Time limit: 0
Quiz-summary
0 of 40 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
Information
Good luck!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 40 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- Answered
- Review
-
Question 1 of 40
1. Question
1 pointsWhat route would have the lowest administrative distance?Correct
Incorrect
-
Question 2 of 40
2. Question
1 pointsRefer to the exhibit. What command would be used to configure a static route on R1 so that traffic from both LANs can reach the 2001:db8:1:4::/64 remote network?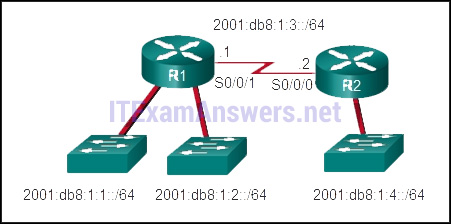 Correct
Correct
Incorrect
-
Question 3 of 40
3. Question
1 pointsWhat is a characteristic of the distribution layer in the three layer hierarchical model?Correct
Incorrect
Hint
One of the functions of the distribution layer is aggregating large-scale wiring closet networks. Providing access to end users is a function of the access layer, which is the network edge. Acting as a backbone is a function of the core layer. -
Question 4 of 40
4. Question
1 pointsWhich three statements are generally considered to be best practices in the placement of ACLs? (Choose three.)Correct
Incorrect
Hint
Extended ACLs should be placed as close as possible to the source IP address, so that traffic that needs to be filtered does not cross the network and use network resources. Because standard ACLs do not specify a destination address, they should be placed as close to the destination as possible. Placing a standard ACL close to the source may have the effect of filtering all traffic, and limiting services to other hosts. Filtering unwanted traffic before it enters low-bandwidth links preserves bandwidth and supports network functionality. Decisions on placing ACLs inbound or outbound are dependent on the requirements to be met. -
Question 5 of 40
5. Question
1 pointsRefer to the exhibit. How is a frame sent from PCA forwarded to PCC if the MAC address table on switch SW1 is empty?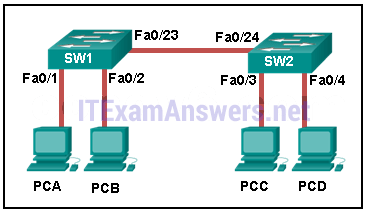 Correct
Correct
Incorrect
Hint
When a switch powers on, the MAC address table is empty. The switch builds the MAC address table by examining the source MAC address of incoming frames. The switch forwards based on the destination MAC address found in the frame header. If a switch has no entries in the MAC address table or if the destination MAC address is not in the switch table, the switch will forward the frame out all ports except the port that brought the frame into the switch. -
Question 6 of 40
6. Question
1 pointsWhich address prefix range is reserved for IPv4 multicast?Correct
Incorrect
Hint
Multicast IPv4 addresses use the reserved class D address range of 224.0.0.0 to 239.255.255.255. -
Question 7 of 40
7. Question
1 pointsWhich statement describes a difference between the operation of inbound and outbound ACLs?Correct
Incorrect
-
Question 8 of 40
8. Question
1 pointsWhat are three primary benefits of using VLANs? (Choose three.)Correct
Incorrect
Hint
Security, cost reduction, and improved IT staff efficiency are all benefits of using VLANs, along with higher performance, broadcast storm mitigation, and simpler project and application management. End users are not usually aware of VLANs, and VLANs do require configuration. Because VLANs are assigned to access ports, they do not reduce the number of trunk links. -
Question 9 of 40
9. Question
1 pointsWhat routing table entry has a next hop address associated with a destination network?Correct
Incorrect
Hint
