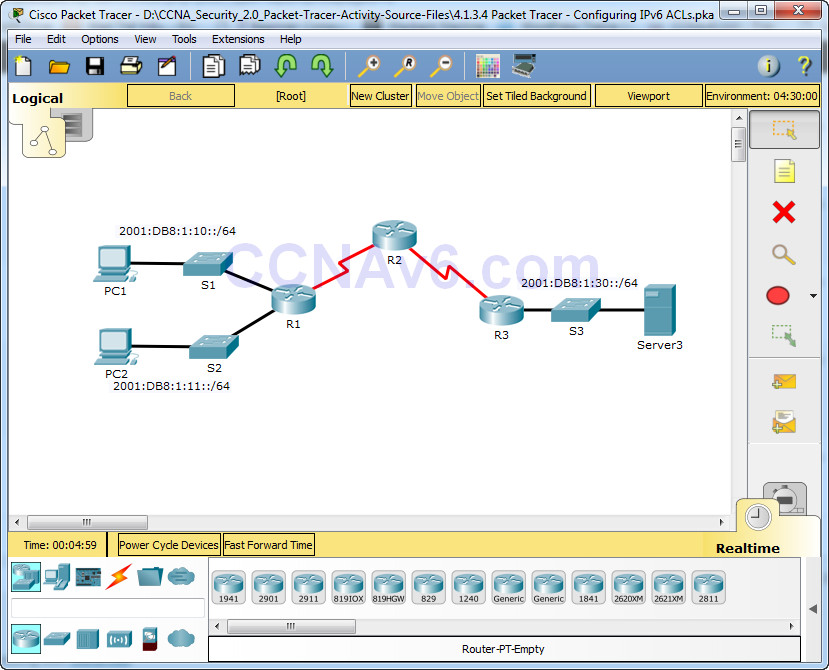
Packet Tracer – Configuring IPv6 ACLs Topology Addressing Table Objectives Part 1: Configure, Apply, and Verify an IPv6 ACL Part 2: Configure, Apply, and Verify a Second IPv6 ACL Part 1: Configure, Apply, and Verify an IPv6 ACL Logs indicate that a computer on the 2001:DB8:1:11::0/64 network …
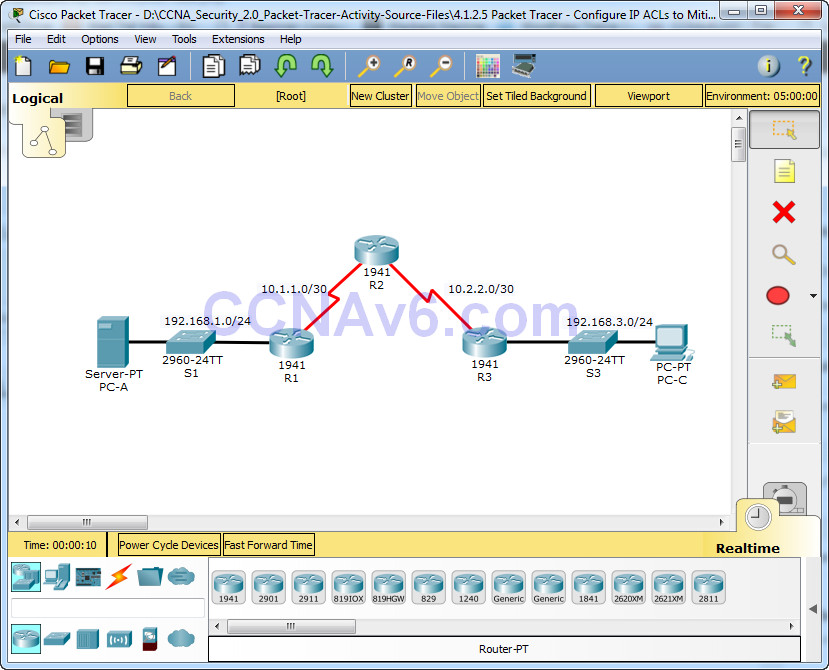
Packet Tracer – Configure IP ACLs to Mitigate Attacks Topology Addressing Table Objectives • Verify connectivity among devices before firewall configuration. • Use ACLs to ensure remote access to the routers is available only from management station PC-C. • Configure ACLs on R1 and R3 to mitigate …
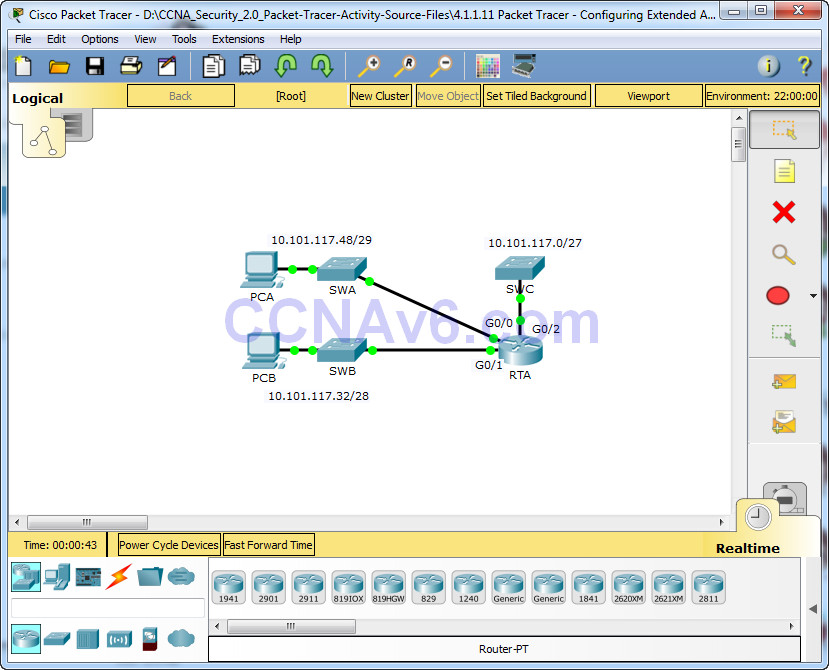
