1. When should a network performance baseline be measured?
- during normal work hours of an organization*
- immediately after the main network devices restarted
- after normal work hours to reduce possible interruptions
- when a denial of service attack to the network is detected and blocked
2. A network engineer issues the show cdp neighbor command on several network devices during the process of network documentation. What is the purpose of performing this command?
- to obtain information about directly connected Cisco devices*
- to check the networks that are advertised by the neighboring routers
- to verify the network addresses that are attached to the network devices
- to check the connectivity of PCs that are connected to the network devices
3. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?
- syslog records and messages
- the network performance baseline*
- debug output and packet captures
- network configuration files
4. In which step of gathering symptoms does the network engineer determine if the problem is at the core, distribution, or access layer of the network?
- Document the symptoms.
- Determine the symptoms.
- Gather information.
- Determine ownership.
- Narrow the scope.*
5. A network technician is troubleshooting an email connection problem. Which question to the end-user will provide clear information to better define the problem?
- Is your email working now?
- How big are the emails you tried to send?
- What kind of equipment are you using to send emails?
- When did you first notice your email problem? *
6. A team of engineers has identified a solution to a significant network problem. The proposed solution is likely to affect critical network infrastructure components. What should the team follow while implementing the solution to avoid interfering with other processes and infrastructure?
- change-control procedures*
- one of the layered troubleshooting approaches
- knowledge base guidelines
- syslog messages and reports
7. After which step in the network troubleshooting process would one of the layered troubleshooting methods be used?
- documenting symptoms
- determining ownership
- narrowing the scope
- gathering symptoms from suspect devices*
8. A user reports that the workstation cannot connect to a networked printer in the office in order to print a report created with word processing software. Which troubleshooting action by the helpdesk technician would follow the divide-and-conquer approach?
- Ask the user to launch the web browser.
- Ask the user to save the working document.
- Ask the user to issue the ipconfig command.*
- Ask the user to unplug and reattach the network cable.
9. A network engineer is troubleshooting a network problem and can successfully ping between two devices. However, Telnet between the same two devices does not work. Which OSI layers should the administrator investigate next?
- all of the layers
- from the network layer to the application layer*
- from the network layer to the physical layer
- only the network layer
10. Which troubleshooting method begins by examining cable connections and wiring issues?
- top-down
- bottom-up*
- substitution
- divide-and-conquer
11. Which number represents the most severe level of syslog logging?
- 0*
- 1
- 7
- 10
- 100
12. A company is setting up a web site with SSL technology to protect the authentication credentials required to access the web site. A network engineer needs to verify that the setup is correct and that the authentication is indeed encrypted. Which tool should be used?
- fault-management tool
- protocol analyzer*
- baselining tool
- cable analyzer
13. Which two specialized troubleshooting tools can monitor the amount of traffic that passes through a switch? (Choose two.)
- TDR
- digital multimeter
- NAM*
- portable network analyzer*
- DTX cable analyzer
14. Refer to the exhibit. Which two statements describe the results of entering these commands? (Choose two.)
- R1 will send system messages of levels 0 (emergencies) to level 4 (warnings) to a server.*
- R1 will not send critical system messages to the server until the command debug all is entered.
- R1 will reset all the warnings to clear the log.
- R1 will output the system messages to the local RAM.
- The syslog server has the IPv4 address 192.168.10.10.*
15. An administrator is troubleshooting an Internet connectivity problem on a router. The output of the show interfaces gigabitethernet 0/0 command reveals higher than normal framing errors on the interface that connects to the Internet. At what layer of the OSI model is the problem likely occurring?
- Layer 1
- Layer 2*
- Layer 3
- Layer 4
- Layer 7
16. Users report that the new web site http://www.company1.biz cannot be accessed. The helpdesk technician checks and verifies that the web site can be accessed with http://www.company1.biz:90. Which layer in the TCP/IP model is involved in troubleshooting this issue?
- application
- transport*
- internet
- network access
17. A user reports that after an OS patch of the networking subsystem has been applied to a workstation, it performs very slowly when connecting to network resources. A network technician tests the link with a cable analyzer and notices that the workstation sends an excessive number of frames smaller than 64 bytes and also other meaningless frames. What is the possible cause of the problem?
