Category: CCNA CyberOps Labs – Activities
2.2.5 Lab – Becoming a Defender (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Research and analyze what it takes to become a network defender. Part 1: Conduct search of Certifications. Part 2: Investigate positions available …
1.3.4 Lab – Visualizing the Black Hats (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Research and analyze cyber security incidents. Background / Scenario The FBI has estimated that cybercrime cost individuals and companies over 3.5 …
1.1.6 Lab – Cybersecurity Case Studies (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Research and analyze cyber security incidents. Part 1: Conduct search of high profile cyberattacks. Part 2: Write an analysis of a cyberattack. …
1.1.5 Lab – Installing the Virtual Machines (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Part 1: Prepare a Personal Computer for Virtualization Part 2: Import a Virtual Machine into VirtualBox Inventory Background / Scenario Computing …
1.0.6 Class Activity – Top Hacker Shows Us How It is Done (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Understand vulnerabilities of wireless and other common technologies Part 1: View the TEDx Video “Top Hacker …
1.2.3 Lab – Learning the Details of Attacks (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Research and analyze IoT application vulnerabilities. Part 1: Conduct a Search of IoT Application Vulnerabilities Background / Scenario The Internet …
Objectives Apply your knowledge of security incident handling procedures to formulate questions about given incident scenarios. Background / Scenario Computer security incident response has become a vital part of any organization. The process for handling a security incident can be complicated and involve many different groups. An organization …
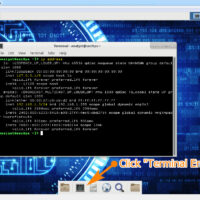
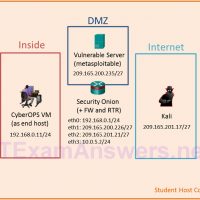
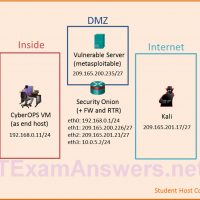
Topology Objectives In this lab, you will review logs during an exploitation of a documented vulnerability to determine the compromised hosts and file. Part 1: Prepare the Virtual Environment Part 2: Reconnaissance Part 3: Exploitation Part 4: Infiltration Part 5: Review the Logs Background / Scenario The 5-tuple …
Topology Objectives In this lab, you will review logs during an exploitation of documented HTTP and DNS vulnerabilities. Part 1: Prepare the Virtual Environment Part 2: Investigate an SQL Injection Attack Part 3: Data Exfiltration Using DNS Background / Scenario MySQL is a popular database used by numerous …
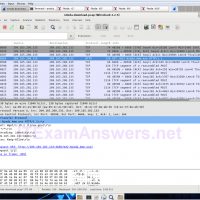
Objectives Part 1: Prepare the Virtual Environment Part 2: Analyze Pre-Captured Logs and Traffic Captures Background / Scenario Looking at logs is very important but it is also important to understand how network transactions happen at the packet level. In this lab, you will analyze the traffic in …