Quiz-summary
0 of 208 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
Information
good luck to you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 208 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- Answered
- Review
-
Question 1 of 208
1. Question
1 pointsWhich statements about using leased lines for your WAN infrastructure are true? (choose 2 options)Correct
Incorrect
-
Question 2 of 208
2. Question
1 pointsWhich condition does the err-disabled status indicate on an Ethernet interface? choose 1 optionsCorrect
Incorrect
-
Question 3 of 208
3. Question
1 pointsWhich condition indicates that service password-encryption is enabled? choose 1 optionsCorrect
Incorrect
-
Question 4 of 208
4. Question
1 pointsWhich type of device can be replaced by the use of subinterfaces for VLAN routing? choose 1 optionsCorrect
Incorrect
-
Question 5 of 208
5. Question
1 pointsWhich command can you enter to determine whether serial interface 0/2/0 has been configured using HDLC encapsulation?choose 1 optionsCorrect
Incorrect
-
Question 6 of 208
6. Question
1 pointsWhich Layer 2 protocol encapsulation type supports synchronous and asynchronous circuits and has built-in security mechanisms?choose 1 optionsCorrect
Incorrect
-
Question 7 of 208
7. Question
1 pointsRefer to the exhibit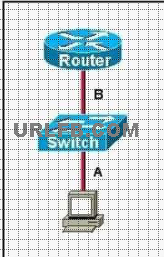 The two connected ports on the switch are not turning orange or green
Which three would be the most effective steps to troubleshoot this physical layer problem? (Choose three)
Correct
The two connected ports on the switch are not turning orange or green
Which three would be the most effective steps to troubleshoot this physical layer problem? (Choose three)
Correct
Incorrect
-
Question 8 of 208
8. Question
1 pointsWhich statements about IPv6 prefixes are true? choose 3 optionsCorrect
Incorrect
-
Question 9 of 208
9. Question
1 pointsWhich command can you enter to display duplicate IP addresses that the DHCP server assigns?choose 1 optionsCorrect
Incorrect
-
Question 10 of 208
10. Question
1 pointsWhat are advantages of VLANs? choose 3 optionsCorrect
Incorrect
-
Question 11 of 208
11. Question
1 points11. Scenario. Refer to the topology Your company has decided to connect the main office with three Other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices_ Use appropriate show commands to troubleshoot the issues and answer all four questions Instructions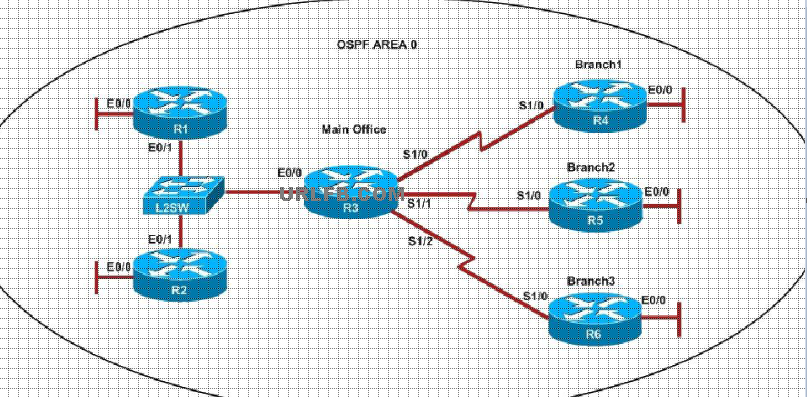 An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branchl office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branchl office. What is causing the problem? Correct
Incorrect
-
Question 12 of 208
12. Question
1 pointsYour company has decided to connect the main office with three Other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices_ Use appropriate show commands to troubleshoot the issues and answer all four questions Instructions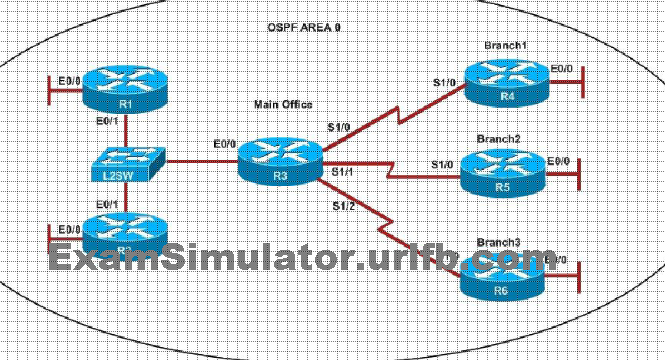 An OSPF neighbor adjacency is not formed between R3 in the main office and R5 in the Branch2 office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R5 in the Branch2 office. What is causing the problem? Correct
Incorrect
-
Question 13 of 208
13. Question
1 pointsDuring which phase of PPPoE is PPP authentication performed? choose 1 optionsCorrect
Incorrect
-
Question 14 of 208
14. Question
1 pointsWhat is the authoritative source for an address lookup? choose 1 optionsCorrect
Incorrect
-
Question 15 of 208
15. Question
1 pointsAn engineer is troubleshooting an EIGRP problem on a router and needs to confirm the IP addresses of the devices with which the router has established adjacency. The retransmit interval and the queue counts for the adjacent routers also need to be checked. What command will display the required information?choose 1 options- (show ip eigrp neighbors)
Correct
Incorrect
-
Question 16 of 208
16. Question
1 pointsWhich function of the IP SLAs ICMP jitter operation can you use to determine whether a VoIP issue is caused by excessive end-to-end time?choose 1 optionsCorrect
Incorrect
-
Question 17 of 208
17. Question
1 pointsWhich statements about IPv4 multicast traffic are true?choose 2 optionsCorrect
Incorrect
-
Question 18 of 208
18. Question
1 pointsWhat are characteristics of the TCP protocol?choose 3 optionsCorrect
Incorrect
-
Question 19 of 208
19. Question
1 pointsWhat are reasons that duplex mismatches can be difficult to diagnose? Choose 2 optionsCorrect
Incorrect
-
Question 20 of 208
20. Question
1 pointsWhich command can you enter to verify that a 128-bit address is live and responding? Choose 1 optionsCorrect
Incorrect
-
Question 21 of 208
21. Question
1 pointsWhen an interface is configured with PortFast BPDU guard, how does the interface respond when it receives a BPDU?choose 1 optionsCorrect
Incorrect
-
Question 22 of 208
22. Question
1 pointsWhich statement about RADIUS security is true? Choose 1 optionsCorrect
Incorrect
-
Question 23 of 208
23. Question
1 pointsScenario Refer to the topology Your company has decided to connect the main office with three Other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices. Use appropriate show commands to troubleshoot the issues and answer all four questions Instructions An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
Incorrect
-
Question 24 of 208
24. Question
1 pointsWhat are benefits of private IPv4 IP addresses? Choose 2 optionsCorrect
Incorrect
-
Question 25 of 208
25. Question
1 pointsRefer to the exhibit. 00:00:39: %LINEPROTO-5-UPDOWN: Line protocol on Interface Vlan1, changed state to down 00:00:40: %SPANTREE-5-EXTENDED_SYSID: Extended SysId enabled for type vlan 00:00:42: %SYS-5-CONFIG_I: Configured from memory by console 00:00:42: %SYS-5-RESTART: System restarted– Cisco IOS Software, C2960 Software (C2960-LANBASEK9-M), Version 12.2(25)SEE2, RELEASE SOFTWARE (fc.1) Copyright(c) 1986-2006 by Cisco Systems, Inc. Compiled Fri 28-Jul-06 11:57 by yenanh 00:00:44: %LINK-5-CHANGED: Interface Vlan1, changed state to administratively down 00:00:44: %LINK-3-UPDOWN: Interface FastEthernet0/1, changed state to up 00:00:44: %LINK-3-UPDOWN: Interface FastEthernet0/2, changed state to up 00:00:44: %LINK-3-UPDOWN: Interface FastEthernet0/11, changed state to up 00:00:45: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/1, changed state to up 00:00:45: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/2, changed state to up 00:00:45: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/11, changed state to up 00:00:48: %LINK-3-UPDOWN: Interface FastEthernet0/12, changed state to up 00:00:49: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/12, changed state to up Which of these statements correctly describes the state of the switch once the boot process has been completed?choose 2 optionsCorrect
Incorrect
-
Question 26 of 208
26. Question
1 pointsWhich statements about IPv6 and routing protocols are true? Choose 2 optionsCorrect
Incorrect
-
Question 27 of 208
27. Question
1 pointsWhich command would you configure globally on a Cisco device that would allow you to view directly connected other Cisco devices?choose 1 options- (cdp run)
Correct
Incorrect
-
Question 28 of 208
28. Question
1 pointsWhich exec command can you enter to verify that a BGP connection to a remote device is established?choose 1 options- (show ip bgp summary)
Correct
Incorrect
-
Question 29 of 208
29. Question
1 pointsWhat will happen if a private IP address is assigned to a public interface connected to an ISP?choose 1 optionsCorrect
Incorrect
-
Question 30 of 208
30. Question
1 pointsIf the primary root bridge experiences a power loss, which switch takes over? choose 1 optionsCorrect
Incorrect
-
Question 31 of 208
31. Question
1 pointsWhich statements about IPv6 prefixes are true? Choose 3 optionsCorrect
Incorrect
-
Question 32 of 208
32. Question
1 pointsWhich command can you enter to verify that a BGP connection to a remote device is established?choose 1 optionsCorrect
Incorrect
-
Question 33 of 208
33. Question
1 pointsA network administrator is troubleshooting an EIGRP problem on a router and needs to confirm the IP addresses of the devices with which the router has established adjacency. The retransmit interval and the queue counts for the adjacent routers also need to be checked. What command will display the required information?choose 1 optionsCorrect
Incorrect
-
Question 34 of 208
34. Question
1 pointsWhich feature builds a FIB and an adjacency table to expedite packet forwarding? Choose 1 optionsCorrect
Incorrect
-
Question 35 of 208
35. Question
1 pointsRefer to the exhibit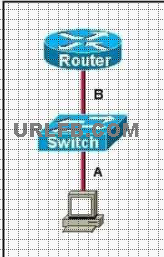 The two connected ports on the switch are not turning orange or green
Which three would be the most effective steps to troubleshoot this physical layer problem? (Choose three) Correct
The two connected ports on the switch are not turning orange or green
Which three would be the most effective steps to troubleshoot this physical layer problem? (Choose three) Correct
Incorrect
-
Question 36 of 208
36. Question
1 pointsA router has learned three possible routes that could be used to reach a destination network. One route is from EIGRP and has a composite metric of 20514560. Another route is from OSPF with a metric of 782. The last is from RIPv2 and has a metric of 4. Which route or routes will the router install in the routing table?choose 1 optionsCorrect
Incorrect
-
Question 37 of 208
37. Question
1 pointsWhich circumstances can cause a GRE tunnel to be in an up/down state? Choose 3 optionsCorrect
Incorrect
-
Question 38 of 208
38. Question
1 pointsWhich statement about LLDP is true? Choose 1 optionsCorrect
Incorrect
-
Question 39 of 208
39. Question
1 pointsWhich statements correctly describe steps in the OSI data encapsulation process? Choose 2 optionsCorrect
Incorrect
-
Question 40 of 208
40. Question
1 pointsIn which formats can the IPv6 address fd15:0db8:0000:0000:0700:0003:400F:572B be written? Choose 2 optionsCorrect
Incorrect
-
Question 41 of 208
41. Question
1 pointsWhich statements correctly describe steps in the OSI data encapsulation process? Choose 2 optionsCorrect
Incorrect
-
Question 42 of 208
42. Question
1 pointsWhat is the result of issuing the frame-relay map ip 192.168.1.2 202 broadcast command?Correct
Incorrect
Hint
Explanation: This command identifies the DLCI that should be used for all packets destined to the 192.168.1.2 address. In this case, DLCI 202 should be used. -
Question 43 of 208
43. Question
1 pointsWhich PPP subprotocol negotiates authentication options?Correct
Incorrect
Hint
Explanation: The PPP Link Control Protocol (LCP) is documented in RFC 1661. LPC negotiates link and PPP parameters to dynamically configure the data link layer of a PPP connection. Common LCP options include the PPP MRU, the authentication protocol, compression of PPP header fields, callback, and multilink options. -
Question 44 of 208
44. Question
1 pointsWhat are two characteristics of Frame Relay point-to-point subinterfaces? (Choose two.)Correct
Incorrect
Hint
Explanation: Subinterfaces are used for point to point frame relay connections, emulating virtual point to point leased lines. Each subinterface requires a unique IP address/subnet. Remember, you can not assign multiple interfaces in a router that belong to the same IP subnet. -
Question 45 of 208
45. Question
1 pointsWhat command is used to verify the DLCI destination address in a Frame Relay static configuration?Correct
Incorrect
Hint
Explanation: Sample “show frame-relay map” output: R1#sh frame mapSerial0/0 (up): ip 10.4.4.1 dlci 401(0x191,0x6410), dynamic,broadcast,, status defined, activeSerial0/0 (up): ip 10.4.4.3 dlci 403(0x193,0x6430), dynamic,broadcast,, status defined, activeSerial0/0 (up): ip 10.4.4.4 dlci 401(0x191,0x6410), static,CISCO, status defined, active -
Question 46 of 208
46. Question
1 pointsWhat is the purpose of Inverse ARP?Correct
Incorrect
Hint
Explanation: Dynamic address mapping relies on the Frame Relay Inverse Address Resolution Protocol (Inverse ARP), defined by RFC 1293, to resolve a next hop network protocol (IP) address to a local DLCI value. The Frame Relay router sends out Inverse ARP requests on its Frame Relay PVC to discover the protocol address of the remote device connected to the Frame Relay network. The responses to the Inverse ARP requests are used to populate an address-to-DLCI mapping table on the Frame Relay router or access server. The router builds and maintains this address-to- DLCI mapping table, which contains all resolved Inverse ARP requests, including both dynamic and static mapping entries. -
Question 47 of 208
47. Question
1 pointsTwo routers named Atlanta and Brevard are connected via their serial interfaces as illustrated, but they are unable to communicate. The Atlanta router is known to have the correct configuration.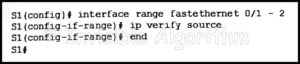
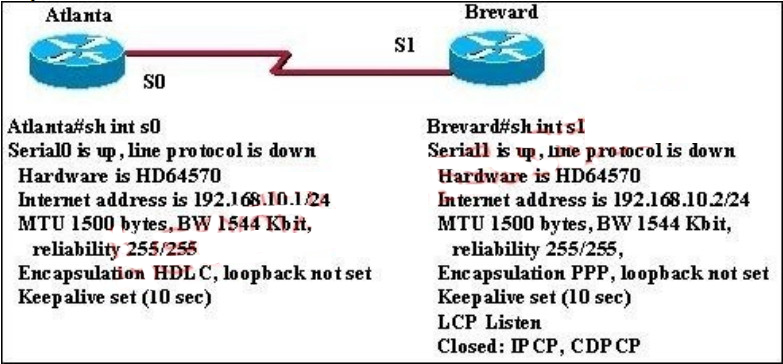 Given the partial configurations, identify the fault on the Brevard router that is causing the lack of connectivity. Correct
Given the partial configurations, identify the fault on the Brevard router that is causing the lack of connectivity. Correct
Incorrect
Hint
Explanation: The correct explanation should be that the Atlanta router is usng HDLC while the Brevard is using PPP. These need to match on both ends. -
Question 48 of 208
48. Question
1 pointsRefer to the exhibit. The company uses EIGRP as the routing protocol. What path will packets take from a host on the 192.168.10.192/26 network to a host on the LAN attached to router R1?
