Instructor Planning Guide
Activities
What activities are associated with this chapter?
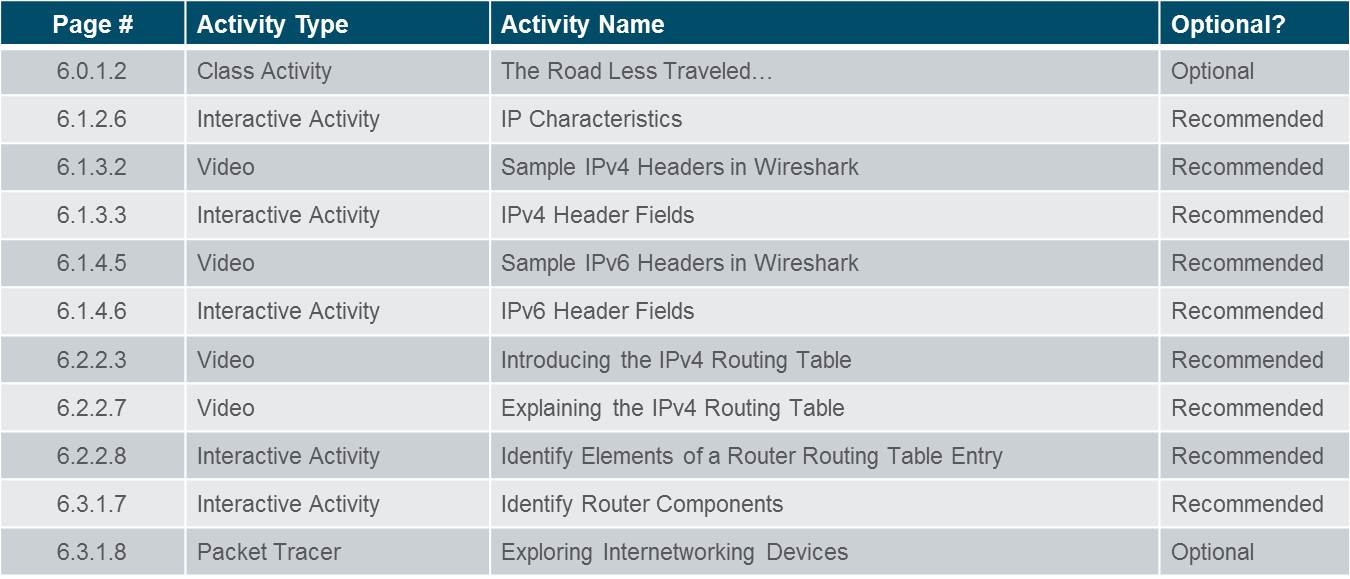
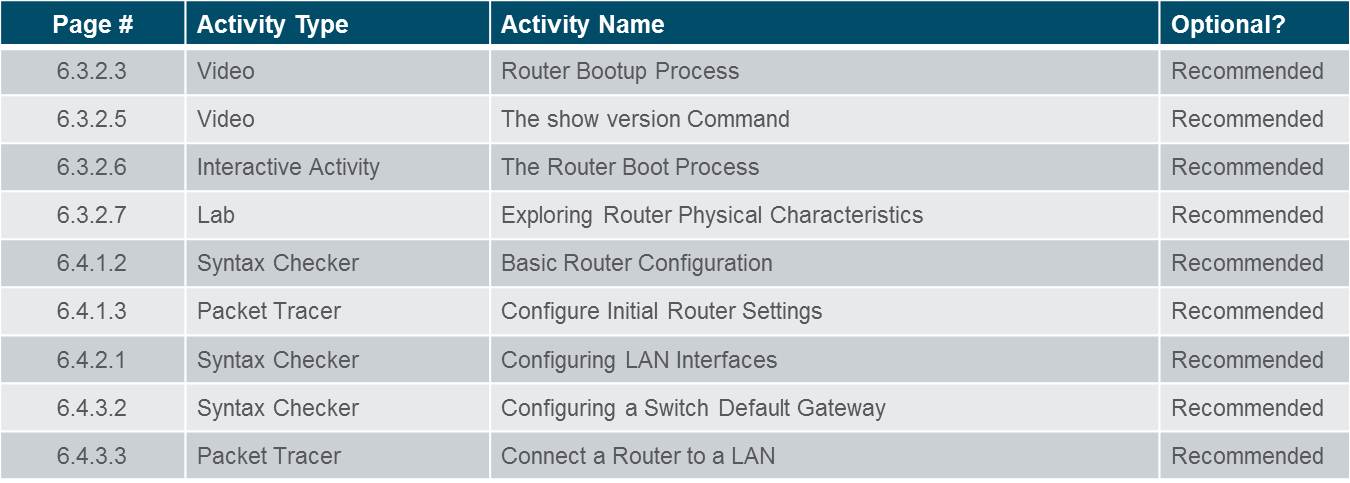
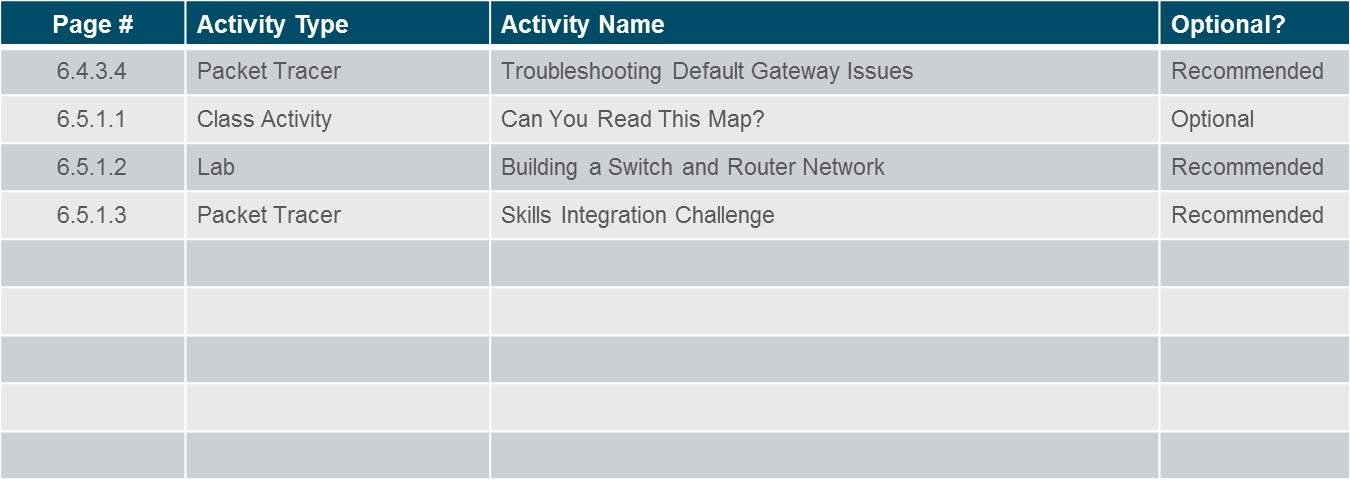
Assessment
Students should complete Chapter 6, “Assessment” after completing Chapter 6.
Quizzes, labs, Packet Tracers and other activities can be used to informally assess student progress.
