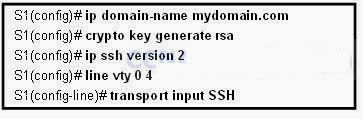 Correct
Correct
Incorrect
-
Question 36 of 100
36. Question
1 pointsWhat is one disadvantage that 802.11a wireless has compared to 802.11g?Correct
Incorrect
-
Question 37 of 100
37. Question
1 pointsWhy is MAC address filtering considered a poor choice in securing a WLAN?Correct
Incorrect
-
Question 38 of 100
38. Question
1 pointsWhat is the purpose of the Spanning Tree algorithm?Correct
Incorrect
-
Question 39 of 100
39. Question
1 pointsWhat are two benefits of a hierarchical network model over a flat network design? (Choose two.)Correct
Incorrect
-
Question 40 of 100
40. Question
1 pointsWhat is the purpose of VLAN trunking?Correct
Incorrect
-
Question 41 of 100
41. Question
1 pointsWhich two statements describe the operation of an access layer Ethernet switch? (Choose two.)Correct
Incorrect
-
Question 42 of 100
42. Question
1 pointsWhich two types of traffic are always transmitted as untagged frames? (Choose two.)Correct
Incorrect
-
Question 43 of 100
43. Question
1 pointsWhich statement correctly describes a function of a Layer 2 switch?Correct
Incorrect
-
Question 44 of 100
44. Question
1 pointsRefer to the exhibit. The Layer 2 switching design that is shown has been implemented in a campus environment that is using Spanning Tree Protocol. All inter-switch links that are shown are trunks. Whenever an inter-switch link fails, the network takes nearly a minute to completely converge. How can the convergence time be reduced?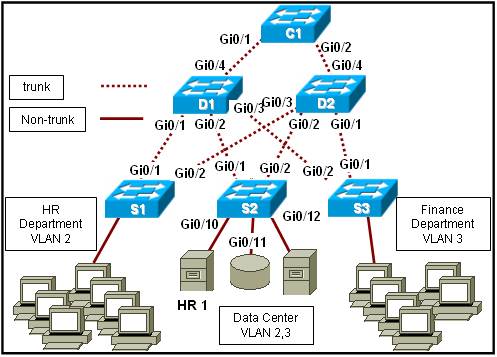 Correct
Correct
Incorrect
-
Question 45 of 100
45. Question
1 pointsRefer to the exhibit. Which two statements are true about the operation of the interfaces? (Choose two.)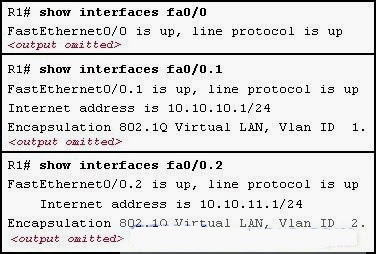 Correct
Correct
Incorrect
-
Question 46 of 100
46. Question
1 pointsRefer to the exhibit. The teacher host is connected to port Fa0/7 on switch STW. A student has decided to share access to the Internet by attaching a hub and laptop to STW as shown. What will be the result of the student making this connection?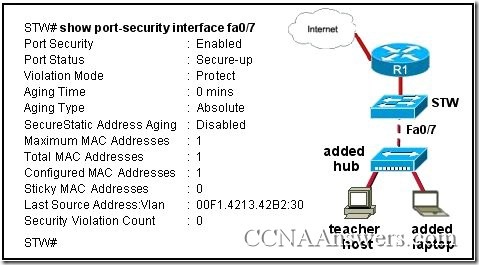 Correct
Correct
Incorrect
-
Question 47 of 100
47. Question
1 pointsA network administrator configures a switch port with the command switchport mode dynamic auto. What is the resulting behavior of the switch port?Correct
Incorrect
-
Question 48 of 100
48. Question
1 pointsWhich STP port type can only appear once on a segment, and must be present in order for traffic to flow on that segment?Correct
Incorrect
-
Question 49 of 100
49. Question
1 pointsRefer to the exhibit. VLAN 10 has been configured on the VTP server. Users who are assigned to VLAN 10 are connected as shown in the exhibit. On the basis of the outputs that are provided, which group of users will be able to communicate with the users on VLAN 10 on SW1?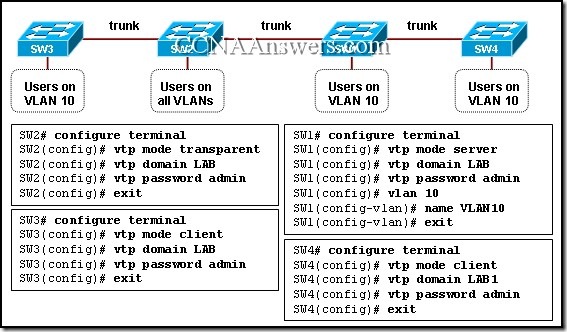 Correct
Correct
Incorrect
-
Question 50 of 100
50. Question
1 pointsRefer to the exhibit. Switches S2 and S3 are properly connected using an ethernet cable. A network administrator has configured both switches with VTP, but S3 is unable to propagate VLANs to S2. What could be the reason for this?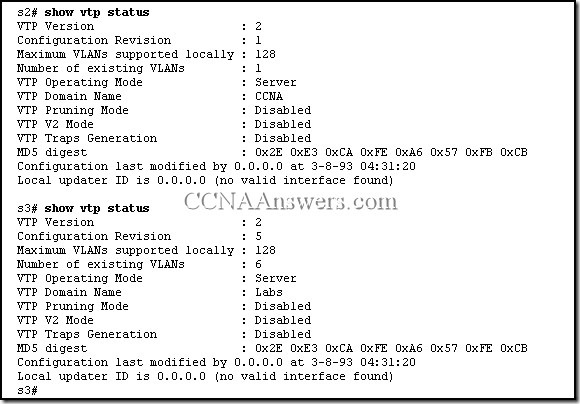 Correct