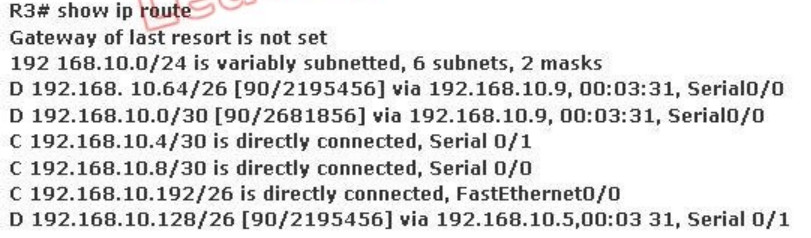 Correct
Correct
Incorrect
Hint
Host on the LAN attached to router R1 belongs to 192.168.10.64/26 subnet. From the output of the routing table of R3 we learn this network can be reach via 192.168.10.9, which is an IP address in 192.168.10.8/30 network (the network between R1 & R3) -> packets destined for 192.168.10.64 will be routed from R3 -> R1 -> LAN on R1. -
Question 49 of 208
49. Question
1 pointsHow does using the service password-encryption command on a router provide additional security?Correct
Incorrect
Hint
Explanation: By using this command, all the (current and future) passwords are encrypted. This command is primarily useful for keeping unauthorized individuals from viewing your password in your configuration file -
Question 50 of 208
50. Question
1 pointsRefer to the exhibit. Switch port FastEthernet 0/24 on ALSwitch1 will be used to create an IEEE 802.1Q-compliant trunk to another switch. Based on the output shown, what is the reason the trunk does not form, even though the proper cabling has been attached?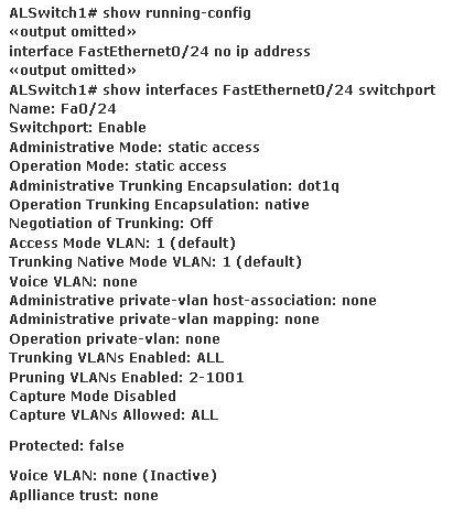 Correct
Correct
Incorrect
Hint
Explanation: According to the output shown the switchport (layer 2 Switching) is enabled and the port is in access mode. To make a trunk link the port should configured as a trunk port, not an access port, by using the following command: (Config-if)#switchport mode trunk -
Question 51 of 208
51. Question
1 pointsRefer to the exhibit. In the Frame Relay network, which IP addresses would be assigned to the interfaces with point-to- point PVCs?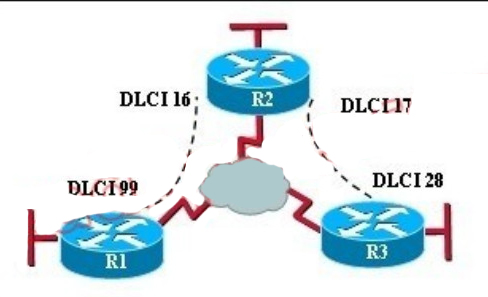 Correct
Correct
Incorrect
Hint
Explanation: With point to point PVC, each connection needs to be in a separate subnet. The R2-R1 connection (DLCI 16 to 99) would have each router within the same subnet. Similarly, the R3-R1 connection would also be in the same subnet, but it must be in a different one than the R2-R1 connection. -
Question 52 of 208
52. Question
1 pointsRefer to the exhibit. A new subnet with 60 hosts has been added to the network. Which subnet address should this network use to provide enough usable addresses while wasting the fewest addresses? Correct
Correct
Incorrect
Hint
Explanation: A subnet with 60 host is 2*2*2*2*2*2 = 64 -2 == 62 6 bits needed for hosts part. Therefore subnet bits are 2 bits (8-6) in fourth octet. 8bits+ 8bits+ 8bits + 2bits = /26 /26 bits subnet is 24bits + 11000000 = 24bits + 192 256 -192 = 64 0 – 63 64 – 127 -
Question 53 of 208
53. Question
1 pointsRefer to the exhibit. All of the routers in the network are configured with the ip subnet-zero command. Which network addresses should be used for Link A and Network A? (Choose two.)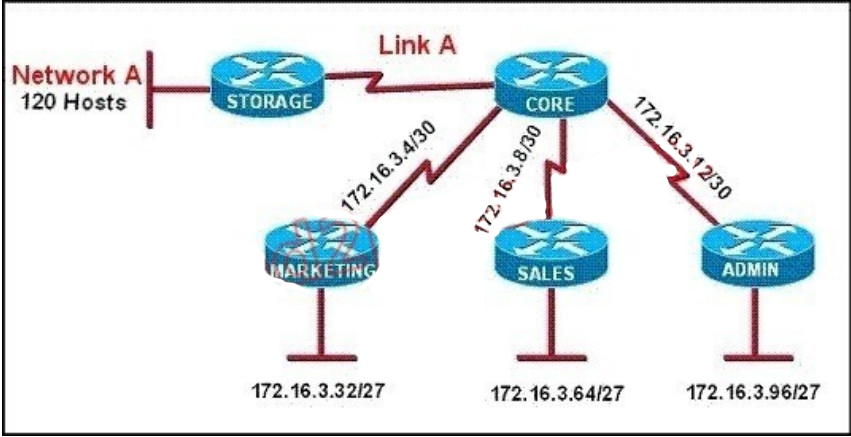 Correct
Correct
Incorrect
Hint
Explanation: Only a /30 is needed for the point to point link and sine the use of the ip subnet-zero was used, 172.16.3.0/30 is valid. Also, a /25 is required for 120 hosts and again 172.16.3.128/25 is the best, valid option. -
Question 54 of 208
54. Question
1 pointsA router has learned three possible routes that could be used to reach a destination network. One route is from EIGRP and has a composite metric of 20514560. Another route is from OSPF with a metric of 782. The last is from RIPv2 and has a metric of 4. Which route or routes will the router install in the routing table?Correct
Incorrect
Hint
Explanation: When one route is advertised by more than one routing protocol, the router will choose to use the routing protocol which has lowest Administrative Distance. The Administrative Distances of popular routing protocols are listed below:
-
Question 55 of 208
55. Question
1 pointsA network administrator needs to allow only one Telnet connection to a router. For anyone viewing the configuration and issuing the show run command, the password for Telnet access should be encrypted. Which set of commands will accomplish this task?Correct
Incorrect
Hint
Explanation: Only one VTY connection is allowed which is exactly what’s requested. Incorrect answer: command. line vty0 4 would enable all 5 vty connections. -
Question 56 of 208
56. Question
1 pointsRefer to the exhibit. The speed of all serial links is E1 and the speed of all Ethernet links is 100 Mb/s. A static route will be established on the Manchester router to direct traffic toward the Internet over the most direct path available. What configuration on the Manchester router will establish a route toward the Internet for traffic that originates from workstations on the Manchester LAN?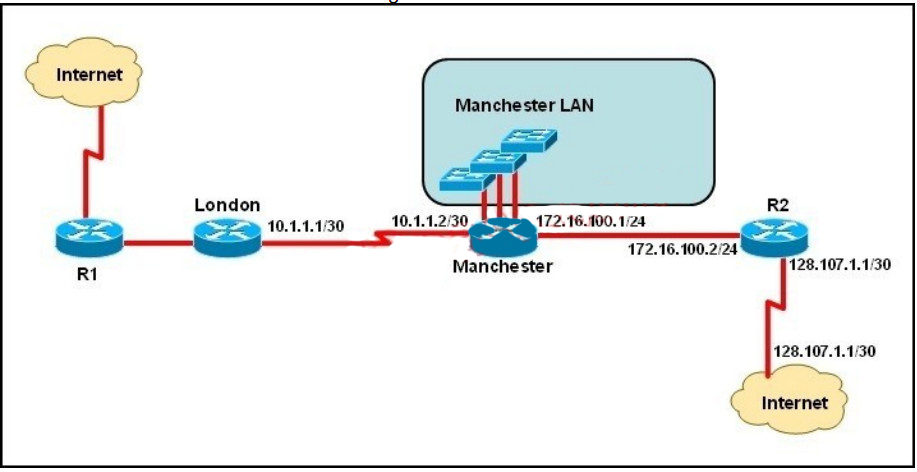 Correct
Correct
Incorrect
Hint
Explanation: We use default routing to send packets with a remote destination network not in the routing table to the next-hop router. You should generally only use default routing on stub networks–those with only one exit path out of the network. According to exhibit, all traffic towards Internet that originates from workstations should forward to Router R1. Syntax for default route is: ip route. -
Question 57 of 208
57. Question
1 pointsRefer to the exhibit. The network administrator must establish a route by which London workstations can forward traffic to the Manchester workstations. What is the simplest way to accomplish this?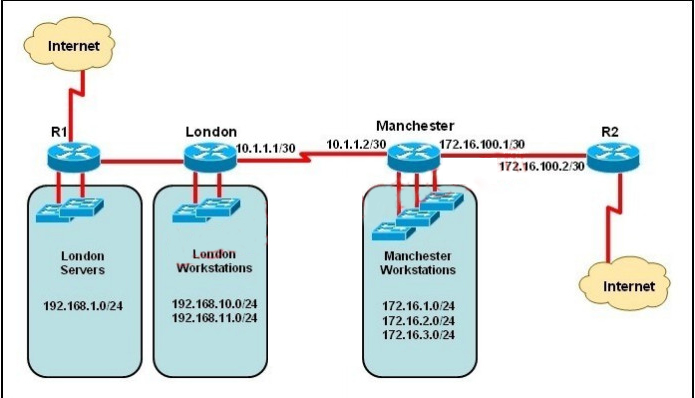 Correct
Correct
Incorrect
Hint
Explanation: This static route will allow for communication to the Manchester workstations and it is better to use this more specific route than a default route as traffic destined to the Internet will then not go out the London Internet connection. -
Question 58 of 208
58. Question
1 pointsRefer to the exhibit. The network administrator requires easy configuration options and minimal routing protocol traffic. What two options provide adequate routing table information for traffic that passes between the two routers and satisfy the requests of the network administrator? (Choose two.) Correct
Correct
Incorrect
Hint
Explanation: The use of static routes will provide the necessary information for connectivity while producing no routing traffic overhead. -
Question 59 of 208
59. Question
1 pointsWhat is the effect of using the service password-encryption command?Correct
Incorrect
Hint
Explanation: Enable vty, console, AUX passwords are configured on the Cisco device. Use the show run command to show most passwords in clear text. If the service password-encryption is used, all the passwords are encrypted. As a result, the security of device access is improved. -
Question 60 of 208
60. Question
1 pointsRefer to the exhibit. What is the effect of the configuration that is shown?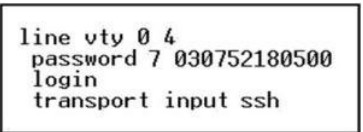 Correct
Correct
Incorrect
Hint
Explanation: Secure Shell (SSH) is a protocol which provides a secure remote access connection to network devices. Communication between the client and server is encrypted in both SSH version 1 and SSH version 2. If you want to prevent non-SSH connections, add the “transport input ssh” command under the lines to limit the router to SSH connections only. Straight (non-SSH) Telnets are refused. www.cisco.com/warp/public/707/ssh.shtml -
Question 61 of 208
61. Question
1 pointsRefer to the exhibit. A junior network administrator was given the task of configuring port security on SwitchA to allow only PC_A to access the switched network through port fa0/1. If any other device is detected, the port is to drop frames from this device. The administrator configured the interface and tested it with successful pings from PC_A to RouterA, and then observes the output from these two show commands. Which two of these changes are necessary for SwitchA to meet the requirements? (Choose two.)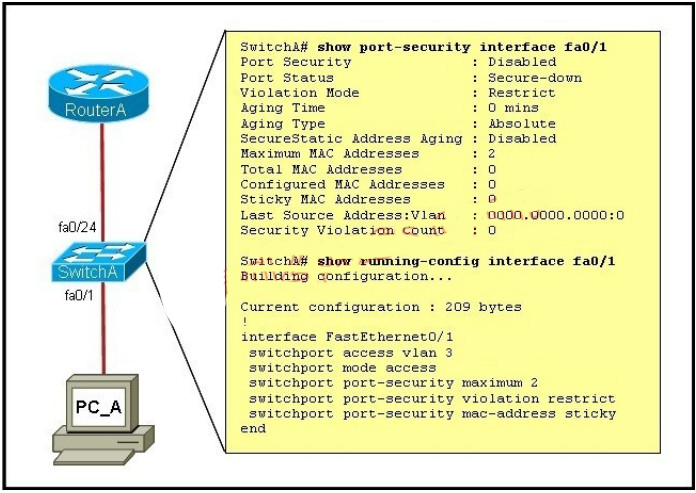 Correct
Correct
Incorrect
Hint
Explanation: From the output we can see that port security is disabled so this needs to be enabled. Also, the maximum number of devices is set to 2 so this needs to be just one if we want the single host to have access and nothing else. -
Question 62 of 208
62. Question
1 pointsRefer to the exhibit. When running OSPF, what would cause router A not to form an adjacency with router B?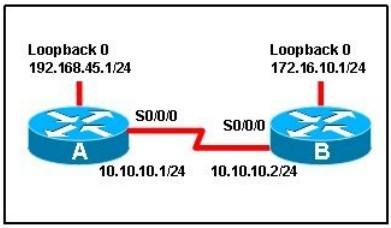 Correct
Correct
Incorrect
Hint
Explanation: To form an adjacency (become neighbor), router A & B must have the same Hello interval, Dead interval and AREA number. -
Question 63 of 208
63. Question
1 pointsWhich two of these statements are true of IPv6 address representation? (Choose two.)Correct
Incorrect
Hint
Explanation: Leading zeros in IPv6 are optional do that 05C7 equals 5C7 and 0000 equals 0 -> D is not correct. -
Question 64 of 208
64. Question
1 pointsWhich set of commands is recommended to prevent the use of a hub in the access layer?Correct
Incorrect
Hint
Explanation: This question is to examine the layer 2 security configuration. In order to satisfy the requirements of this question, you should perform the following configurations in the interface mode: First, configure the interface mode as the access mode Second, enable the port security and set the maximum number of connections to 1. -
Question 65 of 208
65. Question
1 pointsWhat is known as “one-to-nearest” addressing in IPv6?Correct
Incorrect
Hint
