Time limit: 0
Quiz-summary
0 of 55 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
Information
CCNA 2 v6.0 – CCENT (ICND1) Practice Certification Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 55 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- Answered
- Review
-
Question 1 of 55
1. Question
1 pointsHow many /30 subnets can be created from one /27 subnetCorrect
Incorrect
Hint
A /27 subnet contains 32 IP addresses, and a /30 subnet contains 4 IP addresses, so eight /30 subnets can be created from one /27 subnet. -
Question 2 of 55
2. Question
1 pointsWhat information can be verified through the show ip dhcp binding command?Correct
Incorrect
Hint
This command displays a list of all IPv4 address to MAC address bindings that have been provided by the DHCPv4 service. 8.1.2.2 -
Question 3 of 55
3. Question
1 pointsRefer to the exhibit. A network administrator is reviewing port and VLAN assignments on switch S2 and notices that interfaces Gi0/1 and Gi0/2 are not included in the output. Why would the interfaces be missing from the output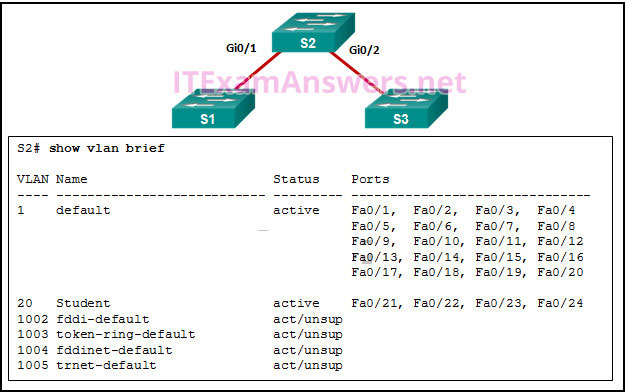 Correct
Correct
Incorrect
Hint
6.2.2 VLAN Trunks Interfaces that are configured as trunks do not belong to a VLAN and therefore will not show in the output of the show vlan brief commands. -
Question 4 of 55
4. Question
1 pointsRefer to the exhibit. A switch with a default configuration connects four hosts. The ARP table for host A is shown. What happens when host A wants to send an IP packet to host D?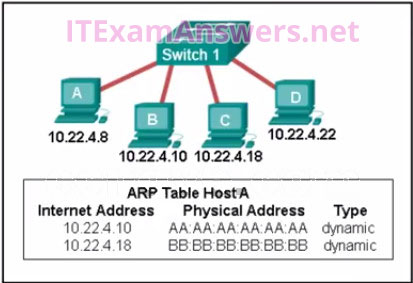 Correct
Correct
Incorrect
-
Question 5 of 55
5. Question
1 pointsRefer to the exhibit. A network administrator needs to add an ACE to the TRAFFIC-CONTROL ACL that will deny IP traffic from the subnet 172.23.16.0/20. Which ACE will meet this requirement?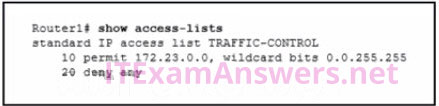 Correct
Correct
Incorrect
-
Question 6 of 55
6. Question
1 pointsWhich three layers of the OSI model map to the application layer of the TCP/IP model? (Choose three.)Correct
Incorrect
-
Question 7 of 55
7. Question
1 pointsRefer to the exhibit. When a packet arrives on interface Serial0/0/0 on R1, with a destination IP address of PC1, which two events occur? (Choose two)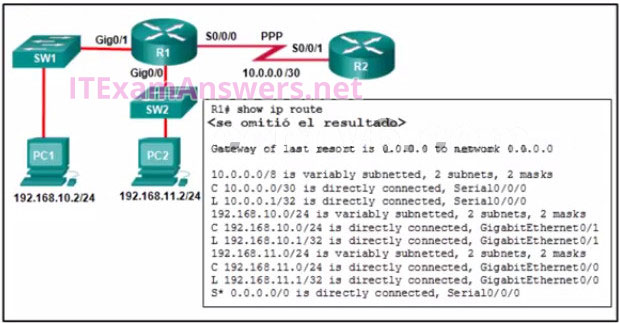 Correct
Correct
Incorrect
Hint
Routing and Switching Essentials 1.1.1 Router Functions 1.2.2 Path Determination A router will look in the routing table for a destination network and locate an exit interface to forward a packet to a destination. After the exit interface is determined, the router will encapsulate a packet into the correct frame type. (PPP) is a data link (layer 2) protocol used to establish a direct connection between two nodes. (from wikipedia) -
Question 8 of 55
8. Question
1 pointsWhat is the purpose of the overload keyword in the ip nat inside source list 1 pool NAT_POOL overload command?Correct
Incorrect
Hint
The primary difference between this configuration and the configuration for dynamic, one-to-one NAT is that the overload keyword is used. The overload keyword enables PAT. 9.2.3.1 -
Question 9 of 55
9. Question
1 pointsWhat type of installation is needed to view syslog messages?Correct
Incorrect
Hint
The syslog protocol allows networking devices to send their system messages across the network to syslog servers. -
Question 10 of 55
10. Question
1 pointsRefer to the exhibit. A network administrator has added a new subnet to the network and needs hosts on that subnet to receive IPv4 addresses from the DHCPv4 server. What two commands will allow hosts on the new subnet to receive addresses from the DHCP4 server? (Choose two.)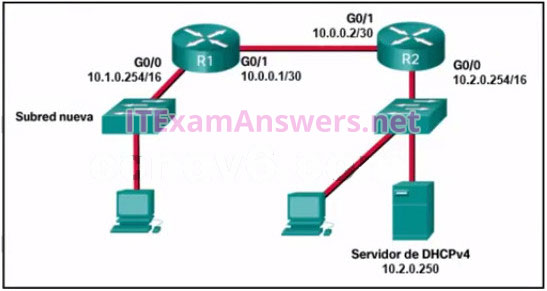 Correct
