Time limit: 0
Quiz-summary
0 of 43 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
Information
CCNA Cyber Ops (Version 1.1) – Chapter 13 Test Online Full
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 43 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- Answered
- Review
-
Question 1 of 43
1. Question
1 pointsWhen dealing with security threats and using the Cyber Kill Chain model, which two approaches can an organization use to help block potential exploitations of a system? (Choose two.)Correct
Incorrect
-
Question 2 of 43
2. Question
1 pointsWhich action should be included in a plan element that is part of a computer security incident response capability (CSIRC)?Correct
Incorrect
-
Question 3 of 43
3. Question
1 pointsWhat is the objective the threat actor in establishing a two-way communication channel between the target system and a CnC infrastructure?Correct
Incorrect
-
Question 4 of 43
4. Question
1 pointsAfter containment, what is the first step of eradicating an attack?Correct
Incorrect
-
Question 5 of 43
5. Question
1 pointsWhat is defined in the SOP of a computer security incident response capability (CSIRC)?Correct
Incorrect
-
Question 6 of 43
6. Question
1 pointsA school has a web server mainly used for parents to view school events, access student performance indicators, and communicate with teachers. The network administrator suspects a security-related event has occurred and is reviewing what steps should be taken. The threat actor has already placed malware on the server causing its performance to slow. The network administrator has found and removed the malware as well as patched the security hole where the threat actor gained access. The network administrator can find no other security issue. What stage of the Cyber Kill Chain did the threat actor achieve?Correct
Incorrect
-
Question 7 of 43
7. Question
1 pointsA school has a web server mainly used for parents to view school events, access student performance indicators, and communicate with teachers. The network administrator suspects a security-related event has occurred and is reviewing what steps should be taken. If the web server runs Microsoft IIS, which Windows tool would the network administrator use to view the access logs?Correct
Incorrect
-
Question 8 of 43
8. Question
