Instructor Planning Guide
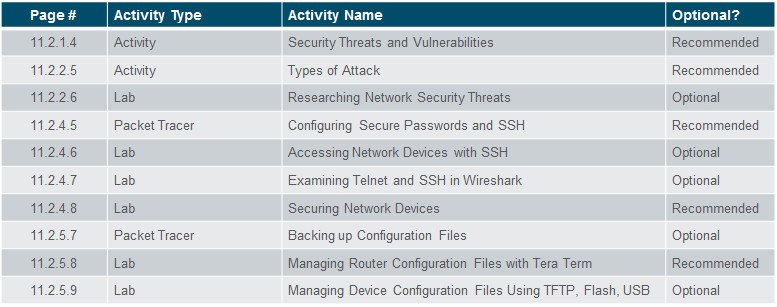
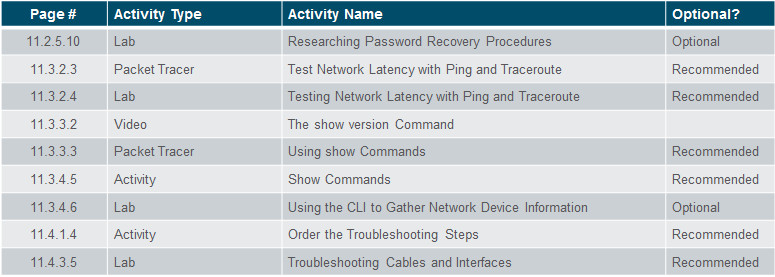
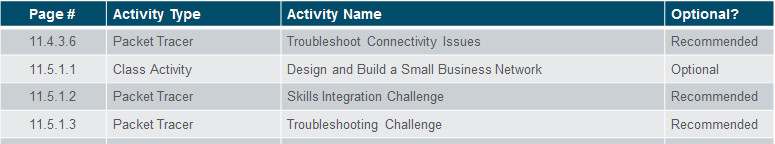
Activities
What activities are associated with this chapter?
Assessment
Students should complete Chapter 11, “Assessment” after completing Chapter 11.
Quizzes, labs, Packet Tracers and other activities can be used to informally assess student progress.
Sections & Objectives
11.1 Network Design
Explain how a small network of directly connected segments is created, configured, and verified.
Identify the devices used in a small network.
Identify the protocols used in a small network.
Explain how a small network serves as the basis of larger networks.
11.2 Network Security
Configure switches and routers with device hardening features to enhance security.
Explain why basic security measures are necessary on network devices.
Identify security vulnerabilities.
Identify general mitigation techniques.
Configure network devices with device hardening features to mitigate security threats.
11.3 Basic Network Performance
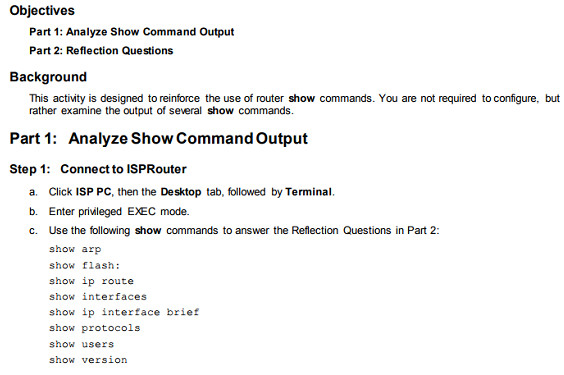
Use common show commands and utilities to establish relative performance baseline for the network.
Use the output of the ping command to establish relative network performance.
Use the output of the tracert command to establish relative network performance.
Use show commands to verify the configuration and status of network devices.
Use host and IOS commands to acquire information about the devices in a network.
11.4 Network Troubleshooting
Troubleshoot a network.
Describe common network troubleshooting methodologies.
Troubleshoot cable issues and interface issues.
Troubleshoot issues with devices in the network.
Chapter 11: Build a Small Network
11.1 – Network Design
11.1.1 – Devices in a Small Network
11.1.1.1 – Small Network Topologies
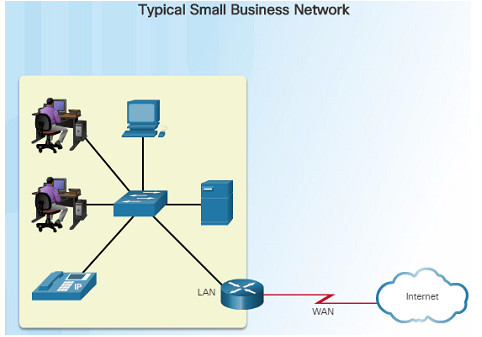
The majority of businesses are small and typically require small networks consisting of a single router with one or more switches and possibly one or more wireless access points. The business might also have IP phones.
- For the Internet connection, the router will normally have a single WAN connection using DSL, cable, or an Ethernet connection.
Managing a small network is similar to managing a large network:
- Maintenance and troubleshooting of existing equipment
- Securing devices and information on the network
11.1.1.2 – Device Selection for a Small Network
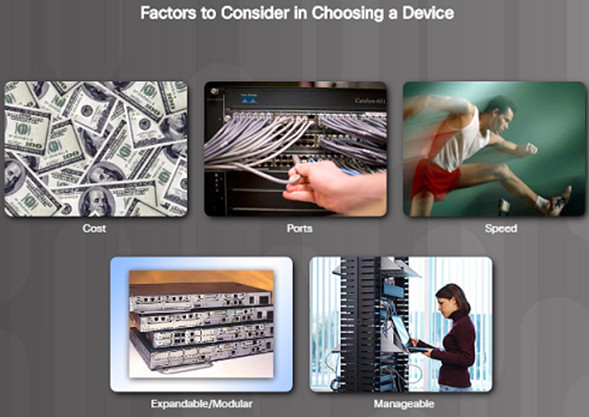
Regardless of the size, all networks require planning and design to ensure that all requirements, cost factors, and deployment options are considered:
- Cost – The cost of a switch or router is determined by its capacity and features.
- Speed and Types of Ports/Interfaces – Choosing the number and types of ports on a router or switch is an important decision.
- Expandability – Networking devices come in both fixed and modular physical configurations for expandability and flexibility.
- Operating System Features and Services – Features and services should be considered including: security, QoS, VoIP, Layer 3 switching, NAT and DHCP.
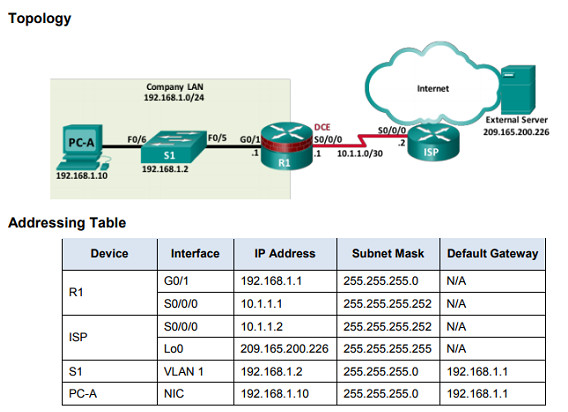
11.1.1.3 – IP Addressing for a Small Network
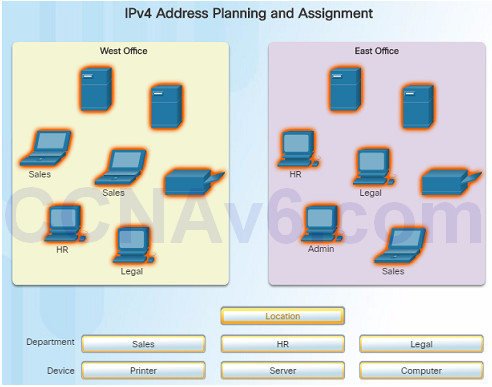
IP addressing space must be planned when implementing a small network.
