- Refer to the exhibit. All of the routers in the network are configured with the ip subnet-zero command. Which network addresses should be used for Link A and Network A? (Choose two)
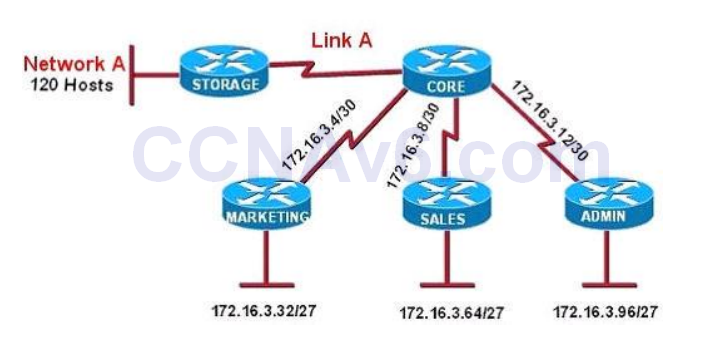
- A. Network A – 172.16.3.48/26
- B. Network A – 172.16.3.128/25*
- C. Network A – 172.16.3.192/26
- D. Link A – 172.16.3.0/30*
- E. Link A – 172.16.3.40/30
- F. Link A – 172.16.3.112/30
Show (Hide) Explanation/ReferenceNetwork A needs 120 hosts < 128 = 27 -> Need a subnet mask of 7 bit 0s -> “/25″.Because the ip subnet-zero command is used, network 172.16.3.0/30 can be used.
Answer E “Link A – 172.16.3.40/30″ is not correct because this subnet belongs to MARKETING subnet (172.16.3.32/27).
Answer F “Link A – 172.16.3.112/30″ is not correct because this subnet belongs to ADMIN subnet (172.16.3.96/27). - What is the correct routing match to reach 172.16.1.5/32?
- A. 172.16.1.0/26*
- B. 172.16.1.0/25
- C. 172.16.1.0/24
- D. the default route
Show (Hide) Explanation/ReferenceAlthough all above answers are correct but 172.16.1.0/26 is the best choice as it is the most specific prefix-match one. - You have been asked to come up with a subnet mask that will allow all three web servers to be on the same network while providing the maximum number of subnets. Which network address and subnet mask meet this requirement?
- A. 192.168.252.0 255.255.255.252
- B. 192.168.252.8 255.255.255.248*
- C. 192.168.252.8 255.255.255.252
- D. 192.168.252.16 255.255.255.240
- E. 192.168.252.16 255.255.255.252
- Refer to the exhibit. What is the most appropriate summarization for these routes?
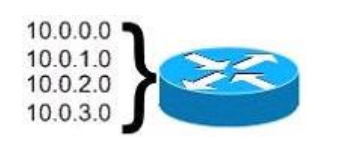
- A. 10.0.0.0/21
- B. 10.0.0.0/22*
- C. 10.0.0.0/23
- D. 10.0.0.0/24
Show (Hide) Explanation/ReferenceWe need to summarize 4 subnets so we have to move left 2 bits (22 = 4). In this question we can guess the initial subnet mask is /24 because 10.0.0.0, 10.0.1.0, 10.0.2.0, 10.0.3.0 belong to different networks. So “/24″ moves left 2 bits -> /22. - How many usable host are there per subnet if you have the address of 192.168.10.0 with a subnet mask of 255.255.255.240?
- A. 4
- B. 8
- C. 16
- D. 14*
Show (Hide) Explanation/ReferenceFrom the subnet mask of 255.255.255.240 (/28) we learn there are 24 – 2 = 14 hosts per subnet. - Assuming a subnet mask of 255.255.248.0, three of the following addresses are valid host addresses. Which are these addresses? (Choose three)
- A. 172.16.9.0*
- B. 172.16.8.0
- C. 172.16.31.0*
- D. 172.16.20.0*
Show (Hide) Explanation/ReferenceFrom the subnet mask of 255.255.248.0 we learn that the increment is 8 therefore 172.16.8.0 is a network address which cannot be assigned to a host. Other network addresses are 172.16.16.0, 172.16.24.0, 172.16.32.0… Notice that 172.16.31.0 is a valid host address (which belongs to 172.16.24.0 to 172.16.31.255 subnet). - Which IP configuration does the CIDR notation 192.168.1.1/25 refer?