Correct
Incorrect
Hint
You need the router interface that is connected to the new subnet and the dhcp server address. -
Question 11 of 55
11. Question
1 pointsRefer to the exhibit. Static NAT is being configured to allow PC 1 access to the web server on the internal network. What two addresses are needed in place of A and B to complete the static NAT configuration? (Choose two.)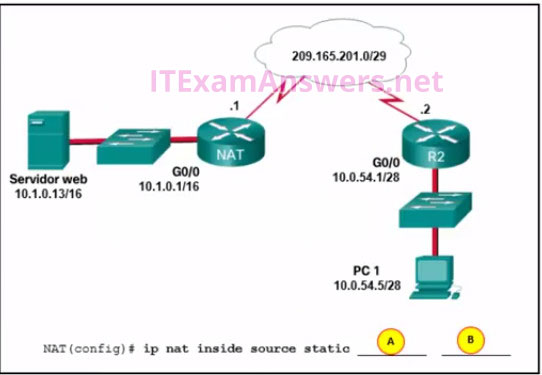 Correct
Correct
Incorrect
-
Question 12 of 55
12. Question
1 pointsWhen creating an IPv6 static route, when must a next-hop IPv6 address and an exit interface both be specifiedCorrect
Incorrect
Hint
Routing and Switching Essentials 2.2.3 Configure IPv6 Static Routes Link-local addresses are only unique on a given link, and the same address could exist out multiple interfaces. For that reason, any time a static route specifies a link-local address as the next hop, it must also specify the exit interface. This is called a fully specified static route. -
Question 13 of 55
13. Question
1 pointsWhich address prefix range is reserved for IPv4 multicast?Correct
Incorrect
-
Question 14 of 55
14. Question
1 pointsRefer to the exhibit. What would happen after the IT administrator enters the new static route?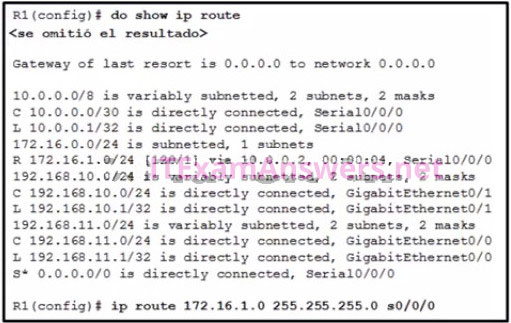 Correct
Correct
Incorrect
Hint
A route will be installed in a routing table if there is not another routing source with a lower administrative distance. If a route with a lower administrative distance to the same destination network as a current route is entered, the route with the lower administrative distance will replace the route with a higher administrative distance. -
Question 15 of 55
15. Question
1 pointsWhat effect does the default-information originate command have on a Cisco router that is configured for RIP?Correct
Incorrect
-
Question 16 of 55
16. Question
1 pointsWhich type of IPv6 address refers to any unicast address that is assigned to multiple hosts?Correct
Incorrect
Hint
The anycast address is a unicast address that is assigned to multiple hosts. Anycast addresses are usually used to locate the nearest server of a specifc type–for example, the nearest DNS or network time server. Assigning the same unicast address to more than one interface makes it an anycast address. You can have link-local, unique local, or global unicast anycast addresses. When you assign an anycast address to an interface, you must explicitly identify the address as an anycast address. -
Question 17 of 55
17. Question
1 pointsAn administrator wants to replace the configuration file on a Cisco router by loading a new configuration file from a TFTP server. What two things does the administrator need to know before performing this task? (Choose two.)Correct
Incorrect
Hint
Routing and Switching Essentials 10.3.3 IOS Image Management In order to identify the exact location of the desired configuration file, the IP address of the TFTP server and the name of the configuration file are essential information. Because the file is a new configuration, the name of the current configuration file is not necessary. -
Question 18 of 55
18. Question
1 pointsRefer to the exhibit. Inter-VLAN communication between VLAN 10, VLAN 20, and VLAN 30 is not successful. What is the problem?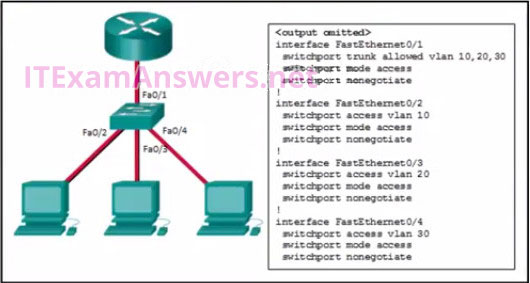 Correct
Correct
Incorrect
Hint