Sections & Objectives
6.1 Network Layer Protocols
Explain how network layer protocols and services support communications across data networks
Describe the purpose of the network layer in data communication.
Explain why the IPv4 protocol requires other layers to provide reliability.
Explain the role of the major header fields in the IPv4 packet.
Explain the role of the major header fields in the IPv6 packet.
6.2 Routing
Explain how routers enable end-to-end connectivity in a small to medium-sized business network.
Explain how network devices use routing tables to direct packets to a destination network.
Compare a host routing table to a routing table in a router.
6.3 Routers
Explain how devices route traffic in a small to medium-sized business network
Describe the common components and interface of a router.
Describe the boot-up process of a Cisco IOS router.
6.4 Configuring a Cisco Router
Configure a router with basic configurations.
Configure initial settings on a Cisco IOS router.
Configure two active interfaces on a Cisco IOS router.
Configure devices to use the default gateway
Chapter 6: Network Layer
6.1 – Network Layer Protocols
6.1.1 – Network Layer in Communications
6.1.1.1 – The Network Layer
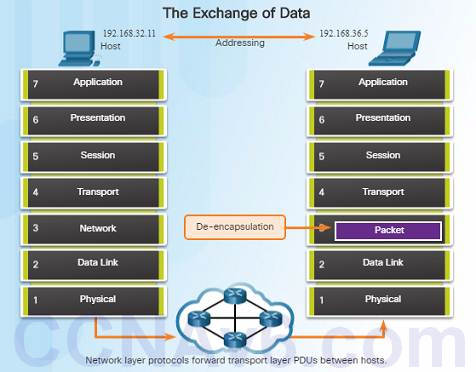
The network layer, which resides at OSI Layer 3, provides services that allow end devices to exchange data across a network.
The network layer uses four processes in order to provide end-to-end transport:
Addressing of end devices – IP addresses must be unique for identification purposes.
Encapsulation – The protocol data units from the transport layer are encapsulated by adding IP header information including source and destination IP addresses.
Routing – The network layer provides services to direct packets to other networks. Routers select the best path for a packet to take to its destination network.
De-encapsulation – The destination host de-encapsulates the packet to see if it matches its own.
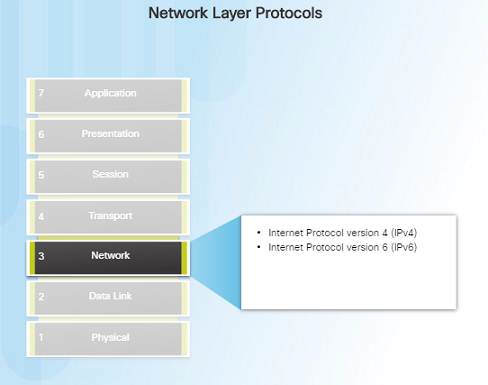
6.1.1.2 – Network Layer Protocols
There are several network layer protocols in existence; however, the most commonly implemented are:
♦ Internet Protocol version 4 (IPv4)
♦ Internet Protocol version 6 (IPv6)
Note: Legacy network layer protocols are not discussed in this course.
6.1.2 – Characteristics of the IP Protocol
6.1.2.1 – Encapsulating IP
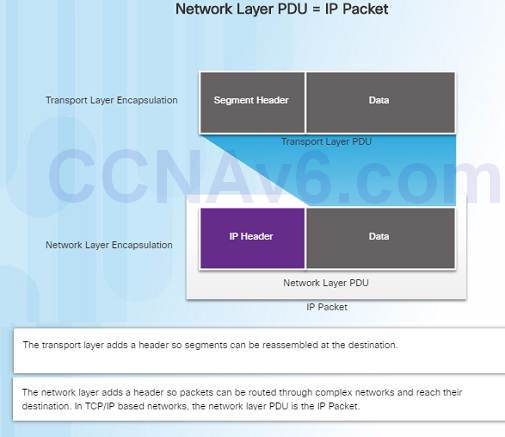
At the network layer, IP encapsulates the transport layer segment by adding an IP header for the purpose of delivery to the destination host.
The IP header stays the same from the source to the destination host.
The process of encapsulating data layer by layer enables the services at different layers to scale without affecting other layers.
Routers implement different network layer protocols concurrently over a network and use the network layer packet header for routing.
6.1.2.2 – Characteristics of IP
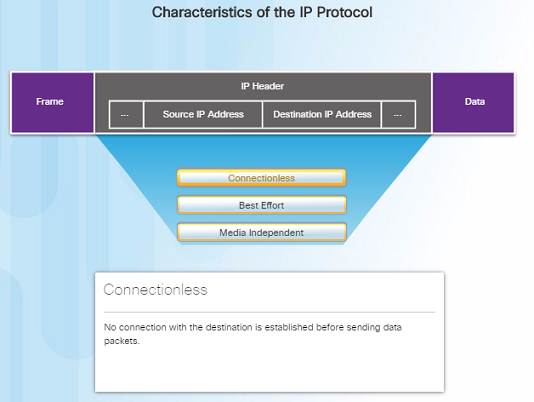
IP was designed as a protocol with low overhead – it provides only the functions required to deliver a packet from the source to a destination.
An IP packet is sent to the destination without prior establishment of a connection
IP was not designed to track and manage the flow of packets.
These functions, if required, are performed by other layers – primarily TCP
6.1.2.3 – IP – Connectionless
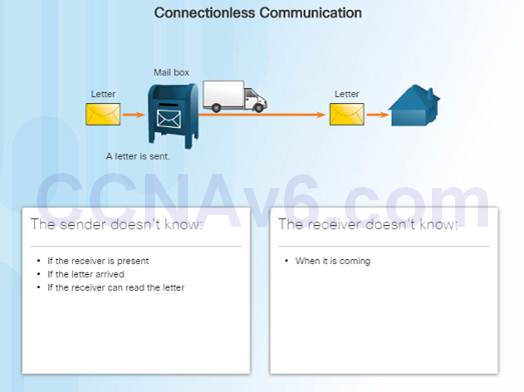
IP is a connectionless protocol:
No dedicated end-to-end connection is created before data is sent.
Very similar process as sending someone a letter through snail mail.
Senders do not know whether or not the destination is present, reachable, or functional before sending packets.
This feature contributes to the low overhead of IP.
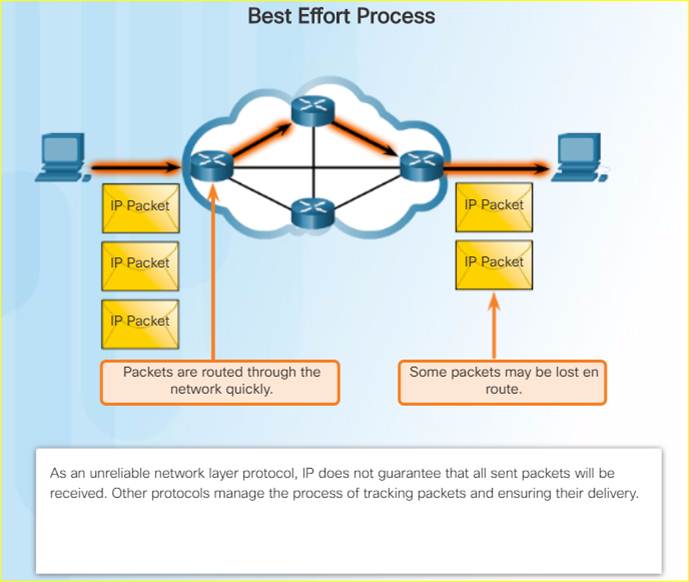
6.1.2.4 – IP – Best Effort Delivery
IP is a Best Effort Delivery protocol:
♦ IP is considered “unreliable” because it does not guarantee that all packets that are sent will be received.