1 pointsA school has a web server mainly used for parents to view school events, access student performance indicators, and communicate with teachers. The network administrator suspects a security-related event has occurred and is reviewing what steps should be taken. Reports of network slowness lead the network administrator to review server alerts. The administrator confirms that an alert was an actual security incident. Which type of security alert classification would this be?Correct
Incorrect
-
Question 9 of 43
9. Question
1 pointsA school has a web server mainly used for parents to view school events, access student performance indicators, and communicate with teachers. The network administrator suspects a security-related event has occurred and is reviewing what steps should be taken. The network administrator believes that the threat actor used a commonly available tool to slow the server down. The administrator concludes that based on the source IP address identified in the alert, the threat actor was probably one of the students. What type of hacker would the student be classified as?Correct
Incorrect
-
Question 10 of 43
10. Question
1 pointsWhat is the goal of an attack in the installation phase of the Cyber Kill Chain?Correct
Incorrect
-
Question 11 of 43
11. Question
1 pointsWhich meta-feature element in the Diamond Model describes information gained by the adversary?Correct
Incorrect
-
Question 12 of 43
12. Question
1 pointsWhat is a benefit of using the VERIS community database?Correct
Incorrect
-
Question 13 of 43
13. Question
1 pointsWhen a security attack has occurred, which two approaches should security professionals take to mitigate a compromised system during the Actions on Objectives step as defined by the Cyber Kill Chain model? (Choose two.)Correct
Incorrect
-
Question 14 of 43
14. Question
1 pointsA threat actor has identified the potential vulnerability of the web server of an organization and is building an attack. What will the threat actor possibly do to build an attack weapon?Correct
Incorrect
-
Question 15 of 43
15. Question
1 pointsWhich action is taken in the postincident phase of the NIST incident response life cycle?Correct
Incorrect
-
Question 16 of 43
16. Question
1 pointsWhich top-level element of the VERIS schema would allow a company to log who the actors were, what actions affected the asset, which assets were affected, and how the asset was affected?Correct
Incorrect
-
Question 17 of 43
17. Question
1 pointsWhat is the role of vendor teams as they relate to CSIRT?Correct
Incorrect
-
Question 18 of 43
18. Question
1 pointsAccording to information outlined by the Cyber Kill Chain, which two approaches can help identify reconnaissance threats? (Choose two.)Correct
