Category: CCNA CyberOps Labs – Activities
Objectives Part 1: Encrypting Messages with OpenSSL Part 2: Decrypting Messages with OpenSSL Background / Scenario OpenSSL is an open source project that provides a robust, commercial-grade, and full-featured toolkit for the Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols. It is also a general-purpose cryptography …
Topology Addressing Table Device Private IP Address Public IP Address FTP_Server 192.168.30.253 209.165.200.227 SYSLOG_SERVER 192.168.11.254 209.165.200.229 Router2 N/A 209.165.200.226 Objectives Part 1: Create FTP traffic. Part 2: Investigate the FTP Traffic Part 3: View Syslog Messages Background In this activity, you will use Packet Tracer to sniff and …
Objectives Part 1: Reading Log Files with Cat, More, and Less Part 2: Log Files and Syslog Part 3: Log Files and Journalctl Background / Scenario Log files are an important tool for troubleshooting and monitoring. Different application generates different log files, each one containing its own set …
Objectives In this lab, you will view a PCAP file from a previous attack against a SQL database. Background / Scenario SQL injection attacks allow malicious hackers to type SQL statements in a web site and receive a response from the database. This allows attackers to tamper with …
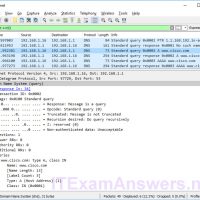
Objectives Part 1: Capture DNS Traffic Part 2: Explore DNS Query Traffic Part 3: Explore DNS Response Traffic Background / Scenario Wireshark is an open source packet capture and analysis tool. Wireshark gives a detailed breakdown of the network protocol stack. Wireshark allows you to filter traffic for …
Objectives Identify the processes running on a computer, the protocol they are using, and their local and remote port addresses. Background / Scenario For a hacker to establish a connection to a remote computer, a port must be listening on that device. This may be due to infection …
Objectives Research and identify social engineering attacks Background / Scenario Social engineering is an attack with the goal of getting a victim to enter personal or sensitive information, this type of attack can be performed by an attacker utilizing a keylogger, phishing email, or an in-person method. This …
Objectives Research and analyze malware Background / Scenario Malware, or malicious software, refers to a variety of malicious software programs that can be used to cause harm to computer systems, steal data, and bypass security measures. Malware can also attack critical infrastructure, disable emergency services, cause assembly lines …
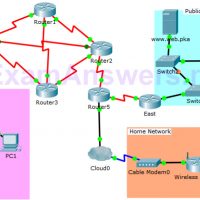
Topology Objectives In this activity, you will observe packet flow in a LAN and WAN topology. You will also observe how the packet flow path may change when there is a change in the network topology. Part 1: Verify Connectivity Part 2: Remote LAN Network Topology Part 3: …
Topology Objectives Part 1: Verify Local Connectivity and Test Access Control List Part 2: Remove Access Control List and Repeat Test Background In this activity, you will observe how an access control list (ACL) can be used to prevent a ping from reaching hosts on remote networks. After …