Explanation: IPv6 Anycast addresses are used for one-to-nearest communication, meaning an Anycast address is used by a device to send data to one specific recipient (interface) that is the closest out of a group of recipients (interfaces). -
Question 66 of 208
66. Question
1 pointsWhat is the first 24 bits in a MAC address called?Correct
Incorrect
Hint
Explanation: An Organizationally Unique Identifier (OUI) is a 24-bit number that uniquely identifies a vendor, manufacturer, or other organization globally or worldwide. They are used as the first 24 nits of the MAC address to uniquely identify a particular piece of equipment. -
Question 67 of 208
67. Question
1 pointsRefer to the exhibit. Which subnet mask will place all hosts on Network B in the same subnet with the least amount of wasted addresses? Correct
Correct
Incorrect
Hint
Explanation: 310 hosts < 512 = 29 -> We need a subnet mask of 9 bits 0 -> 1111 1111.1111 1111.1111 1110.0000 0000 -> 255.255.254.0 -
Question 68 of 208
68. Question
1 pointsRefer to the exhibit. What is the most appropriate summarization for these routes?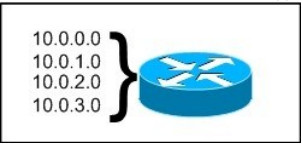 Correct
Correct
Incorrect
Hint
Explanation: The 10.0.0.0/22 subnet mask will include the 10.0.0.0, 10.0.1.0, 10.0.2.0, and 10.0.3.0 networks, and only those four networks. -
Question 69 of 208
69. Question
1 pointsWhat is the difference between a CSU/DSU and a modem?Correct
Incorrect
Hint
Explanation: CSU/DSU is used to convert digital signals from a router to a network circuit such as a T1, while a modem is used to convert digital signals over a regular POTS line. -
Question 70 of 208
70. Question
1 pointsWhich two are features of IPv6? (Choose two.)Correct
Incorrect
Hint
Explanation: IPv6 addresses are classified by the primary addressing and routing methodologies common in networkinG. unicast addressing, anycast addressing, and multicast addressing. -
Question 71 of 208
71. Question
1 pointsWhich two are advantages of static routing when compared to dynamic routing? (Choose two.)Correct
Incorrect
Hint
Explanation: Since static routing is a manual process, it can be argued that it is more secure (and more prone to human errors) since the network administrator will need to make changes to the routing table directly. Also, in stub networks where there is only a single uplink connection, the load is reduced as stub routers just need a single static default route, instead of many routes that all have the same next hop IP address. -
Question 72 of 208
72. Question
1 pointsA network administrator needs to configure port security on a switch. Which two statements are true? (Choose two.)Correct
Incorrect
Hint
Explanation: Follow these guidelines when configuring port security: + Port security can only be configured on static access ports, trunk ports, or 802.1Q tunnel ports. + A secure port cannot be a dynamic access port. + A secure port cannot be a destination port for Switched Port Analyzer (SPAN). + A secure port cannot belong to a Fast EtherChannel or Gigabit EtherChannel port group. + You cannot configure static secure or sticky secure MAC addresses on a voice VLAN. + When you enable port security on an interface that is also configured with a voice VLAN, you must set the maximum allowed secure addresses on the port to at least two. + If any type of port security is enabled on the access VLAN, dynamic port security is automatically enabled on the voice VLAN. + When a voice VLAN is configured on a secure port that is also configured as a sticky secure port, all addresses seen on the voice VLAN are learned as dynamic secure addresses, and all addresses seen on the access VLAN (to which the port belongs) are learned as sticky secure addresses. + The switch does not support port security aging of sticky secure MAC addresses. + The protect and restrict options cannot be simultaneously enabled on an interface.http://www.cisco.com/en/US/docs/switches/lan/catalyst3550/software/release/12.1_19_ea1/config uration/guide/swtrafc.html -
Question 73 of 208
73. Question
1 pointsWhat are three features of the IPv6 protocol? (Choose three.)Correct
Incorrect
Hint
Explanation: An important feature of IPv6 is that it allows plug and play option to the network devices by allowing them to configure themselves independently. It is possible to plug a node into an IPv6 network without requiring any human intervention. This feature was critical to allow network connectivity to an increasing number of mobile devices. This is accomplished by autoconfiguration. IPv6 does not implement traditional IP broadcast, i.e. the transmission of a packet to all hosts on the attached link using a special broadcast address, and therefore does not define broadcast addresses. In IPv6, the same result can be achieved by sending a packet to the link-local all nodes multicast group at address ff02::1, which is analogous to IPv4 multicast to address 224.0.0.1. -
Question 74 of 208
74. Question
1 pointsWhich command enables IPv6 forwarding on a Cisco router?Correct
Incorrect
Hint
Explanation: to enable IPv6 routing on the Cisco router use the following command: ipv6 unicast-routing If this command is not recognized, your version of IOS does not support IPv6. -
Question 75 of 208
75. Question
1 pointsWhich command encrypts all plaintext passwords?Correct
Incorrect
Hint
Explanation: The “service password-encryption” command allows you to encrypt all passwords on your router so they can not be easily guessed from your running-config. This command uses a very weak encryption because the router has to be very quickly decode the passwords for its operation. It is meant to prevent someone from looking over your shoulder and seeing the password, that is all. This is configured in global configuration mode. -
Question 76 of 208
76. Question
1 pointsYou have been asked to come up with a subnet mask that will allow all three web servers to be on the same network while providing the maximum number of subnets. Which network address and subnet mask meet this requirement?Correct
Incorrect
Hint
Explanation: A subnet mask of 255.255.255.248 will allow for up to 6 hosts to reside in this network. A subnet mask of 255.255.255.252 will allow for only 2 usable IP addresses, since we can not use the network or broadcast address. -
Question 77 of 208
77. Question
1 pointsGiven an IP address 172.16.28.252 with a subnet mask of 255.255.240.0, what is the correct network address?Correct
Incorrect
Hint
Explanation: For this example, the network range is 172.16.16.1 – 172.16.31.254, the network address is 172.16.16.0 and the broadcast IP address is 172.16.31.255. -
Question 78 of 208
78. Question
1 pointsWhich IPv6 address is the equivalent of the IPv4 interface loopback address 127.0.0.1?Correct
Incorrect
Hint
Explanation: In IPv6 the loopback address is written as, This is a 128bit number, with the first 127 bits being ‘0’ and the 128th bit being ‘1’. It’s just a single address, so could also be written as ::1/128. -
Question 79 of 208
79. Question
1 pointsYou are working in a data center environment and are assigned the address range 10.188.31.0/23. You are asked to develop an IP addressing plan to allow the maximum number of subnets with as many as 30 hosts each. Which IP address range meets these requirements?Correct
Incorrect
Hint
Explanation: Each subnet has 30 hosts < 32 = 25 so we need a subnet mask which has at least 5 bit 0s -> /27. Also the question requires the maximum number of subnets (which minimum the number of hosts- per-subnet) so /27 is the best choice -> . -
Question 80 of 208
80. Question
1 pointsWhich parameter or parameters are used to calculate OSPF cost in Cisco routers?Correct
Incorrect
Hint
Explanation: The well-known formula to calculate OSPF cost is Cost = 108 / Bandwidth -
Question 81 of 208
81. Question
1 pointsWhy do large OSPF networks use a hierarchical design? (Choose three.)Correct
Incorrect
Hint
Explanation: OSPF implements a two-tier hierarchical routing model that uses a core or backbone tier known as area zero (0). Attached to that backbone via area border routers (ABRs) are a number of secondary tier areas. The hierarchical approach is used to achieve the following: Rapid convergence because of link and/or switch failures Deterministic traffic recovery Scalable and manageable routing hierarchy, reduced routing overhead. -
Question 82 of 208
82. Question
1 pointsHotspot Question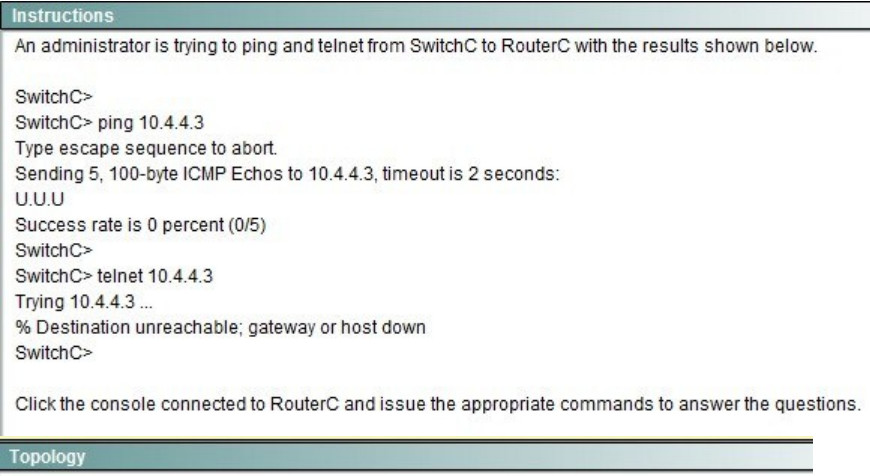
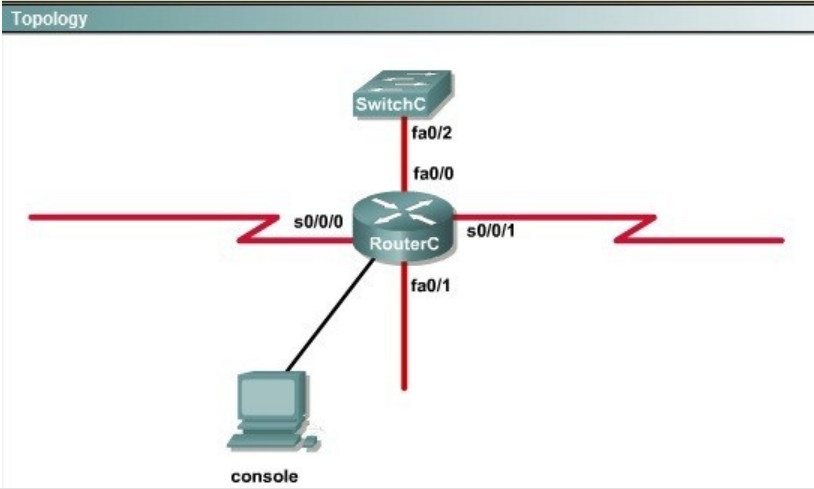
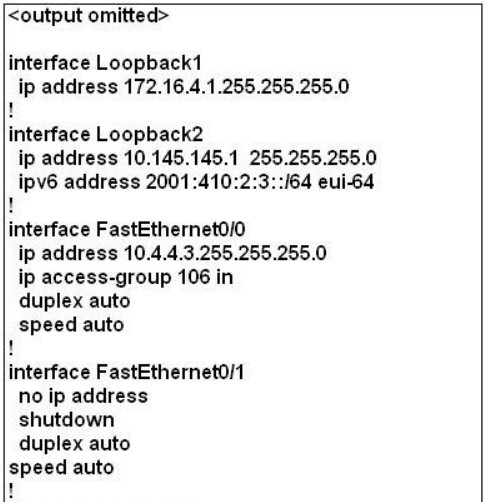
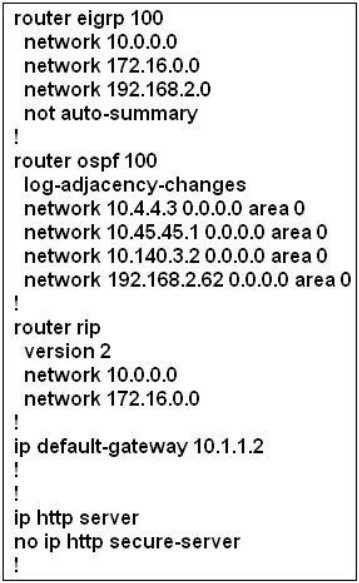
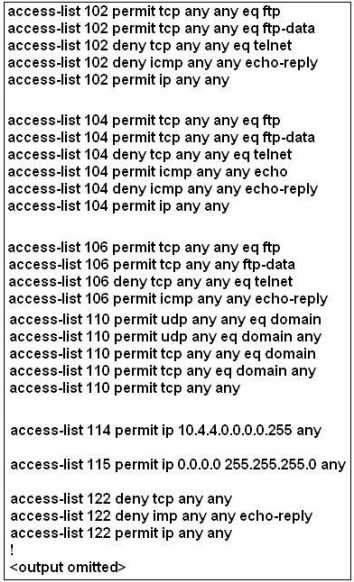 Which will fix the issue and allow ONLY ping to work while keeping telnet disabled? Correct
Which will fix the issue and allow ONLY ping to work while keeping telnet disabled? Correct
Incorrect
Hint
Explanation: Let’s have a look at the access list 104: The question does not ask about ftp traffic so we don’t care about the two first lines. The 3rd line denies all telnet traffic and the 4th line allows icmp traffic to be sent (ping). Remember that the access list 104 is applied on the inbound direction so the 5th line “access-list 104 deny icmp any any echo-reply” will not affect our icmp traffic because the “echo-reply” message will be sent over the outbound direction.
