Time limit: 0
Quiz-summary
0 of 26 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
Information
Good luck!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 26 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- Answered
- Review
-
Question 1 of 26
1. Question
1 pointsWhich broadband wireless technology is based on the 802.11 standard?Correct
Incorrect
Hint
The IEEE 802.11 standard is also known as Wi-Fi. Municipal Wi-Fi is a variant of the 802.11 standard. -
Question 2 of 26
2. Question
1 pointsWhat is the approximate distance limitation for providing a satisfactory ADSL service from the central office to a customer?Correct
Incorrect
Hint
For customers to receive satisfactory ADSL service, the local loop, or distance from the central office, must be less than 5.46 kilometers. -
Question 3 of 26
3. Question
1 pointsWhat is a component of an ADSL connection that is located at the customer site?Correct
Incorrect
Hint
Customer premises equipment (CPE) is the equipment, such as a router or modem, that is located at the customer site and connects the internal network to the carrier network. -
Question 4 of 26
4. Question
1 pointsWhat is the function of the DSLAM in a broadband DSL network?Correct
Incorrect
Hint
On a DSL network the DSLAM is used to multiplex connections from DSL subscribers into a single high-capacity link. The DSLAM is located at the central office of the provider. -
Question 5 of 26
5. Question
1 pointsWhich broadband technology would be best for a small office that requires fast upstream connections?Correct
Incorrect
Hint
Fiber-to-the-home provides fast downstream and upstream connections. DSL, cable, and WiMax provide relatively slow upstream connections. -
Question 6 of 26
6. Question
1 pointsWhat are two WAN connection enhancements that are achieved by implementing PPPoE? (Choose two.)Correct
Incorrect
Hint
Encapsulating a PPP frame within an Ethernet frames enables IP address assignment by ISPs that are using DSL technology, as well as the ability to use CHAP for authentication and accounting. Traditional DSL does not support CHAP authentication. A traditional Ethernet link supports only Ethernet-based data link protocols. -
Question 7 of 26
7. Question
1 pointsWhen PPPoE is configured on a customer router, which two commands must have the same value for the configuration to work? (Choose two.)Correct
Incorrect
Hint
The dialer pool number configured on both the dialer and Ethernet interfaces must match. The interface numbers and the username and the password do not have to match -
Question 8 of 26
8. Question
1 pointsWhy is the MTU for a PPPoE DSL configuration reduced from 1500 bytes to 1492?Correct
Incorrect
Hint
The default maximum data field of an Ethernet frame is 1500 bytes. However, in PPPoE the Ethernet frame payload includes a PPP frame which has also has a header. This reduces the available data MTU to 1492 bytes. -
Question 9 of 26
9. Question
1 pointsWhat are two characteristics of a PPPoE configuration on a Cisco customer router? (Choose two.)Correct
Incorrect
Hint
PPP, CHAP, an IP address, the dialer pool number, and the MTU size are all configured on the dialer interface. The customer router CHAP username and password must match what is configured the ISP router. The pppoe-client command, not the dialer pool command, is applied to the Ethernet interface to link it to the dialer interface. -
Question 10 of 26
10. Question
1 pointsWhere is PPPoE configured on a Cisco router?Correct
Incorrect
Hint
The PPPoE configuration is applied to the dialer interface, not to the Ethernet interface. The dialer interface is linked to the Ethernet interface with the dialer-pool and pppoe-client commands. -
Question 11 of 26
11. Question
1 pointsHow can the use of VPNs in the workplace contribute to lower operating costs?Correct
Incorrect
Hint
VPN technology can be used with broadband connectivity or more expensive leased lines. VPNs provide connectivity between offices, users, and SOHO environments. VPNs do not require a specific ISP to be used. -
Question 12 of 26
12. Question
1 pointsHow is “tunneling” accomplished in a VPN?Correct
Incorrect
Hint
Packets in a VPN are encapsulated with the headers from one or more VPN protocols before being sent across the third party network. This is referred to as “tunneling”. These outer headers can be used to route the packets, authenticate the source, and prevent unauthorized users from reading the contents of the packets. -
Question 13 of 26
13. Question
1 pointsWhich two statements describe a remote access VPN? (Choose two.)Correct
Incorrect
Hint
Remote access VPNs can be used to support the needs of telecommuters and mobile users by allowing them to connect securely to company networks over the Internet. To connect hosts to the VPN server on the corporate network, the remote access VPN tunnel is dynamically built by client software that runs on the hosts. -
Question 14 of 26
14. Question
1 pointsWhich is a requirement of a site-to-site VPN?Correct
Incorrect
Hint
Site-to-site VPNs are static and are used to connect entire networks. Hosts have no knowledge of the VPN and send TCP/IP traffic to VPN gateways. The VPN gateway is responsible for encapsulating the traffic and forwarding it through the VPN tunnel to a peer gateway at the other end which decapsulates the traffic. -
Question 15 of 26
15. Question
