Time limit: 0
Quiz-summary
0 of 417 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
- 365
- 366
- 367
- 368
- 369
- 370
- 371
- 372
- 373
- 374
- 375
- 376
- 377
- 378
- 379
- 380
- 381
- 382
- 383
- 384
- 385
- 386
- 387
- 388
- 389
- 390
- 391
- 392
- 393
- 394
- 395
- 396
- 397
- 398
- 399
- 400
- 401
- 402
- 403
- 404
- 405
- 406
- 407
- 408
- 409
- 410
- 411
- 412
- 413
- 414
- 415
- 416
- 417
Information
Good luck
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 417 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
- 365
- 366
- 367
- 368
- 369
- 370
- 371
- 372
- 373
- 374
- 375
- 376
- 377
- 378
- 379
- 380
- 381
- 382
- 383
- 384
- 385
- 386
- 387
- 388
- 389
- 390
- 391
- 392
- 393
- 394
- 395
- 396
- 397
- 398
- 399
- 400
- 401
- 402
- 403
- 404
- 405
- 406
- 407
- 408
- 409
- 410
- 411
- 412
- 413
- 414
- 415
- 416
- 417
- Answered
- Review
-
Question 1 of 417
1. Question
Which technology supports the stateless assignment of IPv6 addresses?Correct
Incorrect
Hint
DHCPv6 Technology Overview IPv6 Internet Address Assignment Overview IPv6 has been developed with Internet Address assignment dynamics in mind. Being aware that IPv6 Internet addresses are 128 bits in length and written in hexadecimals makes automation of address- assignment an important aspect within network design. These attributes make it inconvenient for a user to manually assign IPv6 addresses, as the format is not naturally intuitive to the human eye. To facilitate address assignment with little or no human intervention, several methods and technologies have been developed to automate the process of address and configuration parameter assignment to IPv6 hosts. The various IPv6 address assignment methods are as follows: 1. Manual Assignment An IPv6 address can be statically configured by a human operator. However, manual assignment is quite open to errors and operational overhead due to the 128 bit length and hexadecimal attributes of the addresses, although for router interfaces and static network elements and resources this can be an appropriate solution. 2. Stateless Address Autoconfiguration (RFC2462) Stateless Address Autoconfiguration (SLAAC) is one of the most convenient methods to assign Internet addresses to IPv6 nodes. This method does not require any human intervention at all from an IPv6 user. If one wants to use IPv6 SLAAC on an IPv6 node, it is important that this IPv6 node is connected to a network with at least one IPv6 router connected. This router is configured by the network administrator and sends out Router Advertisement announcements onto the link. These announcements can allow the on-link connected IPv6 nodes to configure themselves with IPv6 address and routing parameters, as specified in RFC2462, without further human intervention. 3. Stateful DHCPv6 The Dynamic Host Configuration Protocol for IPv6 (DHCPv6) has been standardized by the IETF through RFC3315. DHCPv6 enables DHCP servers to pass configuration parameters, such as IPv6 network addresses, to IPv6 nodes. It offers the capability of automatic allocation of reusable network addresses and additional configuration flexibility. This protocol is a stateful counterpart to "IPv6 Stateless Address Autoconfiguration" (RFC 2462), and can be used separately, or in addition to the stateless autoconfiguration to obtain configuration parameters. 4. DHCPv6-PD DHCPv6 Prefix Delegation (DHCPv6-PD) is an extension to DHCPv6, and is specified in RFC3633. Classical DHCPv6 is typically focused upon parameter assignment from a DHCPv6 server to an IPv6 host running a DHCPv6 protocol stack. A practical example would be the stateful address assignment of "2001:db8::1" from a DHCPv6 server to a DHCPv6 client. DHCPv6-PD however is aimed at assigning complete subnets and other network and interface parameters from a DHCPv6-PD server to a DHCPv6-PD client. This means that instead of a single address assignment, DHCPv6-PD will assign a set of IPv6 "subnets". An example could be the assignment of "2001:db8::/60" from a DHCPv6-PD server to a DHCPv6-PD client. This will allow the DHCPv6-PD client (often a CPE device) to segment the received address IPv6 address space, and assign it dynamically to its IPv6 enabled interfaces. 5. Stateless DHCPv6 Stateless DHCPv6 is a combination of "stateless Address Autoconfiguration" and "Dynamic Host Configuration Protocol for IPv6" and is specified by RFC3736. When using stateless-DHCPv6, a device will use Stateless Address Auto-Configuration (SLAAC) to assign one or more IPv6 addresses to an interface, while it utilizes DHCPv6 to receive "additional parameters" which may not be available through SLAAC. For example, additional parameters could include information such as DNS or NTP server addresses, and are provided in a stateless manner by DHCPv6. Using stateless DHCPv6 means that the DHCPv6 server does not need to keep track of any state of assigned IPv6 addresses, and there is no need for state refreshment as result. On network media supporting a large number of hosts associated to a single DHCPv6 server, this could mean a significant reduction in DHCPv6 messages due to the reduced need for address state refreshments. From Cisco IOS 12.4(15)T onwards the client can also receive timing information, in addition to the "additional parameters" through DHCPv6. This timing information provides an indication to a host when it should refresh its DHCPv6 configuration data. This behavior (RFC4242) is particularly useful in unstable environments where changes are likely to occur. -
Question 2 of 417
2. Question
What are two requirements for an HSRP group? (Choose two.)Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/ip/hot-standby-router-protocol-hsrp/9234-hsrpguidetoc.html#multihsrp Using HSRP, a set of routers works in concert to present the illusion of a single virtual router to the hosts on the LAN. This set is known as an HSRP group or a standby group. A single router elected from the group is responsible for forwarding the packets that hosts send to the virtual router. This router is known as the Active router. Another router is elected as the Standby router. In the event that the Active router fails, the Standby assumes the packet-forwarding duties of the Active router. Although an arbitrary number of routers may run HSRP, only the Active router forwards the packets sent to the virtual router. To minimize network traffic, only the Active and Standby routers send periodic HSRP messages once the protocol has completed the election process. If the Active router fails, the Standby router takes over as the Active router. If the Standby router fails or becomes the Active router, then another router is elected as the Standby router. On a particular LAN, multiple hot standby groups may coexist and overlap. Each standby group emulates a single virtual router. The individual routers may participate in multiple groups. In this case, the router maintains separate state and timers for each group. Each standby group has a single, well-known MAC address, as well as an IP address. -
Question 3 of 417
3. Question
After you configure the Loopback0 interface, which command can you enter to verify the status of the interface and determine whether fast switching is enabled?Correct
Incorrect
Hint
Output from real device Router2901#sh int g0/0 GigabitEthernet0/0 is up, line protocol is up Hardware is CN Gigabit Ethernet, address is c471.fe99.9999 (bia c471.fe99.9999) Description: Lan Internet address is 10.1.1.1/25 MTU 1500 bytes, BW 1000000 Kbit/sec, DLY 10 usec, reliability 255/255, txload 1/255, rxload 1/255 Encapsulation ARPA, loopback not set Keepalive set (10 sec) Full Duplex, 1Gbps, media type is RJ45 output flow-control is unsupported, input flow-control is unsupported ARP type: ARPA, ARP Timeout 04:00:00 Last input 00:00:00, output 00:00:00, output hang never Last clearing of "show interface" counters never Input queue: 0/75/61/0 (size/max/drops/flushes); Total output drops: 0 Queueing strategy: fifo Output queue: 0/40 (size/max) 5 minute input rate 39000 bits/sec, 30 packets/sec 5 minute output rate 73000 bits/sec, 37 packets/sec 41068530 packets input, 3905407112 bytes, 0 no buffer Received 8678853 broadcasts (0 IP multicasts) 0 runts, 0 giants, 45 throttles 0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored 0 watchdog, 79853 multicast, 0 pause input 39267208 packets output, 2262399504 bytes, 0 underruns 0 output errors, 0 collisions, 0 interface resets 79926 unknown protocol drops 0 babbles, 0 late collision, 0 deferred 0 lost carrier, 0 no carrier, 0 pause output 0 output buffer failures, 0 output buffers swapped out Router2901# Router2901 ip int g0/0 GigabitEthernet0/0 