- cabling faults
- corrupted NIC driver*
- Ethernet signal attenuation
- corrupted application installation
18. A network administrator is configuring SSH on a router. When verifying the configuration, the administrator notices that the SSH connection requests fail, but the Telnet connection requests from the same workstation are successful. Which two parts of the router configuration should be checked to try to locate the problem? (Choose two.)
- The ip access-class command is missing.
- The password is misconfigured on the console line.
- The transport input command is incorrect on the vty lines.*
- A standard ACL is possibly blocking the workstation from access to the router.
- An extended ACL that is referencing the port argument for SSH is misconfigured.*
19. A user in a large office calls technical support to complain that a PC has suddenly lost connectivity to the network. The technician asks the caller to talk to nearby users to see if other machines are affected. The caller reports that several immediate neighbors in the same department have a similar problem and that they cannot ping each other. Those who are seated in other departments have connectivity. What should the technician check as the first step in troubleshooting the issue?
- the power outlet to the PC that is used by the caller
- the trunks between switches in the wiring closet
- the status of the departmental workgroup switch in the wiring closet*
- the cable that connects the PC of the caller to the network jack
- the cable connection between a PC and a network outlet that is used by a neighbor
20. A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Choose three.)
- arp -a
- ipconfig*
- nslookup*
- ping*
- telnet
- tracert
- netsh interface ipv6 show neighbor
21. After cables were reconnected to a switch in a wiring closet, several PCs that had been previously configured manually can no longer access resources outside the local network. The PC configurations were not altered in the process and resources on the local network can still be accessed. What is a possible cause of the problem?
- The cabling to the PCs is faulty.
- The PCs are no longer on the correct VLAN.*
- The DHCP server has been misconfigured.
- The DNS configuration on the PCs is incorrect.
22. Refer to exhibit. A network engineer is troubleshooting a WAN connectivity problem. A ping to a remote router is successful and an attempt to telnet to the same router displays the exhibited output. What does the output verify?

- A Telnet password has not been configured on the remote router.
- The web server service is password protected.
- The transport layer is connecting successfully.*
- The remote router IPv6 address is incorrect.
23. Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
- There is connectivity between this device and the device at 192.168.100.1.*
- The connectivity between these two hosts allows for videoconferencing calls.
- There are 4 hops between this device and the device at 192.168.100.1.*
- The average transmission time between the two hosts is 2 miliseconds.
- This host does not have a default gateway configured.
24. Fill in the blank.