The question does not ask about ftp traffic so we don’t care about the two first lines. The 3rd line denies all telnet traffic and the 4th line allows icmp traffic to be sent (ping). Remember that the access list 104 is applied on the inbound direction so the 5th line “access-list 104 deny icmp any any echo-reply” will not affect our icmp traffic because the “echo-reply” message will be sent over the outbound direction. -
Question 83 of 208
83. Question
1 pointsHotspot Question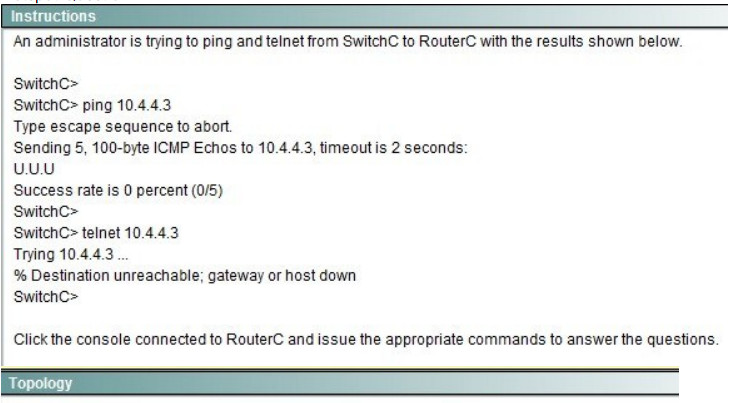
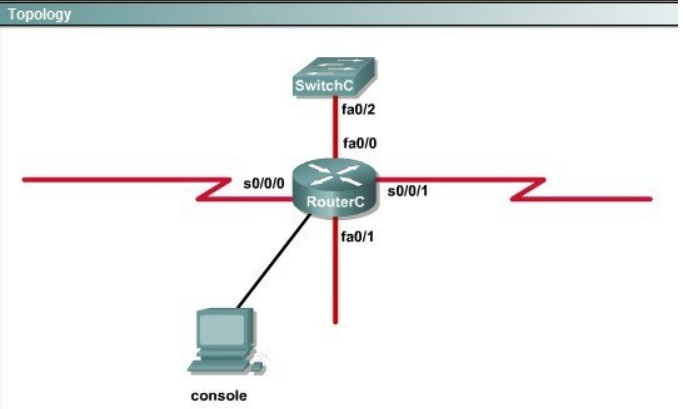
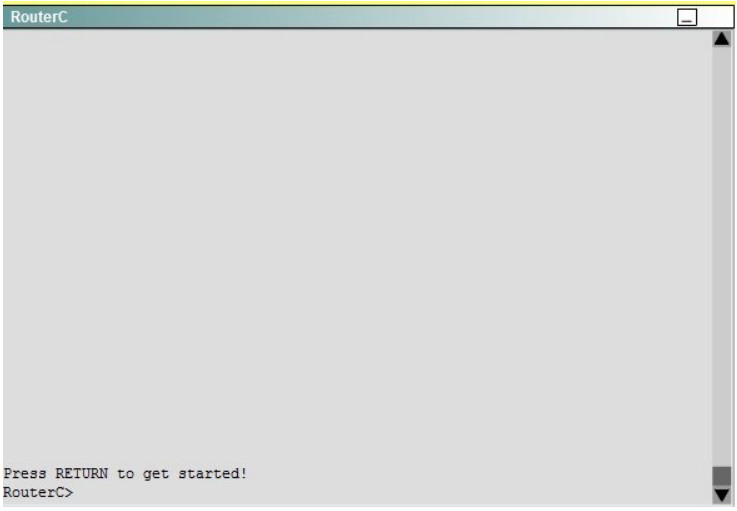
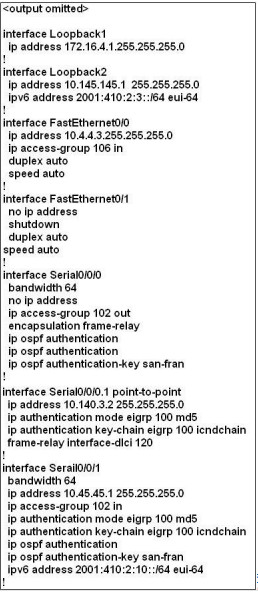
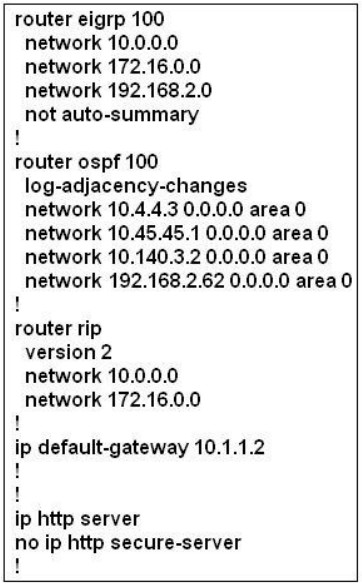
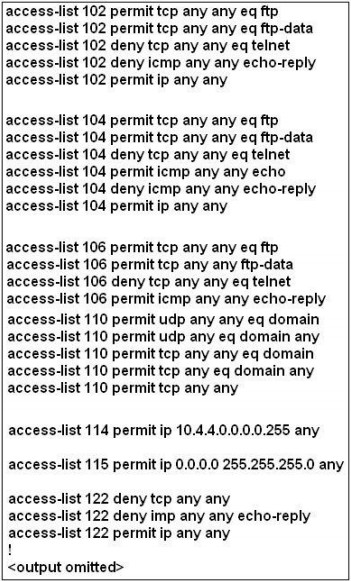 What would be the effect of issuing the command ip access-group 114 in to the fa0/0 interface? Correct
What would be the effect of issuing the command ip access-group 114 in to the fa0/0 interface? Correct
Incorrect
Hint
Explanation: From the output of access-list 114: access-list 114 permit ip 10.4.4.0 0.0.0.255 any we can easily understand that this access list allows all traffic (ip) from 10.4.4.0/24 network. -
Question 84 of 208
84. Question
1 pointsHotspot Question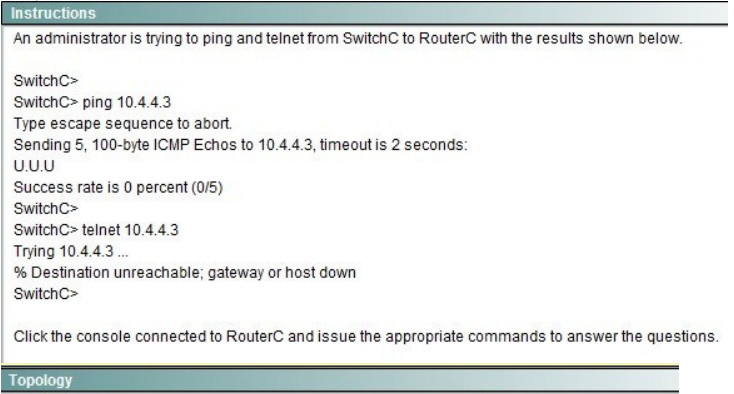
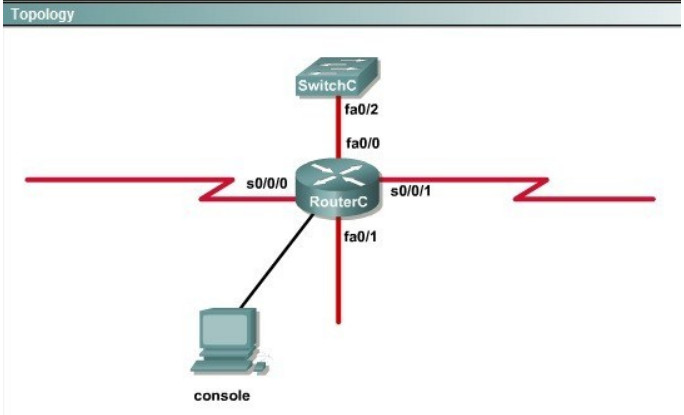
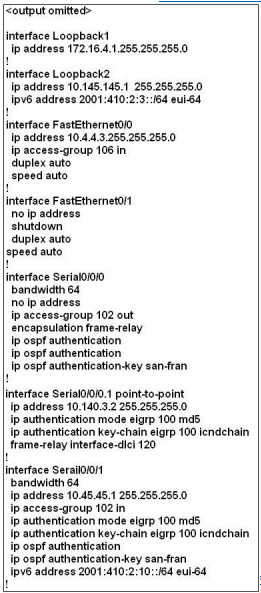
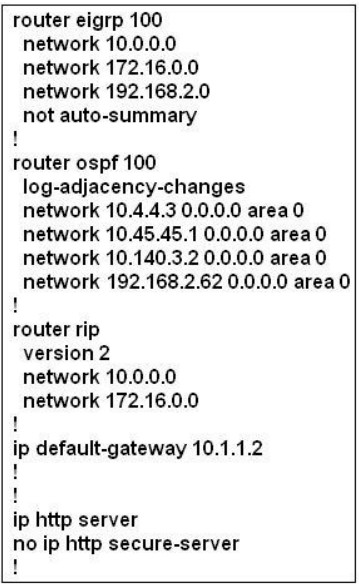
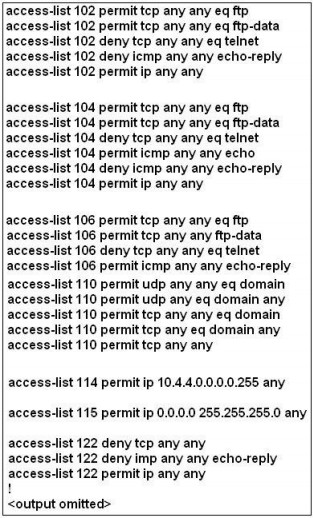 What would be the effect of Issuing the command ip access-group 115 in on the s0/0/1 interface? Correct
What would be the effect of Issuing the command ip access-group 115 in on the s0/0/1 interface? Correct
Incorrect
Hint
Explanation: First let’s see what was configured on interface S0/0/1:
-
Question 85 of 208
85. Question
1 pointsRefer to the exhibit. Based on the information given, which switch will be elected root bridge and why?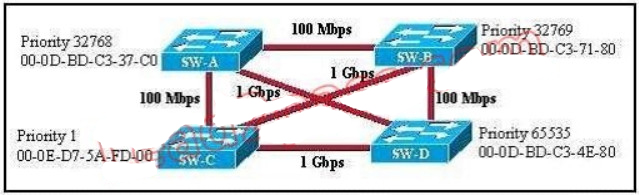 Correct
Correct
Incorrect
-
Question 86 of 208
86. Question
1 pointsIn a switched environment, what does the IEEE 802.1Q standard describe?Correct
Incorrect
Hint
Explanation: A broadcast domain must sometimes exist on more than one switch in the network. To accomplish this, one switch must send frames to another switch and indicate which VLAN a particular frame belongs to. On Cisco switches, a trunk link is created to accomplish this VLAN identification. ISL and IEEE 802.1Q are different methods of putting a VLAN identifier in a Layer 2 frame. The IEEE 802.1Q protocol interconnects VLANs between multiple switches, routers, and servers. With 802.1Q, a network administrator can define a VLAN topology to span multiple physical devices. Cisco switches support IEEE 802.1Q for FastEthernet and Gigabit Ethernet interfaces. An 802.1Q trunk link provides VLAN identification by adding a 4-byte tag to an Ethernet Frame as it leaves a trunk port. -
Question 87 of 208
87. Question
1 pointsWhat are three benefits of GLBP? (Choose three.)Correct
Incorrect
-
Question 88 of 208
88. Question
1 pointsWhich three statements about HSRP operation are true? (Choose three.)Correct
Incorrect
Hint
Explanation: The virtual MAC address of HSRP version 1 is 0000.0C07.ACxx, where xx is the HSRP group number in hexadecimal based on the respective interface. For example, HSRP group 10 uses the HSRP virtual MAC address of 0000.0C07.AC0A. HSRP version 2 uses a virtual MAC address of 0000.0C9F.FXXX (XXX: HSRP group in hexadecimal) -
Question 89 of 208
89. Question
1 pointsWhich three statements about Syslog utilization are true? (Choose three.)Correct
Incorrect
-
Question 90 of 208
90. Question
1 pointsA network administrator enters the following command on a router: logging trap 3. What are three message types that will be sent to the Syslog server? (Choose three.)Correct
Incorrect
-
Question 91 of 208
91. Question
1 pointsWhat is the default Syslog facility level?Correct
Incorrect
-
Question 92 of 208
92. Question
1 pointsWhat command instructs the device to timestamp Syslog debug messages in milliseconds?Correct
Incorrect
Hint
Explanation: The “service timestamps debug” command configures the system to apply a time stamp to debugging messages. The time-stamp format for datetime is MMM DD HH:MM:SS, where MMM is the month, DD is the date, HH is the hour (in 24-hour notation), MM is the minute, and SS is the second. With the additional keyword msec, the system includes milliseconds in the time stamp, in the format HH:DD:MM:SS.mmm, where .mmm is milliseconds -
Question 93 of 208
93. Question
1 pointsRefer to the exhibit. What is the cause of the Syslog output messages?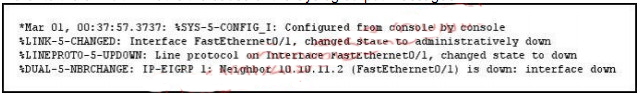 Correct
Correct
Incorrect
-
Question 94 of 208
94. Question
1 pointsWhat are three components that comprise the SNMP framework? (Choose three.)Correct
Incorrect
-
Question 95 of 208
95. Question
1 pointsWhat are three components that comprise the SNMP framework? (Choose three.)Correct
Incorrect
-
Question 96 of 208
96. Question
1 pointsWhat SNMP message alerts the manager to a condition on the network?Correct
Incorrect
-
Question 97 of 208
97. Question
1 pointsWhat Netflow component can be applied to an interface to track IPv4 traffic?Correct
Incorrect
Hint
Explanation: Flow monitors are the Flexible NetFlow component that is applied to interfaces to perform network traffic monitoring. Flow monitors consist of a record and a cache. You add the record to the flow monitor after youcreate the flow monitor. The flow monitor cache is automatically created at the time the flow monitor is applied to the first interface. Flow data is collected from the network traffic during the monitoring process based on the key and nonkey fields in the record, which is configured for the flow monitor and stored in the flow monitor cache. For example, the following example creates a flow monitor named FLOW-MONITOR-1 and enters Flexible NetFlow flow monitor configuration mode: Router(config)# flow monitor FLOW-MONITOR-1 Router(config-flow-monitor)# -
Question 98 of 208
98. Question
1 pointsWhat Cisco IOS feature can be enabled to pinpoint an application that is causing slow network performance?Correct
Incorrect
-
Question 99 of 208
99. Question
1 pointsWhat command visualizes the general NetFlow data on the command line?Correct
Incorrect
Hint
Explanation: The “show ip cache flow” command displays a summary of the NetFlow
-
Question 100 of 208
100. Question
1 pointsWhat are three values that must be the same within a sequence of packets for Netflow to consider them a network flow? (Choose three.)Correct
Incorrect
-
Question 101 of 208
101. Question
1 pointsRefer to the exhibit. A network administrator is configuring an EtherChannel between SW1 and SW2. The SW1 configuration is shown. What is the correct configuration for SW2?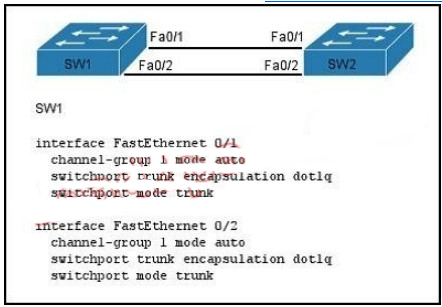 Correct
Correct
Incorrect
-
Question 102 of 208
102. Question
1 pointsWhat are three factors a network administrator must consider before implementing Netflow in the network? (Choose three.)Correct
Incorrect
-
Question 103 of 208
103. Question
1 pointsWhich two statements about the OSPF Router ID are true? (Choose two.)Correct
Incorrect
-
Question 104 of 208
104. Question
1 pointsWhat parameter can be different on ports within an EtherChannel?Correct
Incorrect
-
Question 105 of 208
105. Question
1 pointsWhat are two benefits of using a single OSPF area network design? (Choose two.)Correct
Incorrect
-
Question 106 of 208
106. Question
1 pointsRefer to the exhibit. What set of commands was configured on interface Fa0/3 to produce the given output?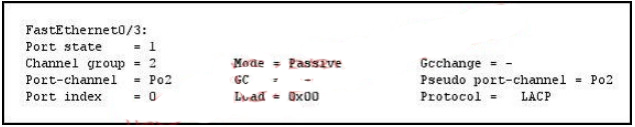 Correct
Correct
Incorrect
-
Question 107 of 208
107. Question
1 pointsRefer to the exhibit. If the devices produced the given output, what is the cause of the EtherChannel problem?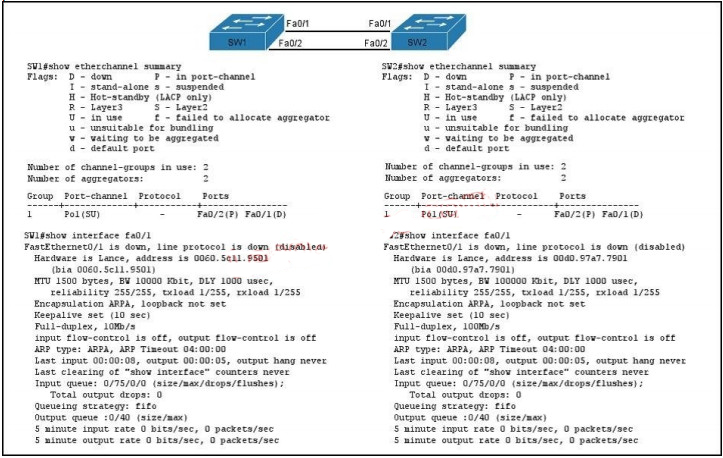 Correct
Correct
Incorrect
-
Question 108 of 208
108. Question
1 pointsWhat are two enhancements that OSPFv3 supports over OSPFv2? (Choose two.)Correct
Incorrect
-
Question 109 of 208
109. Question
1 pointsWhen a router undergoes the exchange protocol within OSPF, in what order does it pass through each state?Correct
Incorrect
-
Question 110 of 208
110. Question
1 pointsA network administrator creates a layer 3 EtherChannel, bundling four interfaces into channel group 1. On what interface is the IP address configured?Correct
Incorrect
-
