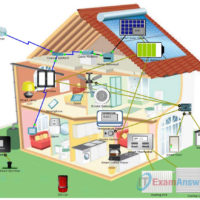
6.2.4.4 Packet Tracer – Threat Modeling to Assess Risk in an IoT System (Instructor Version) Topology This is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives Part 1: Creating …
5.2.1.6 Packet Tracer – Threat Modeling at the IoT Application Layer (Instructor Version) Topology This is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives In this Packet Tracer, you …
4.3.1.6 Packet Tracer – Threat Modeling at the IoT Communication Layer (Instructor Version) Topology The topology is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives In this Packet Tracer, …
3.3.2.5 Packet Tracer – Threat Modeling at the IoT Device Layer (Instructor Version) Topology The topology is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives In this Packet Tracer, …
1.2.1.1 Packet Tracer – Explore the Smart Home (Instructor Version) Topology Objectives Explore the Smart Home Analyze the Usage of Fog Computing in the Smart Home Background / Scenario In this activity, you will explore the smart home example. Depending on the application, some data is best processed …
IoT Fundamentals: IoT Security Exam Answers Quiz IoT Security Exam Answers Online Test IoT Security 1.1 Chapter 1 Quiz Answers Test IoT Security 1.1 Chapter 2 Quiz Answers Test IoT Security 1.1 Chapter 3 Quiz Answers Test IoT Security 1.1 Chapter 4 Quiz Answers Test IoT Security 1.1 …
IoT Security 1.1 Chapter 6 Quiz Exam Answers 1. What is a characteristic of a blockchain? It uses risk avoidance. It is a government approved authentication protocol. It is immutable. It uses the XML format. 2. Which problem associated with transactions is solved by blockchain technology? trust encryption …
IoT Security 1.1 Chapter 5 Quiz Exam Answers 1. A client wants to deploy MQTT on a large enterprise network and is worried about the security of MQTT. The client wants all messages encrypted, including all messages between the broker and clients. What could the client do to …
IoT Security 1.1 Chapter 4 Quiz Exam Answers 1. Why would an engineer only use very short-range radios to allow sensor data to travel from node to node until the data reaches the IoT gateway? increased bandwidth channel requirements power constraints high availability 2. A home owner recently …
IoT Security 1.1 Chapter 3 Quiz Answers 1. Which type of vulnerability is present when a programmer does not account for the size of the input that a user might enter? backdoor installation denial of service out of date firmware buffer overflow 2. Which type of memory media …