Time limit: 0
Quiz-summary
0 of 25 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
Information
Network Defense (NetDef) Module 4 - 8 Group Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 25 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- Answered
- Review
-
Question 1 of 25
1. Question
1 pointsRefer to the exhibit. An administrator has configured a standard ACL on R1 and applied it to interface serial 0/0/0 in the outbound direction. What happens to traffic leaving interface serial 0/0/0 that does not match the configured ACL statements?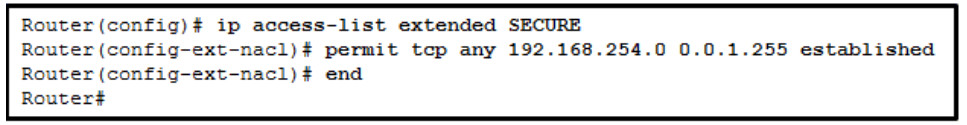 Correct
Correct
Incorrect
Hint
Any traffic that does not match one of the statements in an ACL has the implicit deny applied to it, which means the traffic is dropped. -
Question 2 of 25
2. Question
1 pointsWhen an inbound Internet-traffic ACL is being implemented, what should be included to prevent the spoofing of internal networks?Correct
Incorrect
Hint
Common ACEs to assist with antispoofing include blocking packets that have a source address in the 127.0.0.0/8 range, any private address, or any multicast addresses. Furthermore, the administrator should not allow any outbound packets with a source address other than a valid address that is used in the internal networks of the organization. -
Question 3 of 25
3. Question
1 pointsRefer to the exhibit. What is the result of adding the established argument to the end of the ACE?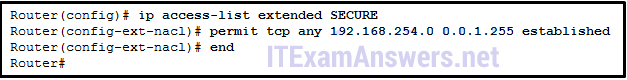 Correct
Correct
Incorrect
Hint
The established argument allows TCP return traffic from established connections to be sent on an outgoing interface to a network. -
Question 4 of 25
4. Question
1 pointsWhat single access list statement matches all of the following networks?- 192.168.16.0
- 192.168.17.0
- 192.168.18.0
- 192.168.19.0
Correct
Incorrect
Hint
The ACL statement access-list 10 permit 192.168.16.0 0.0.3.255 will match all four network prefixes. All four prefixes have the same 22 high order bits. These 22 high order bits are matched by the network prefix and wildcard mask of 192.168.16.0 0.0.3.255. -
Question 5 of 25
5. Question
1 pointsRefer to the exhibit. The IPv6 access list LIMITED_ACCESS is applied on the S0/0/0 interface of R1 in the inbound direction. Which IPv6 packets from the ISP will be dropped by the ACL on R1?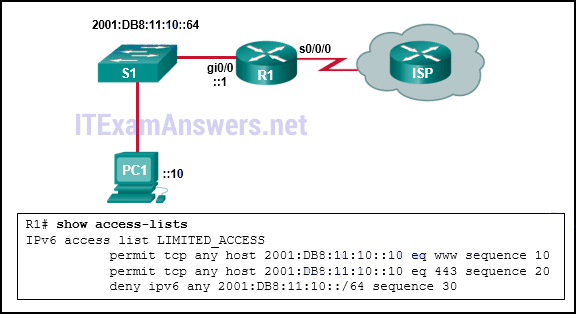 Correct
Correct
Incorrect
Hint
The access list LIMITED_ACCESS will block ICMPv6 packets from the ISP. Both port 80, HTTP traffic, and port 443, HTTPS traffic, are explicitly permitted by the ACL. The neighbor advertisements from the ISP router are implicitly permitted by the implicit permit icmp any any nd-na statement at the end of all IPv6 ACLs. -
Question 6 of 25
6. Question
1 pointsWhat are two characteristics of a stateful firewall? (Choose two.)Correct
Incorrect
Hint
Stateful firewalls are the most versatile and the most common firewall technologies in use. Stateful firewalls provide stateful packet filtering by using connection information maintained in a state table. Stateful filtering is a firewall architecture that is classified at the network layer. It also analyzes traffic at OSI Layers 4 and 5. Stateful firewalls cannot prevent application layer attacks because they do not examine the actual contents of an HTTP connection. -
Question 7 of 25
7. Question
1 pointsHow does a firewall handle traffic when it is originating from the public network and traveling to the DMZ network?Correct
Incorrect
Hint
Traffic originating from the public network and traveling toward the DMZ is selectively permitted and inspected. This type of traffic is typically email, DNS, HTTP, or HTTPS traffic. Return traffic from the DMZ to the public network is dynamically permitted. -
Question 8 of 25
8. Question
1 pointsWhich type of firewall is commonly part of a router firewall and allows or blocks traffic based on Layer 3 and Layer 4 information?Correct
Incorrect
Hint
A stateless firewall uses a simple policy table look-up that filters traffic based on specific criteria. These firewalls are usually part of a router firewall. They permit or deny traffic based on Layer 3 and Layer 4 information. -