6.3.3 Configure Router-on-a-Stick Inter-VLAN Routing To forward all VLANs to the router, the switch interface Fa0/1 must be configured as a trunk interface with the switchport mode trunk command. -
Question 19 of 55
19. Question
1 pointsWhich statement describes the Cisco License Manager?Correct
Incorrect
Hint
Routing and Switching Essentials 10.3.4 Software Licensing Cisco License Manager (CLM) is available as a free download from the Cisco website and is a standalone application that helps network administrators deploy licenses across entire networks. -
Question 20 of 55
20. Question
1 pointsA user sends an HTTP request to a web server on a remote network. During encapsulation for this request, what information is added to the address field of a frame to indicate the destination?Correct
Incorrect
Hint
A frame is encapsulated with source and destination MAC addresses. The source device will not know the MAC address of the remote host. An ARP request will be sent by the source and will be responded to by the router. The router will respond with the MAC address of its interface, the one which is connected to the same network as the source. -
Question 21 of 55
21. Question
1 pointsA network administrator is designing an IPv4 addressing scheme and requires these subnets. 1 subnet of 100 hosts 2 subnets of 80 hosts 2 subnets of 30 hosts 4 subnets of 20 hosts Which combination of subnets and masks will provide the best addressing plan for these requirementsCorrect
Incorrect
Hint
IPv4 subnets that require 100 and 80 hosts are provided by creating subnets of 126 usable addresses, each of which requires 7 host bits. The resulting mask is 255.255.255.128. Subnets that require 30 and 20 hosts are provided by creating subnets of 30 usable addresses, each of which requires 5 host bits. The resulting mask is 255.255.255.224. Creating nine subnets, each consisting of 126 usable addresses, would waste large numbers of addresses in the six smaller subnets. -
Question 22 of 55
22. Question
1 pointsRefer to the exhibit. How was the host route 2001:DB8:CAFE:4::1/128 installed in the routing table?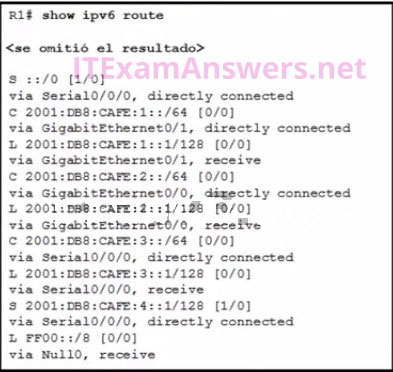 Correct
Correct
Incorrect
Hint
A host route is an IPv6 route with a 128-bit mask. A host route can be installed in a routing table automatically when an IP address is configured on a router interface or manually if a static route is created -
Question 23 of 55
23. Question
1 pointsWhat are three characteristics of the CSMA/CD process? (Choose three.)Correct
Incorrect
Hint
The Carrier Sense Multiple Access/Collision Detection (CSMA/CD) process is used in half-duplex Ethernet LANs. Figure 1 shows an Ethernet LAN using a hub. The CSMA process is as follows: -
Question 24 of 55
24. Question
1 pointsA network engineer is troubleshooting connectivity issues among interconnected Cisco routers and switches. Which command should the engineer use to find the IP address information, host name, and IOS version of neighboring network devices?Correct
Incorrect
Hint
The show cdp neighbors command provides helpful information about each CDP neighbor device, including the following: Device identifiers – The host name of the neighbor device (S1) Port identifier – The name of the local and remote port (Gig 0/1 and Fas 0/5, respectively) Capabilities list – Whether the device is a router or a switch (S for switch; I for IGMP is beyond scope for this course) Platform – The hardware platform of the device (WS-C2960 for Cisco 2960 switch) he show cdp neighbors detail command can also provide information, such as the neighbors’ IOS version and IPv4 address, 10.1.1.3 -