Routing table entries for remote routes will have a next hop IP address. The next hop IP address is the address of the router interface of the next device to be used to reach the destination network. Directly-connected and local routes have no next hop, because they do not require going through another router to be reached. -
Question 10 of 40
10. Question
1 pointsWhich type of inter-VLAN communication design requires the configuration of multiple subinterfaces?Correct
Incorrect
Hint
The router-on-a-stick design always includes subinterfaces on a router. When a multilayer switch is used, multiple SVIs are created. When the number of VLANs equals the number of ports on a router, or when the management VLAN needs to be routed, any of the inter-VLAN design methods can be used. -
Question 11 of 40
11. Question
1 pointsWhich two devices allow hosts on different VLANs to communicate with each other? (Choose two.)Correct
Incorrect
Hint
Members of different VLANs are on separate networks. For devices on separate networks to be able to communicate, a Layer 3 device, such as a router or Layer 3 switch, is necessary. -
Question 12 of 40
12. Question
1 pointsWhich two statements correctly describe a router memory type and its contents? (Choose two.)Correct
Incorrect
Hint
ROM is a nonvolatile memory and stores bootup instructions, basic diagnostic software, and a limited IOS. Flash is a nonvolatile memory used as permanent storage for the IOS and other system-related files. RAM is volatile memory and stores the IP routing table, IPv4 to MAC address mappings in the ARP cache, packets that are buffered or temporarily stored, the running configuration, and the currently running IOS. NVRAM is a nonvolatile memory that stores the startup configuration file. -
Question 13 of 40
13. Question
1 pointsRefer to the exhibit. In what switch mode should port G0/1 be assigned if Cisco best practices are being used?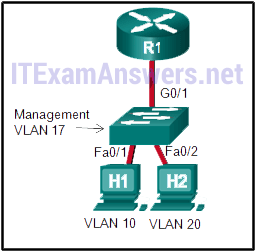 Correct
Correct
Incorrect
Hint
The router is used to route between the two VLANs, thus switch port G0/1 needs to be configured in trunk mode. -
Question 14 of 40
14. Question
1 pointsWhy does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?Correct
Incorrect
-
Question 15 of 40
15. Question
1 pointsWhich range of link-local addresses can be assigned to an IPv6-enabled interface?Correct
Incorrect
-
Question 16 of 40
16. Question
1 pointsWhat are three parts of an IPv6 global unicast address? (Choose three.)Correct
Incorrect
-
Question 17 of 40
17. Question
1 pointsAn IPv6 enabled device sends a data packet with the destination address of FF02::2. What is the target of this packet?Correct
Incorrect
Hint
FF02::2 identifies all IPv6 routers that exist on the link or network. FF02::1 is the target for all IPv6 enabled devices on the link or network. -
Question 18 of 40
18. Question
1 pointsA router is configured to participate in multiple routing protocol: RIP, EIGRP, and OSPF. The router must send a packet to network 192.168.14.0. Which route will be used to forward the traffic?Correct
Incorrect
-
Question 19 of 40
19. Question
1 pointsWhich subnet would include the address 192.168.1.96 as a usable host address?Correct
Incorrect
Hint
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address. -
Question 20 of 40
20. Question
1 pointsWhat does the IP address 192.168.1.15/29 represent?Correct
Incorrect
Hint
A broadcast address is the last address of any given network. This address cannot be assigned to a host, and it is used to communicate with all hosts on that network. -
Question 21 of 40
21. Question