is up, line protocol is up Internet address is 10.1.1.1/25 Broadcast address is 255.255.255.255 Address determined by non-volatile memory MTU is 1500 bytes Helper address is not set Directed broadcast forwarding is disabled Secondary address 192.168.1.7/24 Multicast reserved groups joined: 224.0.0.10 Outgoing access list is not set Inbound access list is not set Proxy ARP is enabled Local Proxy ARP is disabled Security level is default Split horizon is enabled ICMP redirects are always sent ICMP unreachables are always sent ICMP mask replies are never sent IP fast switching is enabled IP fast switching on the same interface is disabled IP Flow switching is disabled IP CEF switching is enabled IP CEF switching turbo vector IP multicast fast switching is enabled IP multicast distributed fast switching is disabled IP route-cache flags are Fast, CEF Router Discovery is disabled IP output packet accounting is disabled IP access violation accounting is disabled TCP/IP header compression is disabled RTP/IP header compression is disabled Policy routing is disabled Network address translation is enabled, interface in domain inside BGP Policy Mapping is disabled Input features: Common Flow Table, Stateful Inspection, Virtual Fragment Reassembly, Virtual Fragment Reassembly After IPSec Decryption, CAR, MCI Check Output features: NAT Inside, Common Flow Table, Stateful Inspection, NAT ALG proxy, CAR Post encapsulation features: CAR IPv4 WCCP Redirect outbound is disabled IPv4 WCCP Redirect inbound is disabled IPv4 WCCP Redirect exclude is disabled Router2901# -
Question 4 of 417
4. Question
Which command sequence can you enter to create VLAN 20 and assign it to an interface on a switch?Correct
Incorrect
-
Question 5 of 417
5. Question
Which three commands can you use to set a router boot image? (Choose three.)Correct
Incorrect
-
Question 6 of 417
6. Question
Which two statements about IPv6 and routing protocols are true? (Choose two.)Correct
Incorrect
-
Question 7 of 417
7. Question
If primary and secondary root switches with priority 16384 both experience catastrophic losses, which tertiary switch can take over?Correct
Incorrect
-
Question 8 of 417
8. Question
Which two statements about late collisions are true? (Choose two.)Correct
Incorrect
-
Question 9 of 417
9. Question
Which command can you enter to set the default route for all traffic to an interface?Correct
Incorrect
-
Question 10 of 417
10. Question
Which two spanning-tree port states does RSTP combine to allow faster convergence? (Choose two.)Correct
Incorrect
-
Question 11 of 417
11. Question
If a router has four interfaces and each interface is connected to four switches, how many broadcast domains are present on the router?Correct
Incorrect
-
Question 12 of 417
12. Question
The left describes the types of cables, while the right describes the purposes of the cables. Drag the items on the left to the proper locations. (Not all items can be used.) (THE COMMUNITY SHARED THAT THERE IS ANOTHER OPTION SO STUDY ALL OF WHAT THIS CABLES ARE FOR)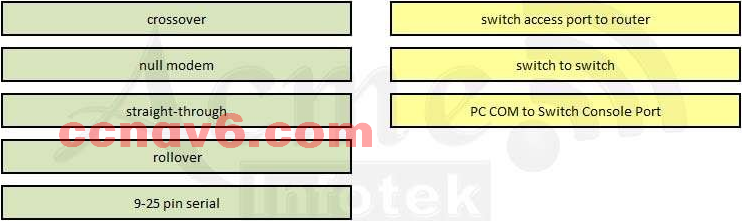
Sort elements
- straight-through
- crossover
- rollover
- null modem
- 9-25 pin serial
-
switch access port to router
-
switch to switch
-
PC COM to Switch Console Port
Correct
Incorrect
-
Question 13 of 417
13. Question
Match the items on the left with appropriate OSI layer on the right. (Not all options are used.)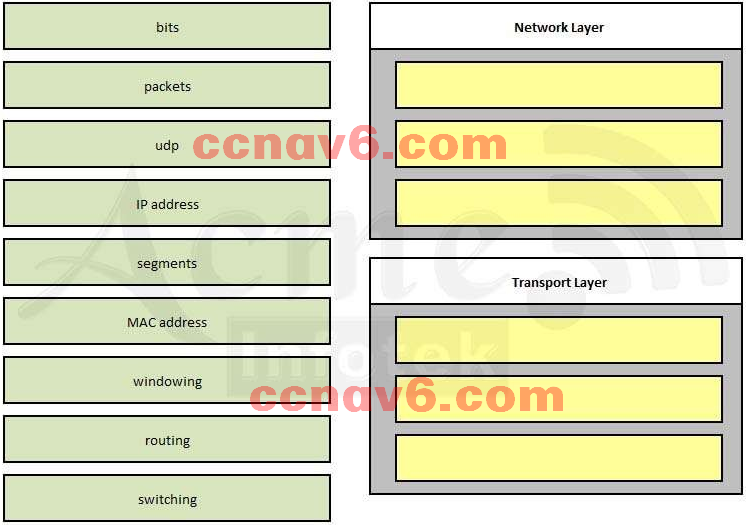
Sort elements
- packets
- IP address
- routing
- udp
- segments
- windowing
- bits
- MAC address
- switching
-
Network Layer
-
Network Layer
-
Network Layer
-
Transport Layer
-
Transport Layer
-
Transport Layer
Correct
Incorrect
-
Question 14 of 417
14. Question
Which command enables IPv6 forwarding on a Cisco router?Correct
Incorrect
-
Question 15 of 417
15. Question
Refer to the exhibit. What is the most appropriate summarization for these routes? Correct
Correct
Incorrect
Hint
Explanation: The 10.0.0.0/22 subnet mask will include the 10.0.0.0, 10.0.1.0, 10.0.2.0, and 10.0.3.0 networks, and only those four networks. -
Question 16 of 417
16. Question
Which set of commands is recommended to prevent the use of a hub in the access layer?Correct
Incorrect
-
Question 17 of 417
17. Question
A router has learned three possible routes that could be used to reach a destination network. One route is from EIGRP and has a composite metric of 20514560. Another route is from OSPF with a metric of 782. The last is from RIPv2 and has a metric of 4. Which route or routes will the router install in the routing table?Correct
Incorrect
-
Question 18 of 417
18. Question
Two routers named Atlanta and Brevard are connected via their serial interfaces as illustrated, but they are unable to communicate. The Atlanta router is known to have the correct configuration.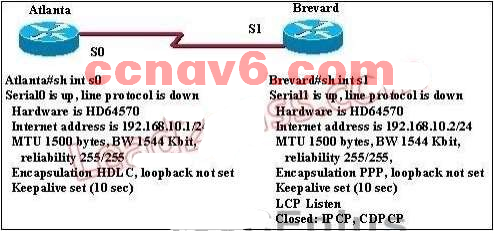 Given the partial configurations, identify the fault on the Brevard router that is causing the lack of connectivity Correct
Given the partial configurations, identify the fault on the Brevard router that is causing the lack of connectivity Correct
Incorrect
-
Question 19 of 417
19. Question
A network administrator needs to configure a serial link between the main office and a remote location. The router at the remote office is a non-Cisco router. How should the network administrator configure the serial interface of the main office router to make the connection?Correct
Incorrect
-
Question 20 of 417
20. Question
Which Layer 2 protocol encapsulation type supports synchronous and asynchronous circuits and has built-in security mechanisms?Correct
Incorrect
-
Question 21 of 417
21. Question
Refer to the exhibit. The two connected ports on the switch are not turning orange or green. What would be the most effective steps to troubleshoot this physical layer problem? (Choose three.) Correct
Correct
Incorrect
-
Question 22 of 417
22. Question
A network administrator is troubleshooting the OSPF configuration of routers R1 and R2. The routers cannot establish an adjacency relationship on their common Ethernet link.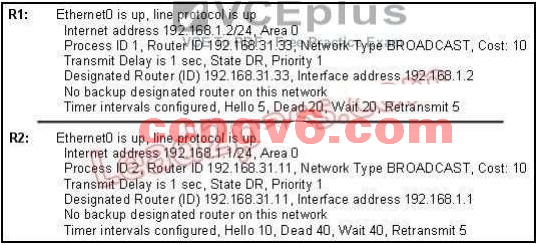 Correct
Correct
Incorrect
-
Question 23 of 417
23. Question
What will happen if a private IP address is assigned to a public interface connected to an ISP?Correct
Incorrect
-
Question 24 of 417
24. Question
Refer to the exhibit. The Bigtime router is unable to authenticate to the Littletime router. What is the cause of the problem?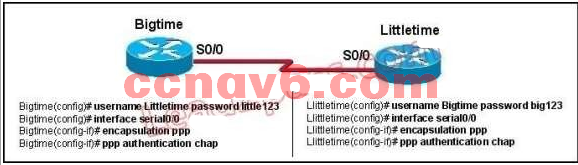 Correct
Correct
Incorrect
-
Question 25 of 417
25. Question
What will be the result if the following configuration commands are implemented on a Cisco switch? Switch(config-if)# switchport port-security Switch(config-if)# switchport port-security mac-address stickyCorrect
Incorrect
-
Question 26 of 417
26. Question
Refer to the exhibit. The following commands are executed on interface fa0/1 of 2950Switch. 2950Switch(config-if)# switchport port-security 2950Switch(config-if)# switchport port-security mac-address sticky 2950Switch(config-if)# switchport port-security maximum 1 The Ethernet frame that is shown arrives on interface fa0/1. What two functions will occur when this frame is received by 2950Switch? (Choose two.)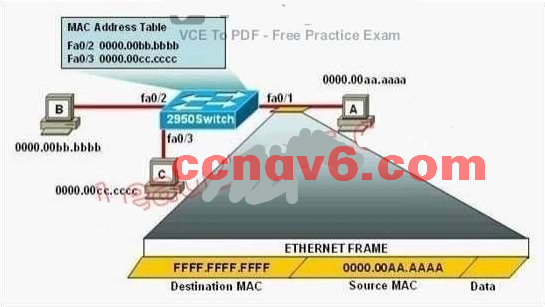 Correct
Correct
Incorrect
-
Question 27 of 417
27. Question
Which command would you configure globally on a Cisco router that would allow you to view directly connected Cisco devices?Correct
Incorrect
-
Question 28 of 417
28. Question
A Cisco router is booting and has just completed the POST process. It is now ready to find and load an IOS image. What function does the router perform next?Correct
Incorrect
-
Question 29 of 417
29. Question
What are three advantages of VLANs? (Choose three.)Correct
Incorrect
-
Question 30 of 417
30. Question
Refer to the exhibit. The output that is shown is generated at a switch. Which three statements are true? (Choose three.)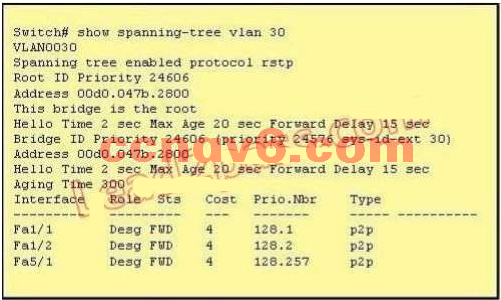 Correct
Correct
Incorrect
-
Question 31 of 417
31. Question
Which two commands can be used to verify a trunk link configuration status on a given Cisco switch interface? (Choose two.)Correct
Incorrect
-
Question 32 of 417
32. Question
Which two states are the port states when RSTP has converged? (Choose two.)Correct
Incorrect
-
Question 33 of 417
33. Question
Refer to the exhibit. A technician has installed Switch B and needs to configure it for remote access from the management workstation connected to Switch A . Which set of commands is required to accomplish this task? Correct
Correct
Incorrect
-
Question 34 of 417
34. Question
Which of the following are benefits of VLANs? (Choose three.)Correct
Incorrect
-
Question 35 of 417