All hosts within an internetwork must have a unique address.
Different types of devices will factor into the IP design including:
- End devices for users
- Servers and peripherals
- Hosts that are accessible from the Internet
- Intermediary devices
Planning and documenting the IP addressing scheme helps administrators track device types. For example, if all servers are assigned a host address in the range of 50-100, it will be easier to identify server traffic by their IP address.
11.1.1.4 – Redundancy in a Small Network
Reliability is another important element of network design – a network failure can be costly
The figure to the left represents a Data Center network.
There are 4 types of redundancy in this figure:
- Redundant servers
- Redundant links
- Redundant switches
- Redundant routers
A server, link, switch, or router could fail and the network would continue to function.

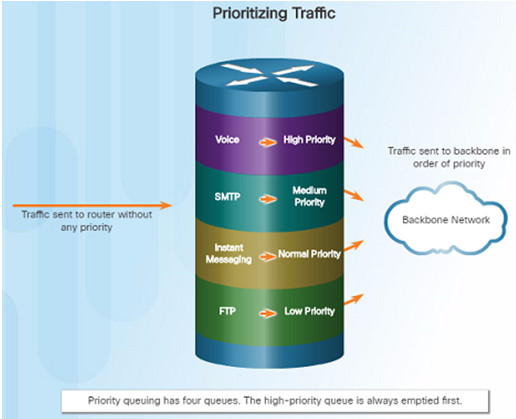
11.1.1.5 – Traffic Managment
The types of traffic and how they should be handled should be considered and prioritized in the network design.
Routers and Switches in a small network should be configured to support real-time traffic such as voice and video. For example:
- Voice à High Priority
- Video à High Priority
- SMTP à Medium Priority
- Instant Messaging à Normal Priority
- FTP à Low Priority
Network traffic should be classified according to priority in order to enhance productivity of employees and minimize network downtime.
11.1.2 – Small Network Applications and Protocols
11.1.2.1 – Common Applications
There are two forms of software programs or processes that provide access to the network:
- Network Applications – The software programs used to communicate over the network. Some end-user applications are network aware, and are able to communicate directly with the lower layers of the protocol stack. Examples include email clients and web browsers.
- Application Layer Services – Other programs need the assistance of application layer services to use network resources such as fire transfer or network print spooling.
Each application or network service uses protocols, which define the standards and data formats to be used to format and direct data.

11.1.2.2 – Common Protocols
Most network professionals work with network protocols which support the applications and services used by employees in a network.
The figure on the left lists some common network protocols that are used in most networks – including small networks.
- Each of these network protocols define:
- Processes on either end of a communication session.
- Types of messages
- Syntax of the messages
- Meaning of information fields
- How messages are sent and the expected response
- Interaction with the next lower layer
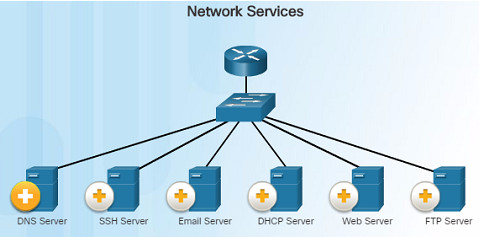
DNS – Service that provides the IP address of a website or domain name so a host can connect to it without using the numerical IP address.
DHCP Server – Service that assigns an IP address, subnet mask, default gateway and other information to clients so they don’t have to enter them manually.
11.1.2.3 – Voice and Video Applications
Businesses today are increasingly using IP telephony and streaming media to communicate with customers and business partners.
A network administrator must ensure that the network can support these applications and services including a supporting infrastructure with appropriate switches and cabling.
VoIP devices convert analog signals into digital IP packets. After the signals are converts into IP packets, the router sends those packets between corresponding locations.

In IP Telephony, the IP phone itself performs the voice-to-IP conversion. Voice-enabled routers are not required within a network with an integrated IP telephony solution. IP Phones use a dedicated server for call control and signaling.
Real-time Applications – the network must be able to support applications that require delay-sensitive delivery. Real-Time Transport Protocol (RTP) and Real-Time Transport Control Protocol (RTCP) are two protocols that support this requirement.
11.1.3 – Scale to Larger Networks
11.1.3.1 – Small Network Growth
The network administrator must allow for growth for small businesses and their networks.
Ideally, the network administrator has enough lead time to allow the network to grow in-line with the growth of the company.
To scale a network, the following are required:
- Network documentation – physical and logical topology
- Device inventory – list of devices that use or comprise the network
- Budget – itemized IT budget, including fiscal year equipment purchasing budget
- Traffic analysis – protocols, applications, and services along with their traffic requirements should be documented
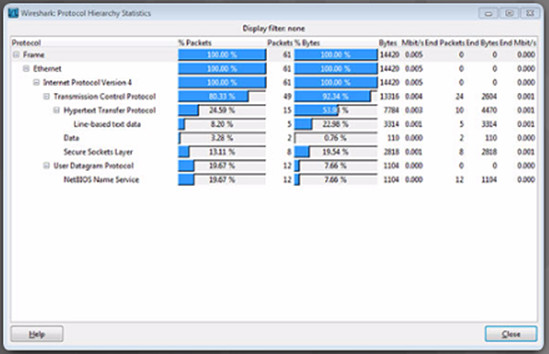
11.1.3.2 – Protocol Analysis
As a network grows, it is very important to understand the type of traffic that is crossing the network as well as the traffic flow.
A protocol analyzer is the primary tool used for this. It can also help identify any unknown traffic and its source.
To determine traffic flow patterns:
- Capture traffic during peak utilization times.
- Perform the capture on different network segments since some traffic will be local to particular segments.
The analysis of traffic patterns can be used to help make decisions on how to manage the traffic for efficiency.
11.1.3.3 – Employee Network Utilization
In addition to understanding changing traffic trends, a network administrator must also be aware of how network use is changing.
A network administrator has the ability to obtain in-person IT “snapshots” of employee application utilization over time. This information can help the network administrator adjust network resources as necessary. These snapshots typically include:
- OS and OS Version
- Non-Network Applications
- Network Applications
- CPU Utilization
- Drive Utilization
- RAM Utilization
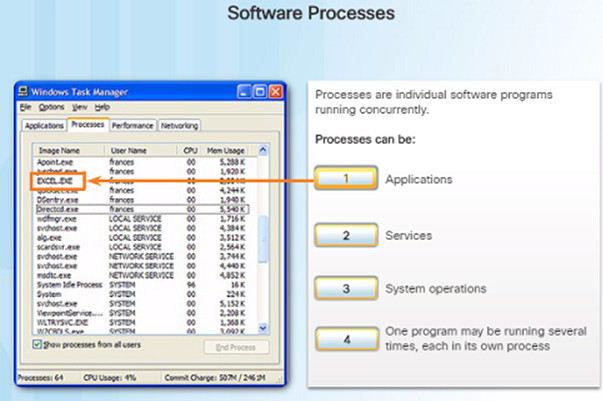
Examples of processes running in the Windows operating system
11.2 – Network Security
11.2.1 – Security Threats and Vulnerabilities
11.2.1.1 – Types of Threats
Computer networks are essential to everyday activities. Individuals and organizations depend on their computers and networks.
An intrusion by an unauthorized person can result in costly network outages and loss of work.
Attacks on a network can be devastating and can result in a loss of time and money.
Intruders can gain access to a network through software vulnerabilities, hardware attacks, or something as simple as password guessing – these intruders are called hackers.

Four types of threats might occur:
Information Theft – Occurs when someone breaks into a computer for the purpose of stealing confidential information.
Data Loss and Manipulation – This is breaking into a computer to destroy or alter data records. An example of data loss: a virus that reformats a person’s hard drive. An example of data manipulation: breaking into a system to change the price of an item.