1 pointsRefer to the exhibit. A network administrator is implementing the stateless DHCPv6 operation for the company. Clients are configuring IPv6 addresses as expected. However, the clients are not getting the DNS server address and the domain name information configured in the DHCP pool. What could be the cause of the problem?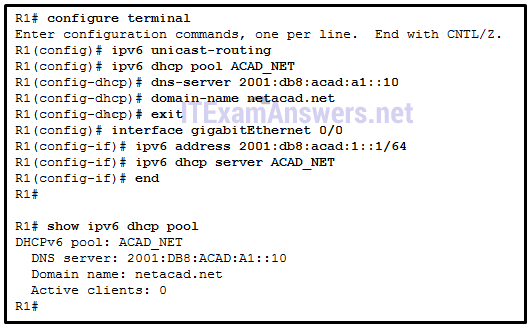 Correct
Correct
Incorrect
Hint
The router is configured for SLAAC operation because there is no configuration command to change the RA M and O flag value. By default, both M and O flags are set to 0. In order to permint stateless DHCPv6 operation, the interface command ipv6 nd other-config-flag should be issued. The GigabitEthernet interface is in working condition because clients can get RA messages and configure their IPv6 addresses as expected. Also, the fact that R1 is the DHCPv6 server and clients are getting RA messages indicates that clients can communicate with the DHCP server. The number of active clients is 0 because the DHCPv6 server does not maintain the state of clients IPv6 addresses (it is not configured for stateful DHCPv6 operation). The DNS server address issue is not relevant to the problem. -
Question 22 of 40
22. Question
1 pointsAn organization is assigned an IPv6 address block of 2001:db8:0:ca00::/56. How many subnets can be created without using bits in the interface ID space?Correct
Incorrect
Hint
Subnetting a /56 prefix to a /64 prefix involves increasing the network prefix by 8 bits. 8 bits will create 256 subnets. The last 64 bits of the address is reserved for the interface ID. -
Question 23 of 40
23. Question
1 pointsWhat is the term that is used for the area of a network that is affected when a device or network service experiences problems?Correct
Incorrect
-
Question 24 of 40
24. Question
1 pointsAs the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?Correct
Incorrect
Hint
EtherChannel is utilized on a network to increase speed capabilities by grouping multiple physical ports into one or more logical EtherChannel links between two switches. STP is used to provide redundant links that dynamically block or forward traffic between switches. FHRPs are used to group physical devices to provide traffic flow in the event of failure. -
Question 25 of 40
25. Question
1 pointsWhich characteristic would most influence a network design engineer to select a multilayer switch over a Layer 2 switch?Correct
Incorrect
Hint
Multilayer switches, also known as Layer 3 switches, can route and build a routing table. This capability is required in a multi-VLAN network and would influence the network designer to select a multilayer switch. The other options are features also available on Layer 2 switches, so they would not influence the decision to select a multilayer switch. -
Question 26 of 40
26. Question
1 pointsA network administrator is planning to add a new switch to the network. What should the network administrator do to ensure the new switch exchanges VTP information with the other switches in the VTP domain?Correct
Incorrect
Hint
In order to exchange VTP information, the new switch must be configured with the same VTP domain name and password as the other switches in the network. -
Question 27 of 40
27. Question
1 pointsRefer to the exhibit. Switch SW-A is to be used as a temporary replacement for another switch in the VTP Student domain. What two pieces of information are indicated from the exhibited output? (Choose two.)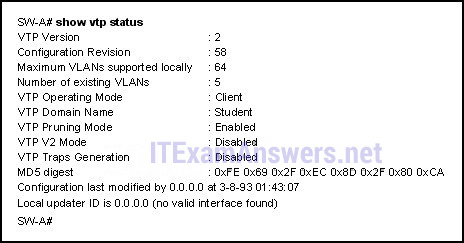 Correct
Correct
Incorrect
Hint