♦ Unreliable means that IP does not have the capability to manage and recover from undelivered, corrupt, or out of sequence packets.
♦ If packets are missing or not in the correct order at the destination, upper layer protocols/services must resolve these issues.
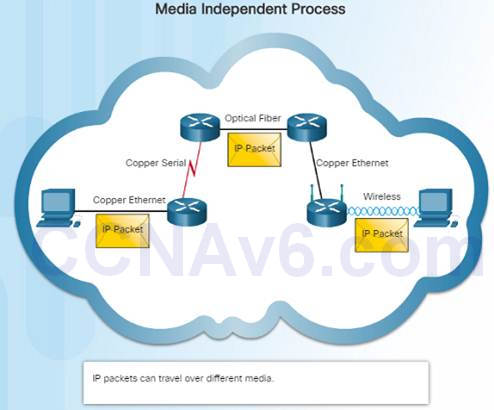
6.1.2.5 – IP – Media Independent
IP operates independently from the media that carries the data at lower layers of the protocol stack – it does not care if the media is copper cables, fiber optics or wireless.
The OSI data link layer is responsible for taking the IP packet and preparing it for transmission over the communications medium.
The network layer does have a maximum size of the PDU that can be transported – referred to as MTU (maximum transmission unit).
The data link layer tells the network layer the MTU.
6.1.3 – IPv4 Packet
6.1.3.1 – IPv4 Packet Header
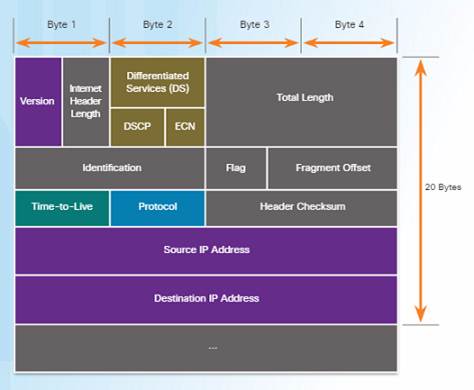
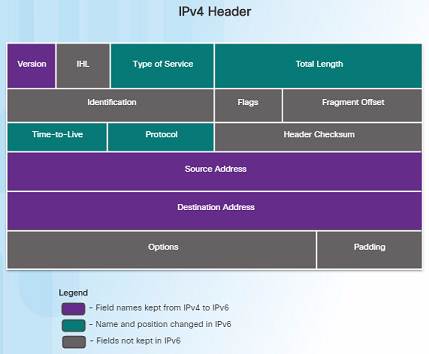
An IPv4 packet header consists of the fields containing binary numbers. These numbers identify various settings of the IP packet which are examined by the Layer 3 process.
Significant fields include:
♦ Version – Specifies that the packet is IP version 4
♦ Differentiated Services or DiffServ (DS) – Used to determine the priority of each packet on the network.
♦ Time-to-Live (TTL) – Limits the lifetime of a packet – decreased by one at each router along the way.
♦ Protocol – Used to identify the next level protocol.
♦ Source IPv4 Address – Source address of the packet.
♦ Destination IPv4 Address – Address of destination.
6.1.3.2 – Video Demonstration – Sample IPv4 Headers in Wireshark
Wireshark is a free and open source packet and network protocol analyzer that allows you to capture and browse network traffic.
6.1.4 – IPv6 Packet
6.1.4.1 – Limitations of IPv4
IPv4 has been updated to address new challenges.
Three major issues still exist with IPv4:
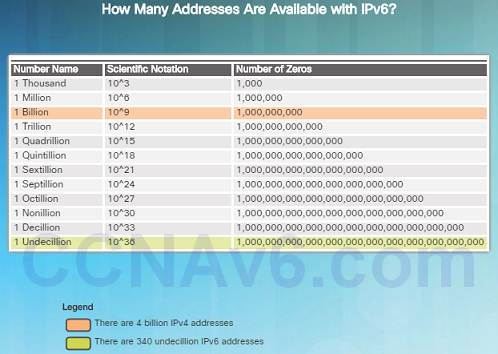
♦ IP address depletion – IPv4 has a limited number of unique public IPv4 addresses available. Although there are about 4 billion IPv4 addresses, the exponential growth of new IP- enabled devices has increased the need.
♦ Internet routing table expansion – A routing table contains the routes to different networks in order to make the best path determination. As more devices and servers are connected to the network, more routes are created. A large number of routes can slow down a router.
♦ Lack of end-to-end connectivity – Network Address Translation (NAT) was created for devices to share a single IPv4 address. However, because they are shared, this can cause problems for technologies that require end-to-end connectivity.

6.1.4.2 – Introducing IPv6
In the early ‘90s, the IETF started looking at a replacement for IPv4 – which led to IPv6.
Advantages of IPv6 over IPv4 include:
♦ Increased address space – based on 128-bit addressing vs. 32-bit with IPv4
♦ Improved packet handling – fewer fields with IPv6 than IPv4
♦ Eliminates the need for NAT – no need to share addresses with IPv6
♦ There are roughly enough IPv6 addresses for every grain of sand on Earth.
6.1.4.3 – Encapsulating IPv6
The IPv6 header is simpler than the IPv4 header.
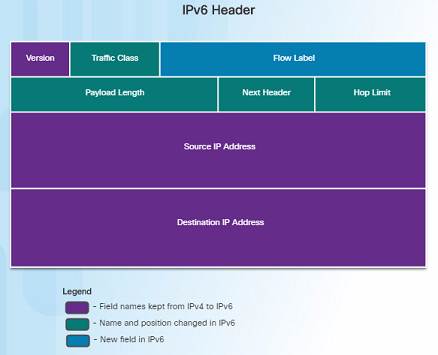
Advantages of IPv6 over IPv4 using the simplified header:
♦ Simplified header format for efficient packet handling
♦ Hierarchical network architecture for routing efficiency
♦ Autoconfiguration for addresses
♦ Elimination of need for network address translation (NAT) between private and public addresses
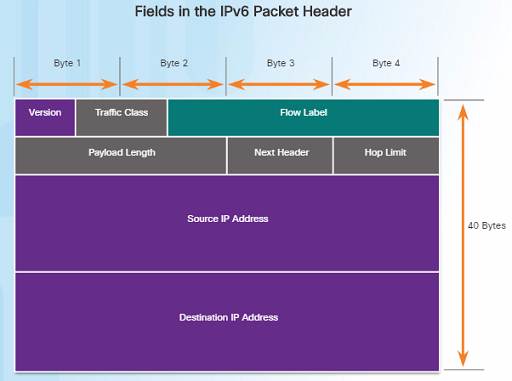
6.1.4.4 – IPv6 Packet Header
IPv6 packet header fields:
♦ Version – Contains a 4-bit binary value set to 0110 that identifies it as a IPv6 packet.
