- Which component of the Cisco SDN solution serves as the centralized management system?
- A. Cisco OpenDaylight
- B. Cisco ACI
- C. Cisco APIC*
- D. Cisco IWAN
Show (Hide) Explanation/ReferenceCisco Application Policy Infrastructure Controller (APIC)
The infrastructure controller is the main architectural component of the Cisco ACI solution. It is the unified point of automation and management for the Cisco ACI fabric, policy enforcement, and health monitoring. The APIC appliance is a centralized, clustered controller that optimizes performance and unifies operation of physical and virtual environments. The controller manages and operates a scalable multitenant Cisco ACI fabric. - Which two statements about northbound and southbound APIs are true? (Choose two)
- A. Only southbound APIs allow program control of the network.
- B. Only northbound APIs allow program control of the network.*
- C. Only southbound API interfaces use a Service Abstraction Layer.*
- D. Only northbound API interfaces use a Service Abstraction Layer.
- E. Both northbound and southbound API interfaces use a Service Abstraction Layer.
- F. Both northbound and southbound APIs allow program control of the network.
Show (Hide) Explanation/ReferenceA northbound interface is an interface that allows a particular component of a network to communicate with a higher-level component. Conversely, a southbound interface allows a particular network component to communicate with a lower-level component.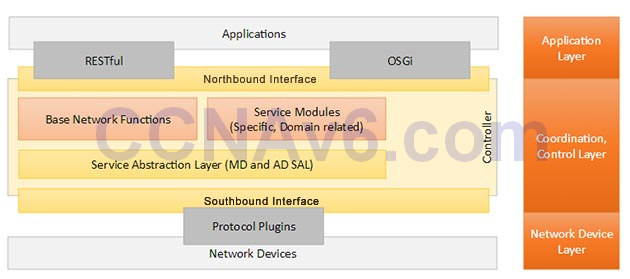
The northbound APIs on an SDN controller enable applications and orchestration systems to program the network and request services from it.
Southbound interfaces are implemented with a Service Abstraction Layer (SAL) which speak to network devices using SNMP and CLI (Command Line Interface) of the elements that make up the network. The main functions of SAL are:
+ Expose device services and capabilities to apps
+ Determine how to fulfill requested service irrespective of the underlying protocolNote:
+ An API is a method for one application (program) to exchange data with another application.
+ Interface here refers to the “software interface”, not the physical interfaces. - Which two options are primary responsibilities of the APIC-EM controller? (Choose two.)
- A. It automates network actions between different device types.*
- B. It provides robust asset management.
- C. It tracks license usage and Cisco IOS versions.
- D. It automates network actions between legacy equipment.
- E. It makes network functions programmable.*
Show (Hide) Explanation/ReferenceThe APIC-EM platform delivers many significant benefits. For example, it:+ Creates an intelligent, open, programmable network with open APIs
+ Can help customers save time, resources, and costs through advanced automation services
+ Can transform business-intent policies into dynamic network configuration
+ Provides a single point for network-wide automation and control - Which utility can you use to identify redundant or shadow rules?
- A. The ACL trace tool in Cisco APIC-EM.
- B. The ACL analysis tool in Cisco APIC-EM.*
- C. The Cisco APIC-EM automation scheduler.
- D. The Cisco IWAN application.
Show (Hide) Explanation/ReferenceCisco APIC-EM supports the following policy analysis features:+ Inspection, interrogation, and analysis of network access control policies.
+ Ability to trace application specific paths between end devices to quickly identify ACLs in use and problem areas.
+ Enables ACL change management with easy identification of conflicts and shadows -> Maybe B is the most suitable answer.The ACL trace tool can only help us to identify which ACL on which router is blocking or allowing traffic. It cannot help identify redundant/shadow rules.
Note:
Cisco Application Policy Infrastructure Controller Enterprise Module (APIC-EM) is a Cisco Software Defined Networking (SDN) controller, which uses open APIs for policy-based management and security through a single controller, abstracting the network and making network services simpler. APIC-EM provides centralized automation of policy-based application profiles.
Reference: CCNA Routing and Switching Complete Study Guide
Cisco Intelligent WAN (IWAN) application simplifies the provisioning of IWAN network profiles with simple business policies. The IWAN application defines business-level preferences by application or groups of applications in terms of the preferred path for hybrid WAN links. Doing so improves the application experience over any connection and saves telecom costs by leveraging cheaper WAN links.
Shadow rules are the rules that are never matched (usually because of the first rules). For example two access-list statements:
access-list 100 permit ip any any
access-list 100 deny tcp host A host BThen the second access-list statement would never be matched because all traffic have been already allowed by the first statement. In this case we call statement 1 shadows statement 2.
- Which utility can you use to identify the cause of a traffic-flow blockage between the two devices in a network?
- A. ACL path analysis tool in APIC-EM*
- B. iWAN application
- C. ACL analysis tool in APIC-EM
- D. APIC-EM automation scheduler
Show (Hide) Explanation/ReferenceThe ACL Path Analysis tool in APIC-EM can help to identify where the traffic was blocked in the transmission.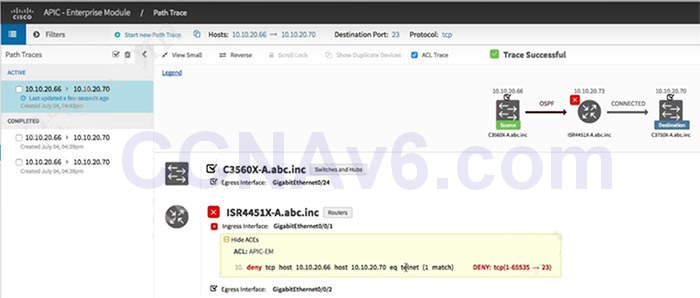
Icon
 means “there are ACLs that permit the traffic applied on the interface”.
means “there are ACLs that permit the traffic applied on the interface”.Icon
 means “traffic may or may not be blocked. For example, if your traffic matches a deny access control entry (ACE), traffic is denied. However, if your traffic matches any other ACEs, it is permitted. You can get this type of results if you leave out the protocol, source port, or destination port when defining a path trace”.
means “traffic may or may not be blocked. For example, if your traffic matches a deny access control entry (ACE), traffic is denied. However, if your traffic matches any other ACEs, it is permitted. You can get this type of results if you leave out the protocol, source port, or destination port when defining a path trace”.Icon
 means “there is an ACL on the device or interface that is blocking the traffic on the path”.
means “there is an ACL on the device or interface that is blocking the traffic on the path”.Icon
 means “there are no ACLs applied on the interface”.
means “there are no ACLs applied on the interface”.
CCNA 200-125 Exam: SDN Solution With Answers
Subscribe
0 Comments
