Time limit: 0
Quiz-summary
0 of 34 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
Information
CCNA Cyber Ops (Version 1.1) – Chapter 3 Test Online Full
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 34 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- Answered
- Review
-
Question 1 of 34
1. Question
1 pointsWhy would a network administrator choose Linux as an operating system in the Security Operations Center (SOC)?Correct
Incorrect
-
Question 2 of 34
2. Question
1 pointsWhich Linux command can be used to display the name of the current working directory?Correct
Incorrect
-
Question 3 of 34
3. Question
1 pointsConsider the result of the ls -l command in the Linux output below. What are the file permissions assigned to the sales user for the analyst.txt file? ls –l analyst.txt -rwxrw-r– sales staff 1028 May 28 15:50 analyst.txtCorrect
Incorrect
-
Question 4 of 34
4. Question
1 pointsA Linux system boots into the GUI by default, so which application can a network administrator use in order to access the CLI environment?Correct
Incorrect
-
Question 5 of 34
5. Question
1 pointsThe image displays a laptop that is acting as the SSH client that is communicating with an SSH server. Refer to the exhibit. Which well-known port number is used by the server?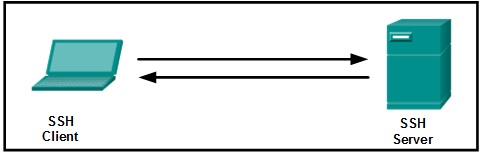 Correct
Correct
Incorrect
-
Question 6 of 34
6. Question
1 pointsHow is a server different from a workstation computer?Correct
Incorrect
-
Question 7 of 34
7. Question
1 pointsWhich two methods can be used to harden a computing device? (Choose two.)Correct
Incorrect
-
Question 8 of 34
8. Question
1 pointsWhat is the main purpose of the X Window System?Correct
Incorrect
-
Question 9 of 34
9. Question
1 pointsWhich Linux command is used to manage processes?Correct
Incorrect
-
Question 10 of 34
10. Question
1 pointsWhy is Linux considered to be better protected against malware than other operating systems?Correct
Incorrect
-
Question 11 of 34
11. Question
1 pointsWhich two Linux commands might be used before using the kill command? (Choose two.)Correct
Incorrect
-
Question 12 of 34
12. Question
1 pointsWhat term is used for operating system updates?Correct
Incorrect
-
Question 13 of 34
13. Question
1 pointsWhat term describes a set of software tools designed to increase the privileges of a user or to grant access to the user to portions of the operating system that should not normally be allowed?Correct
Incorrect
-
Question 14 of 34
14. Question
1 pointsWhat is the well-known port address number used by DNS to serve requests?Correct
Incorrect
-
Question 15 of 34
15. Question
1 pointsWhich file system is the primary file system used by Apple in current Macintosh computers?Correct
Incorrect
-
Question 16 of 34
16. Question
1 pointsWhich type of tool allows administrators to observe and understand every detail of a network transaction?Correct
Incorrect
-
Question 17 of 34
17. Question
1 pointsWhich command can be utilized to view log entries of NGINX system events in real time?Correct
Incorrect
-
Question 18 of 34
18. Question
1 pointsWhat is the purpose of a Linux package manager?Correct
Incorrect
-
Question 19 of 34
19. Question
1 pointsWhich user can override file permissions on a Linux computer?Correct
Incorrect
-
Question 20 of 34
20. Question
1 pointsWhich Linux file system introduced the journaled file system, which can be used to minimize the risk of file system corruption in the event of a sudden power loss?Correct
Incorrect
-
Question 21 of 34
21. Question
1 pointsWhat is the method employed by a Linux kernel to create new processes for multitasking of a process?Correct
Incorrect
-
Question 22 of 34
22. Question
1 pointsWhat is a purpose of apt-get commands?Correct
Incorrect
-
Question 23 of 34
23. Question
1 pointsWhat is the outcome when a Linux administrator enters the man man command?Correct
Incorrect
-
Question 24 of 34
24. Question
1 pointsWhat is a benefit of Linux being an open source operating system?Correct
Incorrect
-
Question 25 of 34
25. Question
1 pointsWhich types of files are used to manage services in a Linux system?Correct
Incorrect
-
Question 26 of 34
26. Question
1 pointsWhich working environment is more user-friendly?Correct
Incorrect
-
Question 27 of 34
27. Question
1 pointsWhich Linux component would be used to access a short list of tasks theapplication can perform?Correct
Incorrect
-
Question 28 of 34
28. Question
1 pointsWhich term is used to describe a running instance of a computer program?Correct
Incorrect
-
Question 29 of 34
29. Question
1 pointsWhich type of tool is used by a Linux administrator to attack a computer or network to find vulnerabilities?Correct
Incorrect
-
Question 30 of 34
30. Question
1 pointsWhich method can be used to harden a computing device?Correct
Incorrect
-
Question 31 of 34
31. Question
1 pointsConsider the result of the ls -l command in the Linux output below. What are the group file permissions assigned to the analyst.txt file?ls -l analyst.txt -rwxrw-r-- sales staff 1028 May 28 15:50 analyst.txt
Correct
Incorrect
-
Question 32 of 34
32. Question
1 pointsMatch the description to the Linux term. (Not all options are used.)Correct
Incorrect
-
Question 33 of 34
33. Question
1 pointsMatch typical Linux log files to the function.Correct
Incorrect
-
Question 34 of 34
34. Question
1 pointsMatch the file system term used in Linux to the function.Correct
Incorrect
