Category: CCNA CyberOps Labs – Activities
Objectives Part 1: Capture and view HTTP traffic Part 2: Capture and view HTTPS traffic Background / Scenario HyperText Transfer Protocol (HTTP) is an application layer protocol that presents data via a web browser. With HTTP, there is no safeguard for the exchanged data between two communicating devices. …
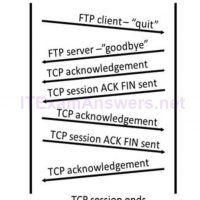
Topology – Part 1 (FTP) Part 1 will highlight a TCP capture of an FTP session. This topology consists of the CyberOps Workstation VM with Internet access. Mininet Topology – Part 2 (TFTP) Part 2 will highlight a UDP capture of a TFTP session using the hosts in …
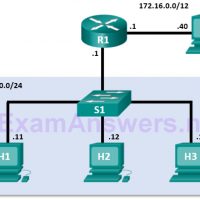
Topology Objectives Part 1: Record a PC’s IP Configuration Information Part 2: Use Wireshark to Capture DNS Queries and Responses Part 3: Analyze Captured DNS or UDP Packets Background / Scenario When you use the Internet, you use the Domain Name System (DNS). DNS is a distributed network …
Topology Objectives Part 1: Exploring Nmap Part 2: Scanning for Open Ports Background / Scenario Port scanning is usually part of a reconnaissance attack. There are a variety of port scanning methods that can be used. We will explore how to use the Nmap utility. Nmap is a …
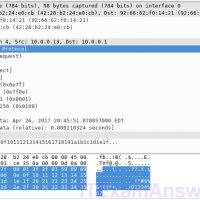
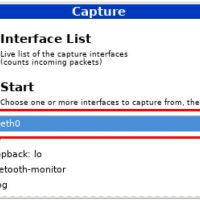
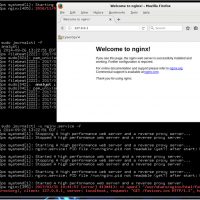
Mininet Topology Objectives Part 1: Prepare the Hosts to Capture the Traffic Part 2: Analyze the Packets using Wireshark Part 3: View the Packets using tcpdump Background / Scenario In this lab, you will use Wireshark to capture and examine packets generated between the PC browser using the …
Mininet Topology Objectives Part 1: Examine the Header Fields in an Ethernet II Frame Part 2: Use Wireshark to Capture and Analyze Ethernet Frames Background / Scenario When upper layer protocols communicate with each other, data flows down the Open Systems Interconnection (OSI) layers and is encapsulated into …
Mininet Topology Objectives Part 1: Install and Verify the Mininet Topology Part 2: Capture and Analyze ICMP Data in Wireshark Background / Scenario The CyberOps VM includes a Python script that, when you run it, will set up and configure the devices shown in the figure above. You …
Objectives Part 1: Verifying Network Connectivity Using Ping Part 2: Tracing a Route to a Remote Server Using Traceroute Part 3: Trace a Route to a Remote Server Using Web-Based Traceroute Tool Background Tracing a route will list each routing device that a packet crosses as it traverses …
Objectives In this lab, you will use familiarize yourself with Linux filesystems. Required Resources CyberOps Workstation VM Part 1: Exploring Filesystems in Linux The Linux filesystem is one of its most popular features. While Linux supports many different types of filesystems, this lab focuses on the ext family, …
Introduction In this lab, you will get familiar with locating and manipulating Linux log files. Required Resources CyberOps Workstation Virtual Machine Part 1: Log File Overview Log files (also spelled logfiles), are files used by computers to log events. Software programs, background processes, services, or transactions between services, …