Lab Objective:
The objective of this lab exercise is for you to learn and understand how to configure a router or switch for SSH access. Your router or switch IOS must support encryption in order for the commands to work. You should see a k9 in the image name as well as a security statement from Cisco saying “This product contains cryptographic features…”.
Lab Purpose:
Protecting your Cisco devices by disabling Telnet and enabling SSH-only access is a core security step, as well as a CCNA exam requirement.
Certification Level:
This lab is suitable for CCENT certification exam preparation.
Lab Difficulty:
This lab has a difficulty rating of 7/10.
Readiness Assessment:
When you are ready for your certification exam, you should complete this lab in no more than 5 minutes.
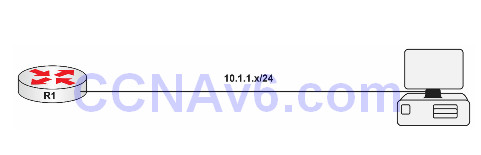
Lab Topology:
Please use any single router or switch to complete this lab so long as it has the correct IOS image.
Task 1:
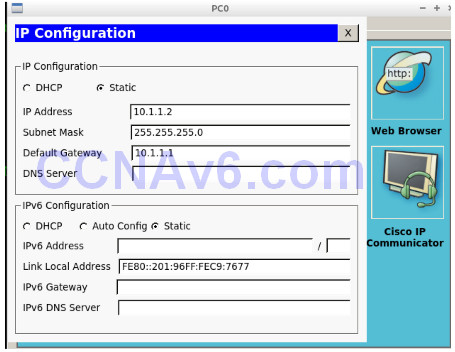
Attach a PC to a router using a switch or crossover cable and add the IP settings above to the devices. Configure any desired hostname on your device.
Task 2:
Configure a username and password on your router. Disable Telnet access on the VTY lines and enable SSH access.
Task 3:
Configure the router to use SSH with the settings below:
- Doman name: howtonetwork.com
- 1024 modulus SSH timeout: 60 seconds
- Authentication retries: 2
- SSH version 2
Task 4:
Disable HTTP (Hypertext Transfer Protocol) access to the router. Issue the appropriate show commands to check your SSH settings.
Task 5:
Connect to the router using a PC with SSH.
Configuration and Verification
Task 1:
For reference information on configuring hostnames and IP addresses, please refer to earlier labs.
For the PC (if you are using Packet Tracer):
Task 2:
R1(config)#username howtonetwork password cisco R1(config)#line vty 0 15 R1(config-line)#transport input ? all All protocols none No protocols ssh TCP/IP SSH protocol telnet TCP/IP Telnet protocol R1(config-line)#transport input ssh This command will also disable Telnet.
Task 3:
R1(config)#ip domain-name howtonetwork.com R1(config)#crypto key generate rsa The name for the keys will be: R1.howtonetwork.com Choose the size of the key modulus in the range of 360 to 2048 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. How many bits in the modulus [512]: 1024 % Generating 1024 bit RSA keys, keys will be non-exportable...[OK] R1(config)#ip ssh time-out ? <1-120> SSH time-out interval (secs) R1(config)#ip ssh time-out 60 R1(config)#ip ssh authentication-retries 2 R1(config)#ip ssh version 2
Task 4:
R1(config)#no ip http server R1#show ip ssh SSH Enabled - version 2.0 Authentication timeout: 60 secs; Authentication retries: 2 R1# R1#show crypto key ? mypubkey Show public keys associated with this router R1#show crypto key my R1#show crypto key mypubkey rsa % Key pair was generated at: 0:2:58 UTC Mar 1 1993 Key name: R1.howtonetwork.com Storage Device: not specified Usage: General Purpose Key Key is not exportable. Key Data: 6af47136 7dfa1d2d 53435e72 197f4ed8 229d6342 5c5b3b19 601bbae0 18491391 7d676c5e 3f4e6cb4 32e2f903 31b53943 40cb31ea 5d2552b3 00160600 77791266 51180b5a 4f759502 5df3ea6c 4ffda4fc 4b5351bb 11f16ac4 2374aeb6 44f60c4e % Key pair was generated at: 0:2:58 UTC Mar 1 1993 Key name: R1.howtonetwork.com.server Temporary key Usage: Encryption Key Key is not exportable. Key Data: 6b8a0260 167f96e7 117d29b7 58907508 704e7231 637db8c1 25a136f0 5b42e367 6177d5ee 78e49562 74c2323f 04153930 553fd07b 54dded20 1c5e4cc1 52a73cda 142c59d4 4f4145c4 045c761d 54f78bbe 2c669877 04727c1e 4c709e24 7d7ea3d2 Task 5: PC>ssh -l paul 10.1.1.1
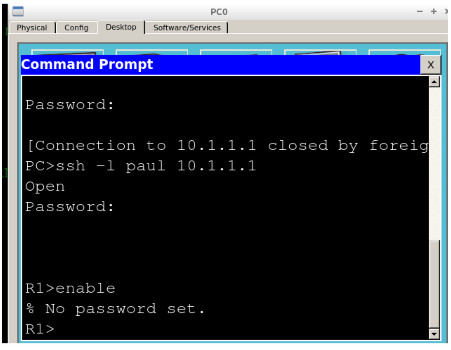
Task 5:
PC>ssh -l paul 10.1.1.1