Category: CCNA CyberOps Labs – Activities
Introduction In this lab, you will use the Linux command line to identify servers running on a given computer. Recommended Equipment CyberOps Workstation Virtual Machine Part 1: Servers Servers are essentially programs written to provide specific information upon request. Clients, which are also programs, reach out to the …
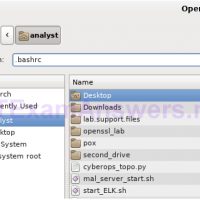
Introduction In this lab, you will use the Linux command line to manage files and folders, and perform some basic administrative tasks. Recommended Equipment CyberOps Workstation Virtual Machine Part 1: Shell Basics The shell is the term used to refer to the command interpreter in Linux. Also known …
Introduction In this lab, you will get familiar with Linux command line text editors and configuration files. Required Resources CyberOps Workstation Virtual Machine Part 1: Graphical Text Editors Before you can work with text files in Linux, you must get familiar with text editors. Text editors are one …
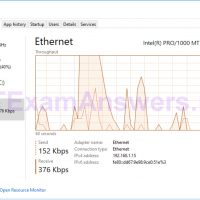
Introduction In this lab, you will use administrative tools to monitor and manage Windows system resources. Recommended Equipment A Windows PC with Internet access Part 1: Starting and Stopping the Routing and Remote Access service You will explore what happens when a service is stopped and then started. …
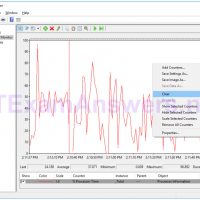
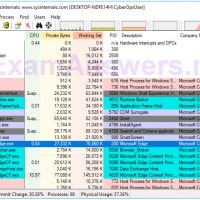
Introduction In this lab, you will explore Task Manager and manage processes from within Task Manager. Part 1: Working in the Processes tab Part 2: Working in the Services tab Part 3: Working in the Performance tab Background / Scenario The Task Manager is a system monitor program …
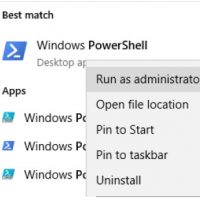
Objectives The objective of the lab is to explore some of the functions of PowerShell. Background / Scenario PowerShell is a powerful automation tool. It is both a command console and a scripting language. In this lab, you will use the console to execute some of the commands …
Introduction In this lab, you will create and modify user accounts in Windows. Part 1: Creating a New Local User Account Part 2: Reviewing User Account Properties Part 3: Modifying Local User Accounts Required Resources A Windows PC Part 1: Creating a New Local User Account Step 1: …
Objectives In this lab, you will explore the processes, threads, and handles using Process Explorer in the SysInternals Suite. You will also use the Windows Registry to change a setting. Part 1: Exploring Processes Part 2: Exploring Threads and Handles Part 3: Exploring Windows Registry Required Resources 1 …
Objectives Research and analyze what it takes to become a network defender Background / Scenario In our technology-centric world, as the world gets more connected, it also gets less safe. Cybersecurity is one of the fastest growing and in-demand professions. Individuals in this field perform a wide variety …
Objectives Research and analyze cyber security incidents Background / Scenario In 2016, it was estimated that businesses lost $400 million dollars annually to cyber criminals. Governments, businesses, and individual users are increasingly the targets of cyberattacks and cybersecurity incidents are becoming more common. In this lab, you will …