♦ Traffic Class – 8-bit field equivalent to the IPv4 Differentiated Services (DS) field.
♦ Flow Label – 20-bit field suggests that all packets with the same flow label receive the same type of handling by routers.
♦ Payload Length – 16-bit field indicates the length of the data portion or payload of the packet.
♦ Next Header – 8-bit field is equivalent to the IPv4 Protocol field. It indicates the data payload type that the packet is carrying.
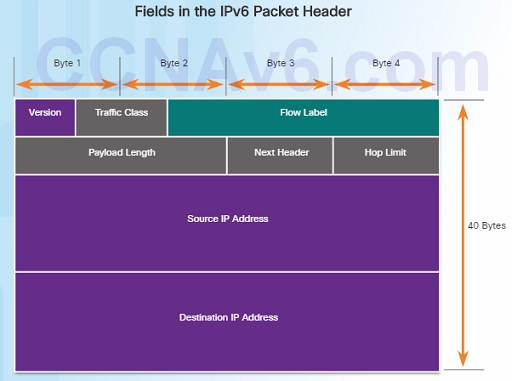
IPv6 packet header fields:
♦ Hop Limit – 8-bit field replaces the IPv4 TTL field. This value is decremented by 1 as it passes through each router. When it reaches zero, the packet is discarded.
♦ Source IPv6 Address – 128-bit field that identifies the IPv6 address of the sending host.
♦ Destination IPv6 Address – 128-bit field that identifies the IPv6 address of the receiving host.
6.1.4.5 – Video Demonstration – Sample IPv6 Headers and Wireshark
This video demonstration walks through an IPv6 packet capture screenshot using Wireshark. The source, destination, type of packet, and purpose of the packet are discussed.
Protocol field information for this IPv6 packet are also deciphered and discussed.

6.2 – Routing
6.2.1 – How a Host Routes
6.2.1.1 – Host Forwarding Decision
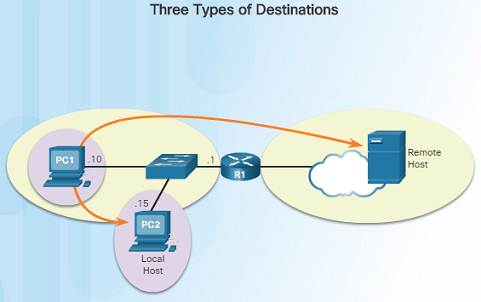
An important role of the network layer is to direct packets between hosts. A host can send a packet to:
♦ Itself – A host can ping itself for testing purposes using 127.0.0.1 which is referred to as the loopback interface.
♦ Local host – This is a host on the same local network as the sending host. The hosts share the same network address.
♦ Remote host – This is a host on a remote network. The hosts do not share the same network address.
The source IPv4 address and subnet mask is compared with the destination address and subnet mask in order to determine if the host is on the local network or remote network.
6.2.1.2 – Default Gateway
The default gateway is the network device that can route traffic out to other networks. It is the router that routes traffic out of a local network.
This occurs when the destination host is not on the same local network as the sending host.
The default gateway will know where to send the packet using its routing table.
The sending host does not need to know where to send the packet other than to the default gateway – or router.
6.2.1.3 – Using the Default Gateway
A host’s routing table usually includes a default gateway address – which is the router IP address for the network that the host is on.
The host receives the IPv4 address for the default gateway from DHCP, or it is manually configured.
Having a default gateway configured creates a default route in the routing table of a host – which is the route the computer will send a packet to when it needs to contact a remote network.
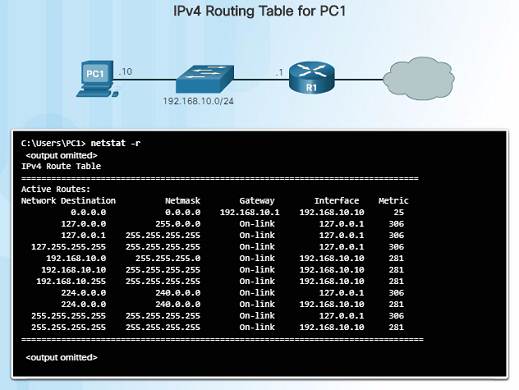
6.2.1.4 – Host Routing Tables
On a Windows host, you can display the routing table using:
♦ route print
♦ netstat -r
Three sections will be displayed:
♦ Interface List – Lists the Media Access Control (MAC) address and assigned interface number of network interfaces on the host.
♦ IPv4 Route Table – Lists all known IPv4 routes.
♦ IPv6 Route Table – Lists all known IPv6 routes.
6.2.2 – Router Routing Tables
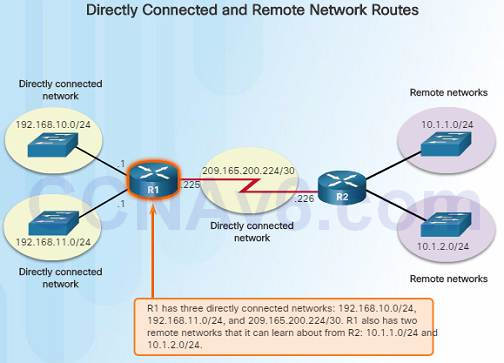
6.2.2.1 – Router Packet Forwarding Decision
When a router receives a packet destined for a remote network, the router has to look at its routing table to determine where to forward the packet. A router’s routing table contains:
♦ Directly-connected routes – These routes come from the active router interfaces configured with IP addresses.
♦ Remote routes – These routes come from remote networks connected to other routers. They are either configured manually or learned through a dynamic routing protocol.
♦ Default route – This is where the packet is sent when a route does not exist in the routing table.
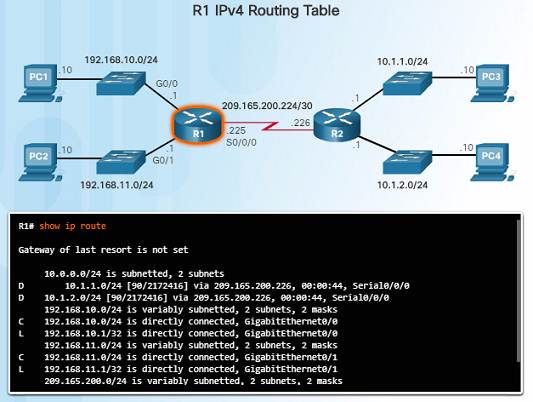
6.2.2.2 – IPv4 Router Routing Table
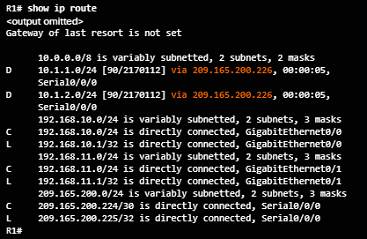
On a Cisco IOS router, the show ip route command is used to display the router’s IPv4 routing table. The routing table shows:
♦ Directly connected and remote routes
♦ How each route was learned
♦ Trustworthiness and rating of the route
♦ When the route was last updated
♦ Which interface is used to reach the destination
A router examines an incoming packet’s header to determine the destination network. If there’s a match, the packet is forwarded using the specified information in the routing table.