Packet Tracer – Configuring Extended ACLs – Scenario 2 Topology Addressing Table Objectives Part 1: Configure, Apply and Verify an Extended Numbered ACL Part 2: Reflection Questions Background / Scenario In this scenario, devices on one LAN are allowed to remotely access devices in another LAN using …
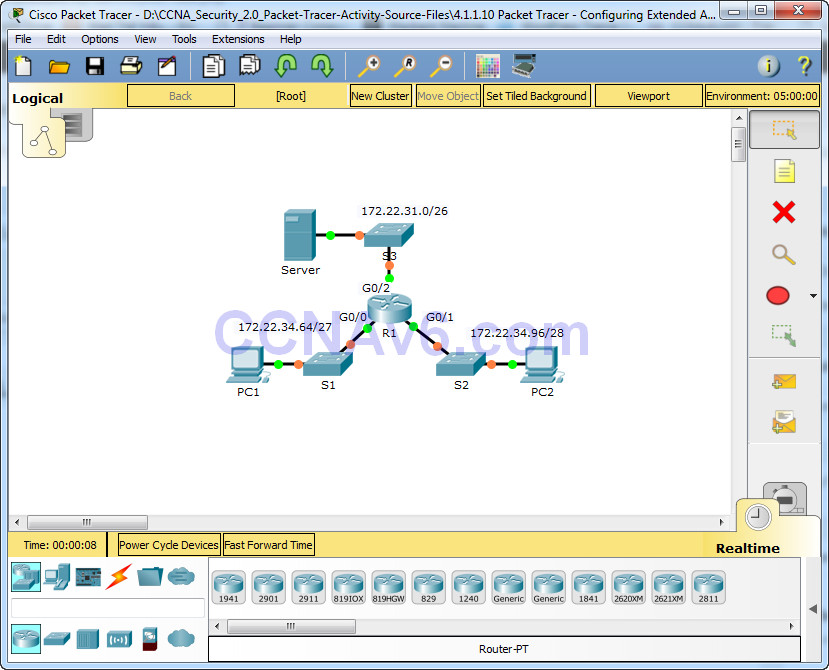
Packet Tracer – Configuring Extended ACLs – Scenario 1 Topology Addressing Table Objectives Part 1: Configure, Apply and Verify an Extended Numbered ACL Part 2: Configure, Apply and Verify an Extended Named ACL Background / Scenario Two employees need access to services provided by the server. PC1 …
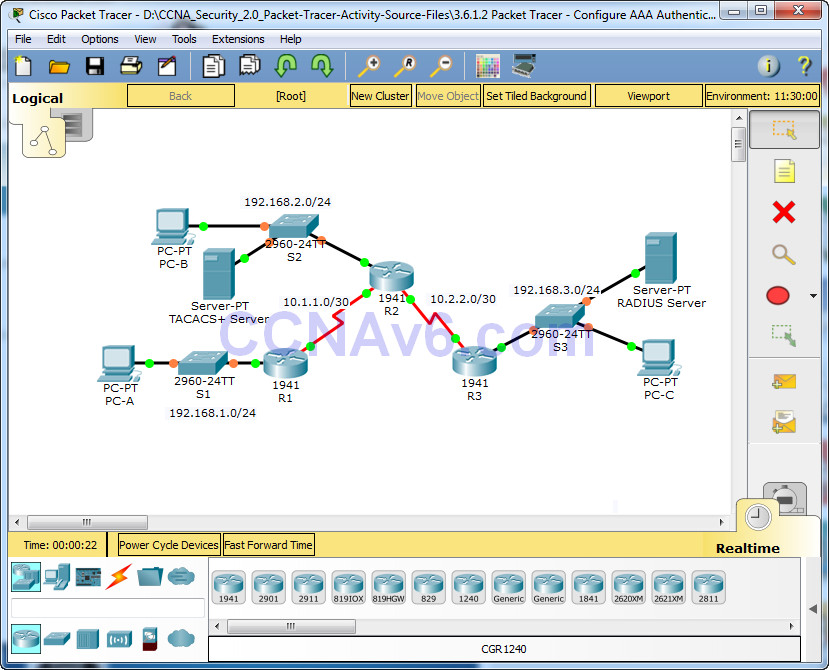