Correct
Incorrect
-
Question 51 of 100
51. Question
1 pointsIn a three-layer hierarchical network design, which distribution layer function delineates broadcast domains?Correct
Incorrect
-
Question 52 of 100
52. Question
1 pointsWhich parameter is used to uniquely identify one wireless network from another?Correct
Incorrect
-
Question 53 of 100
53. Question
1 pointsWhich three statements are correct concerning the default configuration of a new switch? (Choose three.)Correct
Incorrect
-
Question 54 of 100
54. Question
1 pointsRefer to the exhibit. How is port Gi1/1 on SWT-A functioning in the spanning-tree topology?Correct
Incorrect
-
Question 55 of 100
55. Question
1 pointsWhich statement describes the use of voice VLANs in Cisco IP telephony?Correct
Incorrect
-
Question 56 of 100
56. Question
1 pointsRefer to the exhibit. The VTP domain has been configured as shown in the exhibit. The network technician accidentally configured the VTP server as a VTP client. After the technician reloaded the switches, all users in the VTP domain started to complain that they lost connectivity to the users on the same VLANs that are connected to other switches. What should be done in the future to prevent losing all VLAN configurations in a VTP domain?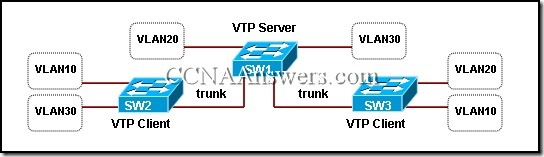 Correct
Correct
Incorrect
-
Question 57 of 100
57. Question
1 pointsRefer to the exhibit. How does SW1 manage traffic coming from Host A? Correct
Correct
Incorrect
-
Question 58 of 100
58. Question
1 pointsWhat impact does the use of the mdix auto configuration command have on an Ethernet interface on a switch?Correct
Incorrect
-
Question 59 of 100
59. Question
1 pointsWhich CLI mode allows users to access all device commands, such as those used for configuration, management, and troubleshooting?Correct
Incorrect
-
Question 60 of 100
60. Question
1 pointsWhat will be the effect of the command S1# copy system:running-config172.16.2.155/tokyo-config?Correct
Incorrect
-
Question 61 of 100
61. Question
1 pointsCompany policy requires disabling the command history buffer on network devices. An administrator enters terminal no history size at the command prompt on a Cisco Catalyst switch and receives no error messages back, but the command history buffer is still available. What is the problem?Correct
Incorrect
-
Question 62 of 100
62. Question
1 pointsA network administrator is implementing VTP in a large campus LAN that contains one hundred switches. What are valid considerations for reliability and administration?Correct
Incorrect
-
Question 63 of 100
63. Question
1 pointsRefer to the exhibit. Switch SW-A is to be used as a temporary replacement for another switch in the VTP Student domain. What two pieces of information are indicated from the exhibited output? (Choose two.)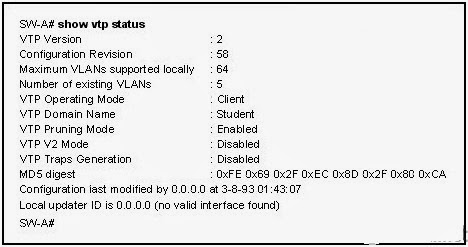 Correct
Correct
Incorrect
-
Question 64 of 100
64. Question