Incorrect
-
Question 19 of 43
19. Question
1 pointsTo ensure that the chain of custody is maintained, what three items should be logged about evidence that is collected and analyzed after a security incident has occurred? (Choose three.)Correct
Incorrect
-
Question 20 of 43
20. Question
1 pointsWhich schema or model was created to anonymously share quality information about security events to the security community?Correct
Incorrect
-
Question 21 of 43
21. Question
1 pointsWhat is the purpose of the policy element in a computer security incident response capability of an organization, as recommended by NIST?Correct
Incorrect
-
Question 22 of 43
22. Question
1 pointsWhat information is gathered by the CSIRT when determining the scope of a security incident?Correct
Incorrect
-
Question 23 of 43
23. Question
1 pointsWhat is the main purpose of exploitations by a threat actor through the weapon delivered to a target during the Cyber Kill Chain exploitation phase?Correct
Incorrect
-
Question 24 of 43
24. Question
1 pointsWhich term is used in the Diamond Model of intrusion to describe a tool that a threat actor uses toward a target system?Correct
Incorrect
-
Question 25 of 43
25. Question
1 pointsWhat is the role of a Computer Emergency Response Team?Correct
Incorrect
-
Question 26 of 43
26. Question
1 pointsIn the NIST incident response process life cycle, which type of attack vector involves the use of brute force against devices, networks, or services?Correct
Incorrect
-
Question 27 of 43
27. Question
1 pointsWhich NIST incident response life cycle phase includes continuous monitoring by the CSIRT to quickly identify and validate an incident?Correct
Incorrect
-
Question 28 of 43
28. Question
1 pointsWhich NIST incident response life cycle phase includes training for the computer security incident response team on how to respond to an incident?Correct
Incorrect
-
Question 29 of 43
29. Question
1 pointsWhich three aspects of a target system are most likely to be exploited after a weapon is delivered? (Choose three.)Correct
Incorrect
-
Question 30 of 43
30. Question
1 pointsWhich meta-feature element in the Diamond Model describes tools and information (such as software, black hat knowledge base, and username and password) that the adversary uses for the intrusion event?Correct
Incorrect
-
Question 31 of 43
31. Question
1 pointsWhich activity is typically performed by a threat actor in the installation phase of the Cyber Kill Chain?Correct
