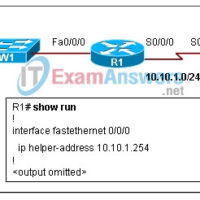
1. Refer to the exhibit. The network administrator enters the command that is shown in the exhibit and then is the show ip route command. The route added by the network administrator is missing from the routing table. What is the reason for this? This static route is …
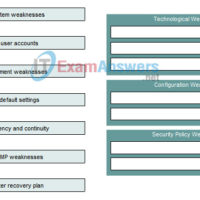
1. Drag the items on the left to the appropriate diagram type on the right. Answer 2. What is one symptom of a physical layer problem? high CPU utilization excessive broadcasts slow STP convergence routing loops 3. A network administrator has received the output “Serial0 is up, line …
1. Which two statements are true about the DHCP server functions? (Choose two.) When a client requests an IP address, the DHCP server searches the binding table for an entry that matches the MAC address for the client. If an entry exists, the corresponding IP address for that …
1. A technician is attempting to explain broadband technology to a customer. Which two descriptions or examples should be used to educate the customer? (Choose two.) includes dialup connections using POTS incompatible with multiplexing uses a wide band of frequencies offers sustained speeds of 128K or more requires …
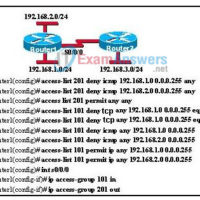
1. Which two statements correctly describe Cisco access control lists? (Choose two.) Extended ACLs are created in interface configuration mode. Extended ACLs filter traffic based on source and destination IP, port number, and protocol. Standard IP ACLs are numbered 1-99, and extended IP ACLs are numbered 100-199. Standard …
1. Drag the term on the left to the associated description on the right. Answer 2. Which two pieces of information can be determined from opening the Cisco SDM homepage of a router? (Choose two.) routing table CDP neighbors snapshot of the router configuration interface status features supported …
1. What is used to identify the path to the next frame-relay switch in a Frame Relay network? CIR DLCI FECN BECN 2. Why are Frame Relay paths referred to as virtual? There are no dedicated circuits to and from the Frame Relay carrier. Frame Relay PVCs are …
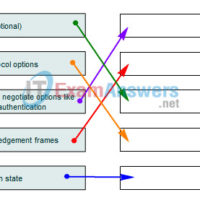
1. Place the PPP establishment steps in the correct order by dragging each step to the appropriate sequence number on the right. 2. Which output from the show interfaces s0/0/0 command indicates that the far end of a point-to-point link has a different encapsulation set than the local …
1. Which three items are considered to be WAN devices? (Choose three.) bridges modems routers Layer 2 switches communication servers repeaters 2. Which layer of the hierarchical network design model is often referred to as the backbone? access distribution network core workgroup WAN 3. Drag the description on …
1. Drag the wireless standard on the left to the appropriate description on the right. 2. Drag the wireless device on the left to the appropriate description on the right. 3. At which layer of the OSI model do wireless access points operate? physical data link network application …