Chapter 5 – Sections & Objectives
- 5.1 Ethernet Protocol
- Explain how the Ethernet sublayers are related to the frame fields.
- Describe the Ethernet MAC address.
- 5.2 LAN Switches
- Explain how a switch operates.
- Explain how a switch builds its MAC address table and forwards frames.
- Describe switch forwarding methods.
- Describe the types of port settings available for Layer 2 switches.
- 5.3 Address Resolution Protocol
- Compare the roles of the MAC address and the IP address.
- Describe the purpose of ARP.
- Explain how ARP requests impact network and host performance.
5.1 Ethernet Protocol
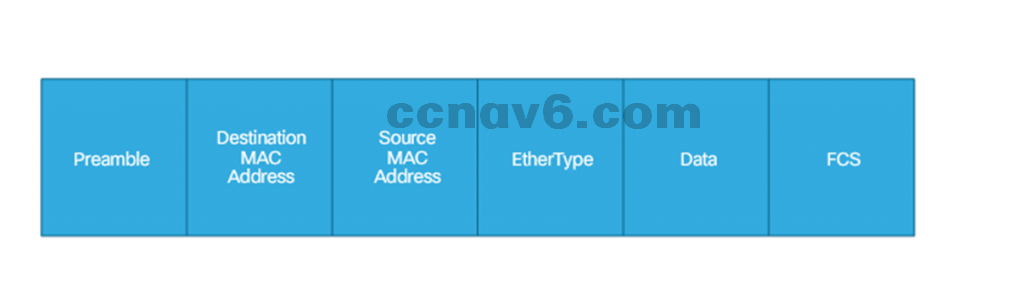
Ethernet Frame
- Ethernet Encapsulation
- Ethernet operates in the data link layer and the physical layer.
- Ethernet supports data bandwidths from 10Mbps through 100Gbps.
- Ethernet standards define both the Layer 2 protocols and the Layer 1 technologies.
- MAC Sublayer
- MAC constitutes the lower sublayer of the data link layer.
- Responsible for Data encapsulation and Media access control.
- Ethernet Evolution
- Ethernet has been evolving since its creation in 1973.
- The Ethernet frame structure adds headers and trailers around the Layer 3 PDU to encapsulate the message being sent.
- Ethernet Frame Fields
- The minimum Ethernet frame size is 64 bytes and the maximum is 1518 bytes.
- Frame smaller than the minimum or greater than the maximum are dropped.
- Dropped frames are likely to be the result of collisions or other unwanted signals and are therefore considered invalid.
Ethernet MAC Addresses
-
- MAC Addresses and Hexadecimal
– MAC address is 48-bit long and expressed as 12 hexadecimal digits.
- MAC Addresses: Ethernet Identity
– IEEE requires a vendor to follow two simple rules:- Must use that vendor’s assigned OUI as the first three bytes.
- All MAC addresses with the same OUI must be assigned a unique value in the last three bytes.
- Frame Processing
- The NIC compares the destination MAC address in the frame with the device’s physical MAC address stored in RAM.
- If there is a match, the framed is passed up the OSI layers.
- If there is no match, the device discards the frame.
- MAC Address Representations
- MAC addresses can be represented with colons, dashes or dots and are case-insensitive.
- 00-60-2F-3A-07-BC, 00:60:2F:3A:07:BC, 0060.2F3A.07BC and 00-60-2f-3a-07-bc are all valid representations of the same MAC address.
- Unicast MAC Address
- Unique address used when a frame is sent from a single transmitting device to a single destination device.
- The source MAC address must always be a unicast.
- Broadcast MAC Address
- Used to address all nodes in the segment.
- The destination MAC address is the address of FF-FF-FF-FF-FF-FF in hexadecimal (48 ones in binary).
- Multicast MAC Address
- Used to address a group of nodes in the segment.
- The multicast MAC address is a special value that begins with 01-00-5E in hexadecimal.
- The remaining portion of the multicast MAC address is created by converting the lower 23 bits of the IP multicast group address into 6 hexadecimal characters.
5.2 LAN Switches
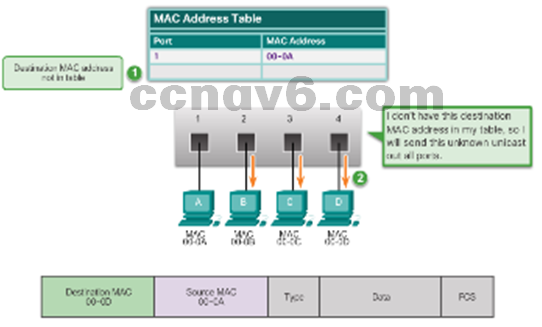
The MAC Address Table
- Switch Fundamentals
- An Ethernet Switch is a Layer 2 device.
