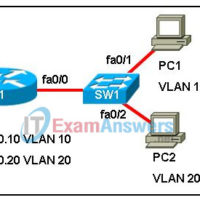
1. Drag the properties associated with interfaces on the left to the appropriate interface type on the right. Answer 2. Refer to the exhibit. PC1 wants to send data to PC2, but does not know the MAC address of PC2. When PC1 sends an ARP request, which interface …
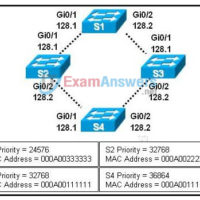
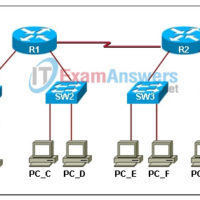
1. Which are two problems associated with redundant switched Ethernet topologies? (Choose two.) broadcast storms routing loops multiple frame copies load balancing incorrect frame addressing unicast frame flooding 2. Refer to the exhibit. The network shown in the exhibit is not running spanning-tree algorithm. What would be the …
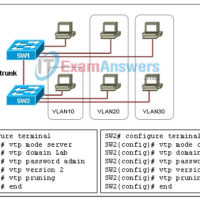
1. How does VTP affect VLAN administration? Port to VLAN assignments for an entire VTP domain can all be done on a single switch. VLANs are only visible on switches that have ports assigned to them. VTP propagates VLAN numbers, but not names, to all switches in a …
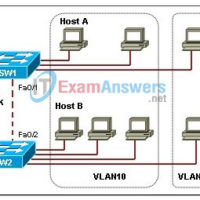
1. Switch1 and Switch2 are both configured with ports in the Marketing, Sales, Production, and Admin VLANs. Each VLAN contains 12 users. How many different subnetworks are needed to address VLANs? 1 2 4 8 12 24 2. What mechanism is used to achieve the separation between different …
1. Refer to the exhibit. What does the error message signify? A parameter is missing. The command was entered in the wrong CLI mode. The data of one of the parameters is incorrect. The command is ambiguous. 2. What is the effect of entering the banner login #Authorized …
1. Which three options correctly associate a layer of the hierarchical design model with its function? (Choose three.) Core — interface for end devices Distribution — traffic control and security policies Access — interface for end devices Distribution — high-speed backbone Core — high-speed backbone Access — implementation …
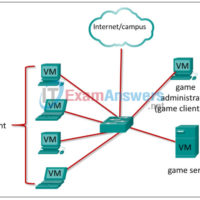
The CyberOps Skills Challenge – Student Guide Reference Topology Note: The topology is provided as an illustration of the logical game architecture. Other topologies can be used as long as the connectivity requirements are met. Purpose This document will support you as you prepare to play the Cyber …
1. Which of the following statements are true regarding routing protocols that use the link-state routing algorithm? (Choose three.) They are known collectively as SPF protocols. They learn routes and send them to directly connected neighbors. They maintain a complex database of the network topology. They are based …
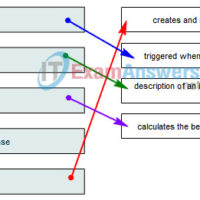
1. Which routing protocol is considered a link-state protocol? RIPv1 RIPv2 EIGRP IS-IS BGP 2. Which of the following mechanisms are used by link-state routing protocols to build and maintain routing tables? (Choose three.) service network advertisements hello packets link-state advertisements routing table broadcasts shortest path first algorithm …
1. What is the purpose of the EIGRP PDM? PDM is the Layer 4 protocol EIGRP uses to share routing information. PDM is the mechanism EIGRP uses to ensure the availability of neighboring routers. PDM is the algorithm engine used by EIGRP to create routing tables. PDM provides …