Identity Theft – This is a form of information theft where personal information is stolen for the purpose of stealing someone’s identity.
Disruption of Service – This is preventing legitimate users from accessing services to which they should be entitled.
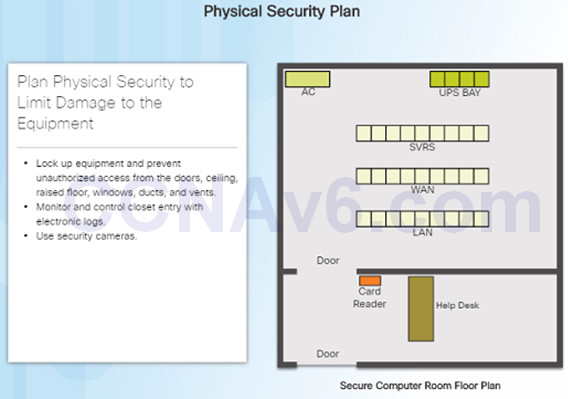
11.2.1.2 – Physical Security
The physical security of network devices is an equally important security vulnerability to manage.
There are four classes of physical threats that must be dealt with:
- Hardware threats – physical damage to servers, routers, switches, cabling plant, and workstations
- Environmental threats – temperature extremes (too hot or cold) or humidity extremes
- Electrical threats – voltage spikes, insufficient supply voltage (brownouts), unconditioned power and power outages.
- Maintenance threats – poor handling of key electrical components (electrostatic discharge), lock of critical spare parts, and poor labeling.
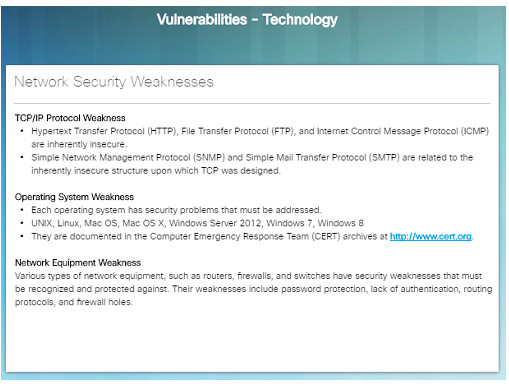
11.2.1.3 – Types of Vulnerabilities
Vulnerability is the degree of weakness which is inherent in every network and device and includes: routers, switches, desktops, servers, and security devices.
Typically, servers and desktop computers are the devices under attack.
There are three primary vulnerabilities that can lead to various attacks. Here are some examples
- Technological – Weaknesses within insecure protocols, Operating System and network equipment weaknesses.
- Configuration – Unsecured user accounts, system accounts with easily guessable passwords, misconfigured network equipment.
- Security policy – Lack of a written security policy, inadequate monitoring and auditing of the network and resources.
11.2.2 – Network Attacks
11.2.2.1 – Types of Malware
Malware or malcode is short for malicious software – software or code that is designed to damage, disrupt, steal, or inflict damage on data, hosts, or networks.
Viruses, worms, and Trojan horses are examples of malware.
- Viruses – Type of malware (executable file) that is propagated by inserting a copy of itself into and becoming a part of another program. It spreads from computer to computer.
- Worms – Very similar to viruses, but do not require a host program. Worms are standalone software programs that take advantage of system features to trave; through the network.
- Trojan horses – Users are typically tricked into loading and executing this malware on their systems. They usually create back doors to give malicious users access to the system.
11.2.2.2 – Reconnaissance Attacks
In addition to malicious code attacks, networks can also fall prey to various network attacks. There are three major categories of network attacks:
- Reconnaissance attacks – the discovery and mapping of systems, services, or vulnerabilities
- Access attacks – the unauthorized manipulation of data, system access, or user privileges
- Denial of Service – the disabling or corruption of networks, systems, or services
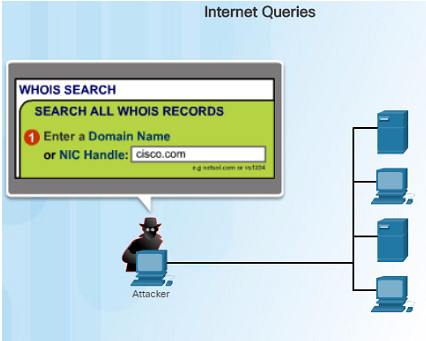
In a Reconnaissance attack, a hacker could use either nslookup or whois to determine the IP addresses assigned to an entity. Once they have the IP address, they can use fping to ping a range of IP addresses to see who is responding. Once they know what IP addresses are responding, they could use nmap to see which ports are listening.
11.2.2.3 – Access Attacks
Access attacks exploit known vulnerabilities in authentication services, FTP services, and web services to gain entry to web accounts, confidential databases, or access other resources. There are four classes of access attacks:
- Password attacks – Hackers can use several methods including: brute-force attacks, Trojan horse programs, and packet sniffers.
- Trust Exploitation – An attacker can access a target system by taking advantage of a trust relationship between the target system and one that is compromised.
- Port Redirection – A hacker installs software on an compromised host and uses that host to access a target host on a different port.
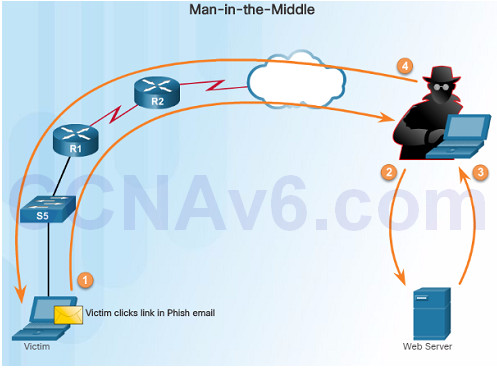
- Man-in-the-middle – An attacker inserts himself in the middle of a conversation. A common type is a Phish email that a victim clicks a link on in their email.
11.2.2.4 – Denial of Service Attacks
Denial of Service (DoS) attacks prevent authorized people from using a service by using up system resources such as disk space, bandwidth, and buffers. The attack can be caused by resource overload or malformed data.
DoS attacks are the most publicized and the most difficult to eliminate. Here are some examples of DoS attacks:
- Ping of Death – An attacker sends a malformed or a very large ping packet.
- SYN Flood – An attacker sends multiple SYN requests to a web server. The web server waits to complete the TCP three-way handshake. A valid user tries to send a SYN request to the web server, but the web server is unavailable
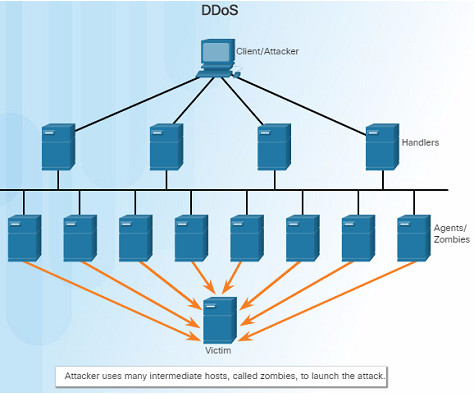
DDoS – an Attacker uses many intermediate hosts, called zombies, to launch an attack on the victim host or server. The intermediate hosts used to launch the attack are usually infected with malware giving control to the attacker.
Smurf attack – an ICMP-based attack where an attacker broadcasts a large number of ICMP packets using the victim’s source IP address. The zombie hosts reply to the target victim in an attempt to overwhelm the WAN link to the destination.
11.2.2.6 – Lab – Researching Network Security Threats
11.2.2.6 Lab – Researching Network Security Threats
In order to defend against network attacks, an administrator should be able to identify external threats that could pose a danger to the network.
This lab will allow you to research network security threats by exploring a very important security-related website, as well as researching recent threats and detailing a specific network security threat.