Question 111 of 208
111. Question
1 pointsRefer to the exhibit. If the router Cisco returns the given output and has not had its router ID set manually, what value will OSPF use as its router ID?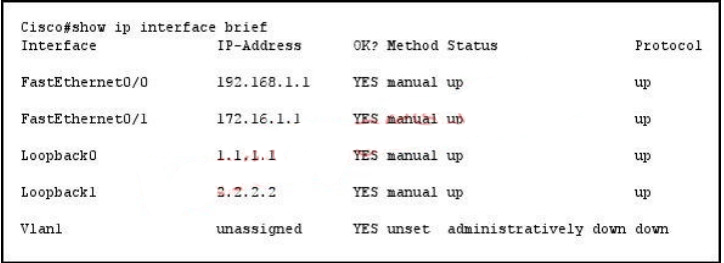 Correct
Correct
Incorrect
-
Question 112 of 208
112. Question
1 pointsWhat command sequence will configure a router to run OSPF and add network 10.1.1.0 /24 to area 0?Correct
Incorrect
-
Question 113 of 208
113. Question
1 pointsWhat OSPF command, when configured, will include all interfaces into area 0?Correct
Incorrect
-
Question 114 of 208
114. Question
1 pointsWhich statement describes the process ID that is used to run OSPF on a router?Correct
Incorrect
-
Question 115 of 208
115. Question
1 pointsWhich three are the components of SNMP? (Choose three)Correct
Incorrect
Explanation: SNMP is an application-layer protocol that provides a message format for communication between SNMP managers and agents. SNMP provides a standardized framework and a common language used for the monitoring and management of devices in a network. The SNMP framework has three parts: + An SNMP manager + An SNMP agent + A Management Information Base (MIB) The SNMP manager is the system used to control and monitor the activities of network hosts using SNMP. The most common managing system is called a Network Management System (NMS). The term NMS can be applied to either a dedicated device used for network management, or the applications used on such a device. A variety of network management applications are available for use with SNMP. These features range from simple command-line applications to feature-rich graphical user interfaces (such as the CiscoWorks2000 line of products). The SNMP agent is the software component within the managed device that maintains the data for the device and reports these data, as needed, to managing systems. The agent and MIB reside on the routing device (router, access server, or switch). To enable the SNMP agent on a Cisco routing device, you must define the relationship between the manager and the agent. The Management Information Base (MIB) is a virtual information storage area for network management information, which consists of collections of managed objects.
Hint
-
Question 116 of 208
116. Question
1 pointsWhat are the Popular destinations for syslog messages to be saved?Correct
Incorrect
Hint
Explanation: By default, switches send the output from system messages and debug privileged EXEC commands to a logging process. The logging process controls the distribution of logging messages to various destinations, such as the logging buffer (on RAM), terminal lines (console terminal), or a UNIX syslog server, depending on your configuration. The process also sends messages to the console. Note: Syslog messages can be written to a file in Flash memory although it is not a popular place to use. We can configure this feature with the command logging file flash:filename. -
Question 117 of 208
117. Question
1 pointsSyslog was configured with a level 3 trap. Which 4 types of logs would be generated (choose four)Correct
Incorrect
Hint
Explanation: The Message Logging is divided into 8 levels as listed below: Level Keyword Description 0 emergencies System is unusable 1 alerts Immediate action is needed 2 critical Critical conditions exist 3 errors Error conditions exist 4 warnings Warning conditions exist 5 notification Normal, but significant, conditions exist 6 informational Informational messages 7 debugging Debugging messages The highest level is level 0 (emergencies). The lowest level is level 7. If you specify a level with the “logging console level” command, that level and all the higher levels will be displayed. For example, by using the “logging console warnings” command, all the logging of emergencies, alerts, critical, errors, warnings will be displayed. -
Question 118 of 208
118. Question
1 pointsWhat are the benefit of using Netflow? (Choose three.)Correct
Incorrect
-
Question 119 of 208
119. Question
1 pointsWhich protocol can cause overload on a CPU of a managed device?Correct
Incorrect
Hint
Explanation: Sometimes, messages like this might appear in the router console: %SNMP-3-CPUHOG: Processing [chars] of [chars] They mean that the SNMP agent on the device has taken too much time to process a request. You can determine the cause of high CPU use in a router by using the output of the show process cpu command. Note: A managed device is a part of the network that requires some form of monitoring and management (routers, switches, servers, workstations, printers…). -
Question 120 of 208
120. Question
1 pointsWhat are the three things that the Netflow uses to consider the traffic to be in a same flow?Correct
Incorrect
Hint
Explanation: What is an IP Flow? Each packet that is forwarded within a router or switch is examined for a set of IP packet attributes. These attributes are the IP packet identity or fingerprint of the packet and determine if the packet is unique or similar to other packets. Traditionally, an IP Flow is based on a set of 5 and up to 7 IP packet attributes. IP Packet attributes used by NetFlow: + IP source address + IP destination address + Source port + Destination port + Layer 3 protocol type + Class of Service + Router or switch interface -
Question 121 of 208
121. Question
1 pointsWhat is the alert message generated by SNMP agents called ?Correct
Incorrect
Hint
Explanation: A TRAP is a SNMP message sent from one application to another (which is typically on a remote host). Their purpose is merely to notify the other application that something has happened, has been noticed, etc. The big problem with TRAPs is that they’re unacknowledged so you don’t actually know if the remote application received your oh-so-important message to it. SNMPv2 PDUs fixed this by introducing the notion of an INFORM, which is nothing more than an acknowledged TRAP. -
Question 122 of 208
122. Question
1 pointsWhat are three reasons to collect Netflow data on a company network? (Choose three.)Correct
Incorrect
-
Question 123 of 208
123. Question
1 pointsWhich three statements about the features of SNMPv2 and SNMPv3 are true? (Choose three.)Correct
Incorrect
-
Question 124 of 208
124. Question
1 pointsWhat authentication type is used by SNMPv2?Correct
Incorrect
-
Question 125 of 208
125. Question
1 pointsWhich three features are added in SNMPv3 over SNMPv2?Correct
Incorrect
-
Question 126 of 208
126. Question
1 pointsIn a GLBP network, who is responsible for the arp request?Correct
Incorrect
-
Question 127 of 208
127. Question
1 pointsWhat levels will be trapped if the administrator executes the command router(config)# logging trap 4 (Choose four) ?Correct
Incorrect
Hint
Explanation: The Message Logging is divided into 8 levels as listed below: Level Keyword Description 0 emergencies System is unusable 1 alerts Immediate action is needed 2 critical Critical conditions exist 3 errors Error conditions exist 4 warnings Warning conditions exist 5 notification Normal, but significant, conditions exist 6 informational Informational messages 7 debugging Debugging messages If you specify a level with the “logging trap level” command, that level and all the higher levels will be logged. For example, by using the “logging trap 4 command, all the logging of emergencies, alerts, critical, errors, warnings will be logged. -
Question 128 of 208
128. Question
1 pointsHotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.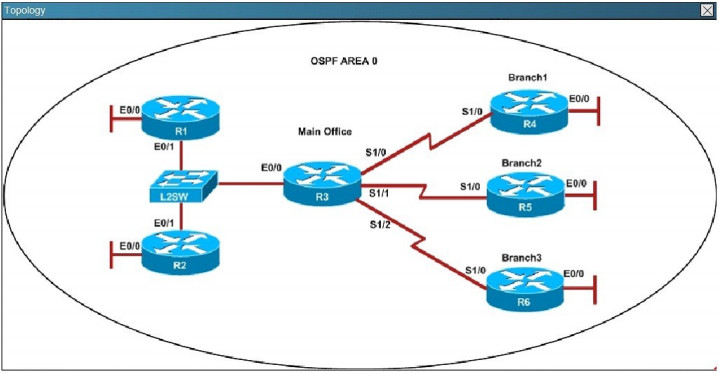 An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branchl office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branchl office. What is causing the problem? Correct
Incorrect
Hint
Explanation: A show running-config command on R3 and R4 shows that R4 is incorrectly configured for area 2:
-
Question 129 of 208
129. Question
1 pointsHotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.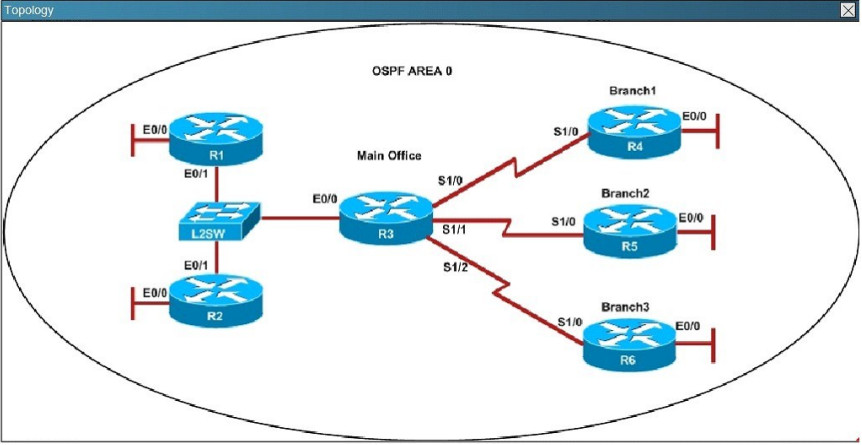 R1 does not form an OSPF neighbor adjacency with R2. Which option would fix the issue? Correct
R1 does not form an OSPF neighbor adjacency with R2. Which option would fix the issue? Correct
Incorrect
Hint
Explanation: Looking at the configuration of R1, we see that R1 is configured with a hello interval of 25 on interface Ethernet 0/1 while R2 is left with the default of 10 (not configured).
