Time limit: 0
Quiz-summary
0 of 20 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
Information
Good luck for you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- Answered
- Review
-
Question 1 of 20
1. Question
1 pointsWhich characteristic of the network layer in the OSI model allows carrying packets for multiple types of communications among many hosts?Correct
Incorrect
Hint
The function of the network layer protocols specifies the packet structure and processing used to carry the data from one host to another host. The actual communication data is encapsulated in the network layer PDU. The feature of its operation without regard to the data carried in each packet allows the network layer to carry packets for multiple types of communications. -
Question 2 of 20
2. Question
1 pointsWhat are two characteristics of IP? (Choose two.)Correct
Incorrect
Hint
The Internet Protocol (IP) is a connectionless, best effort protocol. This means that IP requires no end-to-end connection nor does it guarantee delivery of packets. IP is also media independent, which means it operates independently of the network media carrying the packets. -
Question 3 of 20
3. Question
1 pointsWhen a connectionless protocol is in use at a lower layer of the OSI model, how is missing data detected and retransmitted if necessary?Correct
Incorrect
Hint
When connectionless protocols are in use at a lower layer of the OSI model, upper-level protocols may need to work together on the sending and receiving hosts to account for and retransmit lost data. In some cases, this is not necessary, because for some applications a certain amount of data loss is tolerable. -
Question 4 of 20
4. Question
1 pointsWhich field in the IPv4 header is used to prevent a packet from traversing a network endlessly?Correct
Incorrect
Hint
The value of the Time-to-Live (TTL) field in the IPv4 header is used to limit the lifetime of a packet. The sending host sets the initial TTL value; which is decreased by one each time the packet is processed by a router. If the TTL field decrements to zero, the router discards the packet and sends an Internet Control Message Protocol (ICMP) Time Exceeded message to the source IP address. The Differentiated Services (DS) field is used to determine the priority of each packet. Sequence Number and Acknowledgment Number are two fields in the TCP header. -
Question 5 of 20
5. Question
1 pointsWhat IPv4 header field identifies the upper layer protocol carried in the packet?Correct
Incorrect
Hint
It is the Protocol field in the IP header that identifies the upper-layer protocol the packet is carrying. The Version field identifies the IP version. The Differential Services field is used for setting packet priority. The Identification field is used to reorder fragmented packets. -
Question 6 of 20
6. Question
1 pointsWhat is one advantage that the IPv6 simplified header offers over IPv4?Correct
Incorrect
Hint
The IPv6 simplified header offers several advantages over IPv4: · Better routing efficiency and efficient packet handling for performance and forwarding-rate scalability · No requirement for processing checksums · Simplified and more efficient extension header mechanisms (as opposed to the IPv4 Options field) · A Flow Label field for per-flow processing with no need to open the transport inner packet to identify the various traffic flows -
Question 7 of 20
7. Question
1 pointsRefer to the exhibit. Which route from the PC1 routing table will be used to reach PC2? Correct
Correct
Incorrect
Hint
PC1 and PC2 are both on network 192.168.10.0 with mask 255.255.255.0, so there is no need to access the default gateway (entry 0.0.0.0 0.0.0.0). Entry 127.0.0.1 255.255.255.255 is the loopback interface and entry 192.168.10.10 255.255.255.255 identifies the PC1 address interface. -
Question 8 of 20
8. Question
1 pointsRefer to the exhibit. R1 receives a packet destined for the IP address 192.168.2.10. Out which interface will R1 forward the packet?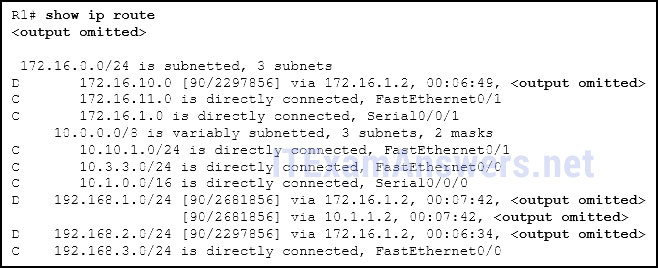 Correct
Correct
Incorrect
Hint
If a route in the routing table points to a next hop address, the router will perform a second lookup to determine out which interface the next hop is located. -
Question 9 of 20
9. Question
1 pointsWhat type of route is indicated by the code C in an IPv4 routing table on a Cisco router?Correct
Incorrect
Hint
Some of the IPv4 routing table codes include the following: C – directly connected S – static D – EIGRP * – candidate default -
Question 10 of 20
10. Question
1 pointsWhat routing table entry has a next hop address associated with a destination network?Correct
Incorrect
Hint
Routing table entries for remote routes will have a next hop IP address. The next hop IP address is the address of the router interface of the next device to be used to reach the destination network. Directly-connected and local routes have no next hop, because they do not require going through another router to be reached. -
