Category: CCNA CyberOps Labs – Activities
Objectives In this lab, you will learn how to use regular expressions to search for desired strings of information. Background / Scenario A regular expression (regex) is a pattern of symbols that describes data to be matched in a query or other operation. Regular expressions are constructed similarly …
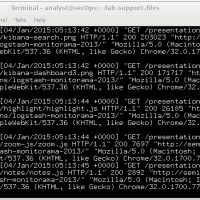
Objectives Part 1: Normalize Timestamps in a Log File Part 2: Normalize Timestamps in an Apache Log File Part 3: Log File Preparation in Security Onion Background / Scenario This lab will prepare students to learn where log files are located and how to manipulate and view log …
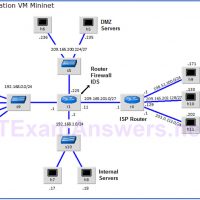
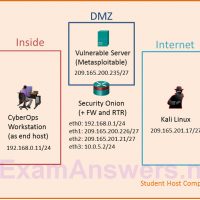
Topology Objectives Part 1: Preparing the Virtual Environment Part 2: Firewall and IDS Logs Part 3: Terminate and Clear Mininet Process Background / Scenario In a secure production network, network alerts are generated by various types of devices such as security appliances, firewalls, IPS devices, routers, switches, servers, …
Topology Objectives Part 1: Use syslog to capture log files from multiple network devices Part 2: Observe AAA user access logging Part 3: Observe NetFlow information Background / Scenario In this activity, you will use Packet Tracer to view network data generated by syslog, AAA, and NetFlow. Part …
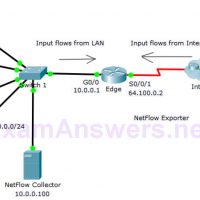
Topology Objectives Part 1: Observe NetFlow Flow Records – One Direction Part 2: Observe NetFlow Records for a Session that Enters and Leaves the Collector Background In this activity, you will use Packet Tracer to create network traffic and observe the corresponding NetFlow flow records in a NetFlow …
Topology Objectives In this lab, you will set up a virtual network environment by connecting multiple virtual machines in Virtualbox. Background / Scenario A virtual network security sandbox or multi-VM lab environment is useful for security analysis and testing. This multi-VM environment is a requirement for more advanced …
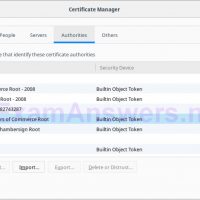
Objectives Part 1: Certificates Trusted by Your Browser Part 2: Checking for Man-In-Middle Background / Scenario As the web evolved, so did the need for security. HTTPS (where the ‘S’ stands for security) along with the concept of a Certificate Authority was introduced by Netscape back in 1994 …
Objectives Part 1: Creating Hashes with OpenSSL Part 2: Verifying Hashes Background / Scenario Hash functions are mathematical algorithms designed to take data as input and generate a fixed-size, unique string of characters, also known as the hash. Designed to be fast, hash functions are very hard to …
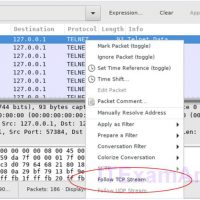
Objectives Part 1: Examine a Telnet Session with Wireshark Part 2: Examine an SSH Session with Wireshark Background / Scenario In this lab, you will configure a router to accept SSH connectivity and use Wireshark to capture and view Telnet and SSH sessions. This will demonstrate the importance …
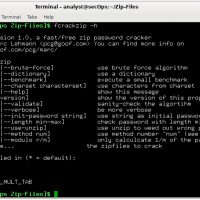
Objectives Part 1: Create and Encrypt Files Part 2: Recover Encrypted Zip File Passwords Background / Scenario What if you work for a large corporation that had a corporate policy regarding removable media? Specifically, it states that only encrypted zipped documents can be copied to portable USB flash …