6.2.2.3 – Video Demonstration – Introducing the IPv4 Routing Table
A host has a routing table that can be viewed with the netstat –r command.
The routing table includes routes to different networks and information about those routes. For example:
♦ The D to the left of the 10.1.1.0/24 route indicates that it was learned via the EIGRP routing protocol.
♦ The letter C means that the network is directly connected.
♦ The default gateway of last resort is also indicated.

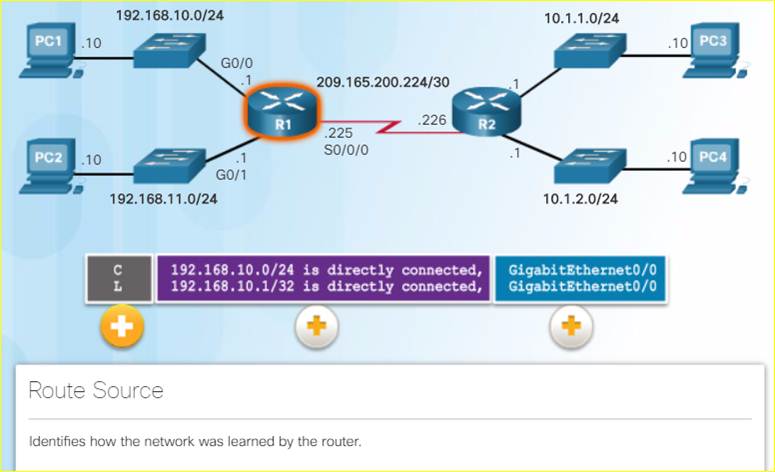
6.2.2.4 – Directly Connected Routing Table Entries
When a router interface is configured and activated, the following two routing table entries are created automatically:
♦ C – Identifies that the network is directly connected and the interface is configured with an IP address and activated.
♦ L – Identifies that it is a local interface. This is the IPv4 address of the interface on the router.
6.2.2.5 – Remote Network Routing Table Entries
10.1.1.0/24 identifies the destination network.
90 is the administrative distance for the corresponding network – or the trustworthiness of the route. The lower the number, the more trustworthy it is.
2170112 – represents the metric or value assigned to reach the remote network. Lower values indicate preferred routes.
209.165.200.226 – Next-hop or IP address of the next router to forward the packet.
00:00:05 – Route Timestamp identifies when the router was last heard from.
Serial/0/0/0 – Outgoing Interface
The D represents the Route Source which is how the network was learned by the router. D identifies the route as an EIGRP route or (Enhanced Interior Gateway Routing Protocol)
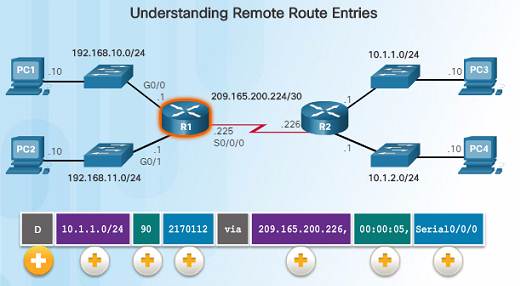
6.2.2.6 – Next-Hop Address
When a packet arrives at a router destined for a remote network, it will send the packet to the next hop address corresponding to the destination network address in its routing table.
For example, if the R1 router in the figure to the left receives a packet destined for a device on the 10.1.1.0/24 network, it will send it to the next hop address of 209.165.200.226.
Notice in the routing table, a default gateway address is not set – if the router receives a packet for a network that isn’t in the routing table, it will be dropped.

6.2.2.7 – Video Demonstration – Explaining the IPv4 Routing Table
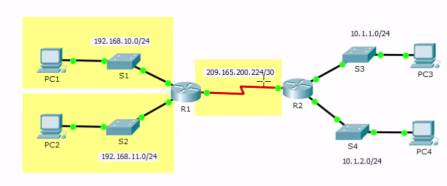
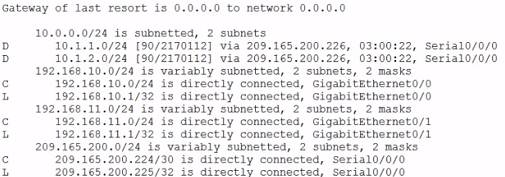
Router R1:
Has three directly connected routes highlighted in yellow.
The first two routing entries of the routing table for networks 10.1.1.0/24 and 10.1.2.0/24 are for the remote networks connected to the R2 router.
R1 learned about these networks from R2 via the EIGRP dynamic routing protocol.
Next hop router is indicated via 209.165.200.226. This is where the router needs to forward the packet.
The router will send the packet to the next hop address by exiting its own Serial/0/0/0 interface.
A connected network entry does not have a next hop address. It will indicate which interface to exit out of, for example, GigabitEthernet0/0.
6.3 – Routers
6.3.1 – Anatomy of a Router
6.3.1.1 – A Router is a Computer
A router is a computer. Like computers, a router requires a CPU, an operating system, and memory.
Cisco routers are designed to meet the needs of wide variety of businesses and networks:
♦ Branch – Teleworkers, small businesses, and medium-size branch sites.
♦ WAN – Large businesses, organizations and enterprises.
♦ Service Provider – Large service providers.
The focus of the CCNA certification is on the branch family of routers.

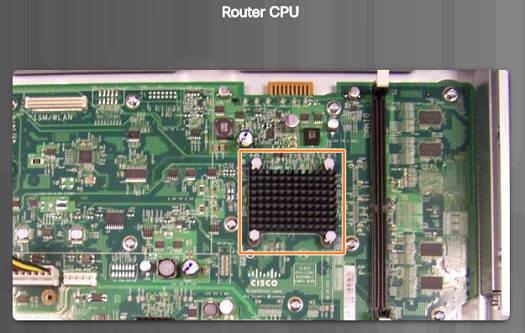
6.3.1.2 – Router CPU and OS
Like computers, Cisco routers require a CPU to execute OS instructions including system initialization, routing functions and switching functions.
The component highlighted in the figure to the left is the CPU of a Cisco 1941 with the heatsink attached. A heatsink is used to dissipate the heat from the CPU for cooling purposes.
The CPU requires an operating system to provide routing and switching functions. Most Cisco devices use the Cisco Internetwork Operating System (IOS).
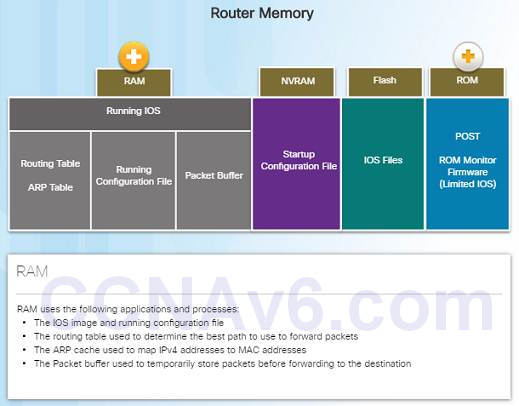
6.3.1.3 – Router Memory
Volatile memory – requires continual power to store information.
