Command
IP Access-list
Use
This command is used to create named access-lists that matches packets on a given criteria. While access-lists are most commonly associated with security, there are numerous uses.
The benefit to named access-list is that you can assign a logical name and also reorder the access-list as needed. A little known fact is that you can also re-order numbered access-lists using this command.
Syntax
R1(config)#ip access-list <standard or extended> <name>
Options
The options are the same as regular numbered access-lists.
Wildcard Masks
Wildcard masks are how access-lists know what networks apply to the list. They are the inverse of the subnet mask.
For example, network 123.123.123.0 0.0.0.255 would match any ip address in the 123.123.123.0/24 network.
Because a /24 mask is 255.255.255.0 the inverse would be 0.0.0.255. For the network 34.77.108.0/28, the subnet mask would be 255.255.255.248 and the inverse would be 0.0.0.7
Notice how the subnet mask and the inverse add to 255.
Example
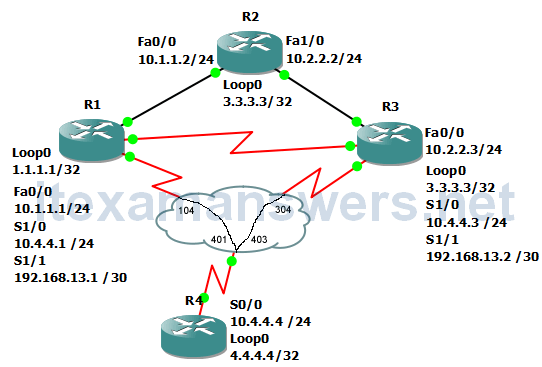
In this example, an access-list is created on R2 that will only deny packets sourced by the host 1.1.1.1 and apply the list to Fa0/0.
R2(config)#ip access-list standard NO_R1_LOOP R2(config-std-nacl)#deny 1.1.1.1 R2(config-std-nacl)#permit any R2(config-std-nacl)#int fa0/0 R2(config-if)#ip access-group NO_R1_LOOP in
Notice that only 1.1.1.1 is denied.
R1(config)#do ping 10.1.1.2 source 1.1.1.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.1.1.2, timeout is 2 seconds: Packet sent with a source address of 1.1.1.1 U.U.U Success rate is 0 percent (0/5) R1(config)#do ping 10.1.1.2 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.1.1.2, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/13/32 ms R1(config)#do ping 10.1.1.2 source lo1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.1.1.2, timeout is 2 seconds: Packet sent with a source address of 11.11.11.11 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/20/44 ms
In this example, the named access-list is modified to deny anything in the 1.0.0.0/8 network, instead of the host 1.1.1.1.
R2(config)#do show ip access-list NO_R1_LOOP Standard IP access list NO_R1_LOOP 10 deny 1.1.1.1 20 permit any (216 matches) R2(config)#ip access-list standard NO_R1_LOOP R2(config-std-nacl)#no 10 R2(config-std-nacl)#do show ip access-list NO_R1_LOOP Standard IP access list NO_R1_LOOP 20 permit any (243 matches) R2(config-std-nacl)#10 deny 1.0.0.0 0.255.255.255 R2(config-std-nacl)#do show ip access-list NO_R1_LOOP Standard IP access list NO_R1_LOOP 10 deny 1.0.0.0, wildcard bits 0.255.255.255 20 permit any (258 matches)
For the next example, the access-list 95 is edited to deny anything in the 1.0.0.0/8 network instead of the host 1.1.1.1.
R2(config)#ip access-list standard 95 R2(config-std-nacl)#no 10 R2(config-std-nacl)#do sh access-list 95 Standard IP access list 95 20 permit any (37908 matches) R2(config-std-nacl)#10 deny 1.0.0.0 0.255.255.255 R2(config-std-nacl)#do sh access-list 95 Standard IP access list 95 10 deny 1.0.0.0, wildcard bits 0.255.255.255 20 permit any (37908 matches)
