Time limit: 0
Quiz-summary
0 of 22 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
Information
Good luck for you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 22 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- Answered
- Review
-
Question 1 of 22
1. Question
1 pointsWhat method can be used by two computers to ensure that packets are not dropped because too much data is being sent too quickly?Correct
Incorrect
Hint
In order for two computers to be able to communicate effectively, there must be a mechanism that allows both the source and destination to set the timing of the transmission and receipt of data. Flow control allows for this by ensuring that data is not sent too fast for it to be received properly. -
Question 2 of 22
2. Question
1 pointsWhat type of communication will send a message to all devices on a local area network?Correct
Incorrect
Hint
Broadcast communication is a one-to-all communication. A unicast communication is a one-to-one communication. Multicast is a one-to-many communication where the message is delivered to a specific group of hosts. Allcast is not a standard term to describe message delivery. -
Question 3 of 22
3. Question
1 pointsWhat process is used to place one message inside another message for transfer from the source to the destination?Correct
Incorrect
Hint
Encapsulation is the process of placing one message format into another message format. An example is how a packet is placed in its entirety into the data field as it is encapsulated into a frame. -
Question 4 of 22
4. Question
1 pointsA web client is sending a request for a webpage to a web server. From the perspective of the client, what is the correct order of the protocol stack that is used to prepare the request for transmission?Correct
Incorrect
Hint
1. HTTP governs the way that a web server and client interact. 2. TCP manages individual conversations between web servers and clients. 3. IP is responsible for delivery across the best path to the destination. 4. Ethernet takes the packet from IP and formats it for transmission. -
Question 5 of 22
5. Question
1 pointsWhich statement is correct about network protocols?Correct
Incorrect
Hint
Network protocols are implemented in hardware, or software, or both. They interact with each other within different layers of a protocol stack. Protocols have nothing to do with the installation of the network equipment. Network protocols are required to exchange information between source and destination devices in both local and remote networks. -
Question 6 of 22
6. Question
1 pointsWhich statement is true about the TCP/IP and OSI models?Correct
Incorrect
Hint
he TCP/IP internet layer provides the same function as the OSI network layer. The transport layer of both the TCP/IP and OSI models provides the same function. The TCP/IP application layer includes the same functions as OSI Layers 5, 6, and 7. -
Question 7 of 22
7. Question
1 pointsWhat is an advantage of using standards to develop and implement protocols?Correct
Incorrect
Hint
Standards-based protocols enable products from different manufacturers to interoperate successfully. Standards-based protocols enable many manufacturers to implement that protocol. If different manufacturers implement different requirements within the same protocol, then their products will not be interoperable. -
Question 8 of 22
8. Question
1 pointsWhat three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)Correct
Incorrect
Hint
DNS, DHCP, and FTP are all application layer protocols in the TCP/IP protocol suite. ARP and PPP are network access layer protocols, and NAT is an internet layer protocol in the TCP/IP protocol suite. -
Question 9 of 22
9. Question
1 pointsWhat are proprietary protocols?Correct
Incorrect
Hint
Proprietary protocols have their definition and operation controlled by one company or vendor. Some of them can be used by different organizations with permission from the owner. The TCP/IP protocol suite is an open standard, not a proprietary protocol. -
Question 10 of 22
10. Question
1 pointsWhat is an advantage of network devices using open standard protocols?Correct
Incorrect
Hint
An advantage of network devices implementing open standard protocols, such as from the TCP/IP suite, is that clients and servers running different operating systems can communicate with each other. Open standard protocols facilitate innovation and competition between vendors and across markets, and can reduce the occurrence of monopolies in networking markets. -