- It uses MAC addresses to make forwarding decisions.
- The MAC address table is sometimes referred to as a content addressable memory (CAM) table.
- Learning MAC Addresses
- Switches dynamically build the CAM by monitoring source MACs.
- Every frame that enters a switch is checked for new addresses.
- The frame is forwarded based on the CAM.
- Filtering Frames
- Since the switch knows where to find a specific MAC address, it can filter the frames to that port only.
- Filtering is not done is the destination MAC is not present in the CAM.
Switch Forwarding Methods
- Frame Forwarding Methods on Cisco Switches
- Store-And-Forward
- Cut-Through
- Cut-Through Switching
- Fast-forward switching
- Lowest level of latency immediately forwards a packet after reading the destination address.
- Typical cut-through method of switching.
- Fragment-free switching
- Switch stores the first 64 bytes of the frame before forwarding.
- Most network errors and collisions occur during the first 64 bytes.
- Memory Buffering on Switches
- Port-based memory
- Share memory

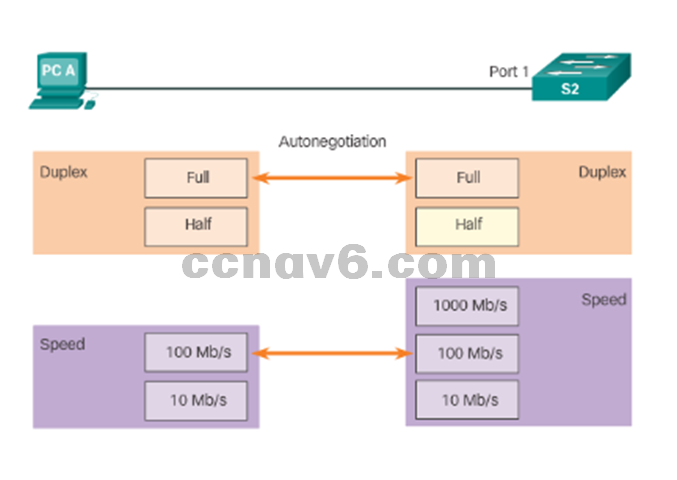
Switch Port Settings
- Duplex and Speed Settings
- Full-duplex – Both ends of the connection can send and receive simultaneously.
- Half-duplex – Only one end of the connection can send at a time.
- A common cause of performance issues on Ethernet links is when one port on the link operates at half-duplex and the other on full-duplex.
- Auto-MDX
- Detects the type of connection required and configures the interface accordingly.
- Helps reducing configuration errors.
5.3 Address Resolution Protocol
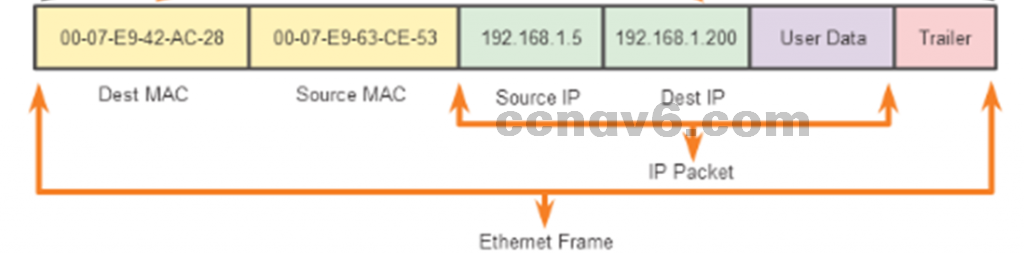
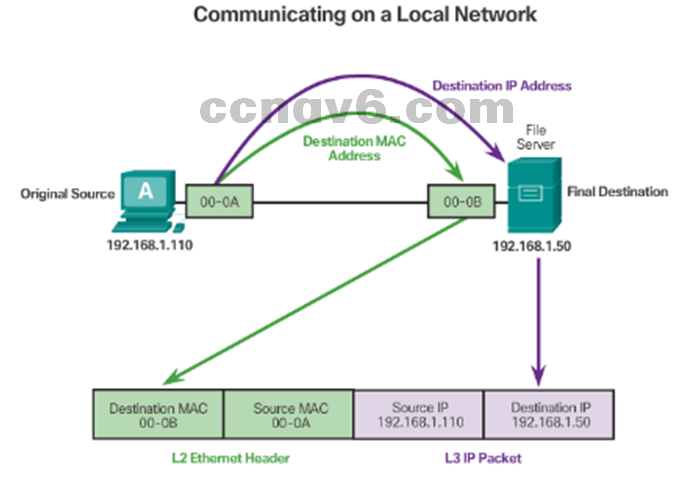
MAC and IP
- The combination of MAC and IP facilitate the End-to-End communication.
