Topology Objectives Configure multi-area OSPFv3 for IPv4 AF. Configure multi-area OSPFv3 for IPv6 AF. Verify multi-area behavior. Configure stub and totally stubby areas for both IPv4 and IPv6 AFs. Background In this lab, you will configure the network with multi-area OSPFv3 routing using the address family feature for …
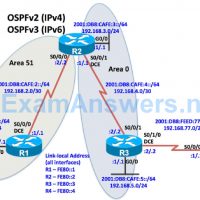
Topology Objectives Configure multi-area OSPFv2 for IPv4. Configure multi-area OSPFv3 for IPv6 Verify multi-area behavior. Configure stub and totally stubby areas for OSPFv2. Configure stub and totally stubby areas for OSPFv3. Background In this lab, you will configure the network with multi-area OSPFv2 routing for IPv4 and multi-area …
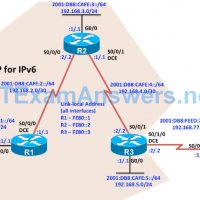
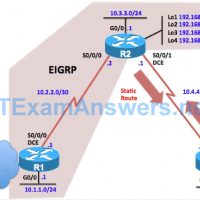
Topology Objectives Configure Named EIGRP for IPv4 and IPv6. Verify Named EIGRP configuration. Configure and verify passive routes Named EIGRP configuration. Configure and verify default route using Named EIGRP configuration. Background What is known as “classic” EIGRP requires separate EIGRP configuration modes and commands for IPv4 and IPv6. …
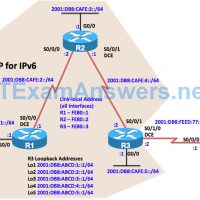
Topology Objectives Configure EIGRP for IPv6. Verify EIGRP for IPv6. Configure and verify passive routes using EIGRP for IPv6. Configure and verify summary routes using EIGRP for IPv6. Configure and verify default route using EIGRP for IPv6. Step 1: Configure the addressing and serial links. a. Using the …
Topology Objectives Configure basic EIGRP. Configure EIGRP stub routing options. Verify EIGRP stub routing options Background To improve network stability and reduce resource utilization on the HQ network you have decided to configure one of the branch routers, R2 as an EIGRP stub router. Note: This lab uses …
1. Refer to the exhibit. A network security specialist issues the command tcpdump to capture events. What does the number 6337 indicate? the number of transactions currently captured the process id of the tcpdump command the port that tcpdump is listening to the Snort signature id that tcpdump …
CCNA Cybersecurity Operations (Version 1.1) – CyberOps Practice Final Exam 1. A person coming to a cafe for the first time wants to gain wireless access to the Internet using a laptop. What is the first step the wireless client will do in order to communicate over the …
1. In the NIST incident response process life cycle, which type of attack vector involves the use of brute force against devices, networks, or services? Media Impersonation Attrition Loss or theft 2. Which NIST incident response life cycle phase includes continuous monitoring by the CSIRT to quickly identify …