35. Question
What are three benefits of implementing VLANs? (Choose three.)Correct
Incorrect
-
Question 36 of 417
36. Question
Which three statements accurately describe Layer 2 Ethernet switches? (Choose three.)Correct
Incorrect
-
Question 37 of 417
37. Question
Which of the following correctly describe steps in the OSI data encapsulation process? (Choose two.)Correct
Incorrect
-
Question 38 of 417
38. Question
Which of the following describes the roles of devices in a WAN? (Choose three.)Correct
Incorrect
-
Question 39 of 417
39. Question
Which interface counter can you use to diagnose a duplex mismatch problem?Correct
Incorrect
-
Question 40 of 417
40. Question
Which feature can you implement to reserve bandwidth for VoIP calls across the call path?Correct
Incorrect
-
Question 41 of 417
41. Question
When an interface is configured with PortFast BPDU guard, how does the interface respond when it receives a BPDU?Correct
Incorrect
-
Question 42 of 417
42. Question
What are three characteristics of the TCP protocol? (Choose three.)Correct
Incorrect
-
Question 43 of 417
43. Question
Which command can you enter to determine whether serial interface 0/2/0 has been configured using HDLC encapsulation?Correct
Incorrect
Hint
Output from real device Router2901#sh int g0/0 GigabitEthernet0/0 is up, line protocol is up Hardware is CN Gigabit Ethernet, address is c471.fe99.9999 (bia c471.fe99.9999) Description: Lan Internet address is 10.1.1.1/25 MTU 1500 bytes, BW 1000000 Kbit/sec, DLY 10 usec, reliability 255/255, txload 1/255, rxload 1/255 Encapsulation ARPA, loopback not set Keepalive set (10 sec) Full Duplex, 1Gbps, media type is RJ45 output flow-control is unsupported, input flow-control is unsupported ARP type: ARPA, ARP Timeout 04:00:00 Last input 00:00:00, output 00:00:00, output hang never Last clearing of "show interface" counters never Input queue: 0/75/61/0 (size/max/drops/flushes); Total output drops: 0 Queueing strategy: fifo Output queue: 0/40 (size/max) 5 minute input rate 39000 bits/sec, 30 packets/sec 5 minute output rate 73000 bits/sec, 37 packets/sec 41068530 packets input, 3905407112 bytes, 0 no buffer Received 8678853 broadcasts (0 IP multicasts) 0 runts, 0 giants, 45 throttles 0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored 0 watchdog, 79853 multicast, 0 pause input 39267208 packets output, 2262399504 bytes, 0 underruns 0 output errors, 0 collisions, 0 interface resets 79926 unknown protocol drops 0 babbles, 0 late collision, 0 deferred 0 lost carrier, 0 no carrier, 0 pause output 0 output buffer failures, 0 output buffers swapped out Router2901# Router2901 ip int g0/0 GigabitEthernet0/0 is up, line protocol is up Internet address is 10.1.1.1/25 Broadcast address is 255.255.255.255 Address determined by non-volatile memory MTU is 1500 bytes Helper address is not set Directed broadcast forwarding is disabled Secondary address 192.168.1.7/24 Multicast reserved groups joined: 224.0.0.10 Outgoing access list is not set Inbound access list is not set Proxy ARP is enabled Local Proxy ARP is disabled Security level is default Split horizon is enabled ICMP redirects are always sent ICMP unreachables are always sent ICMP mask replies are never sent IP fast switching is enabled IP fast switching on the same interface is disabled IP Flow switching is disabled IP CEF switching is enabled IP CEF switching turbo vector IP multicast fast switching is enabled IP multicast distributed fast switching is disabled IP route-cache flags are Fast, CEF Router Discovery is disabled IP output packet accounting is disabled IP access violation accounting is disabled TCP/IP header compression is disabled RTP/IP header compression is disabled Policy routing is disabled Network address translation is enabled, interface in domain inside BGP Policy Mapping is disabled Input features: Common Flow Table, Stateful Inspection, Virtual Fragment Reassembly, Virtual Fragment Reassembly After IPSec Decryption, CAR, MCI Check Output features: NAT Inside, Common Flow Table, Stateful Inspection, NAT ALG proxy, CAR Post encapsulation features: CAR IPv4 WCCP Redirect outbound is disabled IPv4 WCCP Redirect inbound is disabled IPv4 WCCP Redirect exclude is disabled Router2901# -
Question 44 of 417
44. Question
Which two statements about IPv4 multicast traffic are true? (Choose two.)Correct
Incorrect
Hint
http://www.cisco.com/c/dam/en_us/about/ciscoitatwork/downloads/ciscoitatwork/pdf/cisco_it_case_study_multicast.pdf Cisco IOS IP Multicast in the Cisco Network “IP Multicast as defined in RFC1112, the standard for IP Multicast across networks and the Internet, supports one-to-many content needs by delivering application-source traffic to multiple users without burdening the source or the network, using a minimum amount of network bandwidth. At the point where paths diverge, Cisco routers replace IP Multicast packets in the network, resulting in the most efficient delivery of data to multiple receivers.” Even low-bandwidth applications can benefit fro IP Multicast when there are thousands of receivers. High-bandwidth applications, such as MPEG video, may need a large portion of the available network bandwidth for a single stream. In these applications, IP Multicast is the only way to efficiently send the same content to more than one receiver simultaneously, because it makes sure that only one copy of the data stream is sent across any one network link. It relies on each router in the stream to intelligently copy the data stream whenever it needs to deliver it to multiple receivers. -
Question 45 of 417
45. Question
What are two benefits of private IPv4 IP addresses? (Choose two.)Correct
Incorrect
-
Question 46 of 417
46. Question
What is the authoritative source for an address lookup?Correct
Incorrect
-
Question 47 of 417
47. Question
Which command can you enter to verify that a BGP connection to a remote device is established?Correct
Incorrect
-
Question 48 of 417
48. Question
During which phase of PPPoE is PPP authentication performed ?Correct
Incorrect
-
Question 49 of 417
49. Question
Which three circumstances can cause a GRE tunnel to be in an up/down state? (Choose three.)Correct
Incorrect
-
Question 50 of 417
50. Question
Which two statements about using leased lines for your WAN infrastructure are true? (Choose two.)Correct
Incorrect
Hint
from W.Odom Official Cert Guide for ICND1 v3 Telcos offer a wide variety of speeds for leased lines. However, you cannot pick the exact speed you want; instead, you must pick from a long list of predefined speeds. Slower-speed links run at multiples of 64 kbps (kilobits per second), while faster links run at multiples of about 1.5 Mbps (megabits per second). Leased lines have many benefits that have led to their relatively long life in the WAN mar- ketplace. These lines are simple for the customer, are widely available, are of high quality, and are private. However, they do have some negatives as well compared to newer WAN technologies, including a higher cost and typically longer lead times to get the service installed. -
Question 51 of 417
51. Question
Which two statements about wireless LAN controllers are true? (Choose two.)Correct
Incorrect
-
Question 52 of 417
52. Question
Which two statements about northbound and southbound APIs are true? (Choose two.)Correct
Incorrect
-
Question 53 of 417
53. Question
Which command can you enter to set the default route for all traffic to an interface?Correct
Incorrect
-
Question 54 of 417
54. Question
Which statement about RADIUS security is true?Correct
Incorrect
-
Question 55 of 417
55. Question
If you are configuring syslog messages specifying `logging trap warning', which log messages will the router send?Correct
Incorrect
Hint
Explanation: 0 emergencies System is unusable 1 alerts Immediate action is needed 2 critical Critical conditions exist 3 errors Error conditions exist 4 warnings Warning conditions exist 5 notification Normal, but significant, conditions exist 6 informational Informational messages 7 debugging Debugging messages -
Question 56 of 417
56. Question
What is true about Ethernet? (Choose Two.)Correct
Incorrect
Hint
http://www.ieee802.org/3/ CSMA/CD - It uses a carrier sensing scheme in which a transmitting station detects collisions by sensing transmissions from other stations while transmitting a frame. When this collision condition is detected, the station stops transmitting that frame. -
Question 57 of 417
57. Question
What IP SLA ICMP Echo measures?Correct
Incorrect
-
Question 58 of 417
58. Question
What are types of IPv6 static routes? (Choose Three )Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/iproute_pi/configuration/xe-16/iri-xe-16-book/iri-recursive-static-route-xe.html -