-
Question 130 of 208
130. Question
1 pointsHotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.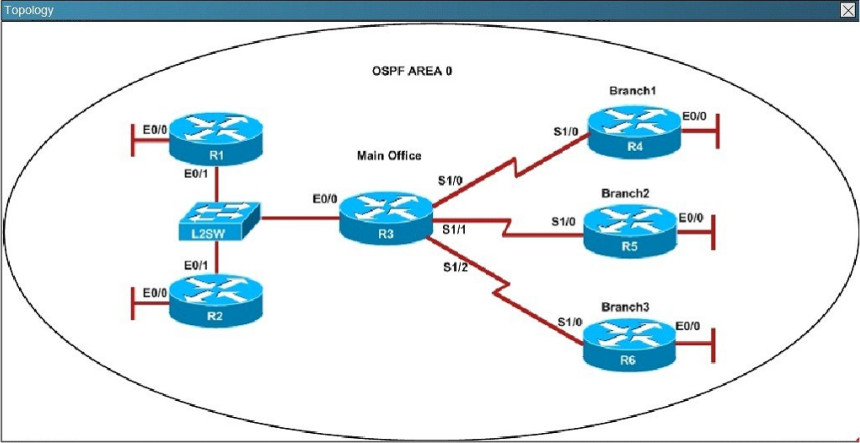 An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
Incorrect
Hint
Explanation: Using the show running-config command we see that R6 has been incorrectly configured with the same router ID as R3 under the router OSPF process.
-
Question 131 of 208
131. Question
1 pointsHotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues.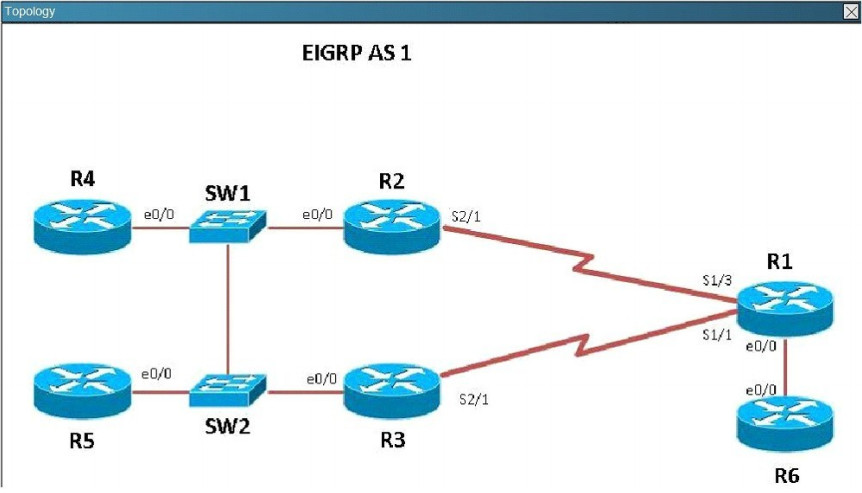 The loopback interfaces on R4 with the IP addresses of 10.4.4.4 /32, 10.4.4.5/32. and 10.4.4.6/32 are not appearing in the routing table of R5 Why are the interfaces missing? Correct
The loopback interfaces on R4 with the IP addresses of 10.4.4.4 /32, 10.4.4.5/32. and 10.4.4.6/32 are not appearing in the routing table of R5 Why are the interfaces missing? Correct
Incorrect
Hint
Explanation: For an EIGRP neighbor to form, the following must match: – Neighbors must be in the same subnet- K values- AS numbers- Authentication method and key strings Here, we see that R4 is configured for EIGRP AS 2, when it should be AS 1.
-
Question 132 of 208
132. Question
1 pointsHotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues. Which path does traffic take from R1 to R5? Correct
Which path does traffic take from R1 to R5? Correct
Incorrect
Hint
Explanation: Using the “show ip int brief command” on R5 we can see the IP addresses assigned to this router. Then, using the “show ip route” command on R1 we can see that to reach 10.5.5.5 and 10.5.5.55 the preferred path is via Serial 1/3, which we see from the diagram is the link to R2.
-
Question 133 of 208
133. Question
1 pointsHotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues. Router R6 does not form an EIGRP neighbor relationship correctly with router R1.
What is the cause for this misconfiguration? Correct
Router R6 does not form an EIGRP neighbor relationship correctly with router R1.
What is the cause for this misconfiguration? Correct
Incorrect
Hint
Explanation: The link from R1 to R6 is shown below: As you can see, they are both using e0/0. The IP addresses are in the 192.168.16.0 network:
As you can see, they are both using e0/0. The IP addresses are in the 192.168.16.0 network:
 But when we look at the EIGRP configuration, the “network 192.168.16.0” command is missing on R6.
But when we look at the EIGRP configuration, the “network 192.168.16.0” command is missing on R6.
 Study the following output taken on R1:
R1# Ping 10.5.5.55 source 10.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.5.5.55, timeout is 2 seconds:
Packet sent with a source address of 10.1.1.1
…….
Success rate is 0 percent (0/5)
Study the following output taken on R1:
R1# Ping 10.5.5.55 source 10.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.5.5.55, timeout is 2 seconds:
Packet sent with a source address of 10.1.1.1
…….
Success rate is 0 percent (0/5) -
Question 134 of 208
134. Question
1 pointsHotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues.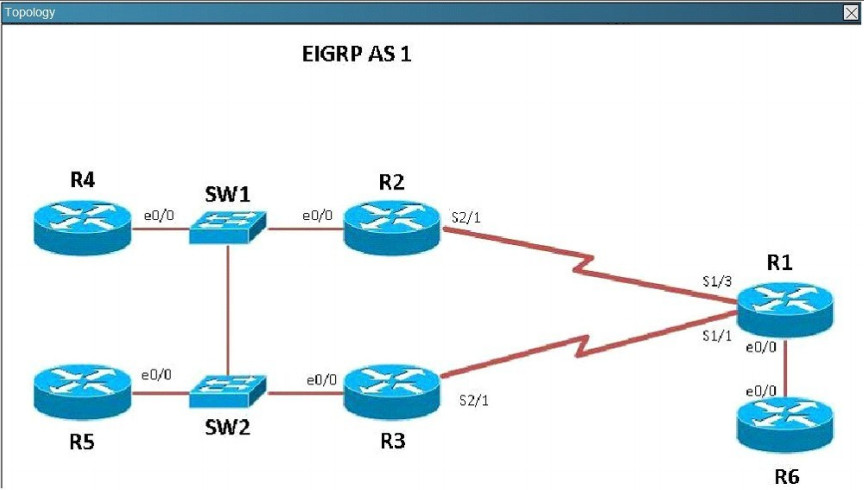 Why are the pings failing? Correct
Why are the pings failing? Correct
Incorrect
Hint
Explanation: R5 does not have a route to the 10.1.1.1 network, which is the loopback0 IP address of R1. When looking at the EIGRP configuration on R1, we see that the 10.1.1.1 network statement is missing on R1.
-
Question 135 of 208
135. Question
1 pointsWhat is a valid HSRP virtual MAC address?Correct
Incorrect
Hint
Explanation: With HSRP, two or more devices support a virtual router with a fictitious MAC address and unique IP address. There are two version of HSRP. + With HSRP version 1, the virtual router’s MAC address is 0000.0c07.ACxx , in which xx is the HSRP group. + With HSRP version 2, the virtual MAC address if 0000.0C9F.Fxxx, in which xxx is the HSRP group. Note: Another case is HSRP for IPv6, in which the MAC address range from 0005.73A0.0000 through 0005.73A0.0FFF. -
Question 136 of 208
136. Question
1 pointsIn GLBP, which router will respond to client ARP requests?Correct
Incorrect
Hint
Explanation: One disadvantage of HSRP and VRRP is that only one router is in use, other routers must wait for the primary to fail because they can be used. However, Gateway Load Balancing Protocol (GLBP) can use of up to four routers simultaneously. In GLBP, there is still only one virtual IP address but each router has a different virtual MAC address. First a GLBP group must elect an Active Virtual Gateway (AVG). The AVG is responsible for replying ARP requests from hosts/clients. It replies with different virtual MAC addresses that correspond to different routers (known as Active Virtual Forwarders – AVFs) so that clients can send traffic to different routers in that GLBP group (load sharing). -
Question 137 of 208
137. Question
1 pointsWhich statement describes VRRP object tracking?Correct
Incorrect
Hint
Explanation: Object tracking is the process of tracking the state of a configured object and uses that state to determine the priority of the VRRP router in a VRRP group -
Question 138 of 208
138. Question
1 pointsWhat is a global command?Correct
Incorrect
Hint
Explanation: When you enter global configuration mode and enter a command, it is applied to the running configuration file that is currently running in ram. The configuration of a global command affects the entire router. An example of a global command is one used for the hostname of the router. -
Question 139 of 208
139. Question
1 pointsAn administrator is unsuccessful in adding VLAN 50 to a switch. While troubleshooting the problem, the administrator views the output of the show vtp status command, which is displayed in the graphic. What commands must be issued on this switch to add VLAN 50 to the database? (Choose two.)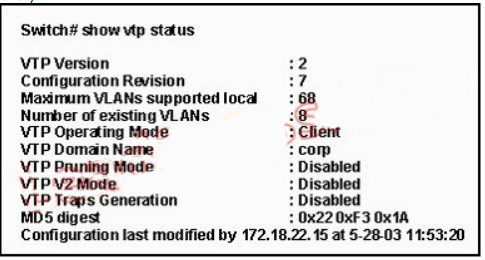 Correct
Correct
Incorrect
-
Question 140 of 208
140. Question
1 pointsWhich of the following IP addresses fall into the CIDR block of 115.64.4.0/22? (Choose three.)Correct
Incorrect
-
Question 141 of 208
141. Question
1 pointsWhich of the following are types of flow control? (Choose three.)Correct
Incorrect
-
Question 142 of 208
142. Question
1 pointsRefer to the exhibit. After a RIP route is marked invalid on Router_1, how much time will elapse before that route is removed from the routing table?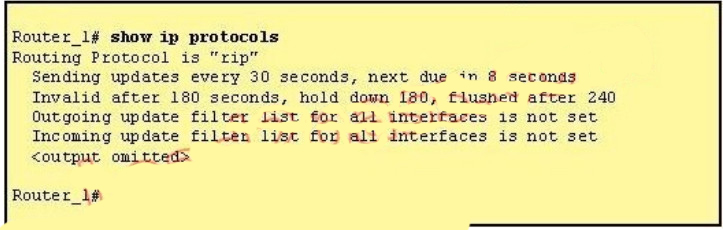 Correct
Correct
Incorrect
-
Question 143 of 208
143. Question
1 pointsRefer to the exhibit. A network associate has configured the internetwork that is shown in the exhibit, but has failed to configure routing properly.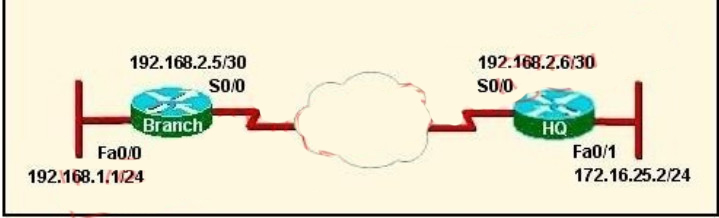 Which configuration will allow the hosts on the Branch LAN to access resources on the HQ LAN with the least impact on router processing and WAN bandwidth? Correct
Which configuration will allow the hosts on the Branch LAN to access resources on the HQ LAN with the least impact on router processing and WAN bandwidth? Correct
Incorrect
-
Question 144 of 208
144. Question
1 pointsWhich additional configuration step is necessary in order to connect to an access point that has SSID broadcasting disabled?Correct
Incorrect
-
Question 145 of 208
145. Question
1 pointsWhat is one reason that WPA encryption is preferred over WEP?Correct
Incorrect
-
Question 146 of 208
146. Question
1 pointsAll WAN links inside the ABC University network use PPP with CHAP for authentication security. Which command will display the CHAP authentication process as it occur between two routers in the network?Correct
Incorrect
-
Question 147 of 208
147. Question
1 pointsRefer to the exhibit. The network is converged. After link-state advertisements are received from Router_A, what information will Router_E contain in its routing table for the subnets 208.149.23.64 and 208.149.23.96?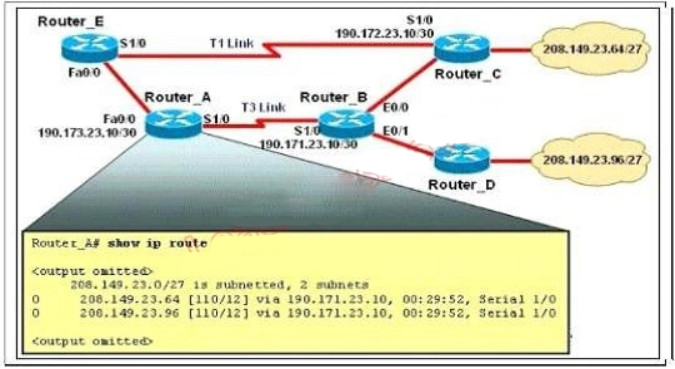 Correct
Correct
Incorrect
-
Question 148 of 208
148. Question
1 pointsWhat are two characteristics of SSH? (Choose two.)Correct
Incorrect
-
Question 149 of 208
149. Question
1 pointsRefer to the exhibit. The access list has been configured on the S0/0 interface of router RTB in the outbound direction. Which two packets, if routed to the interface, will be denied? (Choose two.) access-list 101 deny tcp 192.168.15.32 0.0.0.15 any eq telnet access-list 101 permit ip any any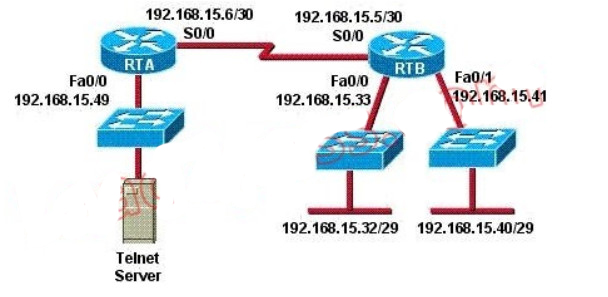 Correct
Correct
Incorrect
-
Question 150 of 208
150. Question
1 pointsRefer to the graphic. It has been decided that Workstation 1 should be denied access to Server1. Which of the following commands are required to prevent only Workstation 1 from accessing Server1 while allowing all other traffic to flow normally? (Choose two.) Correct