Use the ARP cache to verify IPv4 address to Layer 2 Ethernet address mappings on a host computer.
25. Place the options in the following order:
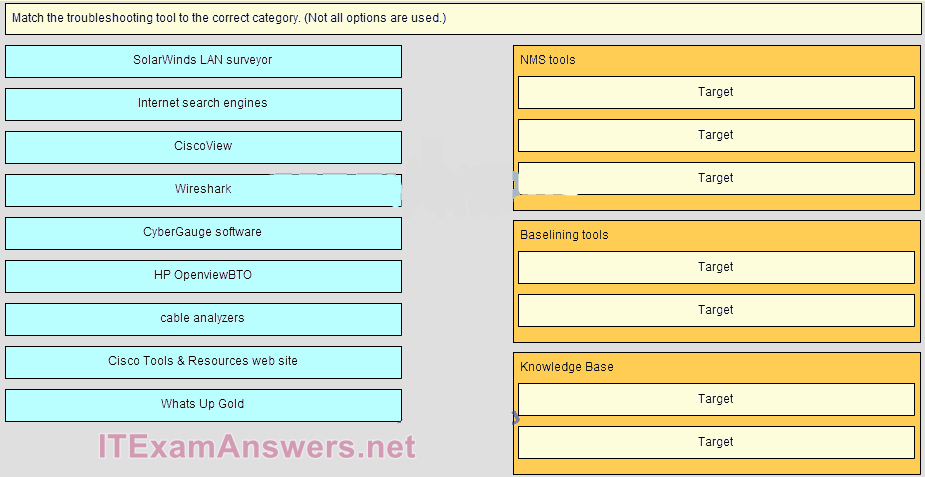
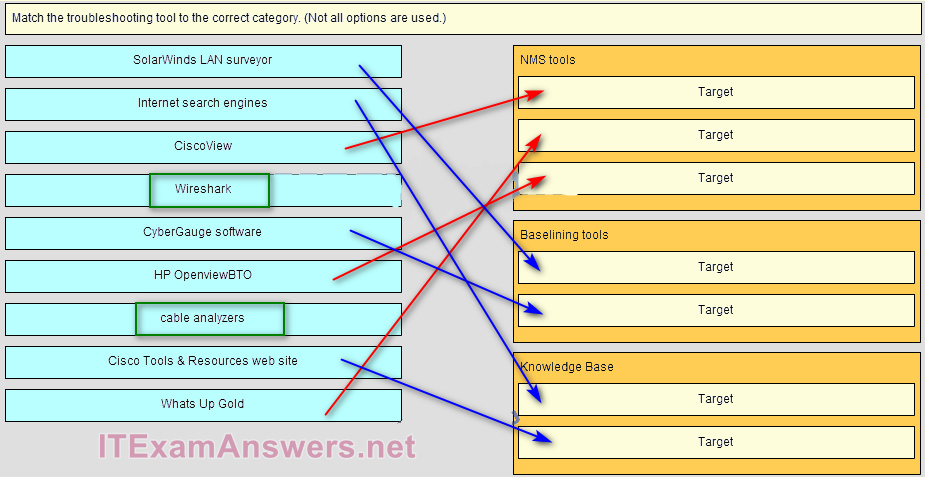 [+] CiscoView
[+] CiscoView
[+] What’s Up Gold
[+] HP OpenviewBTO
[#] SolarWinds LAN surveyor
[#] CyberGauge software
[*] Internet search engines
[*] Cisco Tools & Resources web site
[+] Order does not matter within this group.
[#] Order does not matter within this group.
[*] Order does not matter within this group.
26. Which statement describes the physical topology for a LAN?
- It shows the order in which hosts access the network.
- It describes whether the LAN is a broadcast or token-passing network.
- It defines how hosts and network devices connect to the LAN.*
- It depicts the addressing scheme that is employed in the LAN.
27. What is a purpose of establishing a network baseline?
- It provides a statistical average for network performance.
- It checks the security configuration of network devices.
- It manages the performance of network devices.
- It creates a point of reference for future network evaluations.*
28. The newly configured ASBR that connects a company to the Internet has a default route configured and has the default-information originate command entered. Devices connected through this router can access the Internet. The problem is that no other OSPF routers have a default route in the routing table and no other users throughout the organization can access the Internet. What could be the problem?
- The ASBR should use the exit_interface argument instead of next-hop on the default route.
- The ASBR does not have OSPF configured.
- The ASBR does not have an OSPF neighbor.*
- The other routers are not configured to accept LSA type 4s.
29. An internal corporate server can be accessed by internal PCs, but not by external Internet users that should have access. What could be the issue?
- The switch port to which the server connects has an incorrect VLAN configured.
- Static NAT has not been configured properly or at all.*
- The default gateway router for the server does not have a default route.
- The server does not have a private IP address assigned.
30. A networked PC is having trouble accessing the Internet, but can print to a local printer and ping other computers in the area. Other computers on the same network are not having any issues. What is the problem?
- The default gateway router does not have a default route.
- The switch port to which the PC connects has an incorrect VLAN configured.
- The PC has a missing or incorrect default gateway.*
- The link between the switch to which the PC connects and the default gateway router is down.
31. Which type of tool would an administrator use to capture packets that are going to and from a particular device?
- baselining tool
- protocol analyzer*
- knowledge base
- NMS tool
Download PDF File below:

CCNA 4 (4th semester) has no chapter 9. Did they changed it for students that they registered after 2019 began ?
No, Chapter 9 only applies to the old version 5, ccna4 v6 don’t have chapter 9, you don’t need to study this chapter :)