Time limit: 0
Quiz-summary
0 of 62 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
Information
CCNA Cyber Ops (Version 1.1) – FINAL Test Online Full
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 62 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- Answered
- Review
-
Question 1 of 62
1. Question
1 pointsRefer to the exhibit. A network security specialist issues the command tcpdump to capture events. What does the number 6337 indicate?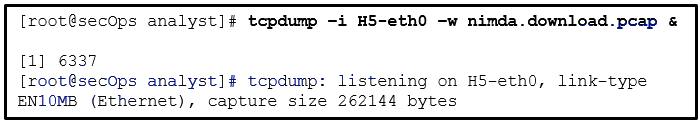 Correct
Correct
Incorrect
Hint
After the tcpdump command is issued, the device displays the message, [1] 6337. The message indicates that the process with PID 6337was sent to the background. -
Question 2 of 62
2. Question
1 pointsHow do cybercriminals make use of a malicious iFrame?Correct
Incorrect
Hint
An inline frame or iFrame is an HTML element that allows the browser to load a different web page from another source. -
Question 3 of 62
3. Question
1 pointsWhat is a difference between symmetric and asymmetric encryption algorithms?Correct
Incorrect
Hint
Asymmetric algorithms can use very long key lengths in order to avoid being hacked. This results in the use of significantly increased resources and time compared to symmetric algorithms. -
Question 4 of 62
4. Question
1 pointsWhat is a network tap?Correct
Incorrect
Hint
A network tap is used to capture traffic for monitoring the network. The tap is typically a passive splitting device implemented inline on the network and forwards all traffic, including physical layer errors, to an analysis device. -
Question 5 of 62
5. Question
1 pointsRefer to the exhibit. A network administrator is viewing some output on the Netflow collector. What can be determined from the output of the traffic flow shown?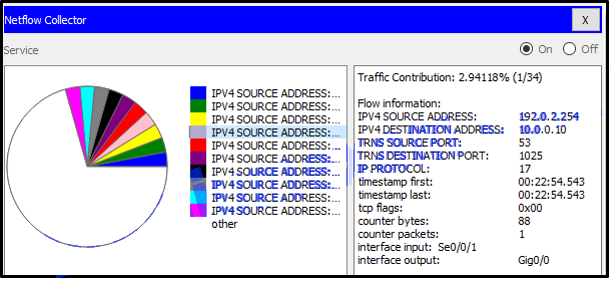 Correct
Correct
Incorrect
Hint
The traffic flow shown has a source port of 53 and a destination port of 1025. Port 53 is used for DNS and because the source port is 53, this traffic is responding to a client machine from a DNS server. The IP PROTOCOL is 17 and specifies that UDP is being used and the TCP flag is set to 0. -
Question 6 of 62
6. Question
1 pointsAccording to NIST, which step in the digital forensics process involves preparing and presenting information that resulted from scrutinizing data?Correct
Incorrect
Hint
NIST describes the digital forensics process as involving the following four steps:- Collection – the identification of potential sources of forensic data and acquisition, handling, and storage of that data
- Examination – assessing and extracting relevant information from the collected data. This may involve decompression or decryption of the data
- Analysis – drawing conclusions from the data. Salient features, such as people, places, times, events, and so on should be documented
- Reporting – preparing and presenting information that resulted from the analysis. Reporting should be impartial and alternative explanations should be offered if appropriate
-
Question 7 of 62
7. Question
1 pointsA technician notices that an application is not responding to commands and that the computer seems to respond slowly when applications are opened. What is the best administrative tool to force the release of system resources from the unresponsive application?Correct
Incorrect
Hint
Use the Task Manager Performance tab to see a visual representation of CPU and RAM utilization. This is helpful in determining if more memory is needed. Use the Applications tab to halt an application that is not responding. -
Question 8 of 62
8. Question
1 pointsWhich three technologies should be included in a security information and event management system in a SOC? (Choose three.)Correct
Incorrect
Hint
Technologies in a SOC should include the following:- Event collection, correlation, and analysis
- Security monitoring
- Security control
- Log management
- Vulnerability assessment
- Vulnerability tracking
- Threat intelligence
- Firewall appliances, VPNs, and IPS are security devices deployed in the network infrastructure.