Question 25 of 55
25. Question
1 pointsFill in the blank- When port security is enabled, a switch port uses the default violation mode of (shutdown) until specifically configured to use a different violation mode.
Correct
Incorrect
Hint
If no violation mode is specified when port security is enabled on a switch port, then the security violation mode defaults to shutdown. Routing and Switching Essentials 5.2.2 Switch Port Security -
Question 26 of 55
26. Question
1 pointsRefer to the exhibit. Which source address is being used by router R1 for packets being forwarded to the Internet?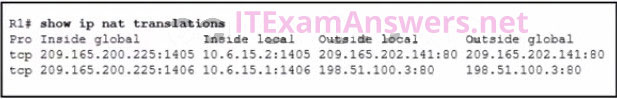 Correct
Correct
Incorrect
Hint
The inside global address is used as the source address for packets leaving the network -
Question 27 of 55
27. Question
1 pointsWhich feature on a Cisco router permits the forwarding of traffic for which there is no specific routeCorrect
Incorrect
Hint
1.2.2 Path Determination A default static route is used as a gateway of last resort to forward unknown destination traffic to a next hop/exit interface. The next-hop or exit interface is the destination to send traffic to on a network after the traffic is matched in a router. The route source is the location a route was learned from. -
Question 28 of 55
28. Question
1 pointsWhich three statements characterize UDP (Choose three.)Correct
Incorrect
Hint
UDP is a simple protocol that provides the basic transport layer functions. It has much lower overhead than TCP because it is not connection-oriented and does not offer the sophisticated retransmission, sequencing, and flow control mechanisms that provide reliability. -
Question 29 of 55
29. Question
1 pointsRefer to the exhibit. What will router R1 do with a packet that has a destination IPv6 address of 2001:db8:cafe:5::1?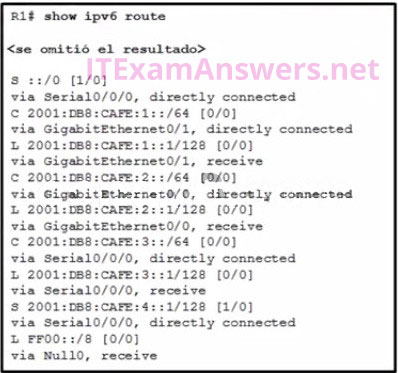 Correct
Correct
Incorrect
Hint
Routing and Switching Essentials 2.2.4 Configure IPv6 Default Routes The route ::/0 is the compressed form of the 0000:0000:0000:0000:0000:0000:0000:0000/0 default route. The default route is used if a more specific route is not found in the routing table. -
Question 30 of 55
30. Question
1 pointsHow will a router handle static routing differently if Cisco Express Forwarding is disabledCorrect
Incorrect
Hint
Routing and Switching Essentials 2.2.1 Configure IPv4 Static Routes In most platforms running IOS 12.0 or later, Cisco Express Forwarding is enabled by default. Cisco Express Forwarding eliminates the need for the recursive lookup. If Cisco Express Forwarding is disabled, multiaccess network interfaces require fully specified static routes in order to avoid inconsistencies in their routing tables. Point-to-point interfaces do not have this problem, because multiple end points are not present. With or without Cisco Express Forwarding enabled, using an exit interface when configuring a static route is a viable option. -
Question 31 of 55
31. Question
1 pointsRefer to the exhibit. A network technician issues the command show vlan to verify the VLAN configuration. Based on the output, which port should be assigned with native VLAN?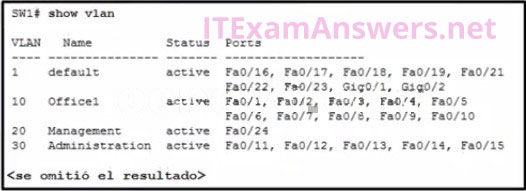 Correct
Correct
Incorrect
-
Question 32 of 55
32. Question
1 pointsWhich two things should a network administrator modify on a router to perform password recovery? (Choose two.)Correct
Incorrect
-
Question 33 of 55
33. Question