Question 59 of 417
59. Question
What is the status of port-channel if LACP is misconfigured ?Correct
Incorrect
-
Question 60 of 417
60. Question
What is true about DTP? (Choose Three.)Correct
Incorrect
Hint
https://en.wikipedia.org/wiki/Dynamic_Trunking_Protocol -
Question 61 of 417
61. Question
How to create a trunk port and allow VLAN 20? (Choose Three.)Correct
Incorrect
-
Question 62 of 417
62. Question
What 8-bit field exists in IP packet for QoS ?Correct
Incorrect
Hint
http://flylib.com/books/2/686/1/html/2/images/1587051990/graphics/13fig01.gif -
Question 63 of 417
63. Question
What feature uses a random time to re-sent a frame?Correct
Incorrect
-
Question 64 of 417
64. Question
Which mode is compatible with Trunk, Access, and desirable ports?Correct
Incorrect
Hint
Explanation from http://www.9tut.com/trunking-questions Maybe this question wanted to ask “if the other end is configured with trunk/access/desirable mode” then which mode is compatible so that the link can work. In that case both “dynamic auto” and “dynamic desirable” mode are correct. The difference between these two modes is “dynamic auto” is passively waiting for the other end to request to form a trunk while “dynamic desirable” will actively attempt to negotiate to convert the link into a trunk. -
Question 65 of 417
65. Question
If you configure syslog messages without specifying the logging trap level, which log messages will the router send ?Correct
Incorrect
Hint
Router(config)# logging trap level - Specifies the kind of messages, by severity level, to be sent to the syslog server. The default is informational (6) and lower ( 0 6). The possible values for level are as follows: Emergency: 0 Alert: 1 Critical: 2 Error: 3 Warning: 4 Notice: 5 Informational: 6 Debug: 7 -
Question 66 of 417
66. Question
Which command can you execute to set the user inactivity timer to 10 seconds?Correct
Incorrect
-
Question 67 of 417
67. Question
Which standards-based First Hop Redundancy Protocol is a Cisco supported alternative to Hot Standby Router Protocol?Correct
Incorrect
-
Question 68 of 417
68. Question
Two hosts are attached to a switch with the default configuration. Which statement about the configuration is true?Correct
Incorrect
-
Question 69 of 417
69. Question
If there are 3 hosts connected in one port of a switch and two other hosts connected in another port, how many collision domains are present on the router?Correct
Incorrect
-
Question 70 of 417
70. Question
What are three parts of an IPv6 global unicast address? (Choose three.)Correct
Incorrect
-
Question 71 of 417
71. Question
You have been asked to come up with a subnet mask that will allow all three web servers to be on the same network while providing the maximum number of subnets. Which network address and subnet mask meet this requirement?Correct
Incorrect
-
Question 72 of 417
72. Question
What parameter can be different on ports within an EtherChannel?Correct
Incorrect
-
Question 73 of 417
73. Question
Which two statements about IPv6 router advertisement messages are true? (Choose two.)Correct
Incorrect
Hint
https://supportforums.cisco.com/document/77521/ipv6-neighbor-discovery-protocol-ndp -
Question 74 of 417
74. Question
Which spanning-tree protocol rides on top of another spanning-tree protocol?Correct
Incorrect
-
Question 75 of 417
75. Question
A network administrator needs to configure port security on a switch. Which two statements are true? (Choose two.)Correct
Incorrect
-
Question 76 of 417
76. Question
Which switching method duplicates the first six bytes of a frame before making a switching decision?Correct
Incorrect
-
Question 77 of 417
77. Question
Which logging command can enable administrators to correlate syslog messages with millisecond precision?Correct
Incorrect
-
Question 78 of 417
78. Question
Which three statements about link-state routing are true? (Choose three.)Correct
Incorrect
-
Question 79 of 417
79. Question
Which command can you enter to determine whether a switch is operating in trunking mode?Correct
Incorrect
-
Question 80 of 417
80. Question
Which command can you enter to view the ports that are assigned to VLAN 20 ?Correct
Incorrect
-
Question 81 of 417
81. Question
In which two formats can the IPv6 address fd15:0db8:0000:0000:0700:0003:400F:572B be written? (Choose two.)Correct
Incorrect
-
Question 82 of 417
82. Question
Which function of the IP SLAs ICMP jitter operation can you use to determine whether a VoIP issue is caused by excessive end-to-end time?Correct
Incorrect
-
Question 83 of 417
83. Question
Refer to the exhibit.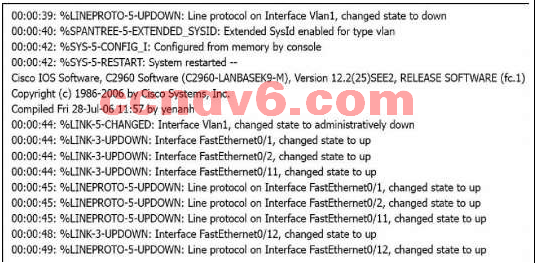 Which of these statements correctly describes the state of the switch once the boot process has been completed? Correct
Which of these statements correctly describes the state of the switch once the boot process has been completed? Correct
Incorrect
-
Question 84 of 417
84. Question
Refer to the exhibit. The network administrator normally establishes a Telnet session with the switch from host A. However, host A is unavailable. The administrator's attempt to telnet to the switch from host fails, but pings to the other two hosts are successful. What is the issue? Correct
Correct
Incorrect
-
Question 85 of 417
85. Question
Which condition does the err-disabled status indicate on an Ethernet interface?Correct
Incorrect
-
Question 86 of 417
86. Question
Refer to the exhibit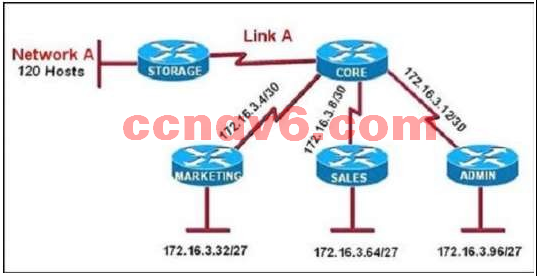 All of the routers in the network are configured with the ip subnet-zero command. Which network addresses should
be used for Link A and Network A? (Choose two.) Correct
All of the routers in the network are configured with the ip subnet-zero command. Which network addresses should
be used for Link A and Network A? (Choose two.) Correct
Incorrect
-
Question 87 of 417
87. Question
Which type of device can be replaced by the use of subinterfaces for VLAN routing ?Correct
Incorrect
-
Question 88 of 417
88. Question
Which statement about LLDP is true?Correct
Incorrect
-
Question 89 of 417
89. Question
If the primary root bridge experiences a power loss, which switch takes over?Correct
Incorrect
-
Question 90 of 417
90. Question
A network administrator is troubleshooting an EIGRP problem on a router and needs to confirm the IP addresses of the devices with which the router has established adjacency. The retransmit interval and the queue counts for the adjacent routers also need to be checked. What command will display the required information?Correct
Incorrect
-
Question 91 of 417
91. Question
Which three statements about IPv6 prefixes are true? (Choose three.)Correct
Incorrect
-
Question 92 of 417
92. Question
Which command can you enter to display duplicate IP addresses that the DHCP server assigns?Correct
Incorrect
-
Question 93 of 417
93. Question
Which three ports will be STP designated ports if all the links are operating at the same bandwidth? (Choose three.)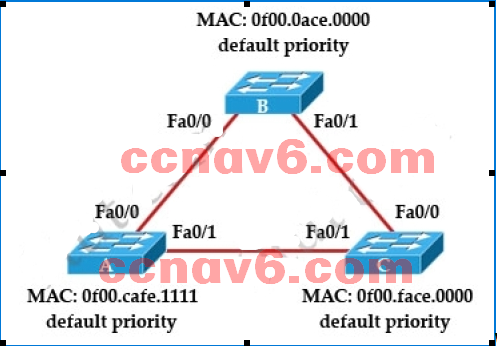 Correct
Correct
Incorrect
-
Question 94 of 417
94. Question
Refer to the exhibit The network administrator cannot connect to Switch 1 over a Telnet session, although the hosts attached to Switch1 can ping the interface Fa0/0 of the router. Given the information in the graphic and assuming that the router and Switch2 are configured properly, which of the following commands should be issued on Switch1 to correct this problem? Correct
The network administrator cannot connect to Switch 1 over a Telnet session, although the hosts attached to Switch1 can ping the interface Fa0/0 of the router. Given the information in the graphic and assuming that the router and Switch2 are configured properly, which of the following commands should be issued on Switch1 to correct this problem? Correct
Incorrect
-
Question 95 of 417
95. Question
Refer to the exhibit.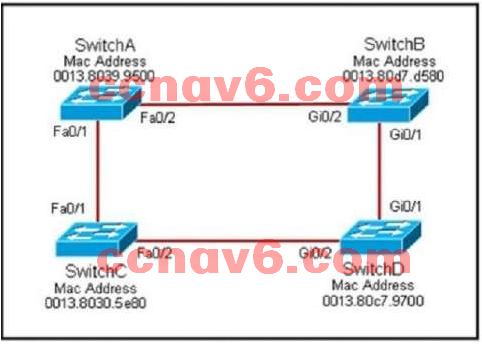 Each of these four switches has been configured with a hostname, as well as being configured to run RSTP.No other configuration changes have been made. Which three of these show the correct RSTP port roles for the indicated switches and interfaces? (Choose three.) Correct
Each of these four switches has been configured with a hostname, as well as being configured to run RSTP.No other configuration changes have been made. Which three of these show the correct RSTP port roles for the indicated switches and interfaces? (Choose three.) Correct
Incorrect
-
Question 96 of 417
96. Question
Which feature builds a FIB and an adjacency table to expedite packet forwarding?Correct
Incorrect
-
Question 97 of 417
97. Question
Which command can you enter to verify that a 128-bit address is live and responding?Correct
