Author: ITExamAnswers
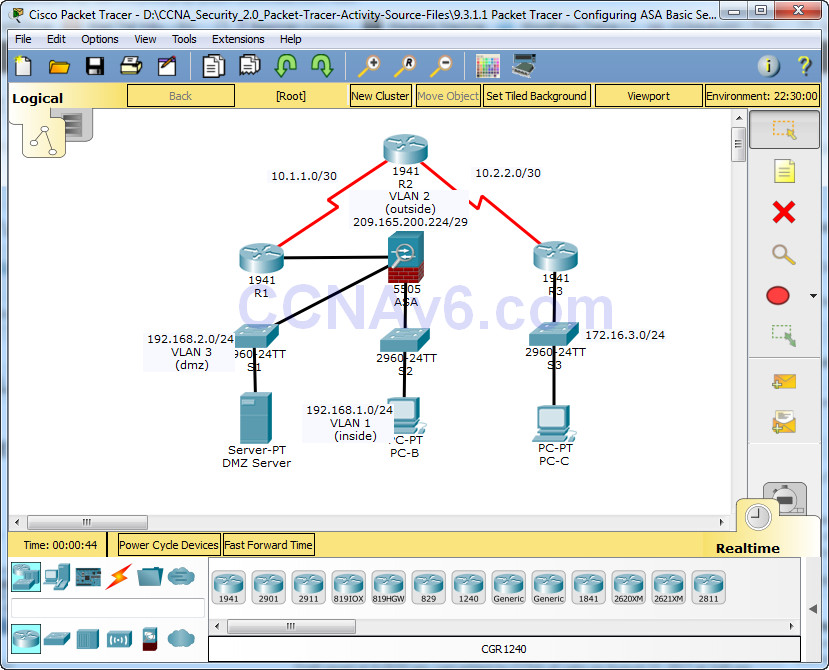
Packet Tracer – Configuring ASA Basic Settings and Firewall Using CLI Topology IP Addressing Table Objectives • Verify connectivity and explore the ASA • Configure basic ASA settings and interface security levels using CLI • Configure routing, address translation, and inspection policy using CLI • Configure DHCP, …
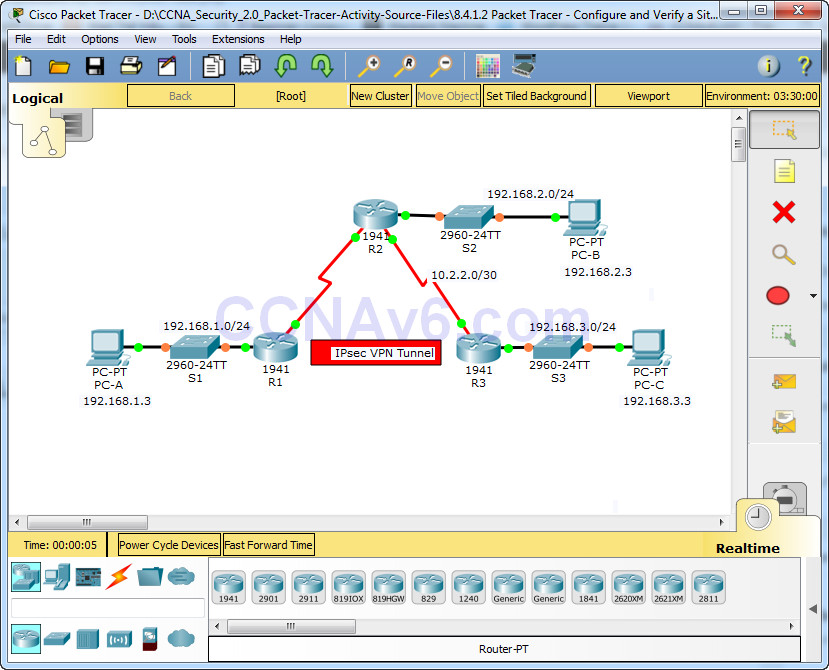
Packet Tracer – Configure and Verify a Site-to-Site IPsec VPN Using CLI Topology Addressing Table Objectives • Verify connectivity throughout the network. • Configure R1 to support a site-to-site IPsec VPN with R3. Background / Scenario The network topology shows three routers. Your task is to configure …