Question 11 of 20
11. Question
1 pointsWhich statement describes a hardware feature of a Cisco 1941 router that has the default hardware configuration?Correct
Incorrect
Hint
The connections in a Cisco 1941 router include two types of ports that are used for initial configuration and command-line interface management access. The two ports are the regular RJ-45 port and a new USB Type-B (mini-B USB) connector. In addition, the router has an AUX port for remote management access, and two Gigabit Ethernet interfaces for LAN access. Compact Flash can be used increase device storage, but it does not perform the functions of the CPU, which is required for operation of the device. -
Question 12 of 20
12. Question
1 pointsFollowing default settings, what is the next step in the router boot sequence after the IOS loads from flash?Correct
Incorrect
Hint
There are three major steps to the router boot sequence: Perform Power-On-Self-Test (POST) Load the IOS from Flash or TFTP server Load the startup configuration file from NVRAM -
Question 13 of 20
13. Question
1 pointsWhat are two types of router interfaces? (Choose two.)Correct
Incorrect
Hint
Router interfaces can be grouped into two categories: · LAN interfaces – Used for connecting cables that terminate with LAN devices, such as computers and switches. This interface can also be used to connect routers to each other. · WAN interfaces – Used for connecting routers to external networks, usually over a larger geographical distance. -
Question 14 of 20
14. Question
1 pointsWhich two pieces of information are in the RAM of a Cisco router during normal operation? (Choose two.)Correct
Incorrect
Hint
The Cisco IOS file is stored in flash memory and copied into RAM during the boot up. The IP routing table is also stored in RAM. The basic diagnostic software is stored in ROM and the startup configuration file is stored in NVRAM. -
Question 15 of 20
15. Question
1 pointsA router boots and enters setup mode. What is the reason for this?Correct
Incorrect
-
Question 16 of 20
16. Question
1 pointsWhat is the purpose of the startup configuration file on a Cisco router?Correct
Incorrect
Hint
The startup configuration file is stored in NVRAM and contains the commands needed to initially configure a router. It also creates the running configuration file that is stored in in RAM. -
Question 17 of 20
17. Question
1 pointsWhich three commands are used to set up secure access to a router through a connection to the console interface? (Choose three.)Correct
Incorrect
Hint
The three commands needed to password protect the console port are as follows: line console 0 password cisco login Theinterface fastethernet 0/0 command is commonly used to access the configuration mode used to apply specific parameters such as the IP address to the Fa0/0 port. The line vty 0 4 command is used to access the configuration mode for Telnet. The0and 4 parameters specify ports 0 through 4, or a maximum of five simultaneous Telnet connections. The enable secret command is used to apply a password used on the router to access the privileged mode. -
Question 18 of 20
18. Question
1 pointsWhich characteristic describes an IPv6 enhancement over IPv4?Correct
Incorrect
Hint
IPv6 addresses are based on 128-bit hierarchical addressing, and the IPv6 header has been simplified with fewer fields, improving packet handling. IPv6 natively supports authentication and privacy capabilities as opposed to IPv4 that needs additional features to support those. The IPv6 address space is many times bigger than IPv4 address space. -
Question 19 of 20
19. Question
1 pointsOpen the PT Activity. The enable password on all devices is cisco. Perform the tasks in the activity instructions and then answer the question. For what reason is the failure occurring?Correct
Incorrect
Hint
The ip default-gateway command is missing on the SW1 configuration. Packets from PC2 are able to successfully reach SW1, but SW1 is unable to forward reply packets beyond the local network without the ip default-gateway command issued. -
Question 20 of 20
20. Question
1 pointsMatch the command with the device mode at which the command is entered. (Not all options are used.)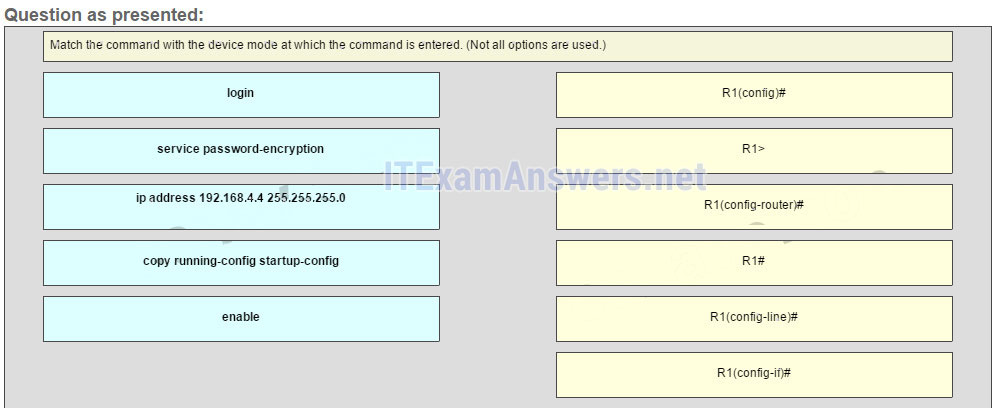
Sort elements
- R1(config-line)#
- R1(config)#
- R1(config-if)#
- R1#
- R1>
- R1(config-router)#
-
login
-
service password-encryption
-
ip address 192.168.4.4 255.255.255.0
-
copy running-config startup-config
-
enable
Correct
Incorrect
Hint
The enable command is entered in R1> mode. The login command is entered in R1(config-line)# mode. The copy running-config startup-config command is entered in R1# mode. The ip address 192.168.4.4 255.255.255.0 command is entered in R1(config-if)# mode. The service password-encryption command is entered in global configuration mode.