If a switch on the same VTP domain is added to the network and the switch has a higher configuration revision number, valid VLANs can be deleted and VLANs from the new switch can be sent to other switches in the VTP domain. This can result in loss of connectivity for some network devices. Always put a false domain name on a new switch and then change the VTP domain name to the correct one so the configuration revision number will be at 0 on the switch to be added. -
Question 28 of 40
28. Question
1 pointsRefer to the exhibit. The network administrator configures both switches as displayed. However, host C is unable to ping host D and host E is unable to ping host F. What action should the administrator take to enable this communication?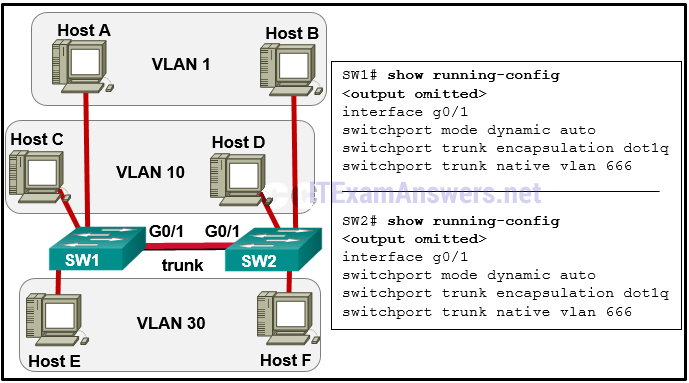 Correct
Correct
Incorrect
Hint
If one trunk port is in auto DTP negotiation mode, a trunk will be formed if the adjacent switch port is placed in trunk or dynamic desirable mode. -
Question 29 of 40
29. Question
1 pointsWhat eliminates switching loops?Correct
Incorrect
Hint
Spanning tree creates a single path through a switch network. This is important at Layer 2 because there is no feature such as the Layer 3 TTL to stop data from traveling infinitely through the network. This helps keep switch MAC address tables stable in broadcast storms, and when multiple frames are sent. -
Question 30 of 40
30. Question
1 pointsRefer to the exhibit. Which switch will be elected the root bridge and which switch will place a port in blocking mode? (Choose two.)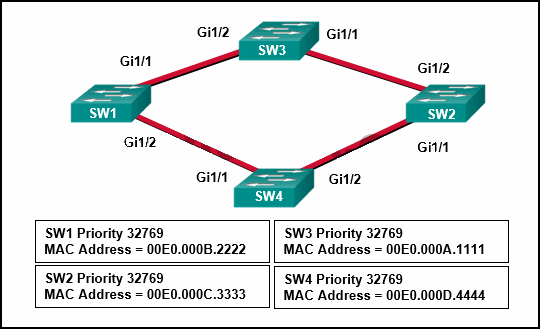 Correct
Correct
Incorrect
Hint
The spanning-tree root bridge election process determines which switch becomes root bridge based first on the lowest priority number and then by lowest MAC address. Because all of the switches have the same priority value, SW3 becomes the root bridge based on lowest MAC address. To determine which ports are blocking or forwarding, first determine which ports become the root port on each switch. Then determine which port becomes the designated port for each link. -
Question 31 of 40
31. Question
1 pointsRefer to the exhibit. A network administrator has configured OFPF in the topology as shown. What is the preferred path to get from the LAN network that is connected to R1 to the LAN network that is connected to R7?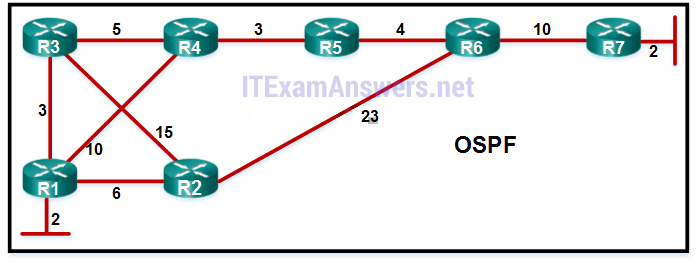 Correct
Correct
Incorrect
Hint
OSPF uses bandwidth to calculate the best path from source to destination. The path with the lowest cost from source to destination is elected as the best path. -
Question 32 of 40
32. Question
1 pointsWhich statement describes the autonomous system number used in EIGRP configuration on a Cisco router?Correct
Incorrect
Hint
The autonomous system number used in the EIGRP configuration is not associated with the Internet Assigned Numbers Authority (IANA) globally assigned autonomous system numbers that are used by external routing protocols. It just functions as a process ID, which is necessary because a router may run multiple instances of EIGRP. Each instance of EIGRP can be configured to support and exchange routing updates for different networks. An organization has the freedom to choose its own AS number in the EIGRP configuration. -
Question 33 of 40
33. Question
1 pointsAn EIGRP router loses the route to a network. Its topology table contains two feasible successors to the same network. What action will the router take?Correct
Incorrect
Hint