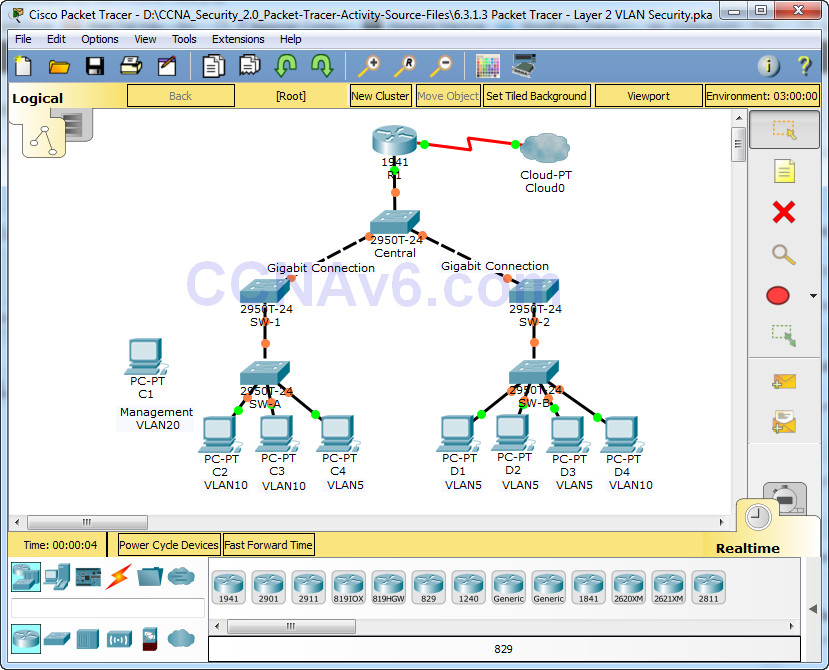
Packet Tracer – Layer 2 VLAN Security Topology Objectives • Connect a new redundant link between SW-1 and SW-2. • Enable trunking and configure security on the new trunk link between SW-1 and SW-2. • Create a new management VLAN (VLAN 20) and attach a management PC …
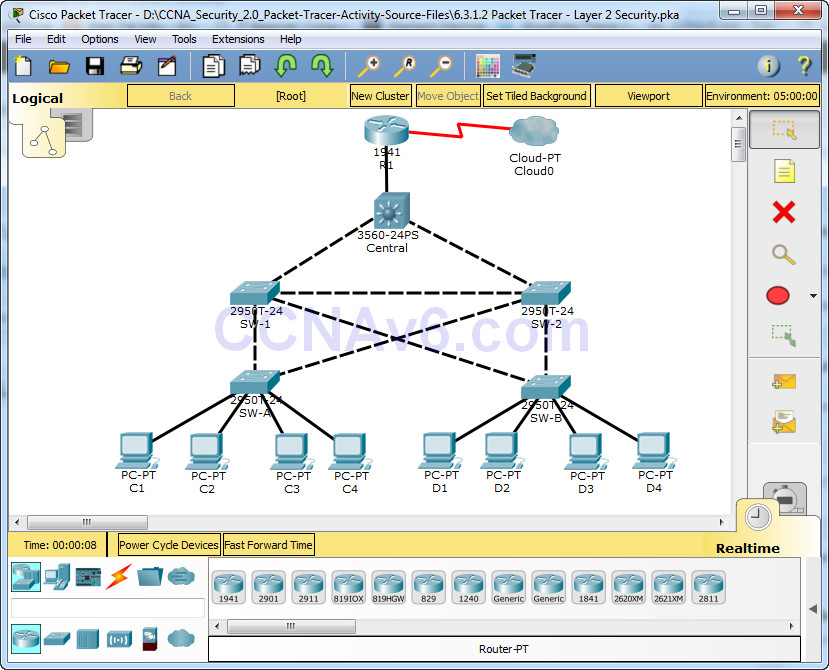
Packet Tracer – Layer 2 Security Topology Objectives • Assign the Central switch as the root bridge. • Secure spanning-tree parameters to prevent STP manipulation attacks. • Enable port security to prevent CAM table overflow attacks. Background / Scenario There have been a number of attacks on …