-
Question 9 of 62
9. Question
1 pointsIn which situation is an asymmetric key algorithm used?Correct
Incorrect
Hint
The SSH protocol uses an asymmetric key algorithm to authenticate users and encrypt data transmitted. The SSH server generates a pair of public/private keys for the connections. Encrypting files before saving them to a storage device uses a symmetric key algorithm because the same key is used to encrypt and decrypt files. The router authentication with CHAP uses a symmetric key algorithm. The key is pre-configured by the network administrator. A VPN may use both an asymmetric key and a symmetric encryption algorithm. For example in an IPSec VPN implementation, the data transmission uses a shared secret (generated with an asymmetric key algorithm) with a symmetric encryption algorithm used for performance. -
Question 10 of 62
10. Question
1 pointsWhich two statements are characteristics of a virus? (Choose two.)Correct
Incorrect
Hint
The type of end user interaction required to launch a virus is typically opening an application, opening a web page, or powering on the computer. Once activated, a virus may infect other files located on the computer or other computers on the same network. -
Question 11 of 62
11. Question
1 pointsWhich Windows Event Viewer log includes events regarding the operation of drivers, processes, and hardware?Correct
Incorrect
Hint
By default Windows keeps four types of host logs:- Application logs – events logged by various applications
- System logs – events about the operation of drivers, processes, and hardware
- Setup logs – information about the installation of software, including Windows updates
- Security logs – events related to security, such as logon attempts and operations related to file or object management and access
-
Question 12 of 62
12. Question
1 pointsWhat is the responsibility of the human resources department when handling a security incident?Correct
Incorrect
Hint
The human resources department may be called upon to perform disciplinary measures if an incident is caused by an employee. -
Question 13 of 62
13. Question
1 pointsWhich two net commands are associated with network resource sharing? (Choose two.)Correct
Incorrect
-
Question 14 of 62
14. Question
1 pointsnetwork security professional has applied for a Tier 2 position in a SOC. What is a typical job function that would be assigned to a new employee?Correct
Incorrect
Hint
In a typical SOC, the job of a Tier 2 incident responder involves deep investigation of security incidents. -
Question 15 of 62
15. Question
1 pointsWhat are three responsibilities of the transport layer? (Choose three.)Correct
Incorrect
-
Question 16 of 62
16. Question
1 pointsWhich technique is necessary to ensure a private transfer of data using a VPN?Correct
Incorrect
Hint
Confidential and secure transfers of data with VPNs require data encryption. -
Question 17 of 62
17. Question
1 pointsAs described by the SANS Institute, which attack surface includes the use of social engineering?Correct
Incorrect
Hint
The SANS Institute describes three components of the attack surface:- Network Attack Surface – exploitation of vulnerabilities in networks
- Software Attack Surface – exploitation of vulnerabilities in web, cloud, or host-based software applications
- Human Attack Surface – exploitation of weaknesses in user behavior
-
Question 18 of 62
18. Question
1 pointsRefer to the exhibit. A network administrator is showing a junior network engineer some output on the server. Which service would have to be enabled on the server to receive such output?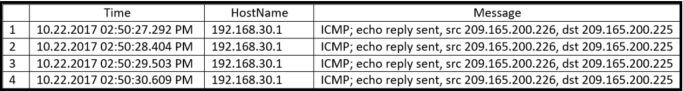 Correct
Correct
Incorrect
Hint
The Simple Network Management Protocol is used by network devices to send and log messages to a syslog server in order to monitor traffic and network device events. The syslog service must be enabled on the server or a syslog server application must be installed in order to receive such traffic. -
Question 19 of 62
19. Question
1 pointsWhich scenario is probably the result of activities by a group of hacktivists?Correct
Incorrect
Hint
Hacktivists are typically hackers who protest against a variety of political and social ideas. Hacktivists publicly protest against organizations or governments by posting articles and leaking sensitive information. Accessing school database and changing grades is probably made by a few script kiddies. Offers from someone to restore data for a hefty fee is a ransomware attack. Attacking the major power grid is typically conducted by a government. -
Question 20 of 62
20. Question
1 pointsWhat are two advantages of the NTFS file system compared with FAT32? (Choose two.)Correct
Incorrect
Hint
The file system has no control over the speed of access or formatting of drives, and the ease of configuration is not file system-dependent. -
Question 21 of 62
21. Question
1 pointsWhat two assurances does digital signing provide about code that is downloaded from the Internet? (Choose two.)Correct
Incorrect
Hint
Digitally signing code provides several assurances about the code:- The code is authentic and is actually sourced by the publisher.
- The code has not been modified since it left the software publisher.
- The publisher undeniably published the code. This provides nonrepudiation of the act of publishing.