Packet Tracer – Configure AAA Authentication on Cisco Routers Topology Addressing Table Objectives • Configure a local user account on R1 and configure authenticate on the console and vty lines using local AAA. • Verify local AAA authentication from the R1 console and the PC-A client. • …
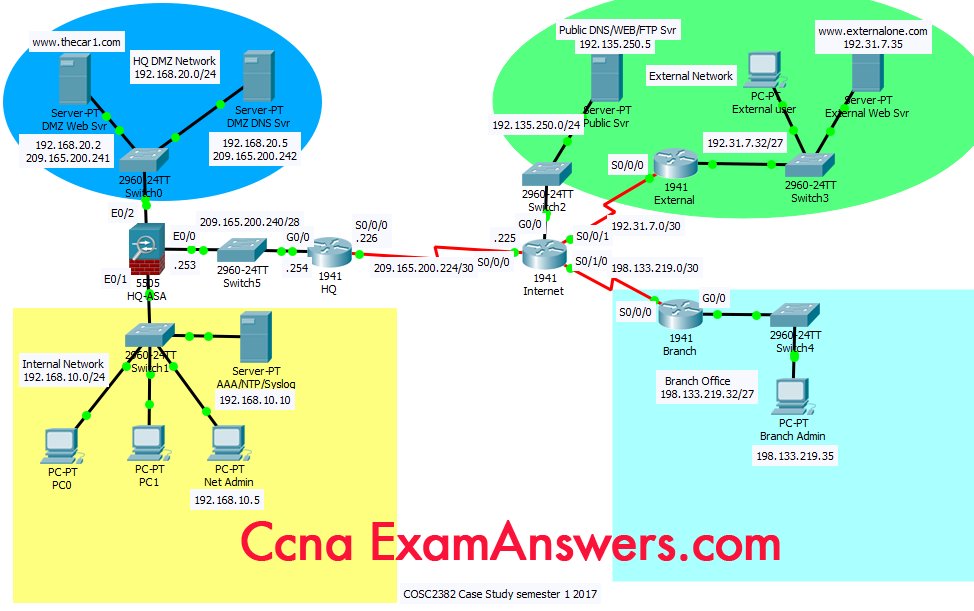
CCNA Security PT Practice SA – Part 2 A few things to keep in mind while completing this activity: Do not use the browser Back button or close or reload any Exam windows during the exam. Do not close Packet Tracer when you are done. It will close …
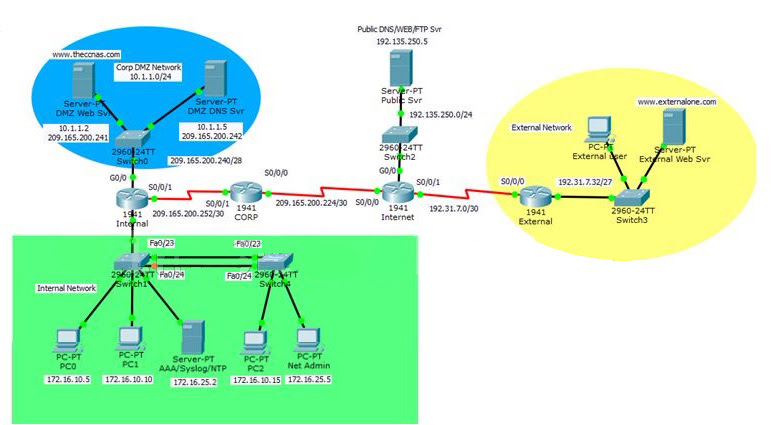
CCNA Security 2.0 PT Practice SA – Part 1 A few things to keep in mind while completing this activity: Do not use the browser Back button or close or reload any exam windows during the exam. Do not close Packet Tracer when you are done. It will close automatically. Click the Submit Assessment button …