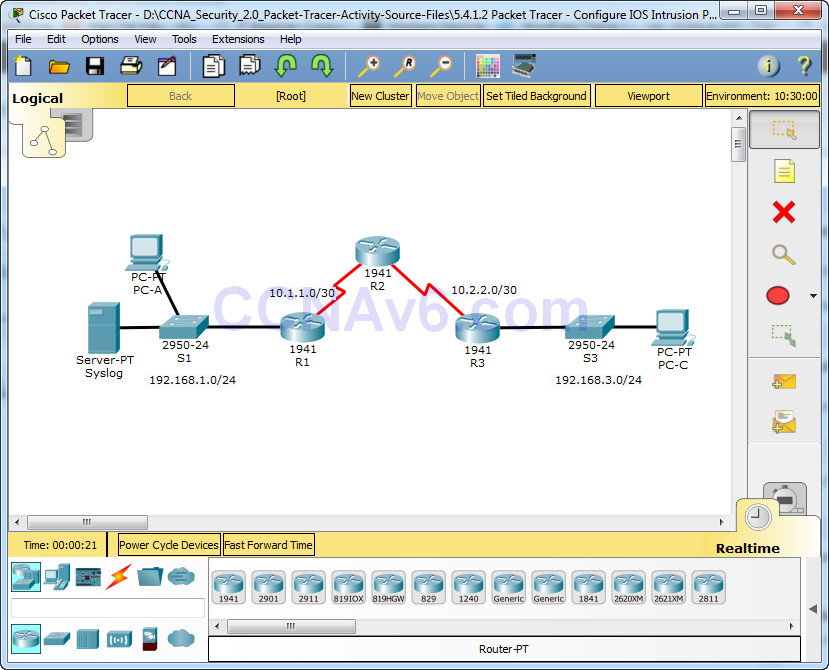
Packet Tracer – Configure IOS Intrusion Prevention System (IPS) Using the CLI Topology Addressing Table Objectives • Enable IOS IPS. • Configure logging. • Modify an IPS signature. • Verify IPS. Background / Scenario Your task is to enable IPS on R1 to scan traffic entering the …
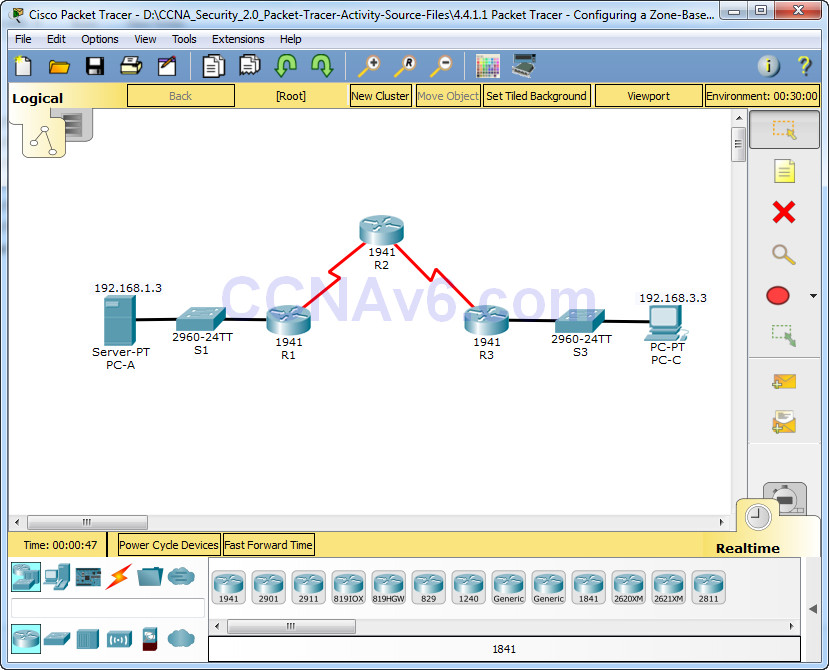
Packet Tracer – Configuring a Zone-Based Policy Firewall (ZPF) Topology Addressing Table Objectives • Verify connectivity among devices before firewall configuration. • Configure a zone-based policy (ZPF) firewall on R3. • Verify ZPF firewall functionality using ping, SSH, and a web browser. Background/Scenario ZPFs are the latest …