- A. 192.168.1.1 255.255.255.64
- B. 192.168.1.1 255.255.255.1
- C. 192.168.1.1 255.255.255.32
- D. 192.168.1.1 255.255.255.256
- E. 192.168.1.1 255.255.255.128*
Show (Hide) Explanation/Reference“/25” means 1111 1111.1111 1111.1000 0000 in binary or 255.255.255.128 in decimal. - CIDR notation (255.255.255.252 ) in “/” notation
- A. 30 *
- B. 31
- C. 32
- D. 33
- Refer to the exhibit:
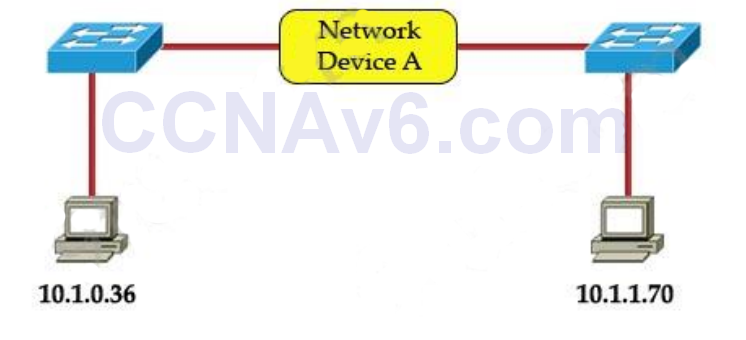
Which three statements correctly describe Network Device A? (Choose three)
- A. With a network wide mask of 255.255.255.128, each interface does not require an IP address.
- B. With a network wide mask of 255.255.255.128, each interface does require an IP address on a unique IP subnet.*
- C. With a network wide mask of 255.255.255.0, must be a Layer 2 device for the PCs to communicate with each other.
- D. With a network wide mask of 255.255.255.0, must be a Layer 3 device for the PCs to communicate with each other.*
- E. With a network wide mask of 255.255.254.0, each interface does not require an IP address.*
Show (Hide) Explanation/ReferenceThe principle here is if the subnet mask makes two IP addresses 10.1.0.36 and 10.1.1.70 in the same subnet then the Network device A does not need to have IP addresses on its interfaces (and we don’t need a Layer 3 device here).A quick way to find out the correct answers is notice that all 255.255.255.x subnet masks will separate these two IP addresses into two separate subnets so we need a Layer 3 device here and each interface must require an IP address on a unique IP subnet -> A, C are not correct while B, D are correct.
With 255.255.254.0 subnet mask, the increment here is 2 in the third octet -> the first subnet is from 10.1.0.0 to 10.1.1.255, in which two above IP addresses belong to -> each interface of Network device A does not require an IP address -> E is correct.
- Refer to the exhibit, you determine that Computer A cannot ping Computer B. Which reason for the problem is most likely true?
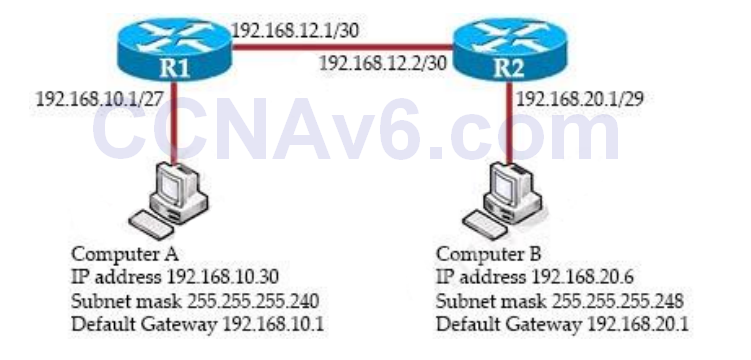
- A. The Subnet mask for Computer A is incorrect*
- B. The default gateway address for Computer A is incorrect
- C. The subnet mask for computer B is incorrect.
- D. The default gateway address for computer B is incorrect
- For which two reasons was RFC 1918 address space define (Choose two)
- A. to preserve public IPv4 address space*
- B. to reduce the occurrence of overlapping IP addresses*
- C. to preserve public IPv6 address space
- D. reduce the size of ISP routing tables
- E. to support the NAT protocol
Show (Hide) Explanation/ReferenceThe RFC 1518 is Classless Interdomain Routing (CIDR). CIDR is a mechanism developed to help alleviate the problem of exhaustion of IP addresses and growth of routing tables.The problems were:
+ With the classful routing system, individual networks were either limited to 254 hosts (/24) or 65,534 hosts (/16). For many network enterprises, 254 hosts were not enough and 65,534 were too large to be used efficiently.
+ Routing information overload. The size and rate of growth of the routing tables in Internet routers is beyond the ability of current software (and people) to effectively manage.
+ Eventual exhaustion of IP network numbers.To solve these problem, CIDR was selected as the solution in 1992.
In contrast to classful routing, which categorizes addresses into one of three blocks, CIDR allows for blocks of IP addresses to be allocated to Internet service providers. The blocks are then split up and assigned to the provider’s customers.
According to the CIDR standard, the first part of an IP address is a prefix, which identifies the network. The prefix is followed by the host identifier so that information packets can be sent to particular computers within the network. A CIDR address includes the standard 32-bit IP address and also the network prefix. For example, a CIDR address of 200.1.45.2/26, the “/26” indicates the first 26 bits are used to identify the unique network, leaving the remaining bits to identify the specific hosts.
Therefore, instead of assigning the whole block of a class B or C address, now smaller blocks of a class can be assigned. For example, instead of assigning a whole block of 200.1.45.0/24, a smaller block, like 200.1.45.0/27 or 200.1.45.32/27, can be assigned.