Question 9 of 25
9. Question
1 pointsWhat is one limitation of a stateful firewall?Correct
Incorrect
Hint
Limitations of stateful firewalls include the following: Stateful firewalls cannot prevent application layer attacks. Protocols such as UDP and ICMP are not stateful and do not generate information needed for a state table. An entire range of ports must sometimes be opened in order to support specific applications that open multiple ports. Stateful firewalls lack user authentication. -
Question 10 of 25
10. Question
1 pointsHow does a firewall handle traffic when it is originating from the private network and traveling to the DMZ network?Correct
Incorrect
Hint
Traffic originating from the private network is inspected as it travels toward the public or DMZ network. This traffic is permitted with little or no restriction. Inspected traffic returning from the DMZ or public network to the private network is permitted. -
Question 11 of 25
11. Question
1 pointsWhen a Cisco IOS zone-based policy firewall is being configured, which three actions can be applied to a traffic class? (Choose three.)Correct
Incorrect
Hint
The inspect CCP action is similar to the classic firewall ip inspect command in that it inspects traffic going through the firewall and allowing return traffic that is part of the same flow to pass through the firewall. The drop action is similar to the deny parameter in an ACL. This action drops whatever traffic fits the defined policy. The pass action is similar to a permit ACL statement–traffic is allowed to pass through because it met the criteria of the defined policy statement. -
Question 12 of 25
12. Question
1 pointsWhich two statements describe the two configuration models for Cisco IOS firewalls? (Choose two.)Correct
Incorrect
Hint
There are two configuration models for Cisco IOS Firewalls, IOS Classic Firewalls and zone-based policy firewalls (ZPF). Both configuration models can be enabled concurrently on a router but they cannot be combined on a single interface. One benefit of using ZPF is that ZPF is not dependent on ACLs. -
Question 13 of 25
13. Question
1 pointsWhat are two benefits of using a ZPF rather than a Classic Firewall? (Choose two.)Correct
Incorrect
Hint
There are several benefits of a ZPF: – It is not dependent on ACLs. – The router security posture is to block unless explicitly allowed. – Policies are easy to read and troubleshoot with C3PL. – One policy affects any given traffic, instead of needing multiple ACLs and inspection actions. In addition, an interface cannot be simultaneously configured as a security zone member and for IP inspection. -
Question 14 of 25
14. Question
1 pointsWhen using Cisco IOS zone-based policy firewall, where is the inspection policy applied?Correct
Incorrect
Hint
After configuring the firewall policy, apply the policy to traffic that would flow between a pair of zones. Use the zone-pair security command in global configuration mode. -
Question 15 of 25
15. Question
1 pointsWhich zone-based policy firewall zone is system-defined and applies to traffic destined for the router or originating from the router?Correct
Incorrect
Hint
Zone-based policy firewalls typically have the private (internal or trusted) zone, the public (external or untrusted) zone, and the default self zone, which does not require any interfaces. The private or internal zone is commonly used for internal LANs. The public zone would include the interfaces that connect to an external (outside the business) interface. -
Question 16 of 25
16. Question
1 pointsWhich cloud security domain covers cloud-specific aspects of infrastructure security and foundations for operating securely in the cloud?Correct
Incorrect
Hint
The Security Guidance for Critical Areas of Focus in Cloud Computing v4 document developed by the Cloud Security Alliance (CSA) covers 14 domains of cloud security. Some of these domains are:- Infrastructure Security – describes cloud-specific aspects of infrastructure security and the foundation for operating securely in the cloud.