1. Which three areas of router security must be maintained to secure an edge router at the network perimeter? (Choose three.) physical security* flash security remote access security operating system security* zone isolation router hardening* 2. What is the purpose of AAA accounting? to prove users are who …
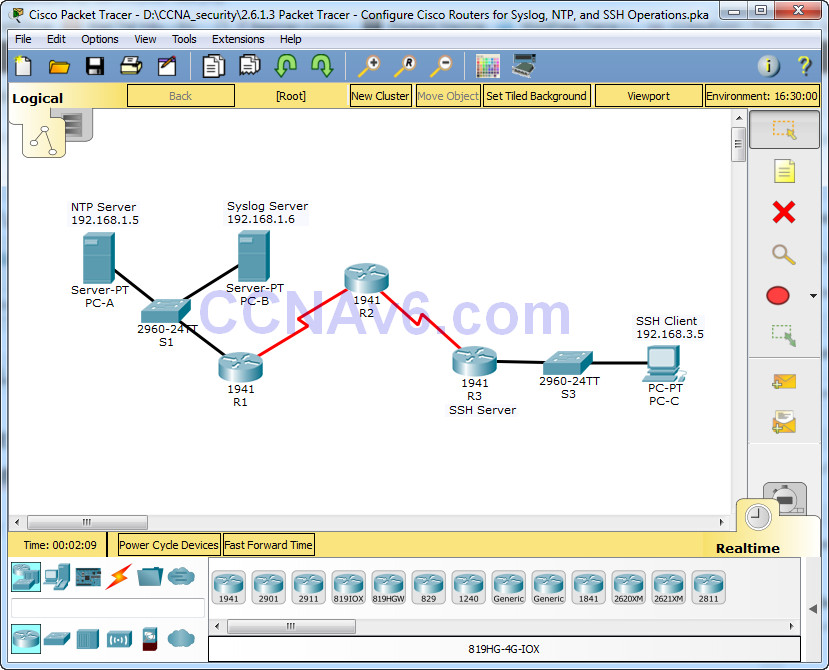
Packet Tracer – Configure Cisco Routers for Syslog, NTP, and SSH Operations Topology Addressing Table Objectives • Configure OSPF MD5 authentication. • Configure NTP. • Configure routers to log messages to the syslog server. • Configure R3 to support SSH connections. Background / Scenario In this activity, …