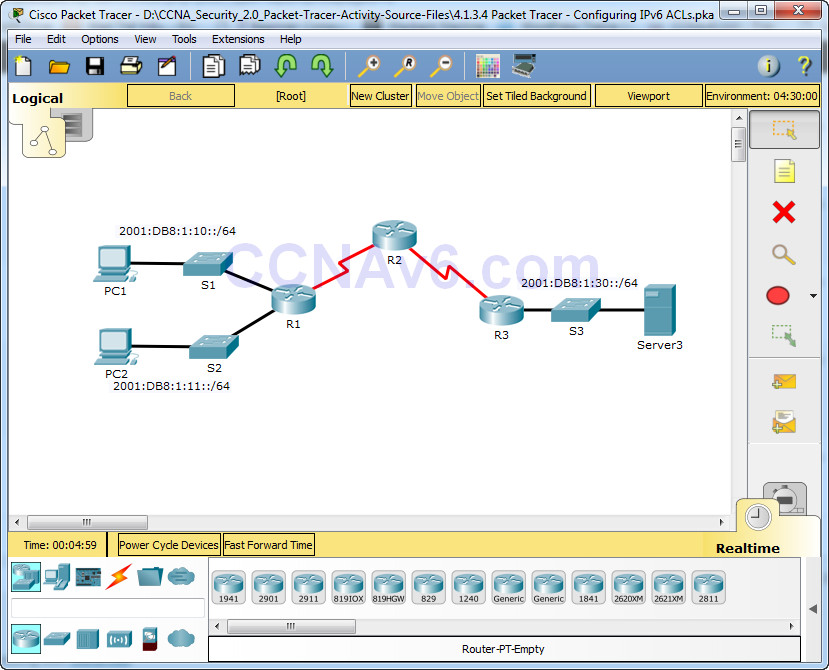
Packet Tracer – Configuring IPv6 ACLs Topology Addressing Table Objectives Part 1: Configure, Apply, and Verify an IPv6 ACL Part 2: Configure, Apply, and Verify a Second IPv6 ACL Part 1: Configure, Apply, and Verify an IPv6 ACL Logs indicate that a computer on the 2001:DB8:1:11::0/64 network …
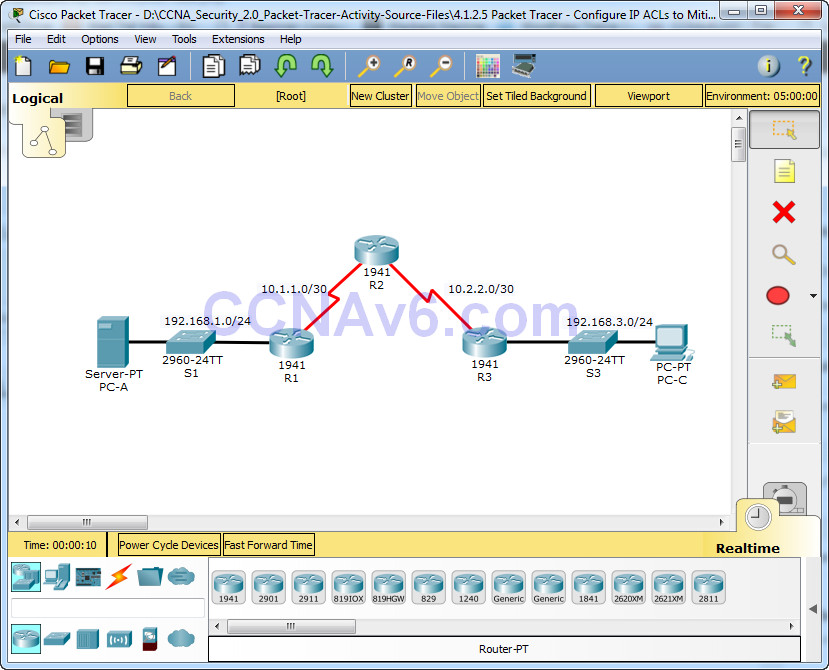
Packet Tracer – Configure IP ACLs to Mitigate Attacks Topology Addressing Table Objectives • Verify connectivity among devices before firewall configuration. • Use ACLs to ensure remote access to the routers is available only from management station PC-C. • Configure ACLs on R1 and R3 to mitigate …