Question 11 of 22
11. Question
1 pointsRefer to the exhibit. If Host1 were to transfer a file to the server, what layers of the TCP/IP model would be used? Correct
Correct
Incorrect
Hint
The TCP/IP model contains the application, transport, internet, and network access layers. A file transfer uses the FTP application layer protocol. The data would move from the application layer through all of the layers of the model and across the network to the file server. -
Question 12 of 22
12. Question
1 pointsWhich three layers of the OSI model are comparable in function to the application layer of the TCP/IP model? (Choose three.)Correct
Incorrect
Hint
The TCP/IP model consists of four layers: application, transport, internet, and network access. The OSI model consists of seven layers: application, presentation, session, transport, network, data link, and physical. The top three layers of the OSI model: application, presentation, and session map to the application layer of the TCP/IP model. -
Question 13 of 22
13. Question
1 pointsAt which layer of the OSI model would a logical address be encapsulated?Correct
Incorrect
Hint
Logical addresses, also known as IP addresses, are encapsulated at the network layer. Physical addresses are encapsulated at the data link layer. Port addresses are encapsulated at the transport layer. No addresses are encapsulated at the physical layer. -
Question 14 of 22
14. Question
1 pointsWhich PDU format is used when bits are received from the network medium by the NIC of a host?Correct
Incorrect
Hint
When received at the physical layer of a host, the bits are formatted into a frame at the data link layer. A packet is the PDU at the network layer. A segment is the PDU at the transport layer. A file is a data structure that may be used at the application layer. -
Question 15 of 22
15. Question
1 pointsWhich PDU is processed when a host computer is de-encapsulating a message at the transport layer of the TCP/IP model?Correct
Incorrect
Hint
At the transport layer, a host computer will de-encapsulate a segment to reassemble data to an acceptable format by the application layer protocol of the TCP/IP model. -
Question 16 of 22
16. Question
1 pointsRefer to the exhibit. HostA is attempting to contact ServerB. Which two statements correctly describe the addressing that HostA will generate in the process? (Choose two.)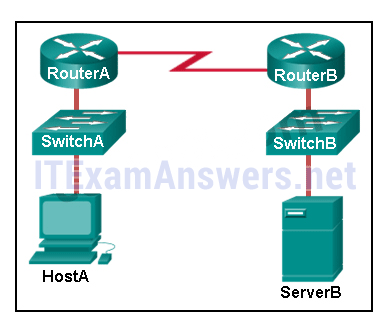 Correct
Correct
Incorrect
Hint
In order to send data to ServerB, HostA will generate a packet that contains the IP address of the destination device on the remote network and a frame that contains the MAC address of the default gateway device on the local network. -
Question 17 of 22
17. Question
1 pointsWhich address does a NIC use when deciding whether to accept a frame?Correct
Incorrect
-
Question 18 of 22
18. Question
1 pointsWhat will happen if the default gateway address is incorrectly configured on a host?Correct
Incorrect
Hint
When a host needs to send a message to another host located on the same network, it can forward the message directly. However, when a host needs to send a message to a remote network, it must use the router, also known as the default gateway. This is because the data link frame address of the remote destination host cannot be used directly. Instead, the IP packet has to be sent to the router (default gateway) and the router will forward the packet toward its destination. Therefore, if the default gateway is incorrectly configured, the host can communicate with other hosts on the same network, but not with hosts on remote networks. -
Question 19 of 22
19. Question
1 pointsWhich characteristic describes the default gateway of a host computer?Correct
Incorrect
Hint
The default gateway is the IP address of an interface on the router on the same network as the sending host. -
Question 20 of 22
20. Question
1 pointsMatch the description to the organization. (Not all options are used.)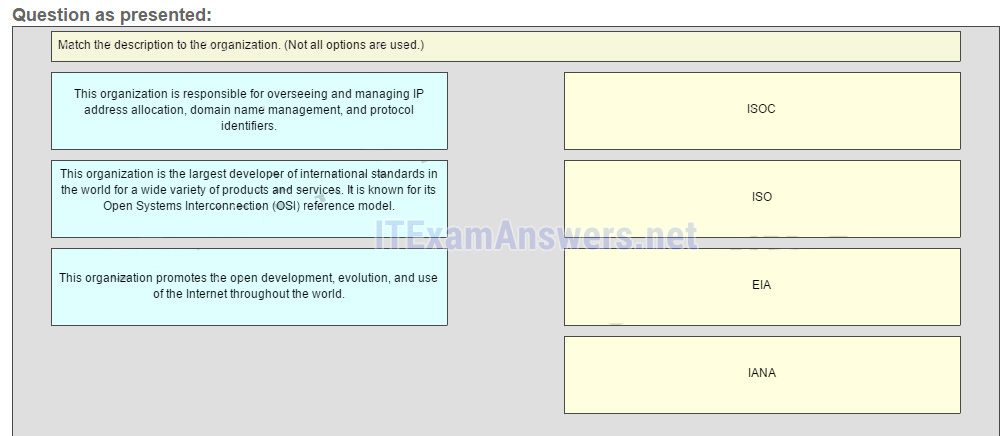
Sort elements
- ISOC
- ISO
- IANA
- EIA
-
The organization promotes the open development, evolution, and use of the internet throughout the world
-
This organization is the largest developer of international standars in the world for a wide variety of products and services. It is know for its Open System Interconection (OSI) reference model.