Non-volatile memory – does not require continual power.
A router uses four types of memory:
♦ RAM – Volatile memory used to store applications, processes, and data needed to be executed by the CPU.
♦ ROM – Non-volatile memory used to store crucial operational instructions and a limited IOS. ROM is firmware embedded on an integrated circuit inside of the router.
♦ NVRAM – Non-volatile memory used as permanent storage for the startup configuration file (startup-config).
♦ Flash – Non-volatile memory used as permanent storage for the IOS and other operating system files such as log or backup files.
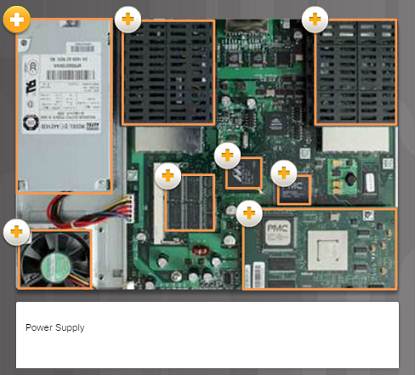
6.3.1.4 – Inside a Router
There are numerous types and models of routers, however, they all have the same general hardware components:
Power supply
Cooling fan
SDRAM – Synchronous Dynamic RAM
Non-volatile RAM (NVRAM)
CPU
Heat shields
Advanced Integration Module (AIM)
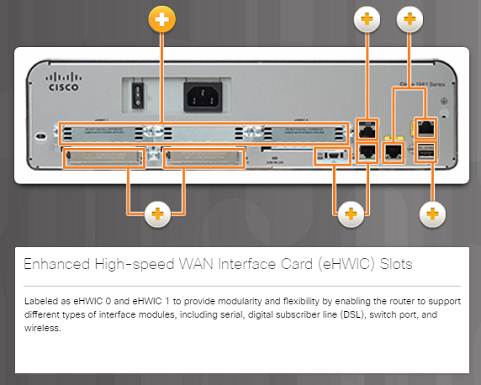
6.3.1.5 – Connect to a Router
Cisco devices, routers, and switches typically interconnect many devices. The Cisco 1941 router backplane includes the following ports and connections:
♦ Enhanced High-speed WAN Interface Card (eHWIC) Slots
♦ Auxiliary (AUX) – RJ-45 port for remote management.
♦ Console Port – Used for initial configuration and Command Line Interface access – RJ-45 or USB Type-B (mini-B USB)
♦ Gigabit Ethernet used to provide LAN access by connecting to switches, users, or to other routers.
♦ Compact Flash Slots – Labeled as CF0 and CF1 and used to provide increased storage flash space upgradable to 4GB.
♦ USB port – used to provide additional storage space.
6.3.1.6 – LAN and WAN Interfaces
Cisco router connections can be classified in two categories:
♦ In-band router interfaces – LAN and WAN interfaces
♦ Management ports – Console and AUX ports

The most common ways to access user EXEC mode in the CLI environment on a Cisco router:
♦ Console – This is a physical management port that provides out-of-band access to the Cisco router. Out-of-band means that it is dedicated and does not require network services to be configured on the router.
♦ Secure Shell (SSH) – This is a secure method of remotely establishing a CLI connection over a network. SSH does require active networking services configured.
♦ Telnet – Telnet is an insecure method of remotely establishing a CLI session through a virtual interface over a network. The connection is not encrypted.
6.3.1.8 – Packet Tracer – Exploring Internetworking Devices
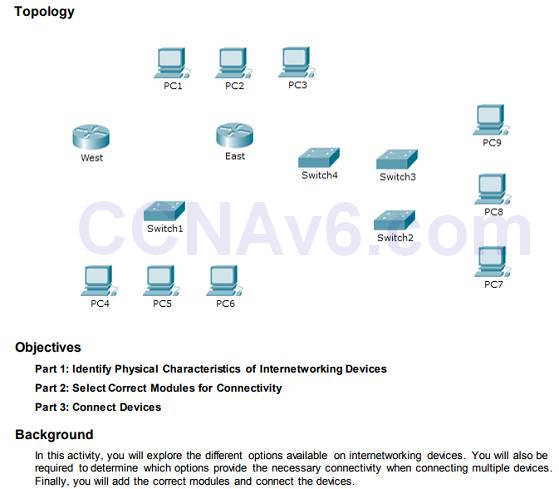
6.3.1.8 Packet Tracer – Exploring Internetworking Devices
In this Packet Tracer activity, you will explore different options available on internetworking devices.
You will be required to determine which options provide the necessary connectivity when connecting multiple devices.
6.3.2 – Router Boot-up
6.3.2.1 – Bootset Files
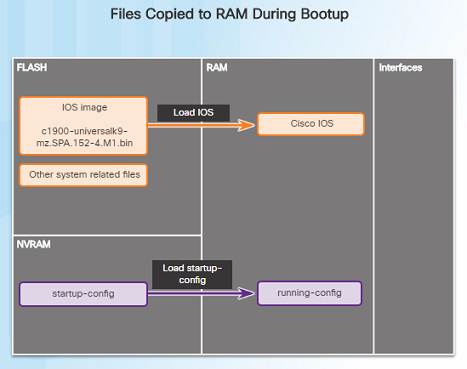
Cisco routers and switches load the IOS image and startup configuration file into RAM when they are booted.
The running configuration is modified when the network administrator makes any changes. These changes should be saved to the startup configuration file in NVRAM in order for them to take effect on the next reboot of the router or during in the event of a power loss.
6.3.2.2 – Router Bootup Process
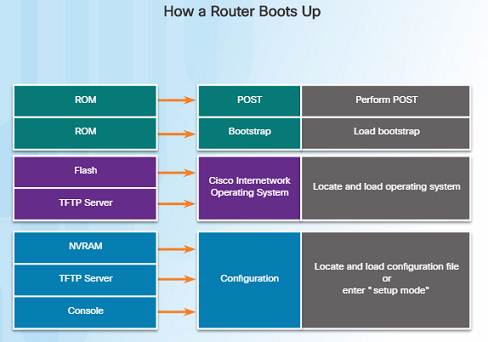
Three major phases to the bootup process of a router:
Perform the POST and load the bootstrap program – During the Power-on Self-Test, the router executes diagnostics from ROM on various hardware components. After the POST, the bootstrap program is copied from ROM into RAM and its job is to locate the Cisco IOS and load it into RAM.
Locate and load the Cisco IOS software – Typically, the IOS is stored in flash memory and is copied into RAM for execution by the CPU.
Locate and load the startup configuration file or enter setup mode – The bootstrap program then copies the startup config file from NVRAM into RAM and becomes the running configuration.
6.3.2.3 – Video Demonstration – Router Bootup Process
The POST checks for errors in the hardware. After the system POST, the router loads the bootstrap program from ROM.
The purpose of the bootstrap program is to locate and load the Cisco IOS software.
After the IOS is loaded, the router then loads the configuration file known as the startup config file which contains all of the configured settings for the router.
If the router can’t find a startup-config file, nor obtain one from a TFTP server, the router will enter initial set-up mode.

