Command
SSH
Use
Allows you to securely connect to a remote device. Unlike telnet, all packets are encrypted. As a result, SSH is a much more secure method of connecting to a device.
Syntax
Router#ssh -l <user> <ip address or DNS name>
Optional Switches
-c Select encryption algorithm
-l Log in using this user name *Requried
-m Select HMAC algorithm
-o Specify options
-p Connect to this port
-v Specify SSH Protocol Version
Note: There are more options for SSH but they are considered above and beyond the CCNA level.
Example
This example demonstrates how to use SSH on one of the routers. Before enabling SSH, however, there a few requirements that must be completed:
- You must set a domain-name on the Router with the ip domain-name <name> command
- You have to generate an encryption key. This is done with the crypto key generate rsa command
- Under line vty <line number>, you will need to enable SSH with transport input ssh
- Under line vty <line number>, you will also need to enable username authentication with local local
- Finally, you need to create a user account on the router with username <word> password <word>
R1(config)#crypto key generate rsa % Please define a domain-name first. ^ % Invalid input detected at ‘^’ marker. R1(config)#ip domain-name howtonetwork.net R1(config)#crypto key generate rsa The name for the keys will be: R1.howtonetwork.net Choose the size of the key modulus in the range of 360 to 2048 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. How many bits in the modulus [512]: % Generating 512 bit RSA keys, keys will be non-exportable…[OK] R1(config)# *Mar 1 00:55:02.791: %SSH-5-ENABLED: SSH 1.99 has been enabled R1(config)# R1(config)#line vty 0 4 R1(config-line)#transport input ssh R1(config-line)#login local R1(config-line)#exit R1(config)#username R1 password cisco
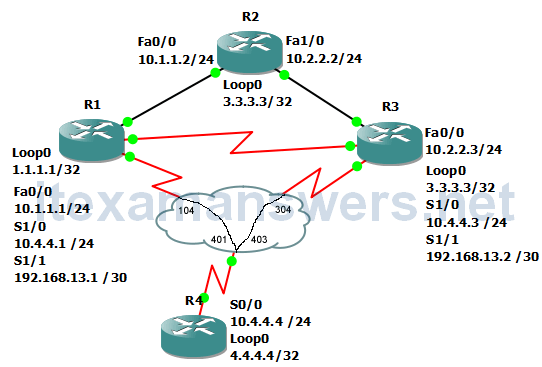
After configuration is complete, we use SSH to connect to R1 via R2.
R2#ssh -l R1 10.1.1.1 Password: ***** R1>