Incorrect
-
Question 98 of 417
98. Question
What are two reasons that duplex mismatches can be difficult to diagnose? (Choose two.)Correct
Incorrect
-
Question 99 of 417
99. Question
Which condition indicates that service password-encryption is enabled?Correct
Incorrect
-
Question 100 of 417
100. Question
Which protocol advertises a virtual IP address to facilitate transparent failover of a Cisco routing device?Correct
Incorrect
-
Question 101 of 417
101. Question
What is the correct routing match to reach 172.16.1.5/32 ?Correct
Incorrect
-
Question 102 of 417
102. Question
Which layer in the OSI reference model is responsible for determining the availability of the receiving program and checking to see if enough resources exist for that communication?Correct
Incorrect
-
Question 103 of 417
103. Question
What is the purpose of the POST operation on a router ?Correct
Incorrect
-
Question 104 of 417
104. Question
Which protocol is the Cisco proprietary implementation of FHRP ?Correct
Incorrect
-
Question 105 of 417
105. Question
Which three characteristics are representative of a link-state routing protocol? (Choose three.)Correct
Incorrect
-
Question 106 of 417
106. Question
Which part of the PPPoE server configuration contains the information used to assign an IP address to a PPPoE client?Correct
Incorrect
-
Question 107 of 417
107. Question
Drag and drop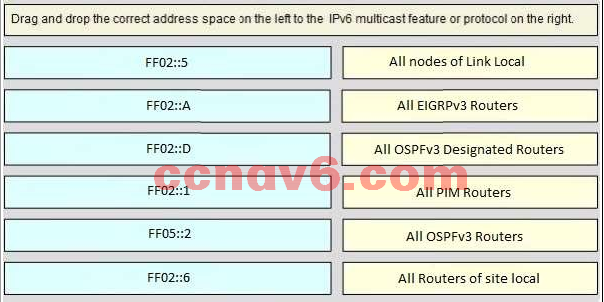
Sort elements
- All Nodes (link-local)
- OSPFv3 Routers
- OSPFv3 Designated Routers
- EIGRPv3 Routers
- PIM Routers
- All Routers (site-local)
-
FF02::1
-
FF02::5
-
FF02::6
-
FF02::A
-
FF02::D
-
FF05::2
Correct
Incorrect
-
Question 108 of 417
108. Question
Which three statements about RSTP are true? (Choose three.)Correct
Incorrect
-
Question 109 of 417
109. Question
What are two benefits of using NAT? (Choose two.)Correct
Incorrect
-
Question 110 of 417
110. Question
Which two commands correctly verify whether port security has been configured on port FastEthernet 0/12 on a switch? (Choose two.)Correct
Incorrect
-
Question 111 of 417
111. Question
Refer to the exhibit. Given this output for SwitchC, what should the network administrator's next action be?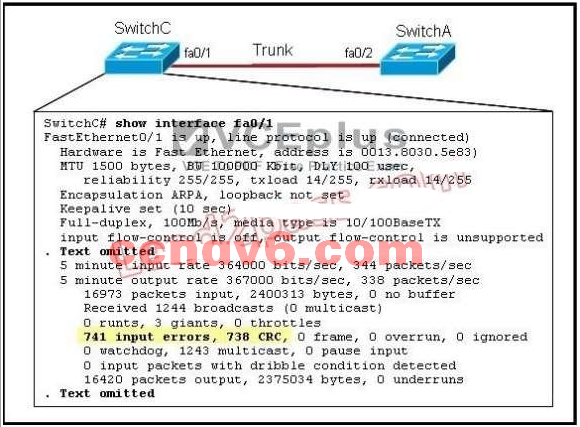 Correct
Correct
Incorrect
-
Question 112 of 417
112. Question
Which statement is correct regarding the operation of DHCP ?Correct
Incorrect
-
Question 113 of 417
113. Question
Which two statements about using the CHAP authentication mechanism in a PPP link are true ? (Choose two.)Correct
Incorrect
-
Question 114 of 417
114. Question
Refer to the exhibit. Switch port FastEthernet 0/24 on ALSwitch1 will be used to create an IEEE 802.1Q-compliant trunk to another switch. Based on the output shown, what is the reason the trunk does not form, even though the proper cabling has been attached?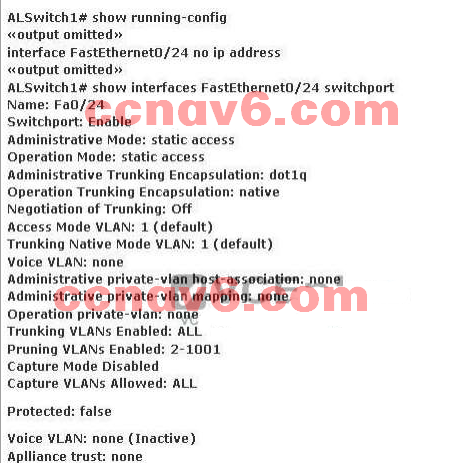 Correct
Correct
Incorrect
-
Question 115 of 417
115. Question
Refer to the exhibit. A junior network administrator was given the task of configuring port security on SwitchA to allow only PC_A to access the switched network through port fa0/1. If any other device is detected, the port is to drop frames from this device. The administrator configured the interface and tested it with successful pings from PC_A to RouterA, and then observes the output from these two show commands. Which two of these changes are necessary for SwitchA to meet the requirements? (Choose two.)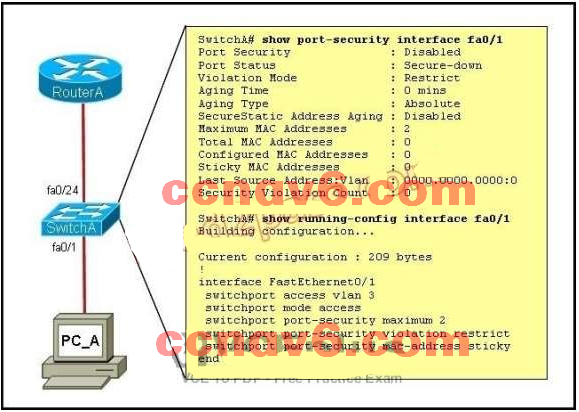 Correct
Correct
Incorrect
-
Question 116 of 417
116. Question
Which three statements about static routing are true? (Choose three.)Correct
Incorrect
-
Question 117 of 417
117. Question
What are the address that will show at the show ip route if we configure the above statements? (Choose Three.)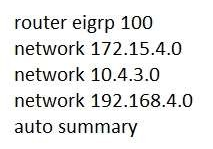 Correct
Correct
Incorrect
-
Question 118 of 417
118. Question
Which feature facilitates the tagging of frames on a specific VLAN ?Correct
Incorrect
-
Question 119 of 417
119. Question
What does split horizon prevent?Correct
Incorrect
-
Question 120 of 417
120. Question
Which value to use in HSRP protocol election process ?Correct
Incorrect
-
Question 121 of 417
121. Question
Which of the following is needed to be enable back the role of active in HSRP ?Correct
Incorrect
-
Question 122 of 417
122. Question
Which command is used to show the interface status of a router ?Correct
Incorrect
-
Question 123 of 417
123. Question
Which of the following privilege level is the most secured ?Correct
Incorrect
-
Question 124 of 417
124. Question
Which IPV6 feature is supported in IPV4 but is not commonly used ?Correct
Incorrect
-
Question 125 of 417
125. Question
Which two statements are true about IPv6 Unique Local Addresses ? (Choose Two.)Correct
Incorrect
-
Question 126 of 417
126. Question
Which range represents the standard access list ?Correct
Incorrect
-
Question 127 of 417
127. Question
What to do when the router password was forgotten ?Correct
Incorrect
-
Question 128 of 417
128. Question
What is true about Cisco Discovery Protocol ?Correct
Incorrect
-
Question 129 of 417
129. Question
Which of the following encrypts the traffic on a leased line ?Correct
Incorrect
-
Question 130 of 417
130. Question
Fill in the blank.- How do you configure a hostname ? (Router(config)#hostname R1)
Correct
Incorrect
-
Question 131 of 417
131. Question
How do you maintain security in multiple websites?Correct
Incorrect
-
Question 132 of 417
132. Question
Refer to the exhibit. Switch-1 needs to send data to a host with a MAC address of 00b0.d056.efa4. What will Switch-1 do with this data?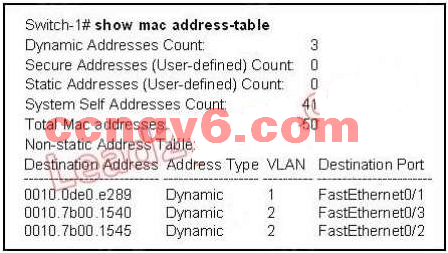 Correct
Correct
Incorrect
-
Question 133 of 417
133. Question
What routing protocol use first-hand information from peers?Correct
Incorrect
Hint
http://www.ciscopress.com/articles/article.asp?p=24090&seqNum=4 The reason is that unlike the routing-by-rumor approach of distance vector, link state routers have firsthand information from all their peer routers. Each router originates information about itself, its directly connected links, and the state of those links (hence the name). This information is passed around from router to router, each router making a copy of it, but never changing it. The ultimate objective is that every router has identical information about the internetwork, and each router will independently calculate its own best paths. -
Question 134 of 417
134. Question
What field is consist of 6 bytes in the field identification frame in IEEE 802.1Q?Correct
Incorrect
-
Question 135 of 417
135. Question
What is new in HSRPv2?Correct
Incorrect
-
Question 136 of 417
136. Question
What’s are true about MPLS?Correct
Incorrect
-
Question 137 of 417
137. Question
A network engineer wants to allow a temporary entry for a remote user with a specific username and password so that the user can access the entire network over the internet. Which ACL can be used?Correct
Incorrect
Hint
http://xgu.ru/wiki/Cisco_ACL -
Question 138 of 417
138. Question
Which command is necessary to permit SSH or Telnet access to a cisco switch that is otherwise configured for these vty line protocols?Correct
Incorrect
-
Question 139 of 417
139. Question
What should be part of a comprehensive network security plan?Correct
Incorrect
-
Question 140 of 417
140. Question
Which two Cisco IOS commands, used in troubleshooting, can enable debug output to a remote location ? (Choose two)Correct
Incorrect
-
Question 141 of 417
141. Question
Which component of the Cisco SDN solution serves as the centralized management system?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/solutions/data-center-virtualization/application-centric-infrastructure/index.html Cisco Application Policy Infrastructure Controller (APIC) Provides single-click access to all Cisco ACI fabric information, enabling network automation, programmability, and centralized management. http://www.cisco.com/c/en/us/products/cloud-systems-management/application-policy-infrastructure-controller-apic/index.html The Cisco Application Policy Infrastructure Controller (Cisco APIC) is the unifying point of automation and management for the Application Centric Infrastructure (ACI) fabric. The Cisco APIC provides centralized access to all fabric information, optimizes the application lifecycle for scale and performance, and supports flexible application provisioning across physical and virtual resources. The Cisco APIC provides centralized access to all fabric information, optimizes the application lifecycle for scale and performance, and supports flexible application provisioning across physical and virtual resources. Centralized application-level policy engine for physical, virtual, and cloud infrastructures Designed for automation, programmability, and centralized management, the Cisco APIC itself exposes northbound APIs through XML and JSON. It provides both a command-line interface (CLI) and GUI which utilize the APIs to manage the fabric holistically. Cisco APIC provides: A single pane of glass for application-centric network policies Fabric image management and inventory Application, tenant, and topology monitoring Troubleshooting -
