Author: ITExamAnswers
DevNet Associate 3.7.2 Module 3: Software Development and Design Quiz (Answers) 1. Which software development methodology prescribes that developers follow a strict process order by completing one step in the SDLC process before proceeding to the next step. Waterfall Agile Lean Scrum 2. Which SDLC development methodology employs …
DevNet Associate 2.3.2 Module 2: The DevNet Developer Environment Quiz Answers 1. What type of learner should take the DevNet Associate course? anyone that does not like working in teams and is a software developer anyone interested in network automation and programmability only new network engineers only new …
DevNet Associate 1.3.4 Module 1 Quiz – Python Review (Answers) 1. A student is learning Python using the interactive interpreter mode. The student issues the commands: >>> routers= >>> switches= >>> devices= >>> devices=devices + >>> for i in devices: if \"R\" in i: routers.append(i) else: switches.append(i) >>> …
DevNet Associate 1.2.3 Quiz Module 1 Quiz – Linux Review (Answers) 1. What Linux command is used to display the contents of the current directory? pwd cat ln ls 2. What command is used to rename a file in a Linux system? mv dd cp rm 3. A …
1. What are three benefits of implementing VSS in a network? (Choose three.) Neighbors see the VSS as a single switch VSS is implemented in the access layer which supports a more simplistic design. VSS can logically combine up to 9 switches. Single management point Interchassis stateful failover …
1. Which SDM template should be enabled if you have a large number of VLANs to support? sdm prefer routing sdm prefer dual-ipv4-and-ipv6 sdm prefer access sdm prefer VLAN 2. Which statement is true about the PoE negotiation process? With 802.3af and 802.3at, the switch tries to detect …
1. Which three commands are necessary to configure NTP authentication between devices? (Choose three.) ntp trusted-key authentication 1 ntp authentication ntp authentication-key 1 md5 ntp trusted-key 1 ntp md5 authentication-key 1 ntp authenticate 2. What is the command to configure a device to be an authoritative NTP server? …
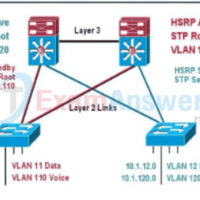
1. Which one of the following GLBP functions answers ARP requests? AVF MVP AVG Active 2. Which two statements about VRRP are true? (Choose two.) VRRP cannot track interfaces or objects. A VRRP group has one master router and one or more backup routers. VRRP provides redundancy for …
1. Refer to the exhibit. Host A is unable to obtain an IP address from the DHCP server. Which procedure would solve this problem? Use the command ip helper-address 10.1.2.1 on interface Fa0/0 of router RTA. Use the command ip helper-address 10.1.2.10 on interface Fa0/0 of router RTA. …
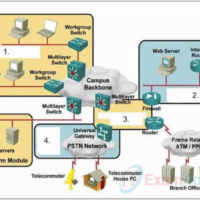
1. What are three properties of peer-to-peer applications? (Choose three.) require dedicated bandwidth allocation can be used in video conference applications require real-time interaction between peer devices can be used to fulfill the requirements for IP phone calls require a direct physical connection between devices require centralized authentication …