Correct
Incorrect
-
Question 151 of 208
151. Question
1 pointsAn access list was written with the four statements shown in the graphic. Which single access list statement will combine all four of these statements into a single statement that will have exactly the same effect?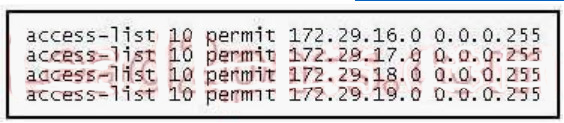 Correct
Correct
Incorrect
-
Question 152 of 208
152. Question
1 pointsA network administrator wants to add a line to an access list that will block only Telnet access by the hosts on subnet 192.168.1.128/28 to the server at 192.168.1.5. What command should be issued to accomplish this task?Correct
Incorrect
-
Question 153 of 208
153. Question
1 pointsAs a network administrator, you have been instructed to prevent all traffic originating on the LAN from entering the R2 router. Which the following command would implement the access list on the interface of the R2 router?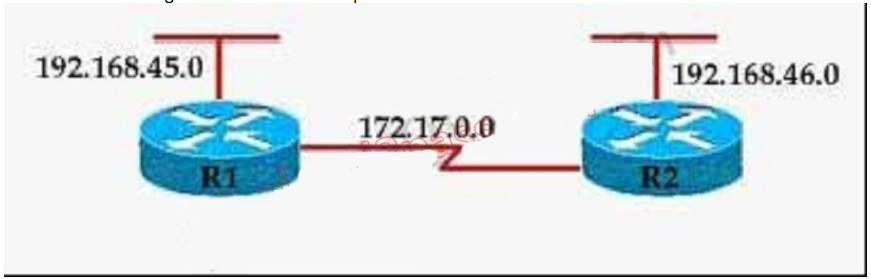 Correct
Correct
Incorrect
-
Question 154 of 208
154. Question
1 pointsThe access control list shown in the graphic has been applied to the Ethernet interface of router R1 using the ip access-group 101 in command. Which of the following Telnet sessions will be blocked by this ACL? (Choose two.)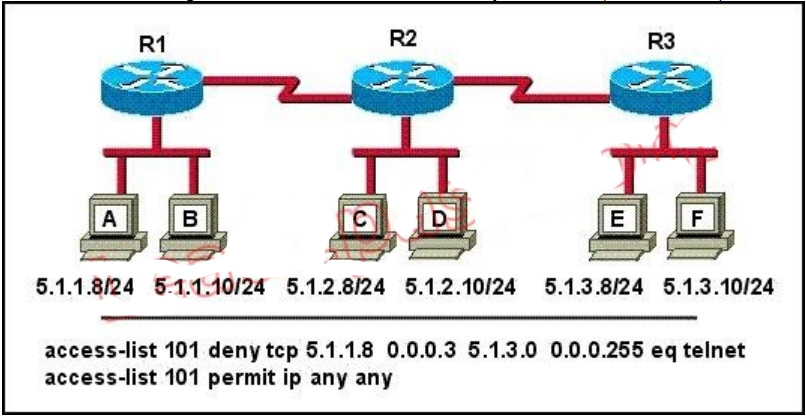 Correct
Correct
Incorrect
-
Question 155 of 208
155. Question
1 pointsThe following access list below was applied outbound on the E0 interface connected to the 192.169.1.8/29 LAN: access-list 135 deny tcp 192.169.1.8 0.0.0.7 eq 20 any access-list 135 deny tcp 192.169.1.8 0.0.0.7 eq 21 any How will the above access lists affect traffic?Correct
Incorrect
-
Question 156 of 208
156. Question
1 pointsThe following configuration line was added to router R1 Access-list 101 permit ip 10.25.30.0 0.0.0.255 any. What is the effect of this access list configuration?Correct
Incorrect
-
Question 157 of 208
157. Question
1 pointsA default Frame Relay WAN is classified as what type of physical network?Correct
Incorrect
-
Question 158 of 208
158. Question
1 pointsWhich of the following are key characteristics of PPP? (Choose three.)Correct
Incorrect
-
Question 159 of 208
159. Question
1 pointsHow should a router that is being used in a Frame Relay network be configured to avoid split horizon issues from preventing routing updates?Correct
Incorrect
-
Question 160 of 208
160. Question
1 pointsThe Frame Relay network in the diagram is not functioning properly. What is the cause of the problem?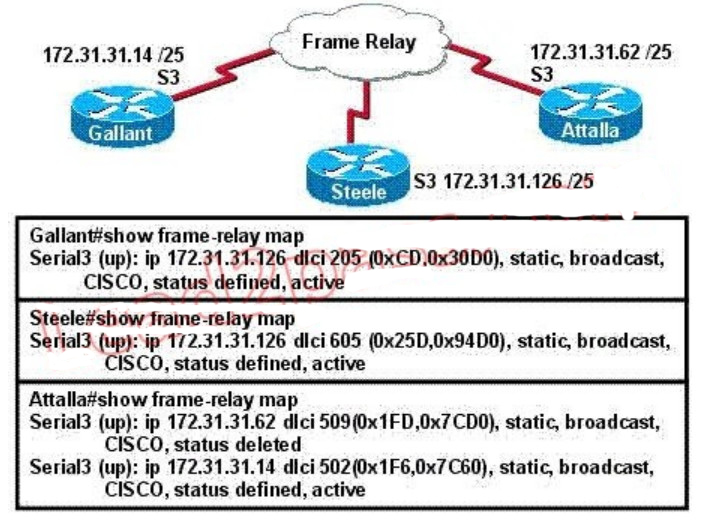 Correct
Correct
Incorrect
-
Question 161 of 208
161. Question
1 pointsAs a CCNA candidate, you must have a firm understanding of the IPv6 address structure. Refer to IPv6 address, could you tell me how many bits are included in each filed?Correct
Incorrect
-
Question 162 of 208
162. Question
1 pointsRefer to the exhibit. How many broadcast domains exist in the exhibited topology?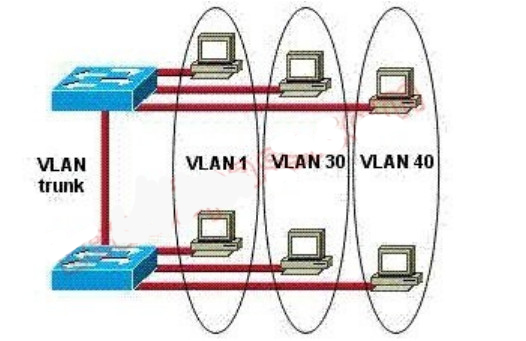 Correct
Correct
Incorrect
-
Question 163 of 208
163. Question
1 pointsRefer to the exhibit. The network administrator has created a new VLAN on Switch1 and added host C and host D. The administrator has properly configured switch interfaces FastEthernet0/13 throughFastEthernet0/14 to be members of the new VLAN. However, after the network administrator completed the configuration, host A could communicate with host B, but host A could not communicate with host C or host D. Which commands are required to resolve this problem?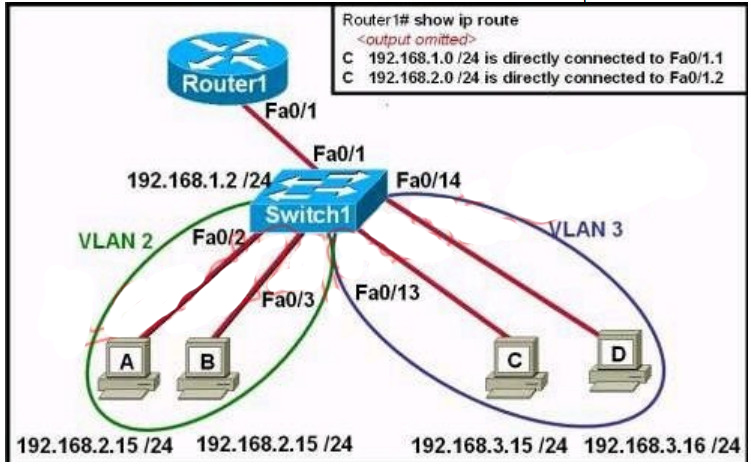 Correct
Correct
Incorrect
-
Question 164 of 208
164. Question
1 pointsOn a network of one department, there are four PCs connected to a switch, as shown in the following figure: After the Switch1 restarts. Host A ( the host on the left ) sends the first frame to Host C (the host on the right). What the first thing should the switch do? Correct
Correct
Incorrect
-
Question 165 of 208
165. Question
1 pointsRefer to the exhibit. The network administrator is in a campus building distant from Building B. WANRouter is hosting a newly installed WAN link on interface S0/0. The new link is not functioning and the administrator needs to determine if the correct cable has been attached to the S0/0 interface. How can the administrator accurately verify the correct cable type on S0/0 in the most efficient manner?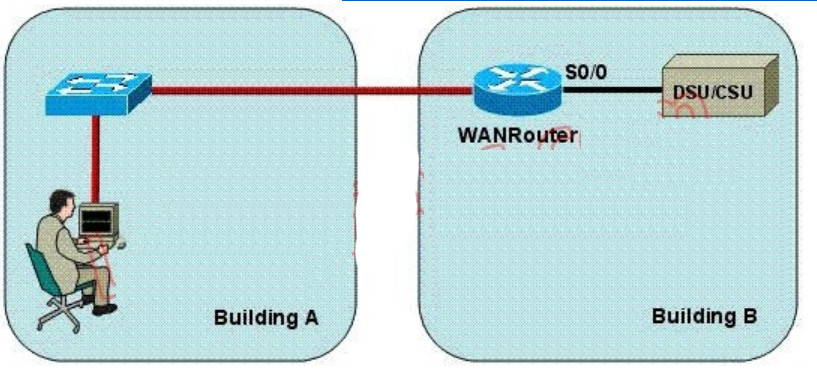 Correct
Correct
Incorrect
-
Question 166 of 208
166. Question
1 pointsWhile troubleshooting a connectivity issue from a PC you obtain the following information: Local PC IP address: 10.0.0.35/24 Default Gateway: 10.0.0.1 Remote Sever: 10.5.75.250/24 You then conduct the following tests from the local PC: Ping 127.0.0.1 – Successful Ping 10.0.0.35 – Successful Ping 10.0.0.1 – Unsuccessful Ping 10.5.75.250 – Unsuccessful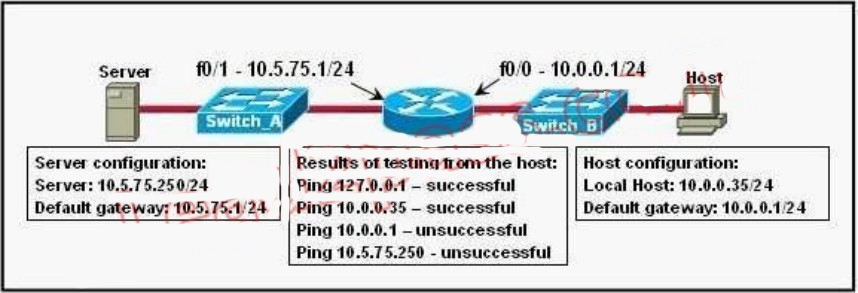 Correct
Correct
Incorrect
-
Question 167 of 208
167. Question
1 pointsA network administrator is troubleshooting the OSPF configuration of routers R1 and R2. The routers cannot establish an adjacency relationship on their common Ethernet link. The graphic shows the output of the show ip ospf interface e0 command for routers R1 and R2.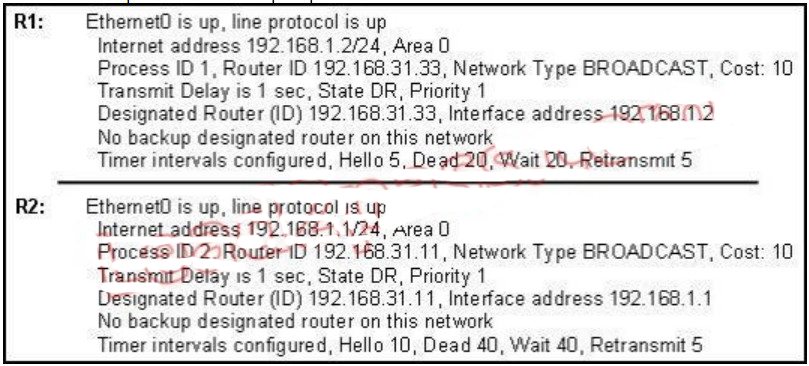 Based on the information in the graphic, what is the cause of this problem? Correct
Based on the information in the graphic, what is the cause of this problem? Correct
Incorrect
-
Question 168 of 208
168. Question
1 pointsThis graphic shows the results of an attempt to open a Telnet connection to router ACCESS1 from router Remote27.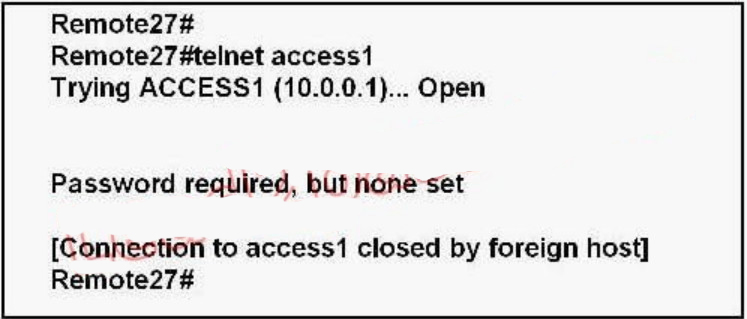 Which of the following command sequences will correct this problem? Correct
Which of the following command sequences will correct this problem? Correct
Incorrect
-
Question 169 of 208
169. Question
1 pointsWhen upgrading the IOS image, the network administrator receives the exhibited error message.'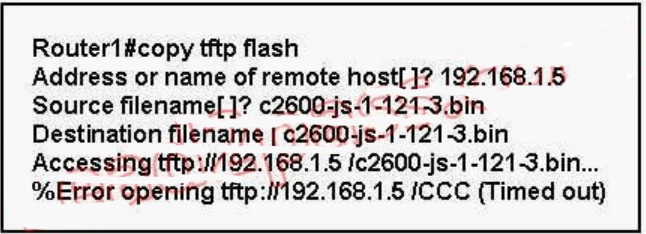 What could be the cause of this error? Correct
What could be the cause of this error? Correct
Incorrect
-
Question 170 of 208
170. Question
1 pointsRefer to the exhibit, Host A pings interface S0/0 on router 3, what is the TTL value for that ping? Correct
Correct
Incorrect
-
Question 171 of 208
171. Question
1 pointsWhich statement is true, as relates to classful or classless routing?Correct
Incorrect
-
Question 172 of 208
172. Question
1 pointsRefer to the exhibit. Why does the telnet connecting fail when a host attempts to connect a remote router?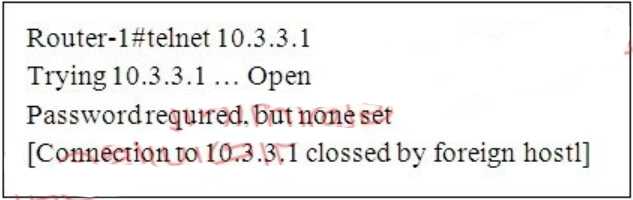 Correct
Correct
Incorrect
-
Question 173 of 208
173. Question
1 pointsWhich name describes an IPV6 host-enable tunneling technique that uses IPV4 UDP,does not require dedicated gateway tunnels,and can pass through existing IPV4 NAT gateways?Correct
Incorrect
-
Question 174 of 208
174. Question
1 pointsWhich pairing reflects a correct protocol-and-metric relationship?Correct
Incorrect
-
Question 175 of 208
175. Question
1 pointsRefer to the exhibit, The VLAN configuration of S1 is not being in this VTP enabled environment. The VTP and uplink port configurations for each switch are displayed. Which two command sets, if issued, resolve this failure and allow VTP to operate as expected?(choose two)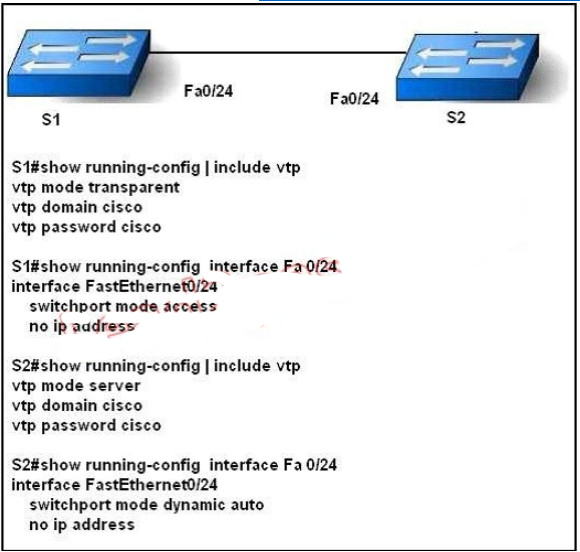 Correct
Correct
Incorrect
-
Question 176 of 208
176. Question
1 pointsHow are VTP advertisements delivered to switches across the network?Correct
Incorrect
-
Question 177 of 208
177. Question
1 pointsRefer to the exhibit. What could be possible causes for the “Serial0/0 is down” interface status? (Choose two.)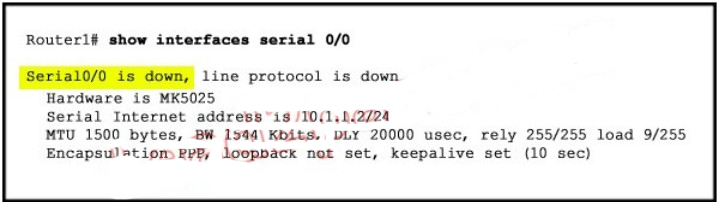 Correct
Correct
Incorrect
-
Question 178 of 208
178. Question
1 pointsRefer to the exhibit. Which two statements are true about the loopback address that is configured on RouterB? (Choose two.) Correct
Correct
Incorrect
-
Question 179 of 208
179. Question
1 pointsA network administrator is explaining VTP configuration to a new technician. What should the network administrator tell the new technician about VTP configuration? (Choose three.)Correct
Incorrect
-
Question 180 of 208
180. Question
1 pointsRefer to the exhibit. Both switches are using a default configuration. Which two destination addresses will host 4 use to send data to host 1? (Choose two.) Correct
Correct
Incorrect
-
Question 181 of 208
181. Question
1 pointsWhat are two reasons a network administrator would use CDP? (Choose two.)Correct
Incorrect
-
Question 182 of 208
182. Question
1 pointsRefer to the exhibit. The router has been configured with these commands: What are the two results of this configuration? (Choose two.)