Question 142 of 417
142. Question
What command can you enter in config mode to create DHCP pool?Correct
Incorrect
-
Question 143 of 417
143. Question
Which utility can you use to determine whether a switch can send echo requests and replies?Correct
Incorrect
-
Question 144 of 417
144. Question
What is the two benefits of DHCP snooping? (Choose two)Correct
Incorrect
-
Question 145 of 417
145. Question
What is the two benefits of DHCP snooping? (Choose two)Correct
Incorrect
-
Question 146 of 417
146. Question
What are the three major components of cisco network virtualization? (Choose Three)Correct
Incorrect
-
Question 147 of 417
147. Question
Which feature is config by setting a variance that is at least 2 times the metric?Correct
Incorrect
-
Question 148 of 417
148. Question
Two features of the extended ping command? (Choose two)Correct
Incorrect
-
Question 149 of 417
149. Question
What command is used to configure a switch as authoritative NTP server?Correct
Incorrect
-
Question 150 of 417
150. Question
Which two statements about syslog logging are true? (choose two)Correct
Incorrect
Hint
tested on real hardware Router2801#sh logging Syslog logging: enabled (11 messages dropped, 1 messages rate-limited, 0 flushes, 0 overruns, xml disabled, filtering disabled) No Active Message Discriminator. No Inactive Message Discriminator Console logging: level debugging, 348 messages logged, xml disabled, filtering disabled Monitor logging: level debugging, 0 messages logged, xml disabled, filtering disabled Buffer logging: level warnings, 56 messages logged, xml disabled, filtering disabled Logging Exception size (4096 bytes) Count and timestamp logging messages: disabled Persistent logging: disabled No active filter modules. ESM: 0 messages dropped Trap logging: level informational, 343 message lines logged Log Buffer (51200 bytes): *May 16 08:11:45: %LINK-3-UPDOWN: Interface Virtual-Access1, changed state to up *May 16 08:11:49: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to up May 16 08:22:11: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to down May 16 08:22:45: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to up May 16 08:35:25: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to down May 16 08:36:49: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to up May 16 10:25:02: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to down May 16 10:25:53: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to up May 16 17:49:46: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to down May 16 17:50:22: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to up Router2801# -------------------------------------------------------------------------- After reload: Router2801#sh logging Syslog logging: enabled (11 messages dropped, 1 messages rate-limited, 0 flushes, 0 overruns, xml disabled, filtering disabled) No Active Message Discriminator. No Inactive Message Discriminator. Console logging: level debugging, 26 messages logged, xml disabled, filtering disabled Monitor logging: level debugging, 0 messages logged, xml disabled, filtering disabled Buffer logging: level warnings, 2 messages logged, xml disabled, filtering disabled Logging Exception size (4096 bytes) Count and timestamp logging messages: disabled Persistent logging: disabled No active filter modules. ESM: 0 messages dropped Trap logging: level informational, 30 message lines logged Log Buffer (51200 bytes): *May 17 11:39:45: %LINK-3-UPDOWN: Interface Virtual-Access1, changed state to up *May 17 11:39:49: %LINK-3-UPDOWN: Interface Virtual-Access2, changed state to up Router2801# -
Question 151 of 417
151. Question
How to enable vlans automatically across multiple switches?Correct
Incorrect
-
Question 152 of 417
152. Question
Which password types are encrypted?Correct
Incorrect
-
Question 153 of 417
153. Question
What is the binary pattern of unique ipv6 unique local address?Correct
Incorrect
-
Question 154 of 417
154. Question
Which statement about ACLs is true?Correct
Incorrect
-
Question 155 of 417
155. Question
What is the cause of the Syslog output messages?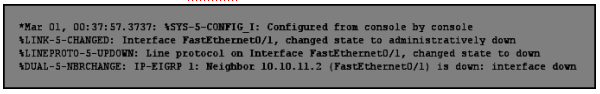 Correct
Correct
Incorrect
-
Question 156 of 417
156. Question
What are contained in layer 2 ethernet frame? (Choose Three.)Correct
Incorrect
-
Question 157 of 417
157. Question
Describe the best way to troubleshoot and isolate a network problem?Correct
Incorrect
-
Question 158 of 417
158. Question
Under normal operations, cisco recommends that you configure switch ports on which vlan?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/switches/catalyst-6500-series-switches/24330-185.html Note: There is a potential security consideration with dot1q that the implicit tagging of the native VLAN causes. The transmission of frames from one VLAN to another without a router can be possible. Refer to the Intrusion Detection FAQ leavingcisco.com for further details. The workaround is to use a VLAN ID for the native VLAN of the trunk that is not used for end-user access. In order to achieve this, the majority of Cisco customers simply leave VLAN 1 as the native VLAN on a trunk and assign access ports to VLANs other than VLAN 1. -
Question 159 of 417
159. Question
In which byte of an IP packet can traffic be marked?Correct
Incorrect
Hint

-
Question 160 of 417
160. Question
Which command can you enter to route all traffic that is destined to 192.168.0.0/20 to a specific interface?Correct
Incorrect
-
Question 161 of 417
161. Question
Which two protocol can detect native vlan mismatch errors? (Choose two.)Correct
Incorrect
Hint
A Oct 5 23:29:16: %CDP-4-NATIVE_VLAN_MISMATCH: Native VLAN mismatch discovered on GigabitEthernet11/43 (512), with WS-C2950-12 FastEthernet0/6 (1) D http://blog.ine.com/2008/07/17/pvst-explained/ Case 1: Change the native VLAN on SW1 connection to R3: SW1: interface FastEthernet 1/3 switchport trunk native vlan 2 Rack1SW2# %SPANTREE-2-RECV_PVID_ERR: Received BPDU with inconsistent peer vlan id 2 on FastEthernet1/3 VLAN1. %SPANTREE-2-BLOCK_PVID_PEER: Blocking FastEthernet1/3 on VLAN2. Inconsistent peer vlan.PVST+: restarted the forward delay timer for FastEthernet1/3 %SPANTREE-2-BLOCK_PVID_LOCAL: Blocking FastEthernet1/3 on VLAN1. Inconsistent local vlan.PVST+: restarted the forward delay timer for FastEthernet1/3 Note that SW2 detects untagged packet with VLAN ID 2, which does not correspond to the locally configured default native VLAN 1. The corresponding port is put in «inconsistent» state. The reason SW2 detects this condition (and not SW1) is because SW1 sending SSTP BPDUs and SW2 is not (it receives superios BPDUs). As soon as native VLAN is converted back to «1» on SW1, consistency is restored: -
Question 162 of 417
162. Question
Which three options are switchport config that can always avoid duplex mismatch error between the switches? (Choose Three.)Correct
Incorrect
Hint
http://www.pathsolutions.com/network-enemy-1-duplex-mismatch/ -
Question 163 of 417
163. Question
What are two benefits of Private IPv4 Addresses? (Choose two.)Correct
Incorrect
Hint
http://smallbusiness.chron.com/advantages-disadvantages-using-private-ip-address-space-46424.html -
Question 164 of 417
164. Question
How many bits represent network id in a IPv6 address?Correct
Incorrect
Hint
http://networkengineering.stackexchange.com/questions/30836/calculate-networking-bits-for-ipv6 64 bits for Nwtwork ID and 64 bits for Interface ID 64+64=128 -
Question 165 of 417
165. Question
?????(An image on exhibit) An interface which we have to determine from the routing the route learned by which routing protocol?Correct
Incorrect
-
Question 166 of 417
166. Question
Which WAN topology is most appropriate for a centrally located server farm with several satellite branches?Correct
Incorrect
Hint
In a Hub-and-spoke Site-to-Site Wide Area Network (WAN) network topology, one physical site act as Hub (Example, Main Office), while other physical sites act as spokes. Spoke sites are connected to each other via Hub site. In Hub-and-spoke Wide Area Network (WAN) topology, the network communication between two spokes always travels through the hub. -
Question 167 of 417
167. Question
Which function allows EIGRP peers to receive notice of implementing topology changes?Correct