Incorrect
-
Question 32 of 43
32. Question
1 pointsWhich top-level element of the VERIS schema would allow a company to document the incident timeline?Correct
Incorrect
-
Question 33 of 43
33. Question
1 pointsWhen dealing with a security threat and using the Cyber Kill Chain model, which two approaches can an organization use to help block potential exploitations on a system? (Choose two.)Correct
Incorrect
-
Question 34 of 43
34. Question
1 pointsWhat is a chain of custody?Correct
Incorrect
-
Question 35 of 43
35. Question
1 pointsWhat type of CSIRT organization is responsible for determining trends to help predict and provide warning of future security incidents?Correct
Incorrect
-
Question 36 of 43
36. Question
1 pointsWhich approach can help block potential malware delivery methods, as described in the Cyber Kill Chain model, on an Internet-facing web server?Correct
Incorrect
-
Question 37 of 43
37. Question
1 pointsAccording to NIST standards, which incident response stakeholder isresponsible for coordinating an incident response with other stakeholders to minimize the damage of an incident?Correct
Incorrect
-
Question 38 of 43
38. Question
1 pointsAfter a threat actor completes a port scan of the public web server of an organization and identifies a potential vulnerability, what is the next phase for the threat actor in order to prepare and launch an attack as defined in the Cyber Kill Chain?Correct
Incorrect
-
Question 39 of 43
39. Question
1 pointsA threat actor collects information from web servers of an organization and searches for employee contact information. The information collected is further used to search personal information on the Internet. To which attack phase do these activities belong according to the Cyber Kill Chain model?Correct
Incorrect
-
Question 40 of 43
40. Question
1 pointsMatch the security incident stakeholder with the role.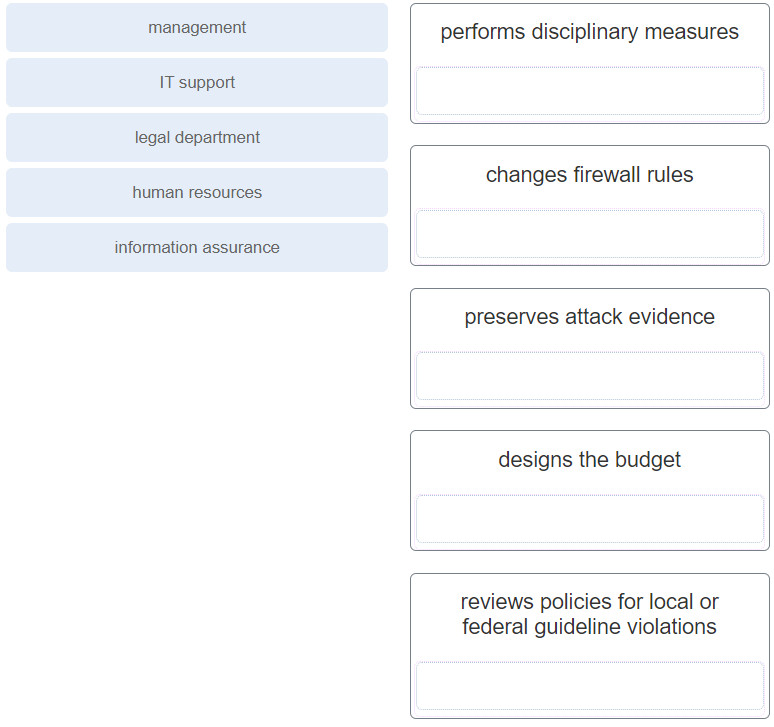 Correct
Correct
Incorrect
-
Question 41 of 43
41. Question
1 pointsMatch the attack vector with the description.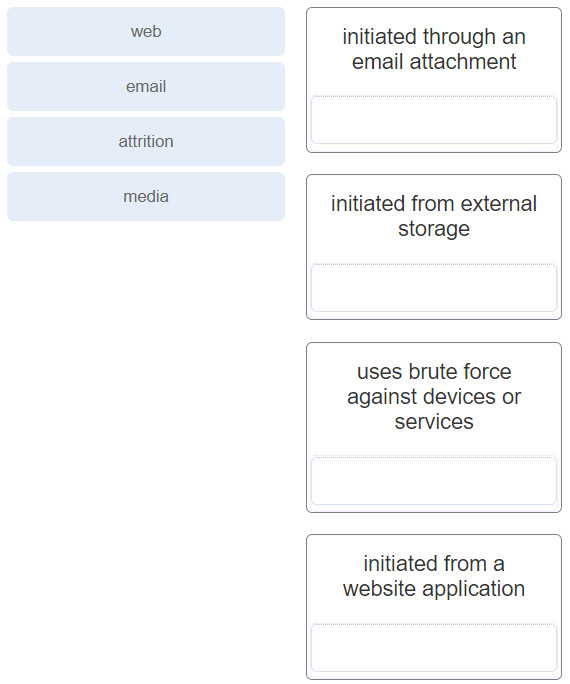 Correct
Correct
Incorrect
-
Question 42 of 43
42. Question
1 pointsMatch the NIST incident response life cycle phase with the description.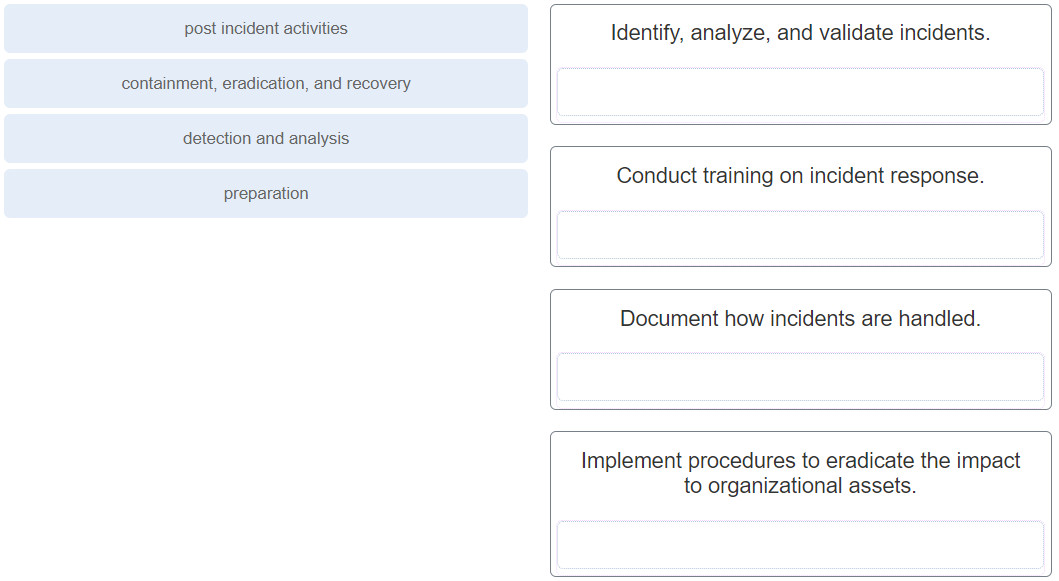 Correct
Correct
Incorrect
-
Question 43 of 43
43. Question
1 pointsMatch the NIST incident response stakeholder with the role.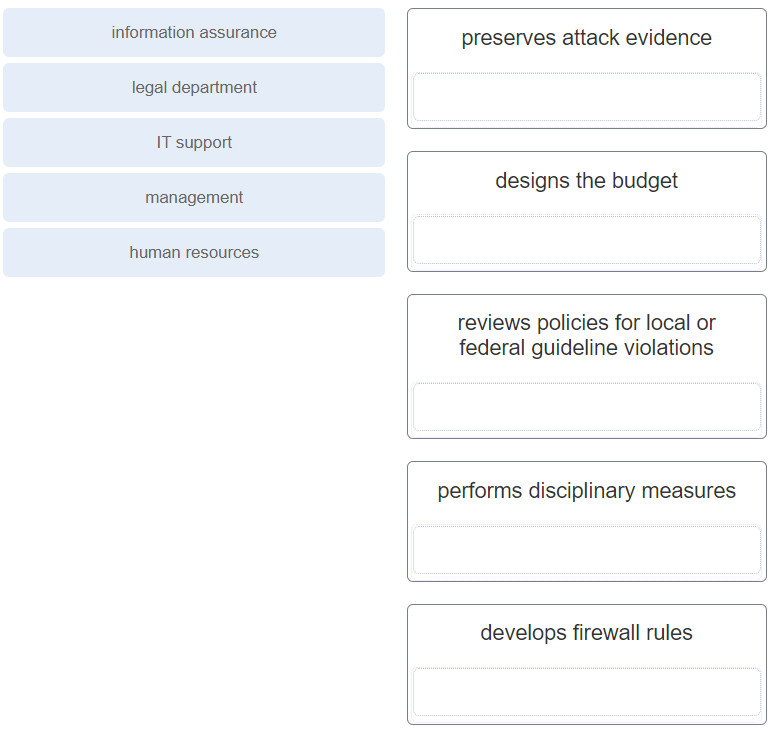 Correct
Correct
Incorrect
