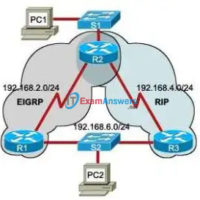
Assessment ERouting Practice Final – CCNA 2 Exploration: Routing Protocols and Concepts (Version 4.0) 1. Refer to exhibit. The network is using the RIPv2 routing protocol. If network 10.0.0.0 goes down, what mechanism will prevent Router1 from advertisting false routing information back to Router2? triggered updates poison reverse …
CCNA 4 Final Exam Answers v5.0 2015 (100%) PDF Download Which two statements about DSL are true? (Choose two.) users are on a shared medium uses RF signal transmission local loop can be up to 3.5 miles (5.5km) physical and data link layers are defined by DOCSIS user …
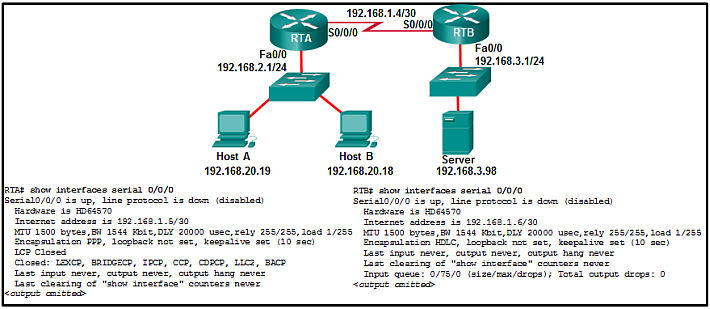
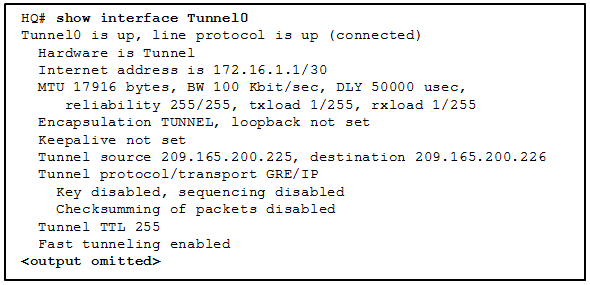
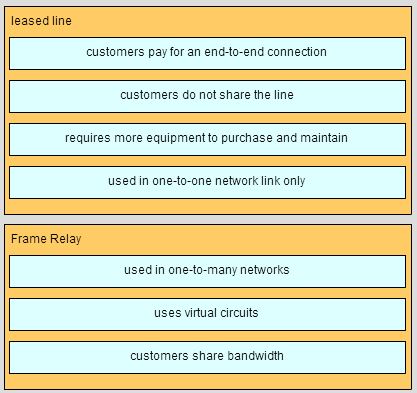
New Version: 1. Which two components of a WAN would more likely be used by an ISP? (Choose two.) demarcation point toll network* CO* CPE DTE 2. What are two advantages of packet switching over circuit switching? (Choose two.) There are fewer delays in the data communications processes. …
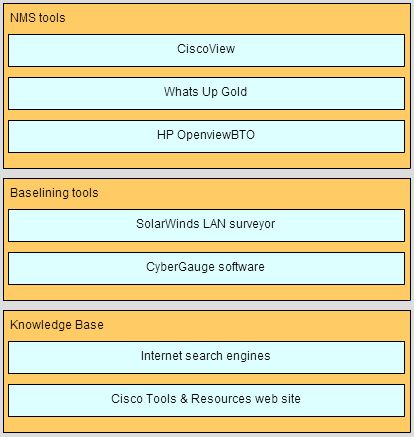
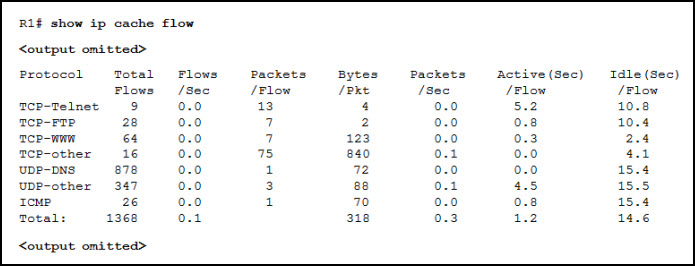
1. When should a network performance baseline be measured? during normal work hours of an organization* immediately after the main network devices restarted after normal work hours to reduce possible interruptions when a denial of service attack to the network is detected and blocked 2. A network engineer …
1. When should a network performance baseline be measured? after normal work hours to reduce possible interruptions during normal work hours of an organization* when a denial of service attack to the network is detected and blocked immediately after the main network devices restarted 2. What is a …
1. What is an example of an M2M connection in the IoT? A user sends an email over the Internet to a friend. Sensors in a warehouse communicate with each other and send data to a server block in the cloud.* Redundant servers communicate with each other to …
1. When QoS is implemented in a converged network, which two factors can be controlled to improve network performance for real-time traffic? (Choose two.) packet addressing delay* jitter* packet routing link speed 2. A network engineer performs a ping test and receives a value that shows the time …
1. What is the behavior of a switch as a result of a successful CAM table attack? The switch will drop all received frames. The switch interfaces will transition to the error-disabled state. The switch will forward all received frames to all other ports. The switch will shut …
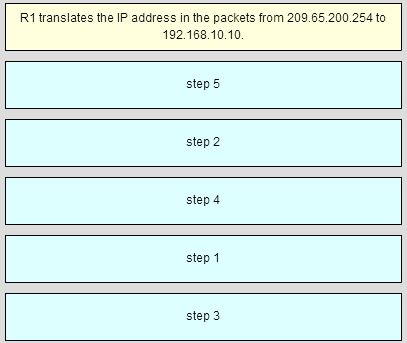
1. Which range represents all the IP addresses that are affected when network 10.120.160.0 with a wildcard mask of 0.0.7.255 is used in an ACE? 10.120.160.0 to 10.120.168.0 10.120.160.0 to 10.127.255.255 10.120.160.0 to 10.120.191.255 10.120.160.0 to 10.120.167.255* 2. What two functions describe uses of an access control list? …
1. Which broadband wireless technology is based on the 802.11 standard? WiMAX UMTS municipal Wi-Fi CDMA 2. What is the approximate distance limitation for providing a satisfactory ADSL service from the central office to a customer? 3.39 miles or 5.46 kilometers 2.11 miles or 3.39 kilometers 11.18 miles …