CCNA 4 v6.0 (Connecting Networks v6) Chapter 8: Network Troubleshooting: Check Your Understanding Questions Answers
1. Which statement describes the physical topology for a LAN?
- It defines how hosts and network devices connect to the LAN.
- It depicts the addressing scheme that is employed in the LAN.
- It describes whether the LAN is a broadcast or token-passing network.
- It shows the order in which hosts access the network.
2. When should a network performance baseline be measured?
- After normal work hours to reduce possible interruptions
- During normal work hours of an organization
- Immediately after the main network devices are restarted
- When a denial-of-service attack to the network is detected and blocked
3. In which step of gathering symptoms does the network engineer determine if the problem is at the core, distribution, or access layer of the network?
- Determine ownership.
- Determine the symptoms.
- Document the symptoms.
- Gather information.
- Narrow the scope.
4. A network technician is troubleshooting an email connection problem. Which question to the end user will provide clear information to better define the problem?
- How big are the emails you tried to send?
- Is your email working now?
- What kind of equipment are you using to send emails?
- When did you first notice your email problem?
5. A team of engineers has identified a solution to a significant network problem. The proposed solution is likely to affect critical network infrastructure components. What should the team follow while implementing the solution to avoid interfering with other processes and infrastructure?
- Change-control procedures
- Knowledge base guidelines
- One of the layered troubleshooting approaches
- Syslog messages and reports
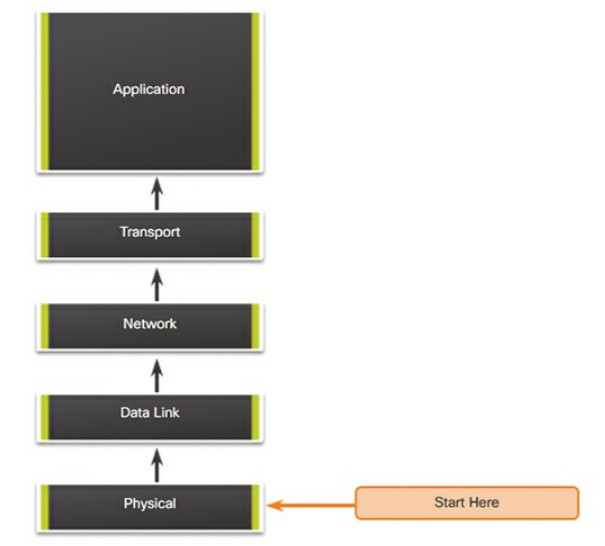
6. A network engineer is troubleshooting a network problem and can successfully ping between two devices. However, Telnet between the same two devices does not work. Which OSI layers should the administrator investigate next?
- All the layers
- From the network layer to the application layer
- From the network layer to the physical layer
- Only the network layer
7. Which troubleshooting method begins by examining cable connections and wiring issues?
- Bottom-up
- Divide-and-conquer
- Substitution
- Top-down
8. An administrator is troubleshooting an Internet connectivity problem on a router. The output of the show interfaces gigabitethernet 0/0 command reveals higher than normal framing errors on the interface that connects to the Internet. At what layer of the OSI model is the problem likely occurring?
- Layer 1
- Layer 2
- Layer 3
- Layer 4
- Layer 7
9. Users report that the new website http://www.company1.biz cannot be accessed. The helpdesk technician checks and verifies that the website can be accessed with http://www.company1.biz:90. Which layer in the TCP/IP model is involved in troubleshooting this issue?
- Application
- Internet
- Network access
- Transport
10. A user reports that after an OS patch of the networking subsystem has been applied to a workstation, it performs very slowly when connecting to network resources. A network technician tests the link with a cable analyzer and notices that the workstation sends an excessive number of frames smaller than 64 bytes and also other meaningless frames. What is the possible cause of the problem?
- Cabling faults
- Corrupted application installation
- Corrupted NIC driver
- Ethernet signal attenuation
11. A networked PC is having trouble accessing the Internet, but it can print to a local printer and ping other computers in the area. Other computers on the same network are not having any issues. What is the problem?
- The default gateway router does not have a default route.
- The link between the switch to which the PC connects and the default gateway router is down.
- The PC has a missing or incorrect default gateway.
- The switch port to which the PC connects has an incorrect VLAN configured.
12. Which three pieces of information are typically recorded in a logical topology diagram? (Choose three.)
- Cable specifications
- Device locations
- Device models and manufacturers
- IP address and prefix lengths
- Routing protocols
- Static routes
13. A company is setting up a website with SSL technology to protect the authentication credentials required to access the website. A network engineer needs to verify that the setup is correct and that the authentication is indeed encrypted. Which tool should be used?
- Baselining tool
- Cable analyzer
- Fault-management tool
- Protocol analyzer
14. Which number represents the most severe level of syslog logging?
- 0
- 1
- 6
- 7