Time limit: 0
Quiz-summary
0 of 27 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
Information
Good luck to you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 27 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- Answered
- Review
-
Question 1 of 27
1. Question
1 pointsWhich two definitions accurately describe the associated application layer protocol? (Choose two.)Correct
Incorrect
Hint
The Domain Name Service (DNS) protocol resolves Internet names to IP addresses. Hypertext Transfer Protocol (HTTP) transfers files that make up the web pages of the World Wide Web. The Simple Mail Transfer Protocol (SMTP) transfers mail messages and attachments. Telnet, a terminal emulation protocol, provides remote access to servers and networking devices. The File Transfer Protocol (FTP) transfers files between systems. -
Question 2 of 27
2. Question
1 pointsThe application layer of the TCP/IP model performs the functions of what three layers of the OSI model? (Choose three.)Correct
Incorrect
Hint
The network access layer of the TCP/IP model performs the same functions as the physical and data link layers of the OSI model. The internetwork layer equates to the network layer of the OSI model. The transport layers are the same in both models. The application layer of the TCP/IP model represents the session, presentation, and application layers of the OSI model. -
Question 3 of 27
3. Question
1 pointsWhich layer in the TCP/IP model is used for formatting, compressing, and encrypting data?Correct
Incorrect
Hint
The application layer of the TCP/IP model performs the functions of three layers of the OSI model – application, presentation, and session. The application layer of the TCP/IP model is the layer that provides the interface between the applications, is responsible for formatting, compressing, and encrypting data, and is used to create and maintain dialogs between source and destination applications. -
Question 4 of 27
4. Question
1 pointsWhat are two characteristics of the application layer of the TCP/IP model? (Choose two.)Correct
Incorrect
Hint
The application layer of the TCP/IP model is the layer that is closest to the end user, providing the interface between the applications. It is responsible for formatting, compressing, and encrypting data, and is used to create and maintain dialog between source and destination applications. -
Question 5 of 27
5. Question
1 pointsA manufacturing company subscribes to certain hosted services from its ISP. The services that are required include hosted world wide web, file transfer, and e-mail. Which protocols represent these three key applications? (Choose three.)Correct
Incorrect
Hint
The ISP uses the HTTP protocol in conjunction with hosting web pages, the FTP protocol with file transfers, and SMTP with e-mail. DNS is used to translate domain names to IP addresses. SNMP is used for network management traffic. DHCP ic commonly used to manage IP addressing. -
Question 6 of 27
6. Question
1 pointsWhat is an example of network communication that uses the client-server model?Correct
Incorrect
Hint
When a user types a domain name of a website into the address bar of a web browser, a workstation needs to send a DNS request to the DNS server for the name resolution process. This request is a client/server model application. The eMule application is P2P. Sharing a printer on a workstation is a peer-to-peer network. Using ARP is just a broadcast message sent by a host. -
Question 7 of 27
7. Question
1 pointsTwo students are working on a network design project. One student is doing the drawing, while the other student is writing the proposal. The drawing is finished and the student wants to share the folder that contains the drawing so that the other student can access the file and copy it to a USB drive. Which networking model is being used?Correct
Incorrect
Hint
In a peer-to-peer (P2P) networking model, data is exchanged between two network devices without the use of a dedicated server. -
Question 8 of 27
8. Question
1 pointsWhat do the client/server and peer-to-peer network models have in common?Correct
Incorrect
Hint
In both the client/server and peer-to-peer network models, clients and servers exist. In peer-to-peer networks, no dedicated server exists, but a device can assume the server role to provide information to a device serving in the client role. -
Question 9 of 27
9. Question
1 pointsWhat is an advantage for small organizations of adopting IMAP instead of POP?Correct
Incorrect
Hint
IMAP and POP are protocols that are used to retrieve email messages. The advantage of using IMAP instead of POP is that when the user connects to an IMAP-capable server, copies of the messages are downloaded to the client application. IMAP then stores the email messages on the server until the user manually deletes those messages. -