11.2.3 – Network Attack Mitigation
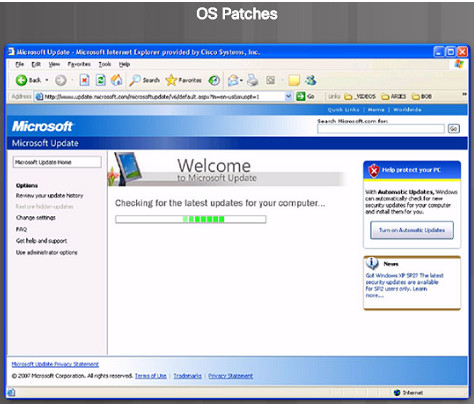
11.2.3.1 – Backup, Upgrade, Update, and Patch
Keeping up-to-date with the latest developments is a critical part of network security and defending against network attacks.
As new malware is released, enterprises need to keep current with the latest versions of antivirus software.
The most effective way to mitigate worm or other attacks is to download security updates from the operating system vendor and install patches on all vulnerable systems.
The use of a central patch server to install critical patches automatically is a very useful solution to this issue.
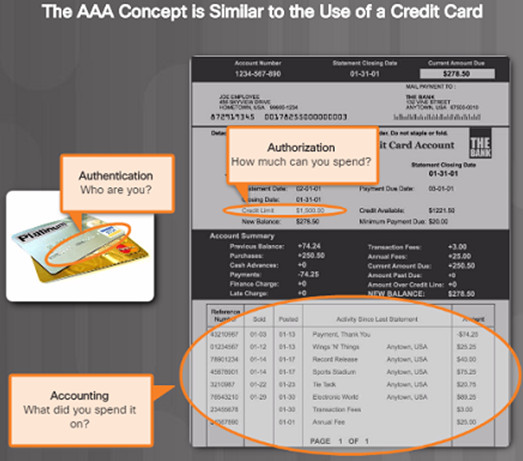
11.2.3.2 – Authentication, Authorization, and Accounting
Authentication, authorization, and accounting (AAA) network security services provide the framework to set up access control on a network device.
AAA is used to control who is permitted to access a network (authentication), what they can do while they are there (authorize), and what did they do when they were accessing the network (accounting).
11.2.3.3 – Firewalls
Firewalls are one of the most effective security tools available for protecting users from external threats.
Network firewalls reside between two or more networks, control the traffic between them and help prevent unauthorized access. Host-based firewalls or personal firewalls are installed on end systems.
Firewalls use various techniques for determining what is permitted or denied:
- Packet filtering – Prevents or allows access based on IP or MAC addresses
- Application filtering – Prevents or allows access by specific application types based on port numbers
- URL filtering – Prevents or allows access to websites based on specific URLs or keywords
- Stateful packet inspection (SPI) – Incoming packets must be legitimate responses to requests from external hosts. Traffic coming in through the firewall from the outside must originate from the inside network unless specifically permitted.

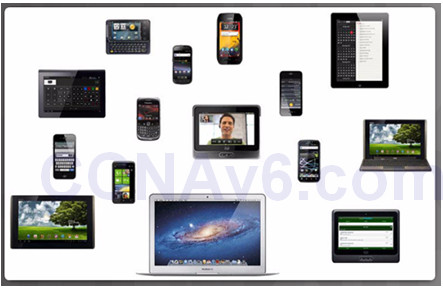
11.2.3.4 – Endpoint Security
An endpoint, or host is an individual computer system or device that acts as a network client.
Common endpoints include: laptops, desktops, servers, smartphones, and tablets.
A company must have a well-documented policy in place that employees must follow since securing endpoint devices is one of the most challenging jobs of a network administrator.
The policy should include the use of antivirus software and host intrusion prevention.
11.2.4 – Device Security
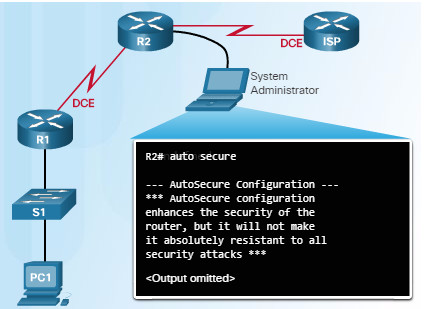
11.2.4.1 – Device Security Overview
When a new operating system is installed on a device, the security settings are set to the default values.
This usually leads to a security threats and the default settings including passwords should be changed.
System updates and security patches should be installed.
For Cisco routers, the Cisco AutoSecure feature can be used to assist in securing the system.
Here are some simple steps that should be taken to most operating systems:
- Default usernames and passwords should be changed immediately.
- Access to system resources should be restricted to only those who need those resources.
- Unnecessary services and applications should be turned off, disabled, and uninstalled if possible.
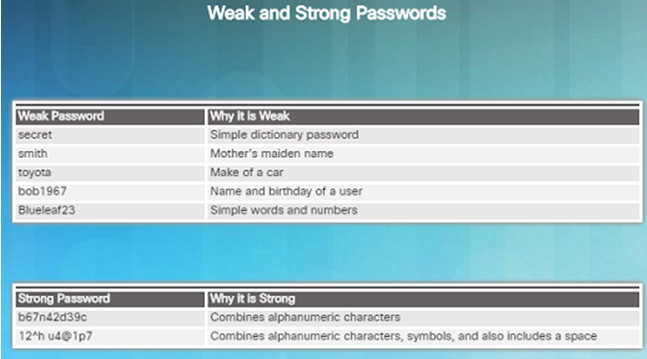
11.2.4.2 – Passwords
Strong passwords are critical in protecting network devices.
Here are some password guidelines to follow:
- Use a password of at least 8 to 10 characters – preferably 10 or more. The longer the better.
- Password should be complex. Include a mix of uppercase, lowercase, numbers, symbols, and spaces if allowed.
- Do not use passwords based on repetition, common dictionary words, letter or number sequences, usernames, relative or pet names, biographical information or any easily identifiable information.
- Deliberately misspell words in your passwords.
- Change your passwords often.
- Never write down your passwords and leave where anyone can find them.
- Use passphrases when possible.
11.2.4.3 – Basic Security Practices
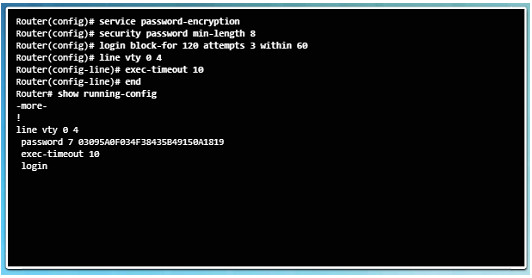
In order to ensure that all configured passwords are a minimum length, use the security passwords min-length command in global configuration mode.
Hackers frequently use a brute-force attack to decrypt encrypted passwords. Block excessive login attempts to a device if a set number of failures occur within a specific amount of time using the command login block-for 120 attempts 3 within 60
This command will block login attempts for 120 seconds if there are three failed login attempts within 60 seconds
Setting the exec timeout on a router will automatically disconnect users if they have been idle for the duration of the timeout value.
Use the global configuration command service password-encryption to encrypt passwords in the configuration file and prevent unauthorized individuals from viewing plain text passwords.