What are the two results of this configuration? (Choose two.)
 Correct
Correct
Incorrect
-
Question 183 of 208
183. Question
1 pointsA company is installing IP phones. The phones and office computers connect to the same device. To ensure maximum throughput for the phone data, the company needs to make sure that the phone traffic is on a different network from that of the office computer data traffic. What is the best network device to which to directly connect the phones and computers, and what technology should be implemented on this device? (Choose two.)Correct
Incorrect
-
Question 184 of 208
184. Question
1 pointsWhat are two benefits of using VTP in a switching environment? (Choose two.)Correct
Incorrect
-
Question 185 of 208
185. Question
1 pointsWhich two statements are true about the command ip route 172.16.3.0 255.255.255.0 192.168.2.4? (Choose two.)Correct
Incorrect
-
Question 186 of 208
186. Question
1 pointsWhat are two advantages of Layer 2 Ethernet switches over hubs? (Choose two.)Correct
Incorrect
-
Question 187 of 208
187. Question
1 pointsRefer to the exhibit. A network associate needs to configure the switches and router in the graphic so that the hosts in VLAN3 and VLAN4 can communicate with the enterprise server in VLAN2. Which two Ethernet segments would need to be configured as trunk links? (Choose two.)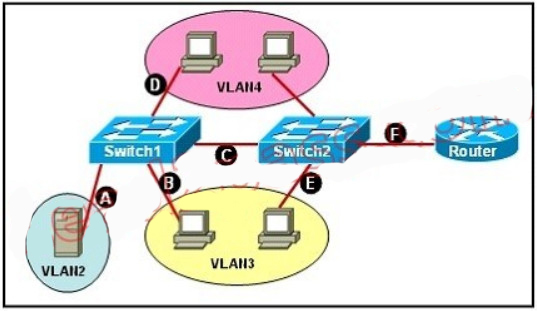 Correct
Correct
Incorrect
-
Question 188 of 208
188. Question
1 pointsWhich two values are used by Spanning Tree Protocol to elect a root bridge? (Choose two.)Correct
Incorrect
-
Question 189 of 208
189. Question
1 pointsRefer to the exhibit. The networks connected to router R2 have been summarized as a 192.168.176.0/21 route and sent to R1. Which two packet destination addresses will R1 forward to R2? (Choose two.)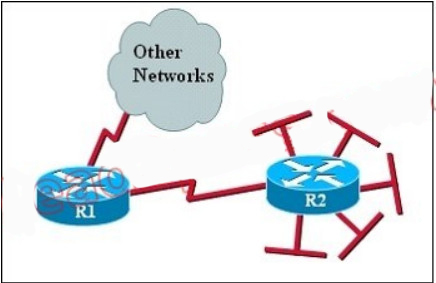 Correct
Correct
Incorrect
-
Question 190 of 208
190. Question
1 pointsWhich three statements are typical characteristics of VLAN arrangements? (Choose three.)Correct
Incorrect
-
Question 191 of 208
191. Question
1 pointsRefer to the exhibit. Which three statements are true about how router JAX will choose a path to the 10.1.3.0/24 network when different routing protocols are configured? (Choose three.)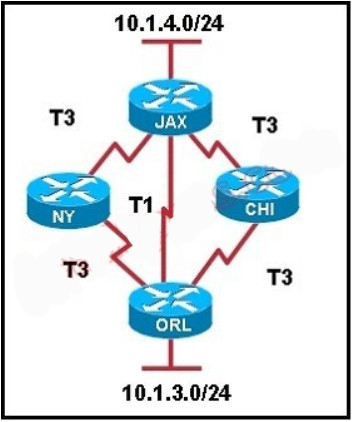 Correct
Correct
Incorrect
-
Question 192 of 208
192. Question
1 pointsRefer to the exhibit. Which three statements correctly describe Network Device A? (Choose three.)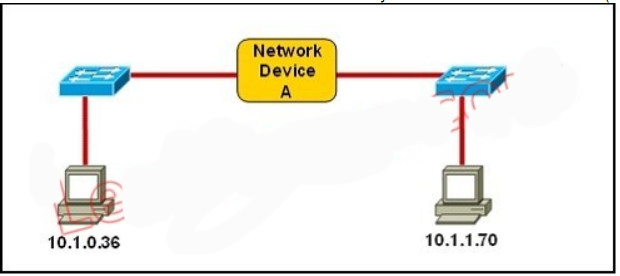 Correct
Correct
Incorrect
-
Question 193 of 208
193. Question
1 pointsSwitch ports operating in which two roles will forward traffic according to the IEEE 802.1w standard? (Choose two.)Correct
Incorrect
-
Question 194 of 208
194. Question
1 pointsRefer to the exhibit. Given the output shown from this Cisco Catalyst 2950, what is the most likely reason that interface FastEthernet 0/10 is not the root port for VLAN 2?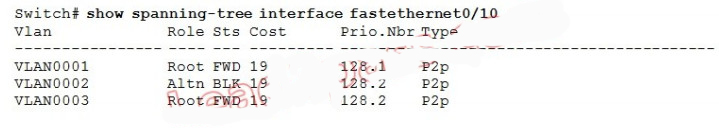 Correct
Correct
Incorrect
-
Question 195 of 208
195. Question
1 pointsRefer to the exhibit. This command is executed on 2960Switch: 2960Switch(config)# mac-address-table static 0000.00aa.aaaa vlan 10 interface fa0/1 Which two of these statements correctly identify results of executing the command? (Choose two.)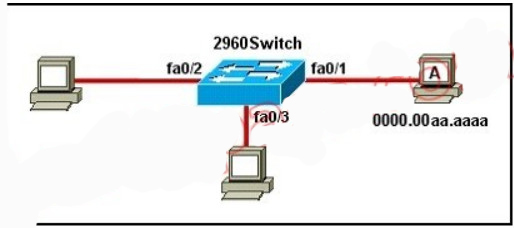 Correct
Correct
Incorrect
-
Question 196 of 208
196. Question
1 pointsWhich of the following describes the roles of devices in a WAN? (Choose three.)Correct
Incorrect
-
Question 197 of 208
197. Question
1 pointsWhat are two characteristics of Telnet? (Choose two.)Correct
Incorrect
-
Question 198 of 208
198. Question
1 pointsWhat are two security appliances that can be installed in a network? (Choose two.)Correct
Incorrect
-
Question 199 of 208
199. Question
1 pointsAssuming a subnet mask of 255.255.248.0, three of the following addresses are valid host addresses. Which are these addresses? (Choose three.)Correct
Incorrect
-
Question 200 of 208
200. Question
1 pointsDrag and Drop Question Drag the security feature on the left to the specific security ricks they he;p protect against on the right (not all optiond are used)Sort elements
- access group
- console password
- enable secret
- CHAP authentication
- VTY password
- service password encryption
-
VTY password
-
console password
-
access - group
-
service password encryption
-
enable secret
Correct
Incorrect
-
Question 201 of 208
201. Question
1 pointsDrag and drop question Routing has been configured on the local router with these commands Local (config) # ip rount 0.0.0.0.0.0.0.0 192.168.1.1 Local (config) # ip rount 10.1.0.0 255.255.255.0 192.168.2.2 Local (config) # ip rount 10.1.0.0 255.255.255.0 192.168.3.3 Drag each destination IP address on the left to its correct next hop address on the rightSort elements
- 10.2.1.3
- 10.6.8.4
- 10.1.0.14
- 10.1.0.123
- 10.1.1.10
- 10.1.4.6
-
Next hop 192.186.1.1
-
Next hop 192.186.1.1
-
Next hop 192.186.2.2
-
Next hop 192.186.2.2
-
Next hop 192.186.3.3
-
Next hop 192.186.3.3
Correct
Incorrect
-
Question 202 of 208
202. Question
1 pointsDrad and drop question Drap the cable type on the left to the purpose for which it is best suited on the right (not all options are used)Sort elements
- crossover
- null modem
- straight throught
- rollover
- 9-25 pin serial
-
straight throught
-
crossover
-
rollover
Correct
Incorrect
-
Question 203 of 208
203. Question
1 pointsDrag and drop question Drad each category on the left to its corresponding router output line to the right. Each router output line is the result of the show ip interface command. Not all categories are used.Sort elements
- layer 1 problem
- layer 2 problem
- layer 3 problem
- port operational
- port disabled
-
port operational
-
layer 2 problem
-
layer 1 problem
-
port disabled
Correct
Incorrect
-
Question 204 of 208
204. Question
1 pointsDrag and drop questionSort elements
- 120
- 110
- 1
- 90
- 0
- 130
- 100
- 20
-
RIP
-
OSPF
-
static rout referencing ip address of next hop
-
internal EIGRP rout
-
directly connected password
Correct
Incorrect
-
Question 205 of 208
205. Question
1 pointsDrag and drop questionSort elements
- DTE
- PVC
- LMI
- DLCI
- CIR
- DCE
- SVC
-
a router is this type of device
-
the most common type of virtual circult
-
provides status massage between DTE and DCE devices
-
identifies the virtual connection between the DTE and switch
Correct
Incorrect
-
Question 206 of 208
206. Question
1 pointsdrag and drop question a user is unable to connect to internet. bassed on the layered approach to troubleshooting and beginner with the lowest layer. drag each procedure on the left to its proper category on the rightSort elements
- verify Ethernet cable connection
- verify NIC operation
- verify Ip configuration
- verify URL
-
Step 1
-
Step 2
-
Step 3
-
Step 4
Correct
Incorrect
-
Question 207 of 208
207. Question
1 pointsDrag and drop question Drag each definition on the left to the matching term on the rightSort elements
- a configurable value based by default on the bandwidth of the interface
- the amount of activity on a network resource
- the data capacity of a link
- the number of point - to -point link in a transmission path
- usually refer to the bit error rate of each network link
- the amount of time required to move a packet from source to destination
-
cost
-
load
-
bandwidth
-
hop count
-
reliability
-
delay
Correct
Incorrect
-
Question 208 of 208
208. Question
1 pointsDrag and drop question Match the term on the left with the appropriate OSI layer on the right. (not all options are used)Sort elements
- packets
- ip addresses
- routing
- UDP
- segments
- windowing
-
network layer
-
network layer
-
network layer
-
transport layer
-
transport layer
-
transport layer
Correct
Incorrect
