1. Which function is provided by MapReduce to Hadoop? storage expansion hypervisor security distributed processing database management 2. Which transferring methodology do traditional message brokers use? publish-subscribe transaction logging client-server real-time 3. Which solution improves web response time by deploying multiple web servers and DNS servers? sharding memcaching …
1. Which term is used to describe the process of discovery that may lead to the creation of a hypothesis? exploratory analysis deductive reasoning inductive reasoning explanatory analysis 2. When you are preparing to give a presentation, which question would be important to ask yourself in order to …
1. When you follow the scientific method, which step would occur after testing the hypotheses through experimentation? Communicate the results of the process. Analyze data from an experiment to draw a conclusion. Ask a question about an observation. Perform research. 2. What is the most commonly used statistical …
1. Which statement is an accurate description of discrete variables? Discrete variables are qualitative and consist of two or more categories in which order matters. They are quantitative with a continuous range of values. They are quantitative with a finite set of values. They are qualitative and consist …
1. Which data trend has seen decision making rely increasingly on data analytics? the increase in the amount of data the security constraints of data the lack of information about data the accuracy of decision making 2. Which statement is true concerning data analytics? Prescriptive analytics uses historical …
1. Which term describes the growth rate of data in the IoT? linear cyclical uniform exponential 2. What are two examples of unstructured data? (Choose two.) video content user account data SQL queries blog entry customer account spreadsheet 3. What is a characteristic of open data? data that …
6.3.2.7 Lab – Blockchain Demo 2.0 (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Complete the Blockchain Demo 2.0 Complete Reflection Questions Background / Scenario Blockchain is the technology behind the cryptocurrency, bitcoin. It uses a …
6.2.3.6 Lab – Assess Risk with DREAD (Instructor Version) Objectives In this lab, you will use the DREAD risk assessment model to assess risk. Part 1: Using the DREAD Scoring System to Assess Risk Part 2: Using the DREAD System to Assess the Risk of a Described Vulnerability …
6.2.1.9 Lab – Using the CVSS (Instructor Version) Objectives In this lab, you will explain the concepts behind a strong password. Part 1: Researching the Details of the CVSS Metrics Used to Compute the CVSS Score Part 2: Using the CVSS Calculator to Determine the Severity Level of …
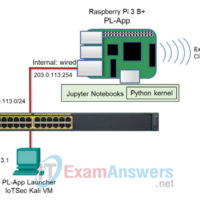
5.1.3.9 Lab – UPnP Vulnerabilities (Instructor Version) Lab Topology Addressing The Pi will acquire an address from the external network, while providing addresses to the internal network. Objectives Part 1: Configuring the Raspberry Pi as a wired router using a BASH script Part 2: Connecting a Client to …