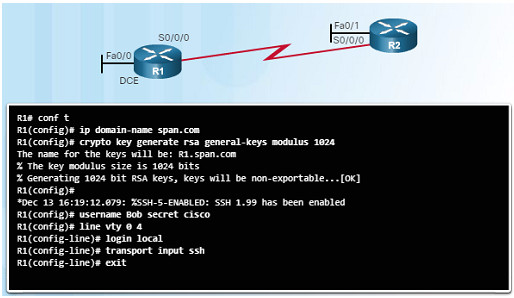
11.2.4.4 – Enable SSH
11.2.4.5 Packet Tracer – Configuring Secure Passwords and SSH
11.2.4.5 Packet Tracer – Configuring Secure Passwords and SSH
11.2.4.6 Lab – Accessing Network Devices with SSH
11.2.4.6 Lab – Accessing Network Devices with SSH
11.2.4.7 Lab – Examining Telnet and SSH in Wireshark
11.2.4.7 Lab – Examining Telnet and SSH in Wireshark
11.2.4.8 Lab – Securing Network Devices
11.2.4.8 Lab – Securing Network Devices
11.3 – Basic Network Performance
11.3.1. – The ping Command
11.3.1.1 – Interpreting Ping Results
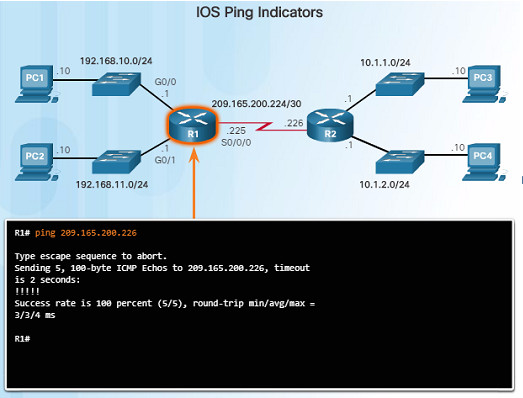
The use of the ping command is a very effective method to test for network connectivity to a particular host, server, or device – it is an important first step in troubleshooting a network failure.
The ping command uses the Internet Control Message Protocol and verifies layer 3 connectivity.
A ping issued from the IOS, such as a Cisco router, will yield several indicators. The most common are:
- ! – indicates receipt of an ICMP echo message. This is what you want to see.
- . – indicates a time expired while waiting for an ICMP echo reply message
- U – an ICMP unreachable message with received
11.3.1.2 – Extended Ping
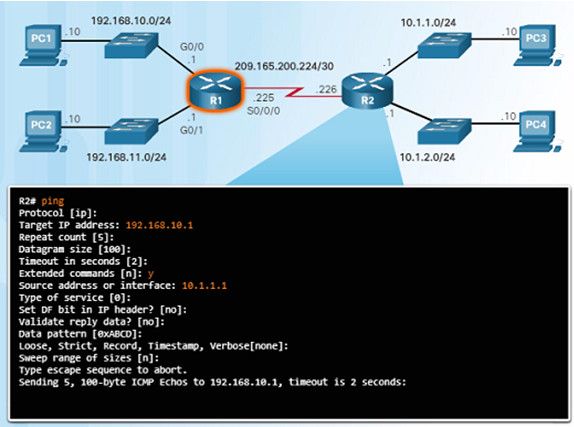
The Cisco IOS offers an “extended” mode of the ping command which will give you more options as shown in the figure to the left.
This mode is entered by typing ping in privileged EXEC mode, without a destination IP address – just type ping and press ENTER.
The example in the figure to the left demonstrates how to force or change the source IP address. This is very useful when troubleshooting.
11.3.1.3 – Network Baseline
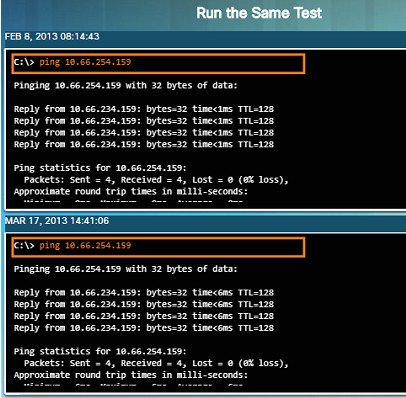
Establishing a network baseline is one of the most effective tools for monitoring and troubleshooting network performance.
Creating an effective baseline is accomplished by measuring performance at various times over a period of time.
One method that can be used is to copy and paste the results from a ping, trace, or other relevant commands into a text file with a time stamp.
Corporate networks should have extensive baseline statistics using professional-grade software tools
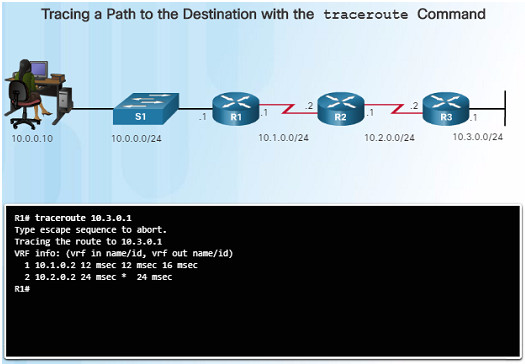
11.3.2 – The traceroute and tracert Command
11.3.2.1 – Interpreting Trace Messages
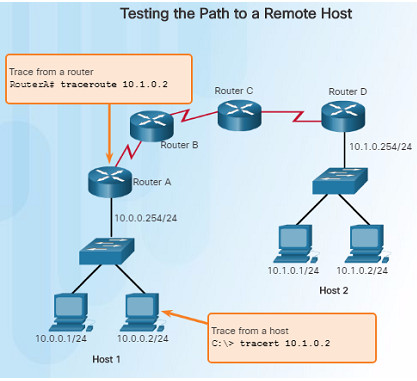
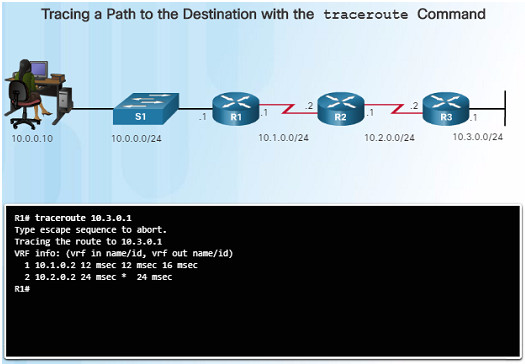
A trace returns a list of hops as a packet is routed through a network. Each router is a hop.
When using windows, use the tracert command.
When performing a trace from a router CLI, use the traceroute command.
A “Request timed out” response indicates that the router did not respond. It is possible that there is a network failure, or the routers were configured to not respond to echo requests used in the trace.
11.3.2.2 – Extended Traceroute
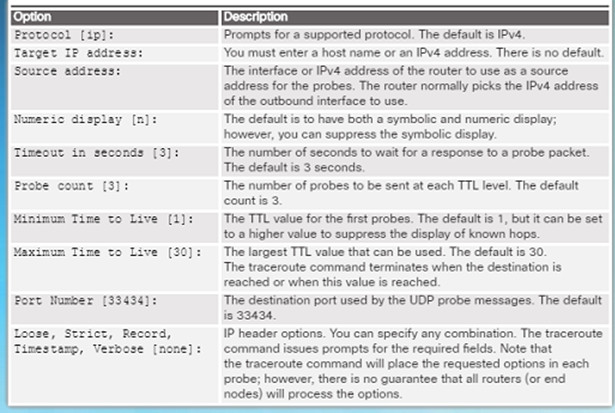
The extended traceroute command is a variation that will allow the network administrator to adjust parameters related to the command.
This command is very useful when troubleshooting routing loops, determining the exact next-hop router, or determining where packets are getting dropped by a router, or denied by a firewall.
The extended traceroute command can be useful in locating the problem. To use the command, type traceroute and press ENTER.
While ping sends icmp packets, traceroute sends IP packets with a TTL value (30 by default).