1 pointsWhat is the purpose of issuing the command switchport mode access on a switch interface?Correct
Incorrect
-
Question 65 of 100
65. Question
1 pointsRefer to the exhibit. What will be the result of the commands that are shown in the exhibit?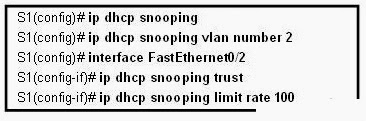 Correct
Correct
Incorrect
-
Question 66 of 100
66. Question
1 pointsRefer to the exhibit. What is the result of issuing these commands?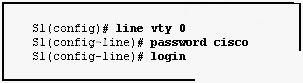 Correct
Correct
Incorrect
-
Question 67 of 100
67. Question
1 pointsWhat VLANs are allowed across a trunk when the range of allowed VLANs is set to the default value?Correct
Incorrect
-
Question 68 of 100
68. Question
1 pointsIn which mode is a VTP switch operating if it does not allow for the creation of local VLANs but it does accept VLAN updates from other switches in the same domain?Correct
Incorrect
-
Question 69 of 100
69. Question
1 pointsWhen port security is used on a switch, which violation mode will cause an SNMP trap to be sent and traffic to be dropped when the number of secure MAC addresses for a port is reached?Correct
Incorrect
-
Question 70 of 100
70. Question
1 pointsWhich type of traffic can still be received on a switch interface that is in STP blocking mode?Correct
Incorrect
-
Question 71 of 100
71. Question
1 pointsWhat is the purpose of configuring a switch port as a trunk port?Correct
Incorrect
-
Question 72 of 100
72. Question
1 pointsA network administrator is planning the upgrade of an enterprise LAN to feature Layer 3 support for the application of data security policies, aggregated links, and redundant devices and links. Which switches in the hierarchical three-layer design model support these network requirements?Correct
Incorrect
-
Question 73 of 100
73. Question
1 pointsThe global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?Correct
Incorrect
-
Question 74 of 100
74. Question
1 pointsWhich type of VLAN would accommodate untagged traffic on a 802.1q trunk port? data VLANCorrect
Incorrect
-
Question 75 of 100
75. Question
1 pointsWhich statement correctly describes an IBSS?Correct
Incorrect
-
Question 76 of 100
76. Question
1 pointsWhich two operations can be performed from the boot loader command line of a Cisco Catalyst switch? (Choose two.)Correct
Incorrect
-
Question 77 of 100
77. Question
1 pointsWhat are two requirements for configuring inter-VLAN routing using the router-on-a-stick model? (Choose two.)Correct
Incorrect
-
Question 78 of 100
78. Question
1 pointsWhat type of message do wireless clients transmit when they are searching for a specific wireless network?Correct
Incorrect
-
Question 79 of 100
79. Question
1 pointsA network administrator enters the enable command at the Switch> prompt of a new switch. What mode will the switch enter?Correct
Incorrect
-
Question 80 of 100
80. Question
1 pointsWhy is priority configured in 4096 increments when using PVST+?Correct
Incorrect
-
Question 81 of 100
81. Question
1 pointsWhat happens when the crypto key zeroize rsa command is entered on a switch configured with thetransport input ssh command on the vty lines?Correct