-
This organization is responsible for overseeing and managing IP address allocation, domain name management, and protocol identifiers
Correct
Incorrect
Hint
The EIA is an international standards and trade organization for electronics organizations. It is best known for its standards related to electrical wiring, connectors, and the 19-inch racks used to mount networking equipment. -
Question 21 of 22
21. Question
1 pointsMatch the protocol function to the description while taking into consideration that a network client is visiting a web site. (Not all options are used.)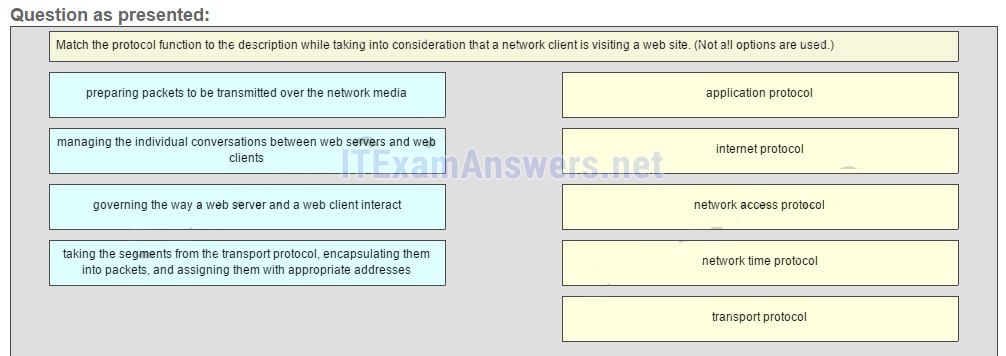
Sort elements
- application protocol
- internet protocol
- network access protocol
- transport protocol
- network time protocol
-
governing the way a web server and a web client interact
-
taking the segments from transport protocol, encapsulating them into packets, and assigning them with appropriate addresses
-
preparing packets to be transmitted over the network media
-
managing the individual conversations between web servers and web clients
Correct
Incorrect
Hint
When a web client visits a web server, several network communication protocols are involved. These different protocols work together to ensure that the messages are received and understood by both parties. These protocols include the following: Application Protocol – governing the way a web server and a web client interact Transport Protocol – managing the individual conversations between web servers and web clients Internet Protocol – taking the formatted segments from the transport protocol, encapsulating them into packets, assigning them the appropriate addresses, and delivering them across the best path to the destination host Network Access Protocol – preparing packets to be transmitted over the network media Network Time Protocol is used to synchronize clocks between computer systems. It is not involved in this case. -
Question 22 of 22
22. Question
1 pointsMatch each description to its corresponding term. (Not all options are used.)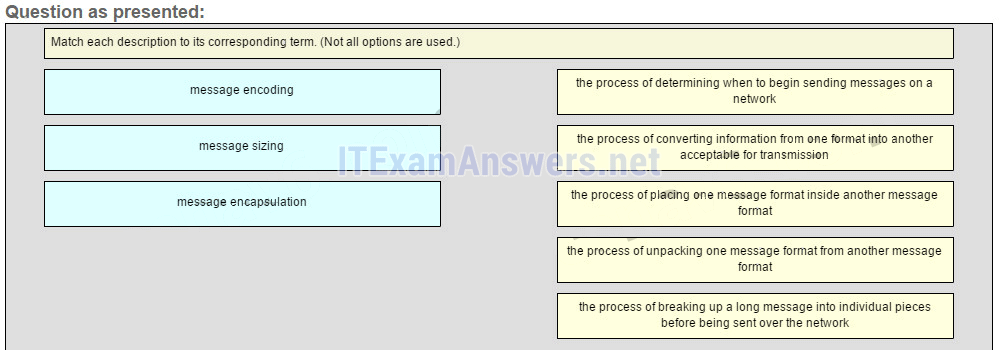
Sort elements
- the process of converting information from one format into another acceptable for transmission
- the process of placing one message format inside another message format
- the process of breaking up a long message into individual pieces before being sent over the network
- the process of determining when to begin sending messages on the network
- the process of unpacking one massage fomat from another message fomat
-
message encoding
-
message encapsulation
-
message sizing
Correct
Incorrect

Question 21 gives me all wrong, but after looking up the correct answers, they are the same as i have answered but they still say i’m wrong.
The same with question 22. The answers for message encoding and message sizing are inverted.
Nevermind on question 22, it’s the correct answers.
Where to see the answer of the question
Hi,
Are these possible questions on the exam? Thnaks
some of the answer changes when i press de “finish” button.
:(
@shai, i’d ask the same question to myself during the test, can you please fix that ?
This is an amazing website by the way, thank you for everything you do for us !
Refer to the exhibit. HostA is attempting to contact ServerB. Which two statements correctly describe the addressing that HostA will generate in the process? (Choose two.)…
what exibit?
Question asking “Which three layers of the OSI model are comparable in function to the application layer of the TCP/IP model? (Choose three.)” should be “Application”, “Presentation”, & “Session” instead of “Transport”
ok, thank you :)
Question 15) I believe the answer should be Application, Presentation, and Session instead of Transport
Whoops, I meant the one saying “Which three layers of the OSI model are comparable in function to the application layer of the TCP/IP model? (Choose three.)”
the reason because is wrong is the question referrer TCP-IP Model remember it doesn’t appear the presentation or session in that model that the reason.