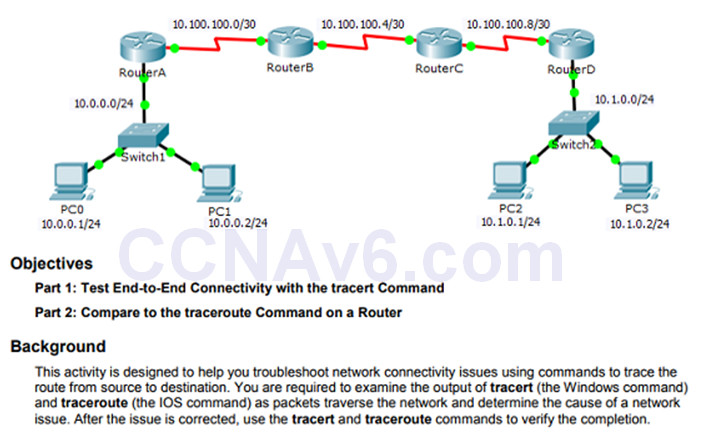
11.3.2.3 – Packet Tracer – Test Connectivity with Traceroute
11.3.2.3 Packet Tracer – Test Connectivity with Traceroute
This Packet Tracer activity will allow you to troubleshoot network connectivity issues using trace commands.
You will be required to examine the output of the tracert and traceroute commands to identify the issue.
Once the issue is corrected, you will have to verify everything is working using the same commands.
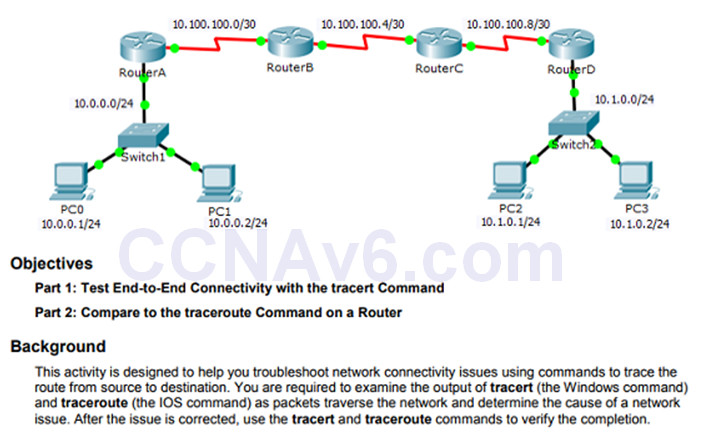
11.3.2.4 – Lab – Testing Network Latency with Ping and Traceroute
11.3.2.4 Lab – Testing Network Latency with Ping and Traceroute
This Lab will allow you to test network latency using the ping and traceroute commands on a live network.
A live network must be used in order to obtain realistic network latency statistics.
 11.3.3 – Show Commands
11.3.3 – Show Commands
11.3.3.1 – Common show Commands Revisited
Network technicians use show commands extensively for verifying the configuration and operation of a device or for troubleshooting purposes.
Common show commands include:
- show running-config
- show interfaces
- show arp
- show ip route
- show protocols
- show version
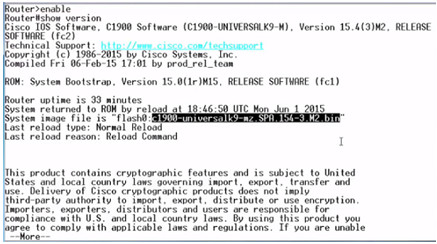
11.3.3.2 – Video Demonstration – The show version Command
This video demonstration walks through the output of the show version command when issued on a Cisco 1941 router.
The IOS software version is highlighted in the figure to the left.
- Details about the output are covered including:
- The time that the router has been up
- Version information
- Interface and memory details
11.3.3.3 – Packet Tracer – Using show Commands
11.3.3.3 Packet Tracer – Using show Commands
This Packet Tracer activity will allow you to practice various show commands and examine the output of those commands.
11.3.4 – Host and IOS Commands
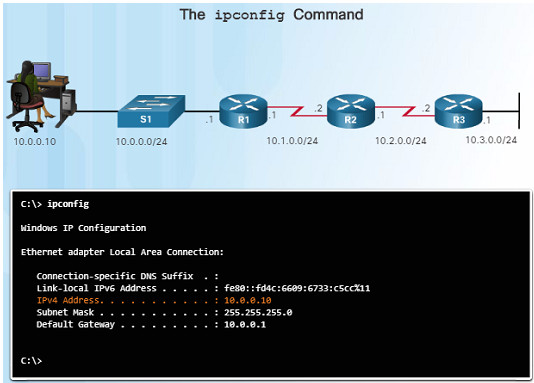
11.3.4.1 – The ipconfig Command
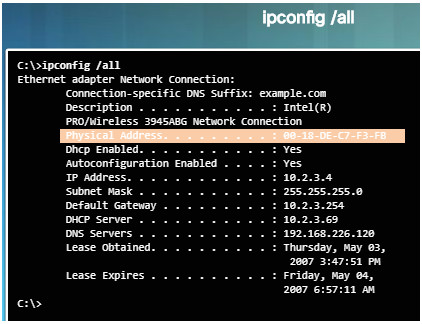
On a Windows computer, the IP address of the default gateway can be viewed by using the ipconfig command.
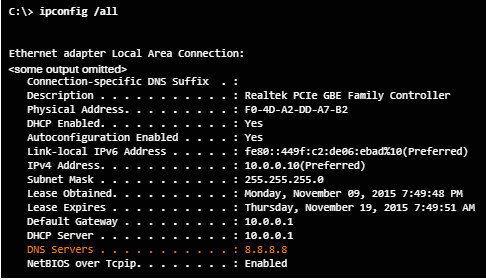
The ipconfig /all command can be used to view the MAC address as well as other important details regarding the Layer 3 addressing of the device.
The ipconfig /displaydns command displays all of the cached DNS entries on a Windows computer system.
11.3.4.2 – The arp Command
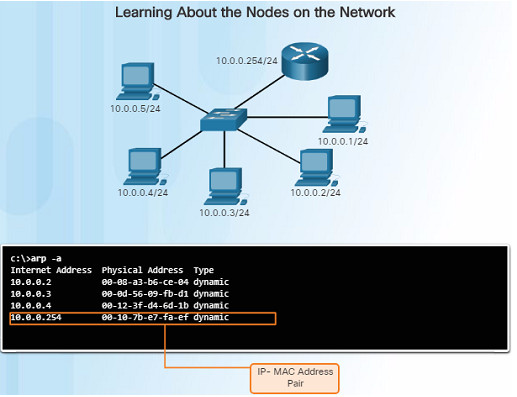
On a Windows computer, the arp -a command lists all devices currently stored in the ARP cache of a particular host.
The IPv4 address, physical address, and the type of addressing (static/dynamic) is displayed for each device.
The arp cache can be cleared using the command arp-d
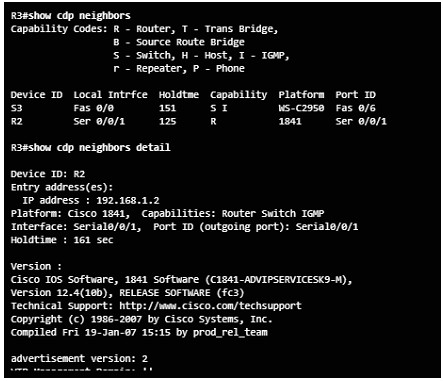
11.3.4.3 – The show cdp neighbors Command
The Cisco Discovery Protocol (CDP) is a Cisco-proprietary protocol that runs at the data link layer that allows adjacent Cisco devices to learn about each other – even without Layer 3 connectivity.
When a Cisco device boots up, CDP starts by default. CDP automatically discovers neighboring devices running CDP.
CDP provides the following information about each CDP neighbor: device identifiers, address list, port identifier, capabilities list, and platform.
The show cdp neighbors detail command will show you the IP address of a neighboring device.