1 pointsWhat functionality does mGRE provide to the DMVPN technology?Correct
Incorrect
Hint
DMVPN is built on three protocols, NHRP, IPsec, and mGRE. NHRP is the distributed address mapping protocol for VPN tunnels. IPsec encrypts communications on VPN tunnels. The mGRE protocol allows the dynamic creation of multiple spoke tunnels from one permanent VPN hub. -
Question 16 of 26
16. Question
1 pointsWhich two scenarios are examples of remote access VPNs? (Choose two.)Correct
Incorrect
Hint
Remote access VPNs connect individual users to another network via a VPN client that is installed on the user device. Site-to-site VPNs are “always on” connections that use VPN gateways to connect two sites together. Users at each site can access the network on the other site without having to use any special clients or configurations on their individual devices. -
Question 17 of 26
17. Question
1 pointsThe graphic shows two routers, R1 and R2, that connect to the Internet. There is a site attached to each router. Site A is attached to router R1 and site B is attached to router R2. A tunnel is shown spanning the Internet between the two routers. Refer to the exhibit. What solution can provide a VPN between site A and site B to support encapsulation of any Layer 3 protocol between the internal networks at each site? Correct
Correct
Incorrect
Hint
A Generic Routing Encapsulation (GRE) tunnel is a non-secure, site-to-site VPN tunneling solution that is capable of encapsulating any Layer 3 protocol between multiple sites across over an IP internetwork. -
Question 18 of 26
18. Question
1 pointsWhich three statements are characteristics of generic routing encapsulation (GRE)? (Choose three.)Correct
Incorrect
Hint
GRE uses a protocol type field in the GRE header to support the encapsulation of any OSI Layer 3 protocol. GRE itself is stateless; it does not include any flow-control mechanisms by default. GRE does not have strong security mechanisms. -
Question 19 of 26
19. Question
1 pointsRefer to the exhibit. Which IP address is configured on the physical interface of the CORP router?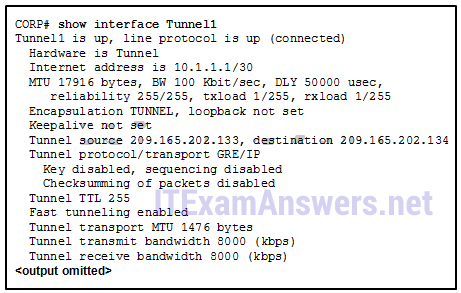 Correct
Correct
Incorrect
Hint
The tunnel source and tunnel destination addresses reference the IP addresses of the physical interfaces on the local and remote routers respectively. -
Question 20 of 26
20. Question
1 pointsRefer to the exhibit. Which IP address would be configured on the tunnel interface of the destination router?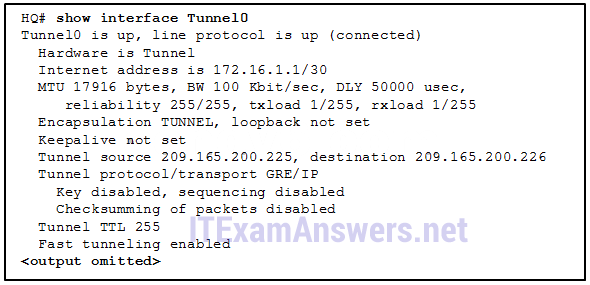 Correct
Correct
Incorrect
Hint
The IP address that is assigned to the tunnel interface on the local router is 172.16.1.1 with a prefix mask of /30. The only other address, 172.16.1.2, would be the destination tunnel interface IP address. Although 209.165.200.226 is listed as a destination address in the output, this is the address of the physical interface at the destination, not the tunnel interface. -
Question 21 of 26
21. Question
1 pointsRefer to the exhibit. A tunnel was implemented between routers R1 and R2. Which two conclusions can be drawn from the R1 command output? (Choose two.)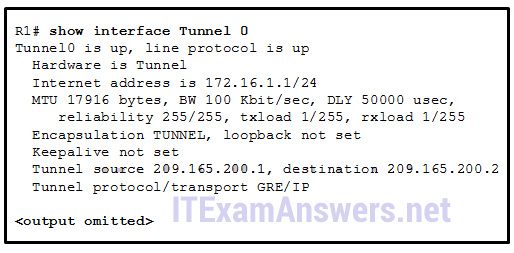 Correct
Correct
Incorrect
Hint
According to the R1 output, a GRE tunnel mode was specified as the tunnel interface mode. GRE is the default tunnel interface mode for Cisco IOS software. GRE does not provide encryption or any other security mechanisms. Therefore, data that is sent across a GRE tunnel is not secure. GRE supports IP multicast tunneling. -
Question 22 of 26
22. Question
1 pointsWhat is used by BGP to determine the best path to a destination?Correct
Incorrect
Hint
BGP uses attributes, such as AS-path, to determine the best path to a destination. -
Question 23 of 26
23. Question
1 pointsWhat command specifies a BGP neighbor that has an IP address of 5.5.5.5/24 and that is in AS 500?Correct
Incorrect
Hint
The neighbor command is used to specify an EBGP neighbor router and peer with it. The command requires that the AS number of the neighbor be included as part of the command. -
Question 24 of 26
24. Question
1 pointsTrue or False? Multiple BGP processes can run on a router.Correct
Incorrect
Hint
Because a BGP router can only belong to a single autonomous system, it can only run a single BGP process. -
Question 25 of 26
25. Question
1 pointsOn the left is a cloud with the following words: ISP 1 AS 64001 Company A 192.168.10.0/24. A router labeled R1 at the edge of this cloud connects through a serial interface labeled 209.165.200.225 to another router labeled R2. The serial interface on R2 is labeled 209.165.200.226. R2 is inside a second cloud labeled ISP 2 AS 650002 Company B 192.168.20.0/24. Refer to the exhibit. Which two configurations will allow router R1 to establish a neighbor relationship with router R2? (Choose two.) Correct
Correct
Incorrect
Hint
To configure EBGP, the router bgp command is followed by the AS number in which the router resides. Conversely, the neighbor command contains the AS number to which the remote router belongs. -
Question 26 of 26
26. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question. What is the code displayed on the web page?Correct
Incorrect
Hint
The basic EBGP configuration includes the following tasks: Step 1: Enable BGP routing. Step 2: Configure the BGP neighbors or neighbor. Step 3: Advertise the network or networks originating from the AS.