1 pointsWhat are two reasons why an administrator might choose to use static routing rather than dynamic routing? (Choose two.)Correct
Incorrect
-
Question 34 of 55
34. Question
1 pointsAn administrator who is troubleshooting connectivity issues on a switch notices that a switch port configured for port security is in the err-disabled state. After verifying the cause of the violation, how should the administrator re-enable the port without disrupting network operation?Correct
Incorrect
Hint
To re-enable the port, use the shutdown interface configuration mode command (Figure 3). Then, use the no shutdown interface configuration command to make the port operational. -
Question 35 of 55
35. Question
1 pointsA network administrator has been allocated the IPv4 10.10.240.0/20 block of addresses for a LAN. Two devices on two different, but contiguous, subnets on the LAN have been assigned the addresses 10.10.247.1/21 and 10.10.248.10/24, respectively. The administrator has to create a third subnet from the remaining address range. To optimize the use of this address space, the new subnet will follow on directly from the existing subnets. What is the first available host address in the next available subnetCorrect
Incorrect
Hint
The complete address range of the subnet with the host 10.10.247.1/21 is 10.10.240.0/21 to 10.10.247.255/21. The complete address range of the subnet that contains the host 10.10.248.10/24 is 10.10.248.0/24 to 10.10.248.255/24. This means that the next subnet will have a network address of 10.10.249.0 with a prefix length between 24 and 30. The first useable host address on this new subnet is therefore 10.10.249.1. -
Question 36 of 55
36. Question
1 pointsRefer to the exhibit. A ping to PC3 is issued from PC0, PC1, and PC2 in this exact order. Which MAC addresses will be contained in the S1 MAC address table that is associated with the Fa0/1 port?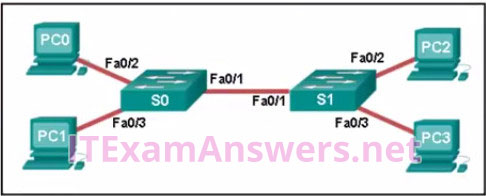 Correct
Correct
Incorrect
Hint
Switch S1 builds a MAC address table based on the source MAC address in the frame and the port upon which the frame enters the switch. The PC2 MAC address will be associated with port FA0/2. Because port FA0/1 of switch S1 connects with another switch, port FA0/1 will receive frames from multiple different devices. The MAC address table on switch S1 will therefore contain MAC addresses associated with each of the sending PCs. -
Question 37 of 55
37. Question
1 pointsRefer to the exhibit. A network administrator issues the show lldp neighbors command to display information about neighboring devices. What can be determined based on the information?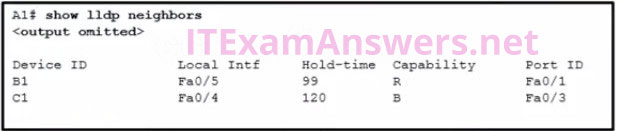 Correct
Correct
Incorrect
-
Question 38 of 55
38. Question
1 pointsWhich two devices allow hosts on different VLANs to communicate with each other (Choose two.)Correct
Incorrect
Hint
Routing and Switching Essentials 6.3.1 Inter-VLAN Routing Operation Members of different VLANs are on separate networks. For devices on separate networks to be able to communicate, a Layer 3 device, such as a router or Layer 3 switch, is necessary. -
Question 39 of 55
39. Question
1 pointsRefer to the exhibit. Host A sends a data packet to host B. What will be the addressing information of the data packet when it reaches host B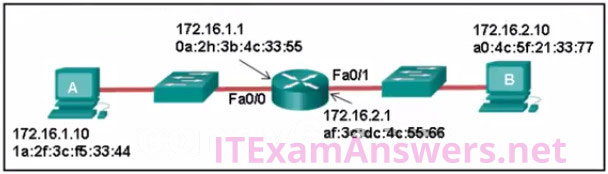 Correct
Correct
Incorrect
-
Question 40 of 55
40. Question
1 pointsData is being sent from a source PC to a destination server. Which three statements correctly describe the function of TCP or UDP in this situation (Choose three.)Correct
Incorrect