6.3.2.4 – Show Version Output
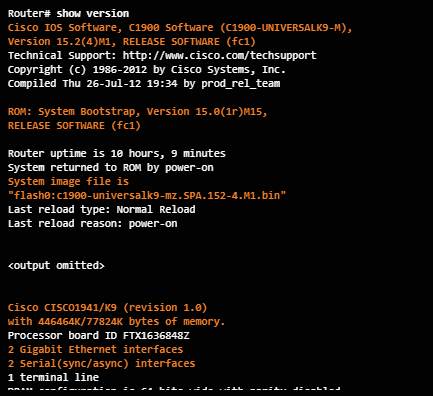
The show version command displays information about the version of the Cisco IOS software running on the router as well as:
♦ The version of the bootstrap program
♦ Information about the hardware configuration
♦ Amount of system memory
6.3.2.5 – Video Demonstration – The show version Command
This demonstration uses a Term Term terminal emulation program to connect to the console of a Cisco 1941 router for the purpose of showing the output of the show version command.
What is the Cisco IOS software version that is running?
How long has the router been up?
What is the name of the system image file and where is it located?
What is the name of the distribution?
What interfaces are on the router?

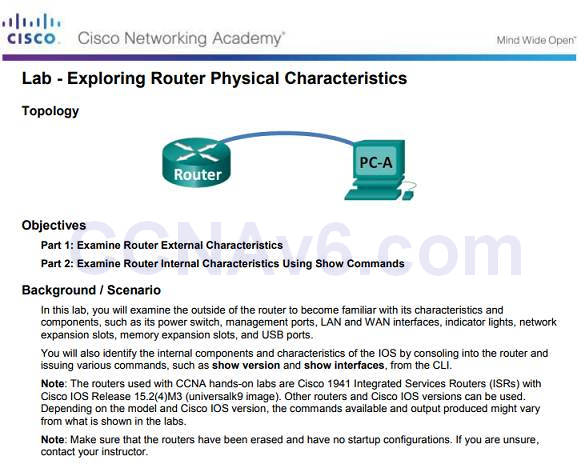
6.3.2.7 – Lab – Exploring Router Physical Characteristics
6.3.2.7 Lab – Exploring Router Physical Characteristics
In this lab, you will examine the outside of a router in order to become familiar with its characteristics and components.
6.4 – Configure a Cisco Router
6.4.1 – Configure Initial Settings
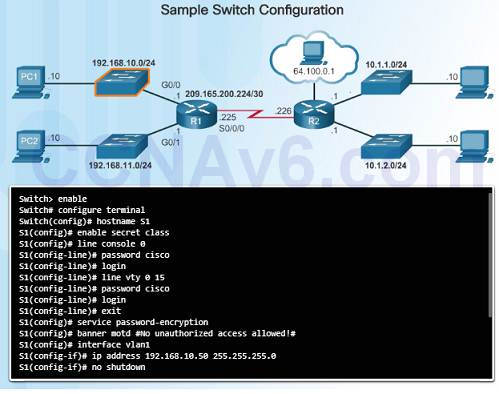
6.4.1.1 – Basic Switch Configuration Steps
Cisco routers and switches have many similarities in regards to their configuration:
♦ Support a similar operating system.
♦ Support similar command structure.
♦ Support many of the same commands.
♦ They also have identical initial configuration steps when implemented in a network.
The commands on the left display a sample configuration of a switch.
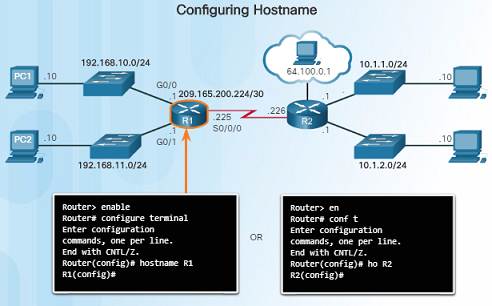
6.4.1.2 – Basic Router Configuration Steps
Similar to the configuration of a switch on the previous slide, the initial configuration should include:
♦ Configure the router’s device name
♦ Secure the user EXEC mode
♦ Secure remote Telnet and SSH access
♦ Secure privileged EXEC mode
♦ Secure all passwords in the config file
♦ Provide legal notification – Authorized access only
♦ Save the configuration
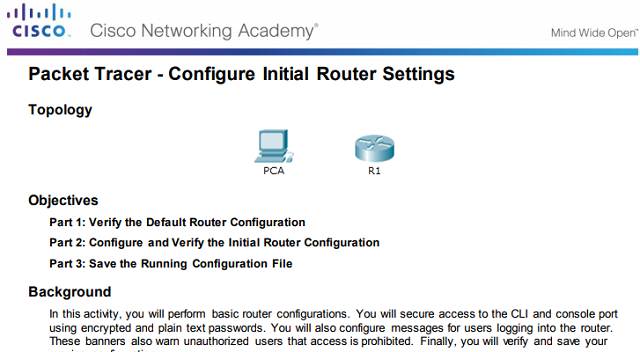
6.4.1.3 – Packet Tracer – Configure Initial Router Settings
6.4.1.3 Packet Tracer – Configure Initial Router Settings
This Packet Tracer activity will allow you to perform basic initial router configurations.
6.4.2 – Configure Interfaces
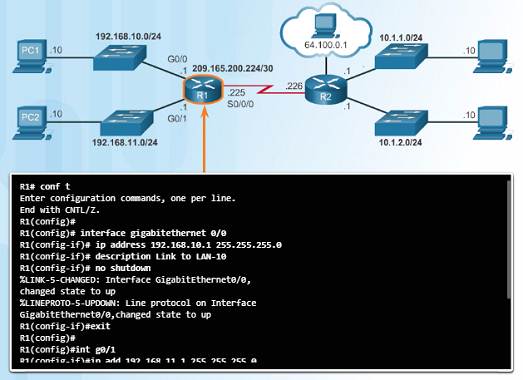
6.4.2.1 – Configure Router Interfaces
For routers to be reachable by other devices in the network, the in-band interfaces must be configured. For example, a Cisco 1941 router has four in-band interfaces:
♦ Two Gigabit Ethernet Interfaces – G0/0 and G0/1
♦ One serial WAN Interface card with two interfaces – S 0/0/0 and S0/0/1
The commands in the figure to the left provide an example of how to configure a router’s interface to provide network connectivity.
It is important that you use the command no shutdown when you are ready to make the interface active.
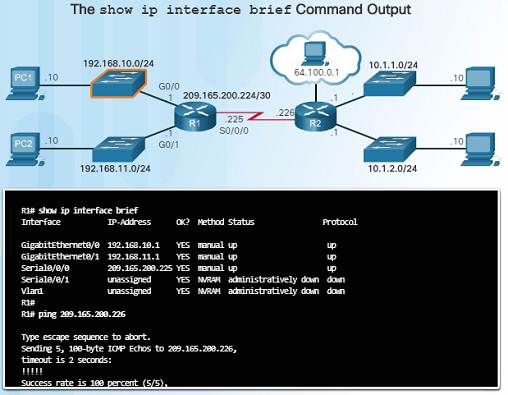
6.4.2.2 – Verify Interface Configuration
After configuring an interface, or for troubleshooting purposes, there are several commands that can be used:
show ip interface brief – Provides you a summarized view of all interfaces to verify if they are activated and operational. Look for Status of “up” and Protocol of “up”.
show ip route – Displays the contents of the IPv4 routing table stored in RAM.
show interfaces – Displays the IPv4 statistics for all interfaces on a router.