-
Question 22 of 62
22. Question
1 pointsWhich statement identifies an important difference between the TACACS+ and RADIUS protocols?Correct
Incorrect
Hint
One key difference between TACACS+ and RADIUS protocols is that TACACS+ provides flexibility by separating authentication and authorization processes. RADIUS, on the other hand, combines authentication and authorization as one process. -
Question 23 of 62
23. Question
1 pointsWhat is a function of SNMP?Correct
Incorrect
Hint
SNMP is an application layer protocol that allows administrators to manage devices on the network by providing a messaging format for communication between network device managers and agents. -
Question 24 of 62
24. Question
1 pointsWhat commonly motivates cybercriminals to attack networks as compared to hactivists or state-sponsored hackers?Correct
Incorrect
Hint
Cybercriminals are commonly motivated by money. Hackers are known to hack for status. Cyberterrorists are motivated to commit cybercrimes for religious or political reasons. -
Question 25 of 62
25. Question
1 pointsIn a networking class, the instructor tells the students to ping the other computers in the classroom from the command prompt. Why do all pings in the class fail?Correct
Incorrect
Hint
Unsuccessful pings usually indicate a network problem which eliminates the virus option. In this case computers in the same classroom would also be on the same network. Port 25 is used used by the email SMTP protocol, not by ping. -
Question 26 of 62
26. Question
1 pointsWhich method can be used to harden a device?Correct
Incorrect
-
Question 27 of 62
27. Question
1 pointsBecause of implemented security controls, a user can only access a server with FTP. Which AAA component accomplishes this?Correct
Incorrect
Hint
One of the components in AAA is authorization. After a user is authenticated through AAA, authorization services determine which resources the user can access and which operations the user is allowed to perform. -
Question 28 of 62
28. Question
1 pointsWhich protocol translates a website name such as www.cisco.com into a network address?Correct
Incorrect
Hint
Domain Name Service translates names into numerical addresses, and associates the two. DHCP provides IP addresses dynamically to pools of devices. HTTP delivers web pages to users. FTP manages file transfers. -
Question 29 of 62
29. Question
1 pointsHow might DNS be used by a threat actor to create mayhem?Correct
Incorrect
Hint
Malware could be used by a threat actor to collect stolen encoded data, decode it, and then gain access to corporate data such as a username/password database. -
Question 30 of 62
30. Question
1 pointsRefer to the exhibit. A cybersecurity analyst is viewing captured packets forwarded on switch S1. Which device has the MAC address d8:cb:8a:5c:d5:8a?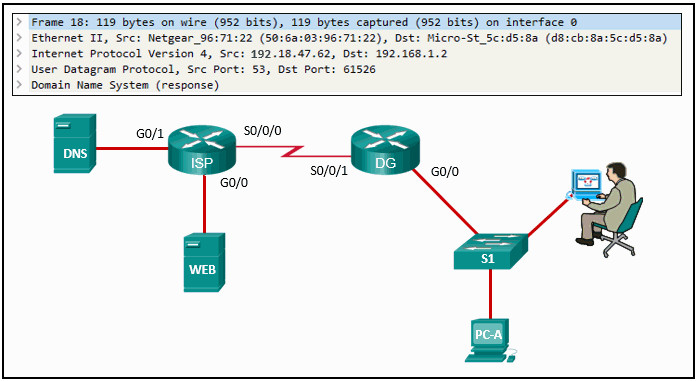 Correct
Correct
Incorrect
Hint
The Wireshark capture is a DNS response from the DNS server to PC-A. Because the packet was captured on the LAN that the PC is on, router DG would have encapsulated the response packet from the ISP router into an Ethernet frame addressed to PC-A and forwarded the frame with the MAC address of PC-A as the destination. -
Question 31 of 62
31. Question
1 pointsWhich statement describes the policy-based intrusion detection approach?Correct
Incorrect
Hint
With the anomaly-based intrusion detection approach, a set of rules or policies are applied to a host. Violation of these policies is interpreted to be the result of a potential intrusion. -
Question 32 of 62
32. Question
1 pointsWhy would threat actors prefer to use a zero-day attack in the Cyber Kill Chain weaponization phase?Correct
Incorrect
Hint
When a threat actor prepares a weapon for an attack, the threat actor chooses an automated tool (weaponizer) that can be deployed through discovered vulnerabilities. Malware that will carry desired attacks is then built into the tool as the payload. The weapon (tool plus malware payload) will be delivered to the target system. By using a zero-day weaponizer, the threat actor hopes that the weapon will not be detected because it is unknown to security professionals and detection methods are not yet developed. -
Question 33 of 62
33. Question
1 pointsWhich two services are provided by the NetFlow tool? (Choose two.)Correct
Incorrect
Hint
NetFlow efficiently provides an important set of services for IP applications including network traffic accounting, usage-based network billing, network planning, security, denial of service monitoring capabilities, and network monitoring. -
Question 34 of 62
34. Question
1 pointsWhy would a network administrator choose Linux as an operating system in the Security Operations Center (SOC)?Correct
Incorrect
-
Question 35 of 62
35. Question
1 pointsWhich two statements describe access attacks? (Choose two.)Correct
Incorrect