Question 10 of 27
10. Question
1 pointsWhich application layer protocol uses message types such as GET, PUT, and POST?Correct
Incorrect
Hint
The GET command is a client request for data from a web server. A PUT command uploads resources and content, such as images, to a web server. A POST command uploads data files to a web server. -
Question 11 of 27
11. Question
1 pointsWhen retrieving email messages, which protocol allows for easy, centralized storage and backup of emails that would be desirable for a small- to medium-sized business?Correct
Incorrect
Hint
IMAP is preferred for small-to medium-sized businesses as IMAP allows centralized storage and backup of emails, with copies of the emails being forwarded to clients. POP delivers the emails to the clients and deletes them on the email server. SMTP is used to send emails and not to receive them. HTTPS is not used for secure web browsing. -
Question 12 of 27
12. Question
1 pointsWhich three statements describe a DHCP Discover message? (Choose three.)Correct
Incorrect
Hint
When a host configured to use DHCP powers up on a network it sends a DHCPDISCOVER message. FF-FF-FF-FF-FF-FF is the L2 broadcast address. A DHCP server replies with a unicast DHCPOFFER message back to the host. -
Question 13 of 27
13. Question
1 pointsWhat part of the URL, http://www.cisco.com/index.html, represents the top-level DNS domain?Correct
Incorrect
Hint
The components of the URL http://www.cisco.com/index.htm are as follows: http = protocol www = part of the server name cisco = part of the domain name index = file name com = the top-level domain -
Question 14 of 27
14. Question
1 pointsWhich two tasks can be performed by a local DNS server? (Choose two.)Correct
Incorrect
Hint
Two important functions of DNS are to (1) provide IP addresses for domain names such as www.cisco.com, and (2) forward requests that cannot be resolved to other servers in order to provide domain name to IP address translation. DHCP provides IP addressing information to local devices. A file transfer protocol such as FTP, SFTP, or TFTP provides file sharing services. IMAP or POP can be used to retrieve an email message from a server. -
Question 15 of 27
15. Question
1 pointsWhich phrase describes an FTP daemon?Correct
Incorrect
Hint
An FTP server runs an FTP daemon, which is a program that provides FTP services. End users who request services must run an FTP client program. -
Question 16 of 27
16. Question
1 pointsWhich statement is true about FTP?Correct
Incorrect
Hint
FTP is a client/server protocol. FTP requires two connections between the client and the server and uses TCP to provide reliable connections. With FTP, data transfer can happen in either direction. The client can download (pull) data from the server or upload (push) data to the server. -
Question 17 of 27
17. Question
1 pointsWhat is true about the Server Message Block protocol?Correct
Incorrect
Hint
The Server Message Block protocol is a protocol for file, printer, and directory sharing. Clients establish a long term connection to servers and when the connection is active, the resources can be accessed. Every SMB message has the same format. The use of SMB differs from FTP mainly in the length of the sessions. SMB messages can authenticate sessions. -
Question 18 of 27
18. Question
1 pointsWhich application layer protocol is used to provide file-sharing and print services to Microsoft applications?Correct
Incorrect
Hint
SMB is used in Microsoft networking for file-sharing and print services. The Linux operating system provides a method of sharing resources with Microsoft networks by using a version of SMB called SAMBA. -
Question 19 of 27
19. Question
1 pointsFill in the blank.- What is the acronym for the protocol that is used when securely communicating with a web server? (HTTPS)
Correct
Incorrect
Hint
Hypertext Transfer Protocol Secure (HTTPS) is the protocol that is used for accessing or posting web server information using a secure communication channel. -
Question 20 of 27
20. Question
1 pointsFill in the blank.- The HTTP message type used by the client to request data from the web server is the (GET) message.
Correct
Incorrect
Hint
GET is one of the message types used by HTTP. A client (web browser) sends the GET message to the web server to request HTML pages. -
Question 21 of 27
21. Question
1 pointsOpen the PT Activity.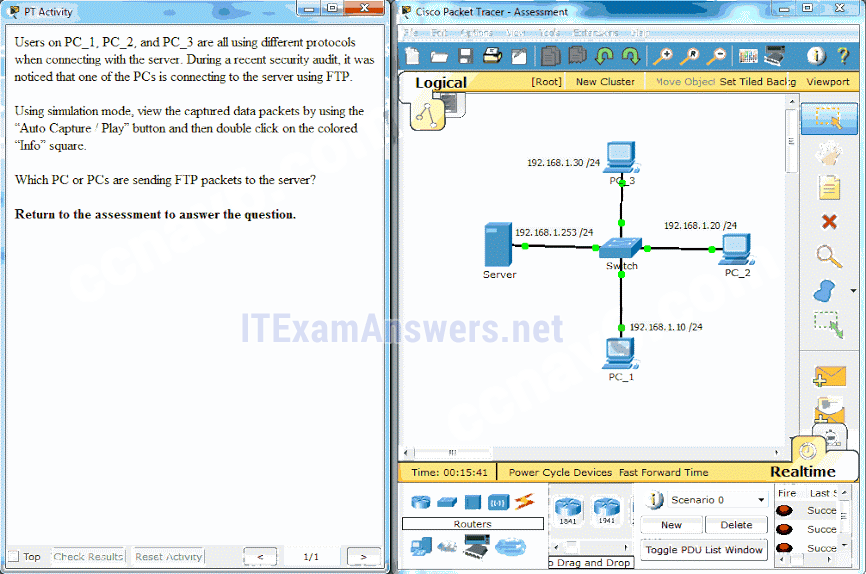 Perform the tasks in the activity instructions and then answer the question.
Which PC or PCs are sending FTP packets to the server? Correct
Perform the tasks in the activity instructions and then answer the question.