Hint
Layer 4 port numbers identify the application or service which will handle the data. The source port number is added by the sending device and will be the destination port number when the requested information is returned. Layer 4 segments are encapsulated within IP packets. UDP, not TCP, is used when low overhead is needed. A source IP address, not a TCP source port number, identifies the sending host on the network. Destination port numbers are specific ports that a server application or service monitors for requests. -
Question 41 of 55
41. Question
1 pointsWhat is defined by the ip nat pool command when configuring dynamic NAT?Correct
Incorrect
Hint
Routing and Switching Essentials 9.2.2 Configure Dynamic NAT Dynamic NAT uses a pool of inside global addresses that are assigned to outgoing sessions. Creating the pool of inside global addresses is accomplished using the ip nat pool command. -
Question 42 of 55
42. Question
1 pointsWhich address type is not supported by IPv6Correct
Incorrect
Hint
IPv6 supports unicast, private, and multicast addresses but does not support Layer 3 broadcasts. -
Question 43 of 55
43. Question
1 pointsWhat is the purpose of setting the native VLAN separate from data VLANs?Correct
Incorrect
Hint
Routing and Switching Essentials 6.1.1 Overview of VLANs When a Cisco switch trunk port receives untagged frames (unusual in well-designed networks), it forwards these frames to the native VLAN. When the native VLAN is moved away from data VLANs, those untagged frames will not compete for bandwidth in the data VLANs. The native VLAN is not designed for carrying management traffic, but rather it is for backward compatibility with legacy LAN scenarios. -
Question 44 of 55
44. Question
1 pointsWhich ACE would permit traffic from hosts only on the 192.168.8.0/22 subnet?Correct
Incorrect
-
Question 45 of 55
45. Question
1 pointsWhich two issues might cause excessive runt and giant frames in an Ethernet network? (Choose two.)Correct
Incorrect
Hint
Routing and Switching Essentials 5.1.2 Configure Switch Ports In an Ethernet network, a runt is a frame that is shorter than 64 bytes and a giant is a frame that is longer than the maximum allowed length. Both are often caused by NIC malfunctioning, but can also be caused by excessive collisions. CRC errors usually indicate a media or cable error caused by electrical interference, loose or damaged connections, or using the incorrect cabling type. -
Question 46 of 55
46. Question
1 pointsRefer to the exhibit. Which static route would an IT technician enter to create a backup route to the 172.16.1.0 network that is only used if the primary RIP learned route fails?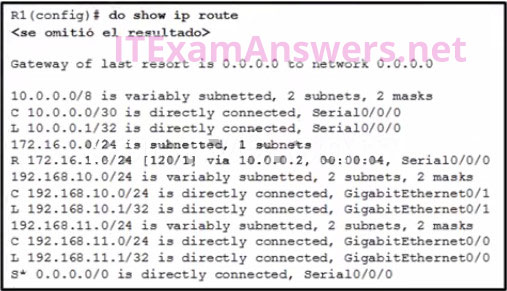 Correct
Correct
Incorrect
Hint
Routing and Switching Essentials 2.2.5 Configure Floating Static Routes A backup static route is called a floating static route. A floating static route has an administrative distance greater than the administrative distance of another static route or dynamic route. -
Question 47 of 55
47. Question
1 pointsRefer to the exhibit. Which three events will occur as a result of the configuration shown on R1? (Choose three.)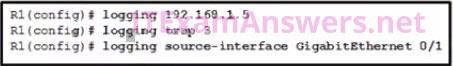 Correct
Correct
Incorrect
-
Question 48 of 55
48. Question
1 pointsWhich IPv6 prefix is reserved for communication between devices on the same link?Correct
Incorrect
Hint