Remember to save your configuration changes with the copy running-config startup-config command.
6.4.3 – Configure the Default Gateway
6.4.3.1 – Default Gateway for a Host
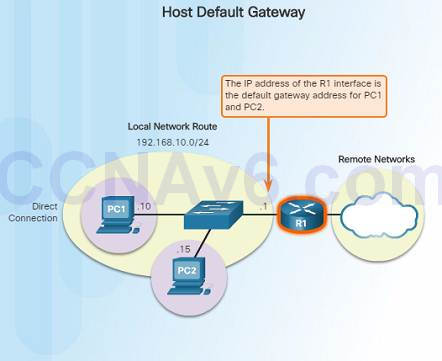
For an end device or a host to communicate over the network, it must be configured with the correct IP address information including the default gateway address.
The default gateway is only used when the host wants to send a packet to a device on another network – if the device is on the same network, it can send it directly to that device.
If PC1 needs to send a packet to PC3 which is on a different network, it must send it to the default gateway address of 192.168.10.1 on router R1’s G0/0 interface.

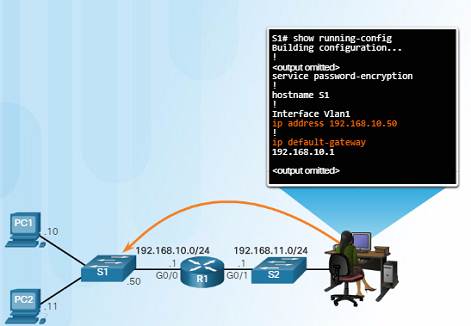
6.4.3.2 – Default Gateway for a Switch
Normally, a Layer 2 device, such as a switch, does not require an IP address to function.
An IP address, subnet mask, and default gateway address are required in order to connect to it remotely (via SSH or Telnet) for configuration or administrative purposes.
Use the command ip default-gateway global configuration command to configure the default gateway on a switch.
It is important to note that a switch does not use the default gateway address to forward packets to from hosts on its local network to remote networks.
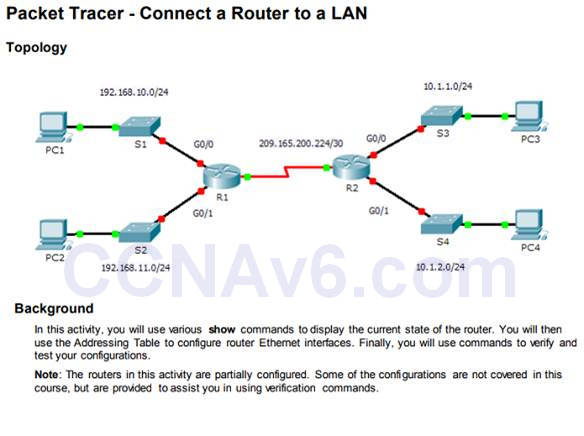
6.4.3.3 – Packet Tracer – Connect a Router to a LAN
6.4.3.3 Packet Tracer – Connect a Router to a LAN
In this Packet Tracer activity, you will use various show commands to view the state of various parts of the router.
You will also configure the router’s Ethernet interfaces using IP addresses that will be provided.
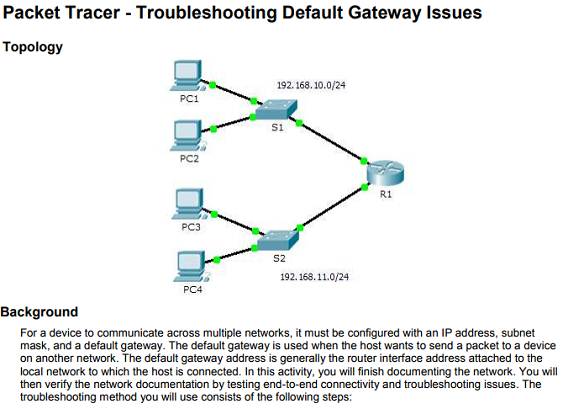
6.4.3.4 – Packet Tracer – Troubleshooting Default Gateway Issues
6.4.3.4 Packet Tracer – Troubleshooting Default Gateway Issues
In this Packet Tracer activity, you will continue to document the network and then verify the documentation by testing end-to-end connectivity.
You will also have a chance to troubleshoot any connectivity issues using the following steps:
♦ Verify the network documentation and use tests to isolate problems.
♦ Determine an appropriate solution for a given problem.
♦ Implement the solution.
♦ Test to verify the problem is resolved.
♦ Document the solution.
6.4 – Configure a Cisco Router
6.5.1 – Conclusion
6.5.1.1 Class Activity – Can You Read This Map?
6.5.1.1 Class Activity – Can You Read This Map?
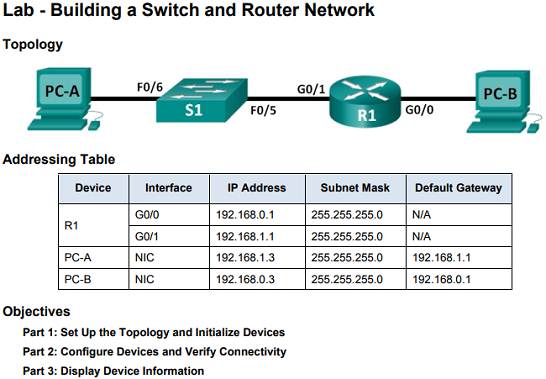
6.5.1.2 – Lab – Building a Switch and Router Network
6.5.1.2 Lab – Building a Switch and Router Network
In this comprehensive lab, you will:
♦ Review IOS commands covered in this chapter.
♦ Cable the equipment as shown in the diagram.
♦ Configure the devices to match the addressing table.
♦ Verify configurations by testing for network connectivity.
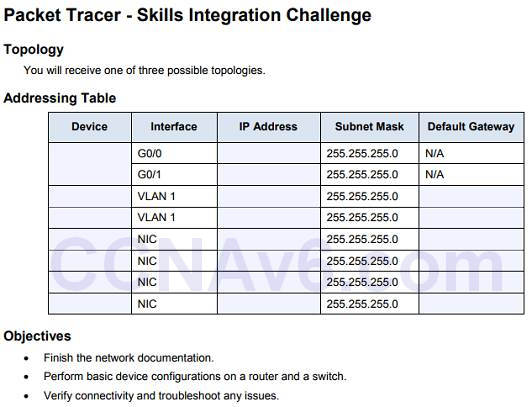
6.5.1.3– Packet Tracer – Skills Integration Challenge
6.5.1.3 Packet Tracer – Skills Integration Challenge
In this Packet Tracer activity, you will have a chance to impress your manager with your ability to configure a router and a switch connecting two LANs.
You will verify your results by testing end-to-end connectivity and troubleshoot as necessary.
New Terms and Commands
Routing
Connectionless
Best effort
Media independent
Maximum transmission unit (MTU)
Fragmentation
Internet Control Message Protocol (ICMP)
Network Address Translation (NAT)
Loopback interface
Default gateway