Which PC or PCs are sending FTP packets to the server? Correct
Incorrect
Hint
After you view the details of the packets that are being transferred between each PC and the server, you will see that the PC that is using a destination port number of 20 or 21 is the PC using the FTP service. PC_2 has an outbound port number of 21 to create an FTP control session with the server at 192.168.1.253. -
Question 22 of 27
22. Question
1 pointsFill in the blank.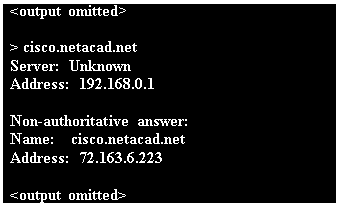
- Refer to the exhibit. What command was used to resolve a given host name by querying the name servers? (nslookup)
Correct
Incorrect
Hint
A user can manually query the name servers to resolve a given host name using the nslookup command. Nslookup is both a command and a utility. -
Question 23 of 27
23. Question
1 pointsMatch a statement to the related network model. (Not all options are used.)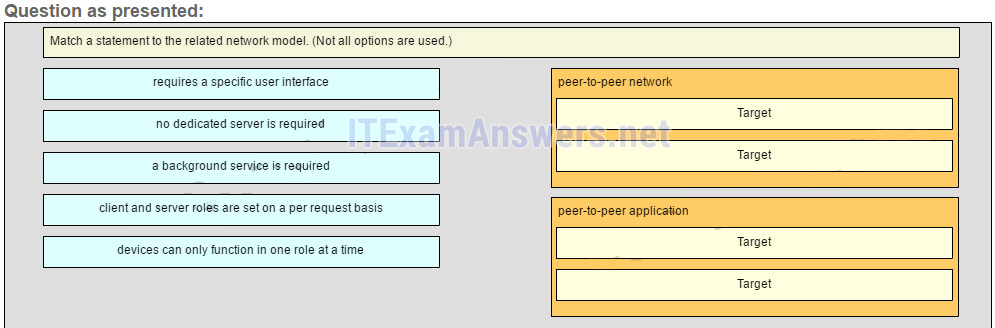
Sort elements
- no dedicated server is required
- client and server roles are set on a per request basis
- requires a specific user interface
- a background service is required
- devices can only funtion in one role at a time
-
peer-to-peer network (1)
-
peer-to-peer network (2)
-
peer-to-peer aplication (1)
-
peer-to-peer aplication (2)
Correct
Incorrect
Hint
Peer-to-peer networks do not require the use of a dedicated server, and devices can assume both client and server roles simultaneously on a per request basis. Because they do not require formalized accounts or permissions, they are best used in limited situations. Peer-to-peer applications require a user interface and background service to be running, and can be used in more diverse situations. -
Question 24 of 27
24. Question
1 pointsMatch the functions to the name of the application. (Not all options are used.)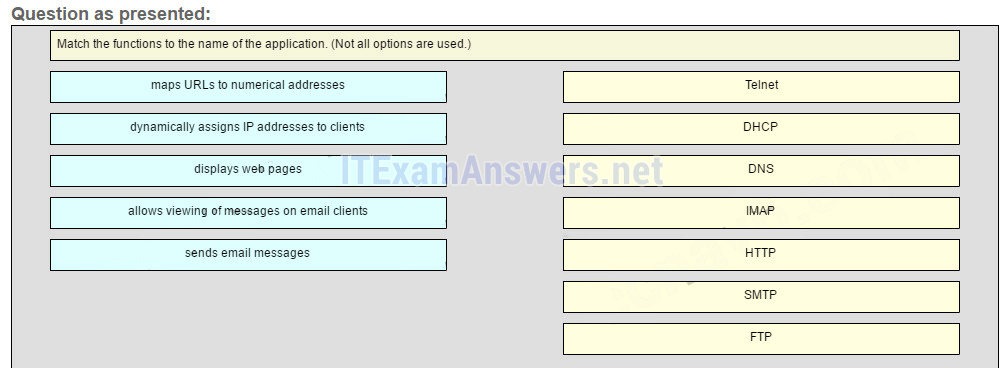
Sort elements
- DHCP
- DNS
- IMAP
- HTTP
- SMTP
- Telnet
- FTP
-
dynamically assigns IP address to clients
-
maps URLs to numerical addresses
-
allows viewing of messages on email clients
-
displays web pages
-
sends email messages
Correct
Incorrect
-
Question 25 of 27
25. Question
1 pointsWhat is the function of the Nslookup utility?Correct
Incorrect
Hint
Nslookup is a command-line utility that is used to send a query to DNS servers to resolve a specific host name to an IP address. -
Question 26 of 27
26. Question
1 pointsWhat message type is used by an HTTP client to request data from a web server?Correct
Incorrect
Hint
HTTP clients send GET messages to request data from web servers. -
Question 27 of 27
27. Question
1 pointsWhich protocol is used by a client to communicate securely with a web server?Correct
Incorrect
Hint
HTTPS is a secure form of HTTP used to access web content hosted by a web server.

i wanna be a CCNA ENG