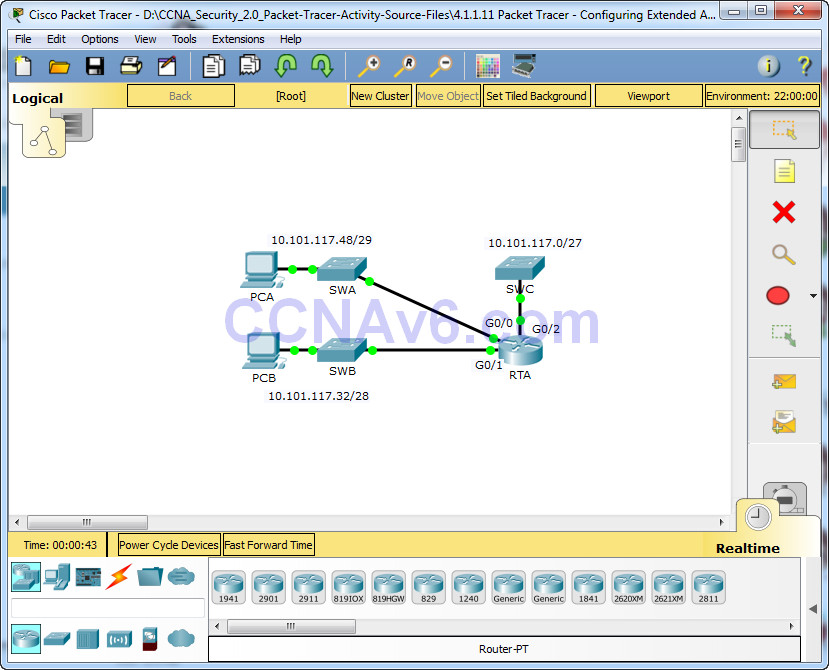
Packet Tracer – Configuring Extended ACLs – Scenario 2 Topology Addressing Table Objectives Part 1: Configure, Apply and Verify an Extended Numbered ACL Part 2: Reflection Questions Background / Scenario In this scenario, devices on one LAN are allowed to remotely access devices in another LAN using …
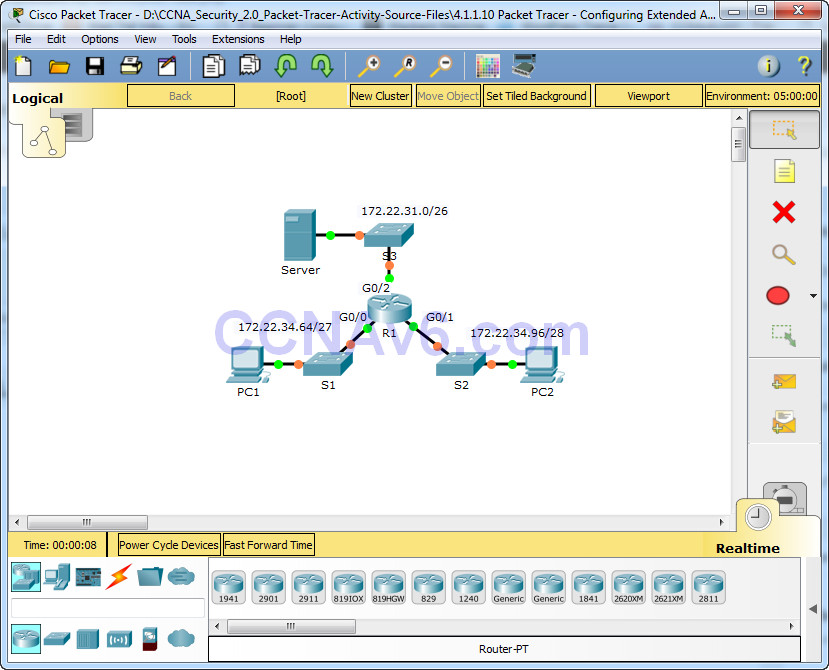
Packet Tracer – Configuring Extended ACLs – Scenario 1 Topology Addressing Table Objectives Part 1: Configure, Apply and Verify an Extended Numbered ACL Part 2: Configure, Apply and Verify an Extended Named ACL Background / Scenario Two employees need access to services provided by the server. PC1 …