Incorrect
-
Question 168 of 417
168. Question
If you configure syslog messages without specifying the logging trap level, which log messages will the router send?Correct
Incorrect
-
Question 169 of 417
169. Question
Which three options are benefits of using TACACS+ on a device? (Choose three)Correct
Incorrect
Hint
http://tacacs.net/docs/TACACS_Advantages.pdf -
Question 170 of 417
170. Question
What layer of the OSI Model is included in TCP/IP Model’s INTERNET layer?Correct
Incorrect
-
Question 171 of 417
171. Question
Which two of these are characteristics of the 802.1Q protocol? (Choose two.)Correct
Incorrect
-
Question 172 of 417
172. Question
Which two features can dynamically assign IPv6 addresses? (Choose two.)Correct
Incorrect
Hint
rfc4862 in which wrote: Appendix C. Changes since RFC 2462 Major changes that can affect existing implementations: o Avoided the wording of “stateful configuration”, which is known to be quite confusing, and simply used “DHCPv6” wherever appropriate. In Obsolete RFC 2462: IPv6 defines both a stateful and stateless address autoconfiguration mechanism. … In the stateful autoconfiguration model, hosts obtain interface addresses and/or configuration information and parameters from a server. -
Question 173 of 417
173. Question
A security administrator wants to profile endpoints and gain visibility into attempted authentications. Which 802.1x mode allows these actions?Correct
Incorrect
-
Question 174 of 417
174. Question
How to verify strong and secured SSH connection?Correct
Incorrect
-
Question 175 of 417
175. Question
How many usable host are there per subnet if you have the address of 192.168.10.0 with a subnet mask of 255.255.255.240?Correct
Incorrect
-
Question 176 of 417
176. Question
What interconnection cable can you use when you use a MDI connection?Correct
Incorrect
-
Question 177 of 417
177. Question
Which cisco platform can verify ACLs?Correct
Incorrect
-
Question 178 of 417
178. Question
In order to comply with new auditing standards, a security administrator must be able to correlate system security alert logs directly with the employee who triggers the alert. Which of the following should the security administrator implement in order to meet this requirement?Correct
Incorrect
-
Question 179 of 417
179. Question
When you deploy multilink PPP on your network, where must you configure the group IP Address on each device?Correct
Incorrect
-
Question 180 of 417
180. Question
If you want multiple hosts on a network, where do you configure the setting?Correct
Incorrect
-
Question 181 of 417
181. Question
Which option is the benefit of implementing an intelligent DNS for a cloud computing solution?Correct
Incorrect
-
Question 182 of 417
182. Question
Which statement about the IP SLAs ICMP Echo operation is true?Correct
Incorrect
-
Question 183 of 417
183. Question
Which action can change the order of entries in a named access-list?Correct
Incorrect
-
Question 184 of 417
184. Question
How does a router handle an incoming packet whose destination network is missing from the routing table?Correct
Incorrect
Hint
Change from “it discards the packet” to “it routes the packet to the default route” because there is new question Which definition of default route is true? with answer “A route used when a destination route is missing.” -
Question 185 of 417
185. Question
Which two components are used to identify a neighbor in a BGP configuration? (Choose two.)Correct
Incorrect
-
Question 186 of 417
186. Question
Which three statements about HSRP operation are true? (Choose three.)?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/ip/hot-standby-router-protocol-hsrp/10583-62.html#topic5 “The active router sources hello packets from its configured IP address and the HSRP virtual MAC address. The standby router sources hellos from its configured IP address and the burned-in MAC address (BIA).” http://www.cisco.com/c/en/us/support/docs/ip/hot-standby-router-protocol-hsrp/10583-62.html#topic14 “By default, these timers are set to 3 and 10 seconds, respectively…” http://www.cisco.com/c/en/us/support/docs/switches/catalyst-6000-series-switches/29545-168.html#q1 Load Sharing with HSRP http://www.cisco.com/c/en/us/support/docs/ip/hot-standby-router-protocol-hsrp/13781-7.html#conf “…has a 256 unique HSRP group ID limit.” “…the allowed group ID range (0-255). … MSFC2A (Supervisor Engine 32) can use any number of group IDs from that range. -
Question 187 of 417
187. Question
Which two options describe benefits of aggregated chassis technology (choose 2)?Correct
Incorrect
-
Question 188 of 417
188. Question
How to trouble DNS issue ( choose two)?Correct
Incorrect
Hint
http://www.cisco.com/en/US/docs/internetworking/troubleshooting/guide/tr1907.html#wp1021264 Ping the destination by name perform a DNS lookup on the destination -
Question 189 of 417
189. Question
Which utility can you use to identify redundant or shadow rules?Correct
Incorrect
-
Question 190 of 417
190. Question
What does traffic shaping do to reduce congestion in a network?Correct
Incorrect
-
Question 191 of 417
191. Question
Which 2 statements about extended traceroute command is true? (choose two)Correct
Incorrect
Hint
Source address: The interface or IP address of the router to use as a source address for the probes. The router normally picks the IP address of the outbound interface to use. Minimum Time to Live [1]: The TTL value for the first probes. The default is 1, but it can be set to a higher value to suppress the display of known hops. Maximum Time to Live [30]: The largest TTL value that can be used. The default is 30. The traceroute command terminates when the destination is reached or when this value is reached. -
Question 192 of 417
192. Question
Which command can you enter to determine the addresses that have been assigned on a DHCP Server?Correct
Incorrect
Hint
http://www.aubrett.com/InformationTechnology/RoutingandSwitching/Cisco/CiscoRouters/ DHCPBindings.aspx “Router#show ip dhcp binding Bindings from all pools not associated with VRF: IP address Client-ID/ Lease expiration Type 10.16.173.0 24d9.2141.0ddd Jan 12 2013 03:42 AM Automatic” -
Question 193 of 417
193. Question
Which statement about SNMPv2 is true?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/ios/12_2/configfun/configuration/guide/ffun_c/fcf014.html#wp1010901 “Model___Level_________Authentication_____Encryption__What Happens v2c_____noAuthNoPriv___Community String__No________Uses a community string match for authentication.” So B & D must be wrong, because there is no “password” in SNMPv2. A is wrong because there is no encryption in SNMPv2. -
Question 194 of 417
194. Question
Which symptom most commonly indicates that 2 connecting interface are configured with a duplex mismatch?Correct
Incorrect
-
Question 195 of 417
195. Question
Which VTP mode can not make a change to vlan?Correct
Incorrect
Hint
VTP Client · VTP clients function the same way as VTP servers, but you cannot create, change, or delete VLANs on a VTP client. · A VTP client only stores the VLAN information for the entire domain while the switch is on. · A switch reset deletes the VLAN information. · You must configure VTP client mode on a switch. -
Question 196 of 417
196. Question
Which function does IP SLA ICMP ECHO operation perform to assist with troubleshooting?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/ios xml/ios/ipsla/configuration/15-mt/sla-15-mt-book/sla_icmp_pathjitter.html -
Question 197 of 417
197. Question
Which mode are in PAgP? (choose two)Correct
Incorrect
Hint
http://www.omnisecu.com/cisco-certified-network-associate-ccna/etherchannel-pagp-and-lacp-modes.php -
Question 198 of 417
198. Question
In an Ethernet network, under what two scenarios can devices transmit? (Choose two.)Correct
Incorrect
-
Question 199 of 417
199. Question
Which two protocols are used by bridges and/or switches to prevent loops in a layer 2 network? (Choose two.)Correct
Incorrect
-
Question 200 of 417
200. Question
At which layer of the OSI model does PPP perform?Correct
Incorrect
-
Question 201 of 417
201. Question
What are three reasons that an organization with multiple branch offices and roaming users might implement a Cisco VPN solution instead of point-to-point WAN links?(Choose three.)Correct
Incorrect
-
Question 202 of 417
202. Question
Which IPv6 header field is equivalent to the TTL?Correct
Incorrect
Hint
Time To Live (TTL)/Hop Limit (8 bits) http://ipv6.com/articles/general/IPv6-Header.htm -
Question 203 of 417
203. Question
which port security mode can assist with troubleshooting by keeping count of violations?Correct
Incorrect
-
Question 204 of 417
204. Question