- Data Security and Encryption – describes those controls related to securing the data itself, of which encryption is one of the most important.
- Application Security – provides guidance on how to securely build and deploy applications in cloud computing environments, specifically for PaaS and IaaS.
- Management Plane and Business Continuity – describes the need to secure the cloud computing management plane and business continuity and disaster recovery procedures.
-
Question 17 of 25
17. Question
1 pointsWhich technique can be used to leverage virtual network topologies to run smaller and more isolated networks without incurring additional hardware costs?Correct
Incorrect
Hint
Microsegmentation (also referred to as hypersegregation) leverages virtual network topologies to run smaller and more isolated networks without incurring additional hardware costs. Microsegmentation techniques allow for more granular control of security for traffic and workflows within the cloud. -
Question 18 of 25
18. Question
1 pointsWhich algorithm is used with symmetric encryption to provide confidentiality?Correct
Incorrect
Hint
Advanced Encryption Standard (AES) is a symmetric encryption algorithm. MD5 is a hashing algorithm while RSA and ECC are asymmetric encryption algorithms. -
Question 19 of 25
19. Question
1 pointsIn which phase of application development is new software verified to run under the required security settings?Correct
Incorrect
Hint
In the staging phase developers test the application in a staging environment to verify that software runs under the required security settings. -
Question 20 of 25
20. Question
1 pointsWhat is the description of VM sprawl?Correct
Incorrect
Hint
VM Sprawl occurs when an organization has more VMs on the network than it can effectively control and manage. -
Question 21 of 25
21. Question
1 pointsWhich measure can a security analyst take to perform effective security monitoring against network traffic encrypted by SSL technology?Correct
Incorrect
Hint
Deploy a Cisco SSL Appliance to decrypt SSL traffic and send it to intrusion prevention system (IPS) appliances to identify risks normally hidden by SSL. -
Question 22 of 25
22. Question
1 pointsWhat technology has a function of using trusted third-party protocols to issue credentials that are accepted as an authoritative identity?Correct
Incorrect
Hint
Digital certificates are used to prove the authenticity and integrity of PKI certificates, but a PKI Certificate Authority is a trusted third-party entity that issues PKI certificates. PKI certificates are public information and are used to provide authenticity, confidentiality, integrity, and nonrepudiation services that can scale to large requirements. -
Question 23 of 25
23. Question
1 pointsMatch the description with the correct term.Correct
Incorrect
Hint
Place the options in the following order:Creating a message that says one thing but means something else to a specific audience Social steganography Making a message confusing so it is harder to understand Obfuscation Hiding data within an audio file Steganography Discovering that hidden information exists within a graphic file Steganalysis -
Question 24 of 25
24. Question
1 pointsWhich method tries all possible passwords until a match is found?Correct
Incorrect
Hint
Two common methods of cracking hashes are dictionary and brute force. Given time, the brute force method will always crack a password. -
Question 25 of 25
25. Question
1 pointsAn IT enterprise is recommending the use of PKI applications to securely exchange information between the employees. In which two cases might an organization use PKI applications to securely exchange information between users? (Choose two.)Correct
Incorrect
Hint
The Public Key Infrastructure (PKI) is a third party-system referred to as a certificate authority or CA. The PKI is the framework used to securely exchange information between parties. Common PKI applications are as follows: SSL/TLS certificate-based peer authentication Secure network traffic using IPsec VPNs HTTPS Web traffic Control access to the network using 802.1x authentication Secure email using the S/MIME protocol Secure instant messaging Approve and authorize applications with Code Signing Protect user data with the Encryption File System (EFS) Implement two-factor authentication with smart cards Securing USB storage devices