fe80::/10 — Addresses in the link-local prefix are only valid and unique on a single link. Within this prefix only one subnet is allocated (54 zero bits), yielding an effective format of fe80::/64. The least significant 64 bits are usually chosen as the interface hardware address constructed in modified EUI-64 format. A link-local address is required on every IPv6-enabled interface—in other words, applications may rely on the existence of a link-local address even when there is no IPv6 routing. These addresses are comparable to the auto-configuration addresses 169.254.0.0/16 of IPv4. fc00::/7 — Unique local addresses (ULAs) are intended for local communication. They are routable only within a set of cooperating sites.[24] The block is split into two halves, the upper half (fd00::/8) is used for “probabilistically unique” addresses in which a 40-bit pseudorandom number is used to obtain a /48 allocation. This means that there is only a small chance that two sites that wish to merge or communicate with each other will have conflicting addresses. No allocation method for the lower half of the block (fc00::/8) is currently defined. These addresses are comparable to IPv4 private addresses (10.0.0.0/8, 172.16.0.0/12 and 192.168.0.0/16) -
Question 49 of 55
49. Question
1 pointsRefer to the exhibit. Packets destined to which two networks will require the router to perform a recursive lookup? (Choose two.)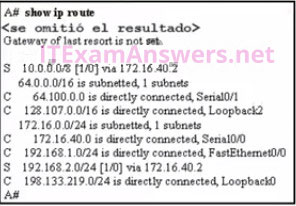 Correct
Correct
Incorrect
-
Question 50 of 55
50. Question
1 pointsRefer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2 (Choose two.)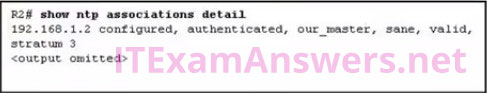 Correct
Correct
Incorrect
Hint
Routing and Switching Essentials 10.2.1 NTP With the show NTP associations command, the IP address of the NTP master is given. -
Question 51 of 55
51. Question
1 pointsA network technician is configuring port security on a LAN switch interface. The security policy requires host MAC addresses to be learned dynamically, stored in the address table, and saved to the switch running configuration. Which command does the technician need to add to the following configuration to implement this policy?Correct
Incorrect
-
Question 52 of 55
52. Question
1 pointsAfter a license has been purchased and installed, what is the next step that is required before it is activated?Correct
Incorrect
Hint
Routing and Switching Essentials 10.3.5 License Verification and Management After the license is installed, the device needs to be reloaded to activate the license. -
Question 53 of 55
53. Question
1 pointsRefer to the exhibit. A technician is programming switch SW3 to manage voice and data traffic through port Fa0/20. What, if anything, is wrong with the configuration?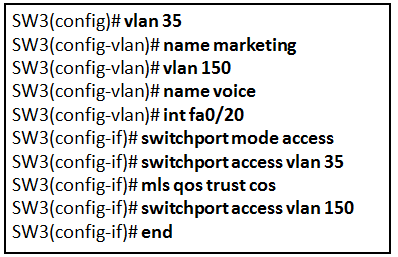 Correct
Correct
Incorrect
-
Question 54 of 55
54. Question
1 pointsA network administrator is using the router-on-a-stick model to configure a switch and a router for inter-VLAN routing. What configuration should be made on the switch port that connects to the routerCorrect
Incorrect
Hint
Routing and Switching Essentials 6.3.3 Configure Router-on-a-Stick Inter-VLAN Routing The port on the switch that connects to the router interface should be configured as a trunk port. Once it becomes a trunk port, it does not belong to any particular VLAN and will forward traffic from various VLANs. -
Question 55 of 55
55. Question
1 pointsOn which switch interface would an administrator configure an IP address so that the switch can be managed remotely?Correct
Incorrect
Hint
5.1.1 Configure a Switch with Initial Settings Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line