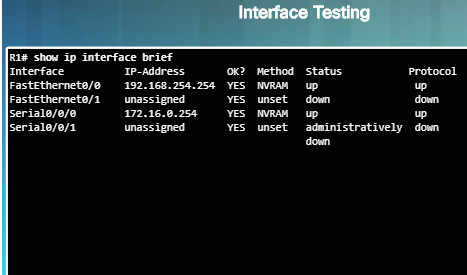
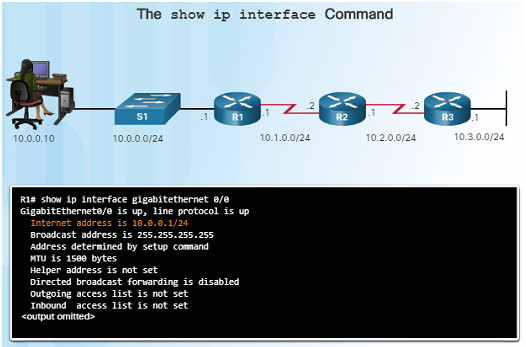
11.3.4.4 – The show ip interface brief Command
One of the most frequently used commands to verify interface configuration and status of all interfaces is the show ip interface brief command.
This command provides a more abbreviated output than the show ip interface command and provides a summary of the key information for all of the network interfaces on a router.
The command displays various information including the IP address assigned to each interface and the operational status of the interface.
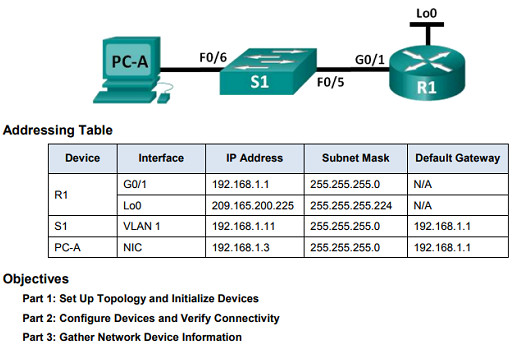
11.3.4.6 – Lab – Using the CLI to Gather Network Device Information
11.3.4.6 Lab – Using the CLI to Gather Network Device Information
Documenting a network is one of the most important tasks of a network professional.
In this lab, you will build a small network, configure the devices, add some basic security, and then document the configurations by using various commands on the router, switch, and PC.
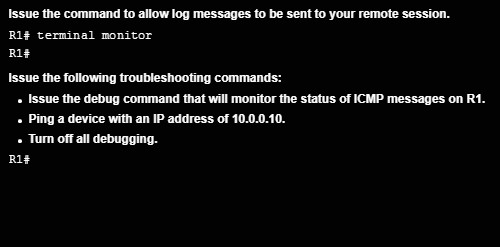
11.3.5 – Debugging
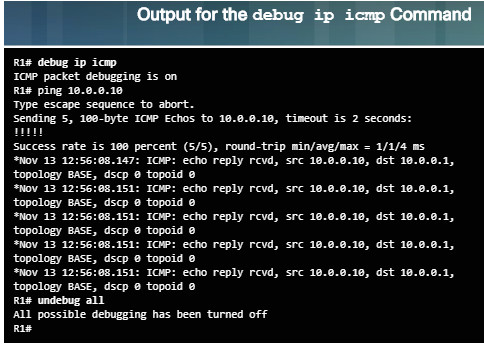
11.3.5.1 – The debug Command
IOS processes, protocols, mechanisms and events generate messages to communicate their status.
These messages can provide valuable information when troubleshooting or verifying system operations.
The IOS debug command, entered in privileged EXEC mode, allows the administrator to display these message in real-time for analysis.
It is possible to narrow the output of the debug command to include only the relevant feature or sub-feature that is needed.
11.3.5.2 – The terminal monitor Command
Connections to grant access to the IOS command line interface can be established locally or remotely.
- Local connections require physical access to the router or switch using a cable.
- Remote connections using SSH or Telnet are made using the network and require a network protocol such as IP to be configured.
Debugging long messages are sent to the console by default and not to virtual lines.
To display log messages on a terminal or virtual console, use the privileged EXEC command: terminal monitor and terminal no monitor to turn it off.
11.4 – Network Troubleshooting
11.4.1 – Troubleshooting Methodologies
11.4.1.1 – Basic Troubleshooting Approaches
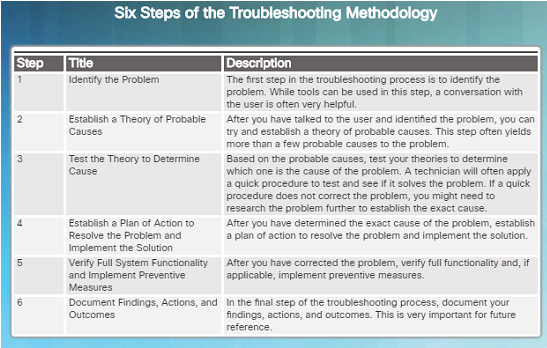

Technicians must be able to analyze the cause of the network problem before they can resolve the issue.
This process is called troubleshooting.
A common and efficient method is based on the scientific method and can be broken down into six steps shown in the figure to the left.
How many devices on the network are experiencing the problem?
- If it’s one device, start troubleshooting at that device.
- If it’s all devices, start troubleshooting at the device where all of those devices are connected.
11.4.1.2 – Resolve or Escalate?
In some cases, it may not be possible to resolve the network problem immediately and may need to be escalated if it requires a manager’s decision.
For example, after troubleshooting, the technician discovers that a router module needs to be replaced. This problem should be escalated for the manager’s approval since it might require a financial commitment.

11.4.1.3 – Verify and Monitor Solution
The Cisco IOS includes powerful tools to help with troubleshooting and verification such as:
ping – can be used to verify successful network connectivity
traceroute – displays the path that packets are using to reach a destination and may show where the packet stopped along the way
Show commands including show ip int brief which will show a summarized view of the interfaces on a device
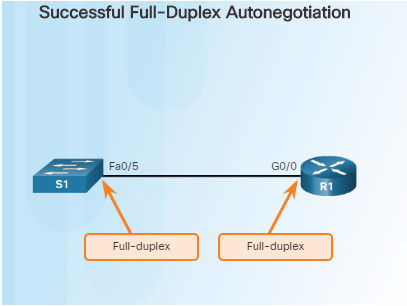
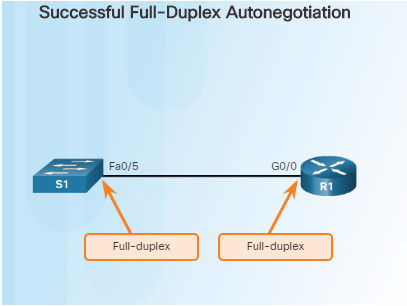
11.4.2.1 – Duplex Operation
In data communications, duplex refers to the direction of the data transmission between two devices such as a router and a switch.
- Half-duplex – the data is restricted to one direction at a time
- Full duplex – the data can go both directions at the same time
For the best communication performance, two connected Ethernet network interfaces must have matching duplex configurations.
- They must both be set to full or half.
- Ethernet autonegotiation was designed to help with this configuration, but could lead to problems if one side is set to auto and the other is not.
