Time limit: 0
Quiz-summary
0 of 34 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
Information
CCNA Cyber Ops (Version 1.1) – Chapter 8 Test Online Full
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 34 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- Answered
- Review
-
Question 1 of 34
1. Question
1 pointsA web server administrator is configuring access settings to require users to authenticate first before accessing certain web pages. Which requirement of information security is addressed through the configuration?Correct
Incorrect
-
Question 2 of 34
2. Question
1 pointsWhat component of a security policy explicitly defines the type of traffic allowed on a network and what users are allowed and not allowed to do?Correct
Incorrect
-
Question 3 of 34
3. Question
1 pointsWhat is the principle of least privilege access control model?Correct
Incorrect
-
Question 4 of 34
4. Question
1 pointsWhich statement describes a difference between RADIUS and TACACS+?Correct
Incorrect
-
Question 5 of 34
5. Question
1 pointsWhat is the purpose of mobile device management (MDM) software?Correct
Incorrect
-
Question 6 of 34
6. Question
1 pointsWhat service determines which resources a user can access along with the operations that a user can perform?Correct
Incorrect
-
Question 7 of 34
7. Question
1 pointsA company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin group. Which component is addressed in the AAA network service framework?Correct
Incorrect
-
Question 8 of 34
8. Question
1 pointsIn threat intelligence communications, what set of specifications is for exchanging cyberthreat information between organizations?Correct
Incorrect
-
Question 9 of 34
9. Question
1 pointsWhat three items are components of the CIA triad? (Choose three.)Correct
Incorrect
-
Question 10 of 34
10. Question
1 pointsA company is experiencing overwhelming visits to a main web server. The IT department is developing a plan to add a couple more web servers for load balancing and redundancy. Which requirement of information security is addressed by implementing the plan?Correct
Incorrect
-
Question 11 of 34
11. Question
1 pointsWhich AAA component can be established using token cards?Correct
Incorrect
-
Question 12 of 34
12. Question
1 pointsWhich method is used to make data unreadable to unauthorized users?Correct
Incorrect
-
Question 13 of 34
13. Question
1 pointsWhich two areas must an IT security person understand in order to identify vulnerabilities on a network? (Choose two.)Correct
Incorrect
-
Question 14 of 34
14. Question
1 pointsWhich three services are provided by the AAA framework? (Choose three.)Correct
Incorrect
-
Question 15 of 34
15. Question
1 pointsHow does BYOD change the way in which businesses implement networks?Correct
Incorrect
-
Question 16 of 34
16. Question
1 pointsWhich technology provides the framework to enable scalable access security?Correct
Incorrect
-
Question 17 of 34
17. Question
1 pointsWhich device is usually the first line of defense in a layered defense-in-depth approach?Correct
Incorrect
-
Question 18 of 34
18. Question
1 pointsWhich type of access control applies the strictest access control and is commonly used in military or mission critical applications?Correct
Incorrect
-
Question 19 of 34
19. Question
1 pointsIn a defense-in-depth approach, which three options must be identified to effectively defend a network against attacks? (Choose three.)Correct
Incorrect
-
Question 20 of 34
20. Question
1 pointsWhich section of a security policy is used to specify that only authorized individuals should have access to enterprise data?Correct
Incorrect
-
Question 21 of 34
21. Question
1 pointsWith the evolution of borderless networks, which vegetable is now used to describe a defense-in-depth approach?Correct
Incorrect
-
Question 22 of 34
22. Question
1 pointsWhat is a characteristic of a layered defense-in-depth security approach?Correct
Incorrect
-
Question 23 of 34
23. Question
1 pointsPasswords, passphrases, and PINs are examples of which security term?Correct
Incorrect
-
Question 24 of 34
24. Question
1 pointsWhat is privilege escalation?Correct
Incorrect
-
Question 25 of 34
25. Question
1 pointsWhat are two characteristics of the RADIUS protocol? (Choose two.)Correct
Incorrect
-
Question 26 of 34
26. Question
1 pointsWhich component of AAA is used to determine which resources a user can access and which operations the user is allowed to perform?Correct
Incorrect
-
Question 27 of 34
27. Question
1 pointsWhich type of business policy establishes the rules of conduct and the responsibilities of employees and employers?Correct
Incorrect
-
Question 28 of 34
28. Question
1 pointsWhich component of AAA allows an administrator to track individuals who access network resources and any changes that are made to those resources?Correct
Incorrect
-
Question 29 of 34
29. Question
1 pointsWhich of the following offers a free service called Automated Indicator Sharing that enables the real-time exchange of cyberthreat indicators?Correct
Incorrect
-
Question 30 of 34
30. Question
1 pointsThe security policy of an organization allows employees to connect to the office intranet from their homes. Which type of security policy is this?Correct
Incorrect
-
Question 31 of 34
31. Question
1 pointsDuring the AAA process, when will authorization be implemented?Correct
Incorrect
-
Question 32 of 34
32. Question
1 pointsWhat device is usually the first line of defense in a layered defense-in-depth approach?Correct
Incorrect
-
Question 33 of 34
33. Question
1 pointsWhat component of a security policy explicitly defines the type of traffic allowed on a network and what users are allowed and not allowed to do?Correct
Incorrect
-
Question 34 of 34
34. Question
1 pointsMatch the type of business policy to the description.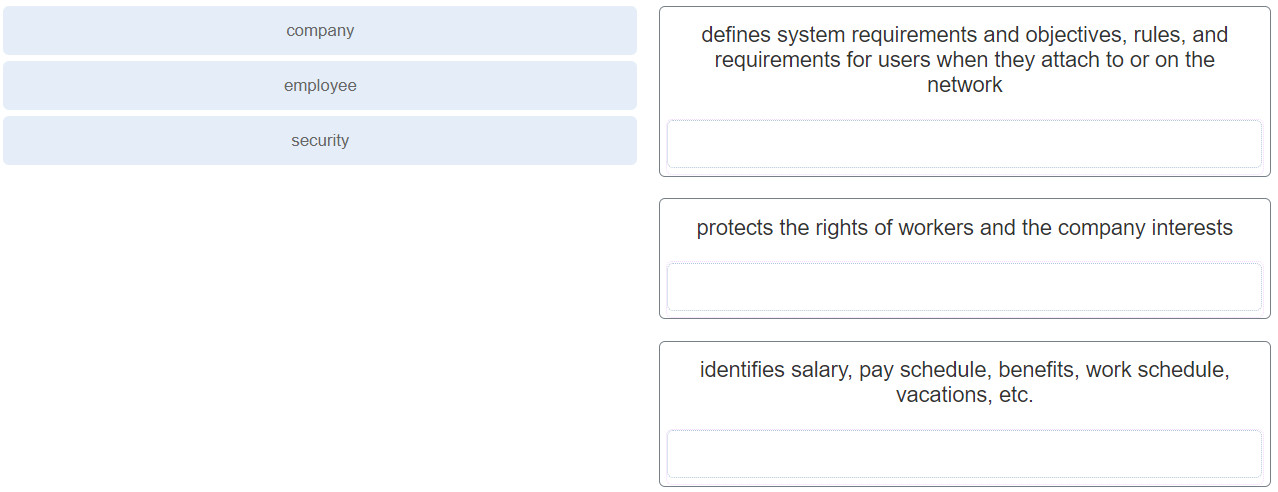 Correct
Correct
Incorrect