- Layer 2 addresses are used to move the frame within the local network
- Layer 3 addresses are used to move the packets through remote networks.
- Destination on Same Network
– Physical address (MAC address) is used for Ethernet NIC to Ethernet NIC communications on the same network. - Destination on Remote Network
– Logical address (IP address) is used to send the packet from the original source to the final destination.
ARP
- Introduction to ARP
- ARP allows the source to request the MAC address of the destination.
- The request is based upon the layer 3 address of the destination (known by the source).
- ARP Functions
- Resolving IPv4 addresses to MAC addresses
- Maintaining a table of mappings
- ARP uses ARP Request and ARP Reply to perform its functions.
- Removing Entries from an ARP Table
- Entries are removed from the device’s ARP table when its cache timer expires.
- Cache timers are OS dependent.
- ARP entries can be manually removed via commands.
- ARP Tables
- On IOS: show ip arp
- On Windows PCs: arp -a

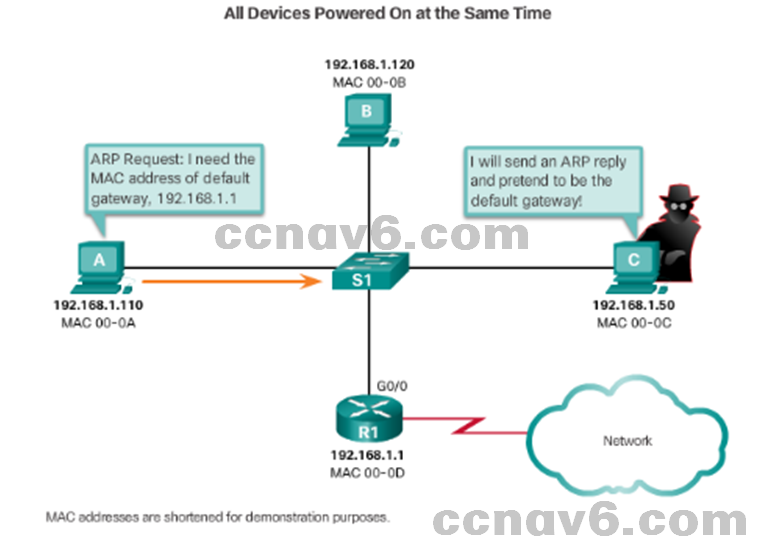
ARP Issues
- ARP Broadcasts
– ARP requests can flood the local segment. - ARP Spoofing
– Attackers can respond to requests and pretend to be providers of services. Example: default gateway
5.4 Chapter Summary
Chapter Summary Summary
- Explain the operation of Ethernet.
- Explain how a switch operates.
- Explain how the address resolution protocol enables communication on a network.
Section 5.1 New Terms and Commands
- IEEE 802.2
- IEEE 802.3
- LLC Sublayer
- MAC Sublayer
- Data Encapsulation
- Frame Delimiting
- Cyclic Redundancy Check
- Carrier Sense Multiple Access (CSMA)
- Ethernet II
- Frame Check Sequence (FCS)
- Preamble
- EtherType
- Runt
- Collision Fragment
- Jumbo
- Baby Giant Frame
- Hexadecimal
- Organizationally Unique Identifier (OUI)
Section 5.2 New Terms and Commands
- burned-in address (BIA)
- ipconfig /all command
- ifconfig command
- Unicast MAC Address
- Broadcast MAC Address
- Multicast MAC Address
- Content Addressable Memory (CAM)
- Store-and-forward
- Cut-through
- Fast-forward switching
- Fragment-free switching
- Port-based Memory Buffering
- Shared Memory Buffering
- Half-duplex
- Full-duplex
- Auto-MDIX
- Address Resolution Protocol (ARP)
Section 5.3 New Terms and Commands
- ARP Table
- ARP Cache
- ARP Request
- ARP Reply
- show ip arp, arp –a
- ARP spoofing