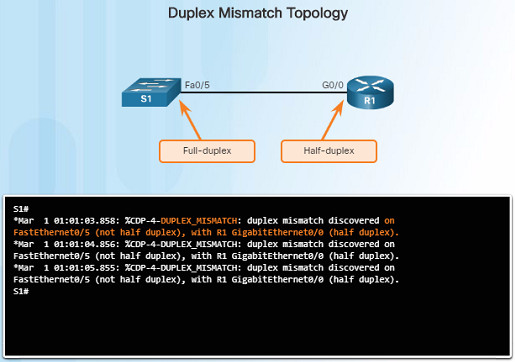
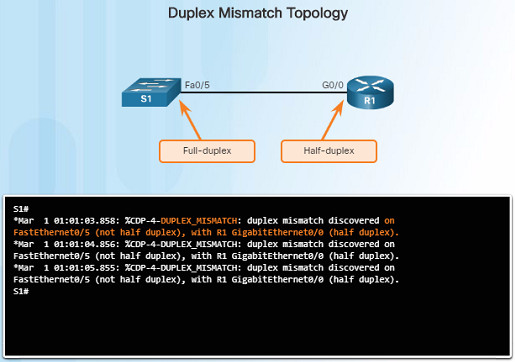
11.4.2.2 – Duplex Mismatch
Duplex mismatch issues are difficult to troubleshoot since the communication between devices still occurs, but is usually much slower.
- ping might not detect the problem.
- A ping could be successful even though there is a mismatch
The Cisco Discovery Protocol (CDP) can detect a duplex mismatch between two Cisco devices as shown in the figure to the left.
These log messages are only displayed on a console or on a remote connection if the terminal monitor command is enabled.
11.4.3 – Troubleshooting Scenarios
11.4.3.1 – IP Addressing Issues on IOS Devices
IP address-related problems will likely cause connectivity issues.
Since IP addresses are hierarchical, any IP addresses assigned to a network device must conform to that network’s range of addresses.
Two common causes of incorrect IPv4 assignments are: manual misconfiguration or DHCP-related issues.
If a mistake is made during the assignment, communication issues with the device will likely occur.
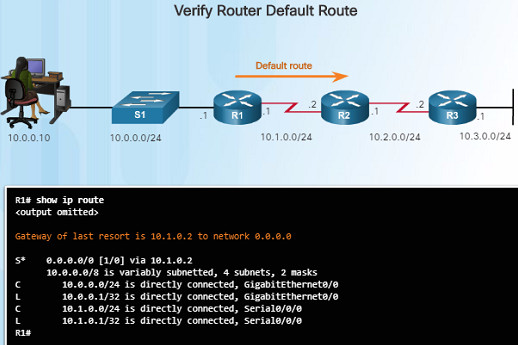
Use the command show ip interface brief to verify what IPv4 addresses are assigned to network interfaces.
11.4.3.2 – IP Addressing Issues on End Devices
On a Windows-based machine, when the device can’t contact a DHCP server, Windows will automatically assign the device to the 169.254.0.0/16 range to allow it to communicate within the local network.
Normally, this is an indication of a problem, and a device assigned with this address/range will not be able to communicate with other devices in the network.
Most end devices are configured with DHCP for automatic IPv4 address assignment.
Use the ipconfig command to verify the IP address assigned to a Windows-based computer.
11.4.3.3 – Default Gateway Issues
The default gateway for an end device is the closest networking device that can forward traffic to other networks – usually a router.
Without a valid default-gateway address, a host will not be able to communicate with devices outside of it’s local network.
- The default gateway for a host should belong to the same network as the end device.
- The default gateway can be set manually or obtained from a DHCP server.
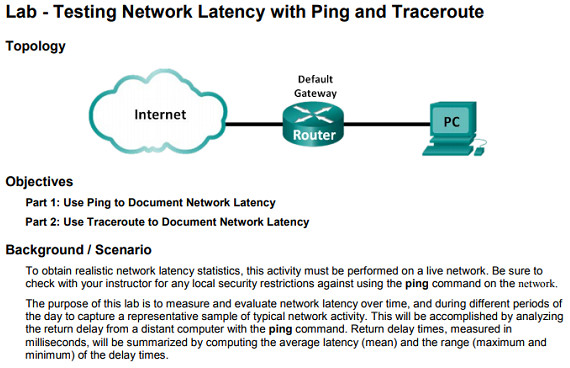
Use the ipconfig command to verify the default gateway on a Windows-based computer.
Use the show ip route command to verify that the default route has been set.
11.4.3.4 – Troubleshooting DNS Issues
Domain Name Service (DNS) is used to match names, such as, www.cisco.com, with numerical IP addresses.
This allows a user to enter www.cisco.com on their web browser instead of entering Cisco’s IP address for their web server.
If DNS is down, it may appear to some users that the “network is down”, when in reality, it might just be that the DNS server is unreachable.
DNS server addresses can be manually entered or automatically assigned using DHCP.
11.4.3.5 – Lab – Troubleshooting Connectivity issues
11.4.3.5 Lab – Troubleshooting Connectivity Issues
This lab will allow you to troubleshoot and resolve network issues using the skills and tools that you’ve learned in this chapter.
You will connect to devices, and use tools to identify network issues, establish a theory of probably cause, test that theory, and resolve the issue.
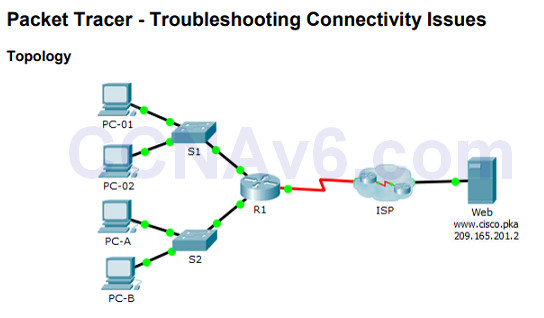
11.4.3.6 – Packet Tracer – Troubleshooting Connectivity Issues
11.4.3.6 Packet Tracer – Troubleshooting Connectivity Issues
This Packet Tracer activity will allow you to troubleshoot and resolve network connectivity issues if possible, or escalated if necessary.
You will also be required to clearly document the issues and any solution(s).
11.5 – Summary
11.5.1 – Conclusion
11.5.1.1 Class Activity – Design and Build a Small Business Network (Capstone Project)
11.5.1.1 Class Activity – Design and Build a Small Business Network (Capstone Project)
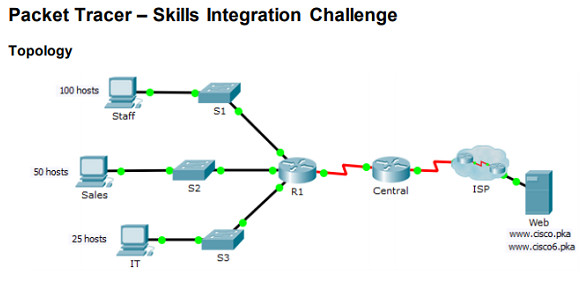
11.5.1.2 – Packet Tracer – Skill Integration Challenge
11.5.1.2 Packet Tracer – Skills Integration Challenge
This Packet Tracer activity will require you to create a new IPv4 addressing scheme that will accommodate 4 subnets using the 192.168.0.0/24 network.
You will also be tasked with finishing the basic security settings and interface configurations of the R1 router.
In addition, you will configure the SVI interface and basic security settings on the S1, S2, and S3 switches.
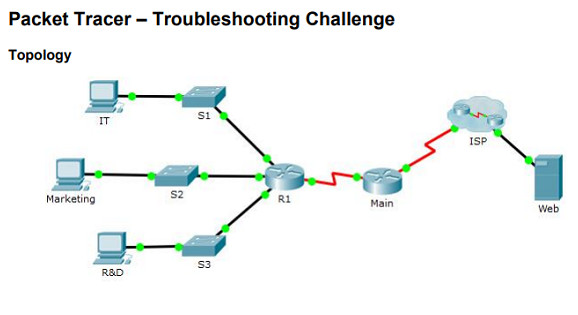
11.5.1.3 – Packet Tracer – Troubleshooting Challenge
11.5.1.3 Packet Tracer – Troubleshooting Challenge
This Packet Tracer activity will require you to correct misconfigurations and verify connectivity between the PCs and the websites, router, and switches.
The PC should be able to access the R1 router using SSH.