-
Question 36 of 62
36. Question
1 pointsWhich type of data would be considered an example of volatile data?Correct
Incorrect
Hint
Volatile data is data stored in memory such as registers, cache, and RAM, or it is data that exists in transit. Volatile memory is lost when the computer loses power. -
Question 37 of 62
37. Question
1 pointsWhich Linux command could be used to discover the process ID (PID) for a specific process before using the kill command?Correct
Incorrect
-
Question 38 of 62
38. Question
1 pointsWhich two characteristics describe a worm? (Choose two.)Correct
Incorrect
-
Question 39 of 62
39. Question
1 pointsWhich two roles are typically performed by a wireless router that is used in a home or small business? (Choose two.)Correct
Incorrect
-
Question 40 of 62
40. Question
1 pointsRefer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?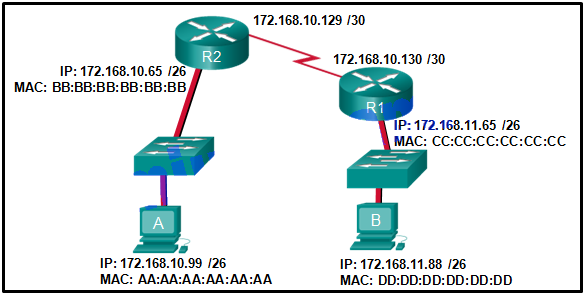 Correct
Correct
Incorrect
-
Question 41 of 62
41. Question
1 pointsA threat actor has gained administrative access to a system and achieved the goal of controlling the system for a future DDoS attack by establishing a communication channel with a CnC owned by the threat actor. Which phase in the Cyber Kill Chain model describes the situation?Correct
Incorrect
-
Question 42 of 62
42. Question
1 pointsHow is a source IP address used in a standard ACL?Correct
Incorrect
-
Question 43 of 62
43. Question
1 pointsRefer to the exhibit. Which access list configuration on router R1 will prevent traffic from the 192.168.2.0 LAN from reaching the Restricted LAN while permitting traffic from any other LAN? Correct
Correct
Incorrect
-
Question 44 of 62
44. Question
1 pointsA company implements a security policy that ensures that a file sent from the headquarters office to the branch office can only be opened with a predetermined code. This code is changed every day. Which two algorithms can be used to achieve this task? (Choose two.)Correct
Incorrect
-
Question 45 of 62
45. Question
1 pointsWhat is the result of using security devices that include HTTPS decryption and inspection services?Correct
Incorrect
-
Question 46 of 62
46. Question
1 pointsWhich three are major categories of elements in a security operations center? (Choose three.)Correct
Incorrect
-
Question 47 of 62
47. Question
1 pointsWhat are two advantages of using the community VERIS database? (Choose two.)Correct
Incorrect
-
Question 48 of 62
48. Question
1 pointsWhich device in a layered defense-in-depth approach denies connections initiated from untrusted networks to internal networks, but allows internal users within an organization to connect to untrusted networks?Correct
Incorrect
-
Question 49 of 62
49. Question
1 pointsBased on the command output shown, which file permission or permissions have been assigned to the other user group for the data.txt file?ls –l data.txt -rwxrw-r– sales staff 1028 May 28 15:50 data.txt
Correct
Incorrect
-
Question 50 of 62
50. Question
1 pointsWhat is indicated by a true negative security alert classification?Correct
Incorrect
-
Question 51 of 62
51. Question
1 pointsWhich metric class in the CVSS Basic Metric Group identifies the impacts on confidentiality, integrity, and availability?Correct
Incorrect
-
Question 52 of 62
52. Question
1 pointsWhat are two evasion techniques that are used by hackers? (Choose two.)Correct
Incorrect
-
Question 53 of 62
53. Question
1 pointsWhich technology might increase the security challenge to the implementation of IoT in an enterprise environment?Correct
Incorrect
-
Question 54 of 62
54. Question
1 pointsWhich type of security threat would be responsible if a spreadsheet add-on disables the local software firewall?Correct
Incorrect
-
Question 55 of 62
55. Question
1 pointsWhy is Diffie-Hellman algorithm typically avoided for encrypting data?Correct
Incorrect
-
Question 56 of 62
56. Question
1 pointsWhich two net commands are associated with network resource sharing? (Choose two.)Correct
Incorrect
-
Question 57 of 62
57. Question
1 pointsWhich Linux command could be used to discover the process ID (PID) for a specific process before using the kill command?Correct
Incorrect
-
Question 58 of 62
58. Question
1 pointsMatch the phase in the NIST incident response life cycle to the action.Correct
Incorrect
-
Question 59 of 62
59. Question
1 pointsMatch the alert classification with the description.Correct
Incorrect
-
Question 60 of 62
60. Question
1 pointsMatch the common network technology or protocol with the description. (Not all options are used.)Correct
Incorrect
-
Question 61 of 62
61. Question
1 pointsMatch the information security component with the description.Correct
Incorrect
-
Question 62 of 62
62. Question
1 pointsMatch the network profile element to the description. (Not all options are used.)Correct
Incorrect

no summary wuiz button lol please i hate you