Because EIGRP uses the DUAL algorithm, the router is able to maintain information on all potential loop-free backup routes. In the event of the failure of a routing table entry, the router immediately inserts the best backup route into the routing table. -
Question 34 of 40
34. Question
1 pointsWhat is a function of OSPF hello packets?Correct
Incorrect
Hint
The OSPF hello packet serves three primary functions: discover OSPF neighbors and establish adjacencies, advertise parameters that OSPF neighbors must agree on, and elect the DR and BDR. -
Question 35 of 40
35. Question
1 pointsRefer to the exhibit. R1 and R2 are OSPFv3 neighbors. Which address would R1 use as the next hop for packets that are destined for the Internet?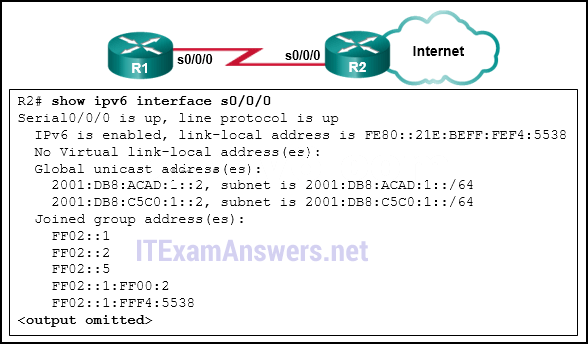 Correct
Correct
Incorrect
Hint
Because IPv6 routers can have multiple global addresses on each interface (or none at all), OSPFv3 uses the link-local addresses as the next hop for all routes. -
Question 36 of 40
36. Question
1 pointsRefer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)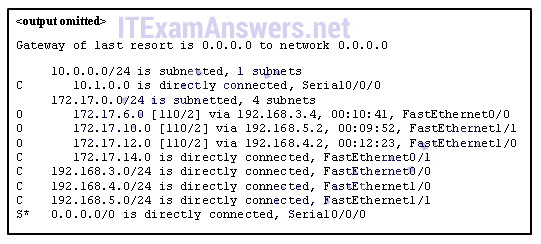
Sort elements
- FastEthernet1/1
- FastEthernet1/0
- FastEthernet0/1
- Serial0/0/0
- FastEthernet0/0
- The packet is dropped
-
packets with destination of 172.17.10.5
-
packets with destination of 172.12.10
-
packets with destination of 172.14.8
-
packets with destination of 172.18.20
-
packets with destination of 172.17.6.15
Correct
Incorrect
-
Question 37 of 40
37. Question
1 pointsMatch the DHCP message types to the order of the DHCPv4 process. (Not all options are used.)Sort elements
- DHCPREPLY
- DHCPOFFER
- DHCPREQUEST
- DHCPACK
- DHCPINFORMATION-REQUEST
-
Step 1
-
Step 2
-
Step 3
-
Step 4
Correct
Incorrect
-
Question 38 of 40
38. Question
1 pointsRefer to the exhibit. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network. (Not all options are used.)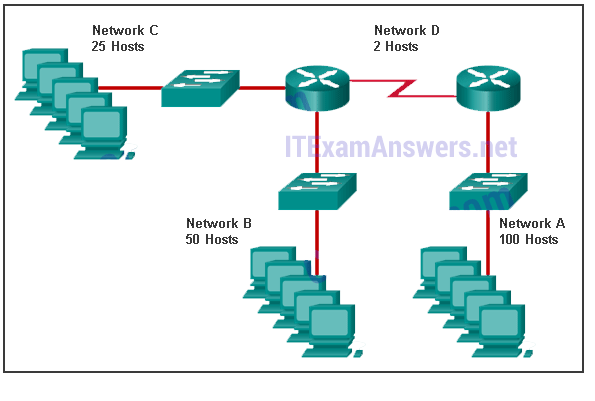
Sort elements
- 192.168.0.0/25
- 192.168.0.128/26
- 192.168.0.192/27
- 192.168.0.224/30
- 192.168.0.0/24
- 192.168.0.228/32
-
Network A
-
Network B
-
Network C
-
Network D
Correct
Incorrect
-
Question 39 of 40
39. Question
1 pointsMatch the description to the term. (Not all options are used.)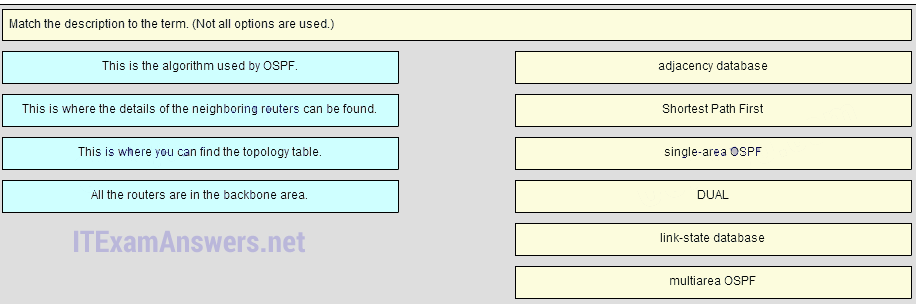
Sort elements
- Shortest Parth fist
- adjacency database
- link-state database
- single-area OSPF
- DUAL
- multiarea OSPF
-
This is the algorithm used by OSPF
-
This is where the details of the neighboring routers can be found
-
This is where you can find the topology table.
-
All the routers are in the backbone area.
Correct
Incorrect
Hint
Place the options in the following order: This is where the details of the neighboring routers can be found. -> adjacency database This is the algorithm used by OSPF. -> Shortest Path First All the routers are in the backbone area. -> Single-area OSPF – not scored – This is where you can find the topology table. -> link-state database – not scored – -
Question 40 of 40
40. Question
1 pointsMatch the order of precedence to the process logic that an OSPFv3 network router goes through in choosing a router ID. (Not all options are used.)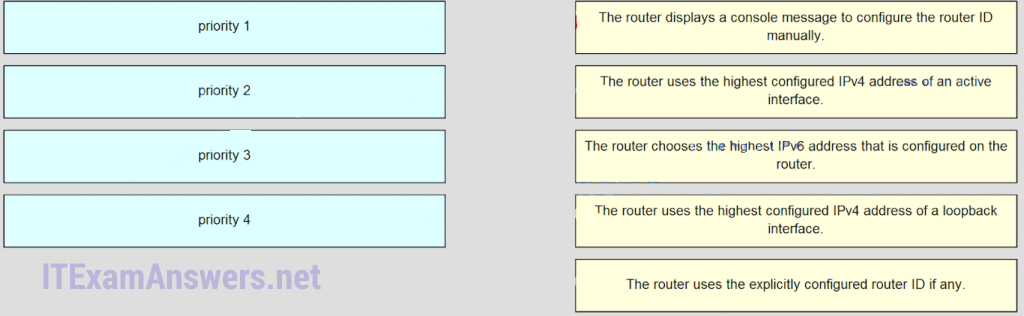
Sort elements
- The routers uses the explicitly configured router ID if any
- The routers uses the highest configured IPv4 address of a loopback interface
- The routers uses the highest configured IPv4 address of an active interface
- The routers display a console message to configure the router ID manually
- The routers chooses the highest IPv6 address that is configured on the router
-
priority 1
-
priority 2
-
priority 3
-
priority 4
Correct
Incorrect