Incorrect
-
Question 82 of 100
82. Question
1 pointsWhat does TKIP have in common with AES?Correct
Incorrect
-
Question 83 of 100
83. Question
1 pointsWhat operational change will occur if an 802.11b client associates with an access point that is currently supporting clients utilizing 802.11g?Correct
Incorrect
-
Question 84 of 100
84. Question
1 pointsA network administrator issued the erase nvram: command on a switch. What will be the outcome of the command?Correct
Incorrect
-
Question 85 of 100
85. Question
1 pointsWhat identifier in the BPDU creates a unique BID for a switch?Correct
Incorrect
-
Question 86 of 100
86. Question
1 pointsWhich three statements are true regarding router-on-a-stick inter-VLAN routing? (Choose three.)Correct
Incorrect
-
Question 87 of 100
87. Question
1 pointsWhat are two benefits of the IEEE 802.11n standard over the IEEE 802.11G? (Choose two.)Correct
Incorrect
-
Question 88 of 100
88. Question
1 pointsWhat is an efficient and cost effective way to minimize the frequency and effects of broadcast storms on an Ethernet LAN?Correct
Incorrect
-
Question 89 of 100
89. Question
1 pointsWhich combination of DTP modes set on adjacent switches will cause the link to become an access link instead of a trunk link?Correct
Incorrect
-
Question 90 of 100
90. Question
1 pointsWhat advantage does cut-through switching provide?Correct
Incorrect
-
Question 91 of 100
91. Question
1 pointsWhich service should be disabled on a Cisco switch or router to prevent packet sniffers from capturing information about the device?Correct
Incorrect
-
Question 92 of 100
92. Question
1 pointsWhich switch forwarding method should be used on a network that employs frame classification based on an assigned Quality of Service (QoS) value?Correct
Incorrect
-
Question 93 of 100
93. Question
1 pointsWhich IEEE trunking protocol is used to encapsulate data traffic over a trunk link on a Cisco switch?Correct
Incorrect
-
Question 94 of 100
94. Question
1 pointsWhen an access point is placed near the outside wall of a building, which implementation design procedure should be used?Correct
Incorrect
-
Question 95 of 100
95. Question
1 pointsWhat allows WLAN clients to learn which networks and access points are available in an area?Correct
Incorrect
-
Question 96 of 100
96. Question
1 pointsWhat technique is a security attack that depletes the pool of IP addresses available for legitimate hosts?Correct
Incorrect
-
Question 97 of 100
97. Question
1 pointsWhich two devices can cause interference with the operation of a WLAN because they operate on similar frequencies? (Choose two.)Correct
Incorrect
-
Question 98 of 100
98. Question
1 pointsWhat is a result of improperly implementing a network with redundancy at Layer 2?Correct
Incorrect
-
Question 99 of 100
99. Question
1 pointsWhich statement is correct about STP architecture?Correct
Incorrect
-
Question 100 of 100
100. Question
1 pointsWhich statement is true about open authentication when it is enabled on an access point?- (requires no authentication)
Correct
Incorrect