which 2 optns are requirements for configuring ripv2 for ipv4 (choose 2 )?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/ios/12_2/ip/configuration/guide/fipr_c/1cfrip.html#wp1000889 “Enabling RIP (Required) Allowing Unicast Updates for RIP (Required)” RIP Version 1 and Version 2 have the same basic requirements! -
Question 205 of 417
205. Question
which configuration command can u apply to a hsrp router so that its local interface becomes active if all other routers in the group fail?Correct
Incorrect
-
Question 206 of 417
206. Question
which 2 statement about EIGRP on IPv6 device is true?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/ip/enhanced-interior-gateway-routing-protocol-eigrp/113267-eigrp-ipv6-00.html -
Question 207 of 417
207. Question
which command can you enter to troubleshoot the failure of address assignment?Correct
Incorrect
-
Question 208 of 417
208. Question
which three technical services support cloud computing?Correct
Incorrect
-
Question 209 of 417
209. Question
which two steps must you perform to enbale router- on- stick on a switch?Correct
Incorrect
-
Question 210 of 417
210. Question
which add prefix does OSPFv3 use when multiple IPv6 address are configured on a single interface?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/iproute_ospf/configuration/15-sy/iro-15-sy-book/ip6-routeospfv3.html#GUID-05F3F09C-FE3E-41D6-9845-111FB17AD030 “In IPv6, you can configure many address prefixes on an interface. In OSPFv3, all address prefixes on an interface are included by default. You cannot select some address prefixes to be imported into OSPFv3; either all address prefixes on an interface are imported, or no address prefixes on an interface are imported.” -
Question 211 of 417
211. Question
which IP configuration does the CIDR notation 192.168.1.1/25 refer?Correct
Incorrect
-
Question 212 of 417
212. Question
CIDR notation (255.255.255.252 ) / notation?Correct
Incorrect
-
Question 213 of 417
213. Question
Which two of these statements regarding RSTP are correct? (Choose two)Correct
Incorrect
-
Question 214 of 417
214. Question
What is known as ―one-to-nearest addressing in IPv6?Correct
Incorrect
-
Question 215 of 417
215. Question
When a device learns multiple routes to a specific network, it installs the route with :Correct
Incorrect
Hint
http://www.ciscopress.com/articles/article.asp?p=2180208&seqNum=9 -
Question 216 of 417
216. Question
Requirement to configure DHCP binding ( 2 options)Correct
Incorrect
-
Question 217 of 417
217. Question
how to see dhcp conflict?Correct
Incorrect
Hint

-
Question 218 of 417
218. Question
What type of MAC address is aged automatically by the switch?Correct
Incorrect
-
Question 219 of 417
219. Question
Which major component of the network virtualization architecture isolate users according to policy?Correct
Incorrect
Hint
Network access control and segmentation of classesof users: Users are authenticated and either allowed or denied into a logical partition. Users are segmented into employees, contractors and consultants, and guests, with respective access to IT assets. This component identifies users who are authorized toaccess the network and then places them into the appropriate logical partition. -
Question 220 of 417
220. Question
Which two statements about firewalls are true?Correct
Incorrect
-
Question 221 of 417
221. Question
Which two statements about data VLANs on access ports are true? ( Choose two)Correct
Incorrect
-
Question 222 of 417
222. Question
Where does the configuration reside when a helper address is configured to support DHCP?Correct
Incorrect
-
Question 223 of 417
223. Question
Which command can you enter to configure an IPV6 floating static route?Correct
Incorrect
-
Question 224 of 417
224. Question
How does NAT overloading provide one-to-many address translation?Correct
Incorrect
-
Question 225 of 417
225. Question
Which three options are types of Layer 2 network attack? (Choose three)Correct
Incorrect
-
Question 226 of 417
226. Question
What does split-horizon do?Correct
Incorrect
-
Question 227 of 417
227. Question
Refer to the exhibit.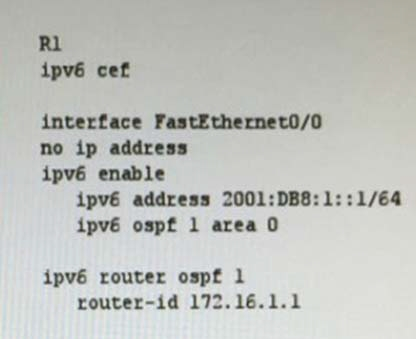 After you apply the given configuration to R1, you notice that it failed to enable OSPF Which action can you take to correct the problem? Correct
After you apply the given configuration to R1, you notice that it failed to enable OSPF Which action can you take to correct the problem? Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/iproute_ospf/configuration/15-sy/iro-15-sy-book/ip6-route-ospfv3.html Prerequisites for IPv6 Routing: OSPFv3 Complete the OSPFv3 network strategy and planning for your IPv6 network. For example, you must decide whether multiple areas are required. Enable IPv6 unicast routing. Enable IPv6 on the interface. -
Question 228 of 417
228. Question
How many broadcast domains are shown in the graphic assuming only the default VLAN is confgured on the switches? Correct
Correct
Incorrect
-
Question 229 of 417
229. Question
Which three statements correcctly describe Network Device A? (Choose three.)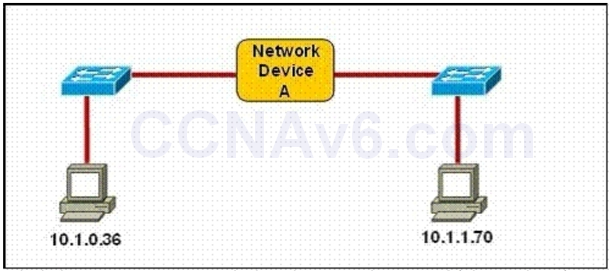 Correct
Correct
Incorrect
-
Question 230 of 417
230. Question
At the end of an RSTP election process, which access layer switch port will assume the discarding role?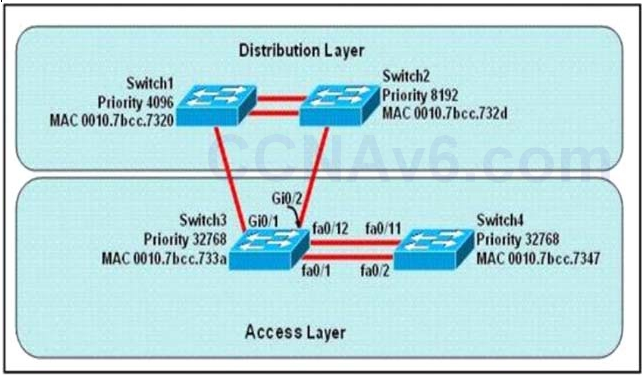 Correct
Correct
Incorrect
Hint
In this question, we only care about the Access Layer switches (Switch3 & 4). Switch 3 has a lower bridge ID than Switch 4 (because the MAC of Switch3 is smaller than that of Switch4) so both ports of Switch3 will be in forwarding state. The alternative port will surely belong to Switch4. Switch4 will need to block one of its ports to avoid a bridging loop between the two switches. But how does Switch4 select its blocked port? Well, the answer is based on the BPDUs it receives from Switch3. A BPDU is superior to another if it has: 1. A lower Root Bridge ID 2. A lower path cost to the Root 3. A lower Sending Bridge ID 4. A lower Sending Port ID These four parameters are examined in order. In this specific case, all the BPDUs sent by Switch3 have the same Root Bridge ID, the same path cost to the Root and the same Sending Bridge ID. The only parameter left to select the best one is the Sending Port ID (Port ID = port priority + port index). In this case the port priorities are equal because they use the default value, so Switch4 will compare port index values, which are unique to each port on the switch, and because Fa0/12 is inferior to Fa0/1, Switch4 will select the port connected with Fa0/1 (of Switch3) as its root port and block the other port -> Port fa0/11 of Switch4 will be blocked (discarding role). -
Question 231 of 417
231. Question
Why is flash memory erased prior to upgrading the IOS image from the TFTP server?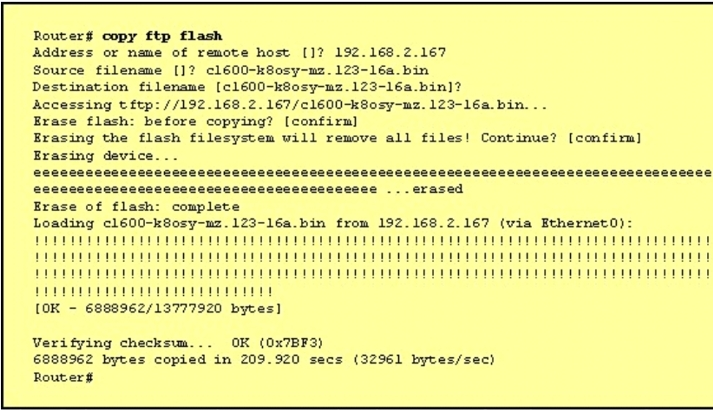 Correct
Correct
Incorrect
-
Question 232 of 417
232. Question
The network shown in the diagram is experiencing connectivity problems. Which of the following will correct the problems? (Choose two.)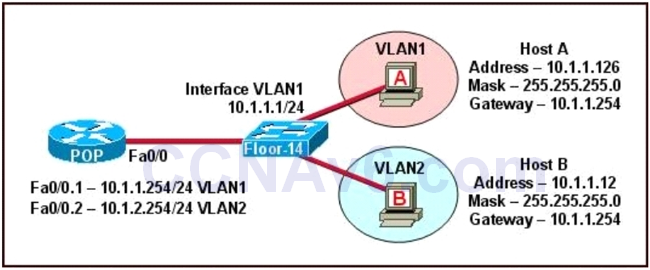 Correct
Correct
Incorrect
-
Question 233 of 417
233. Question
Which utility can you use to identify the cause of a traffic-flow blockage between the two devices in a network?Correct
Incorrect
Hint
Previously was path analysis, but I think its ACL analysis -
Question 234 of 417
234. Question
Which IEEE mechanism is responsible for the authentication of devices when they attempt to connect to a local network?Correct
Incorrect
Hint
IEEE 802.1X is an IEEE Standard for port-based Network Access Control (PNAC). It is part of the IEEE 802.1 group of networking protocols. It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN -
Question 235 of 417
235. Question
When a router is unable to find a known route in the routing table, how does it handle the packet?Correct
Incorrect
-
Question 236 of 417
236. Question
If router R1 knows a static route to a destination network and then learns about the same destination network through a dynamic routing protocol, how does R1 respond?Correct
Incorrect
Hint
By default the administrative distance of a static route is 1, meaning it will be preferred over all dynamic routing protocols. If you want to have the dynamic routing protocol used and have the static route be used only as a backup, you need to increase the AD of the static route so that it is higher than the dynamic routing protocol. -
Question 237 of 417
237. Question
Which two statements about floating static routes are true? (Choose two)Correct
Incorrect
-
Question 238 of 417
238. Question
Refer to the exhibit. If R1 receives a packet destined to 172.16.1.1, to which IP address does it send the packet?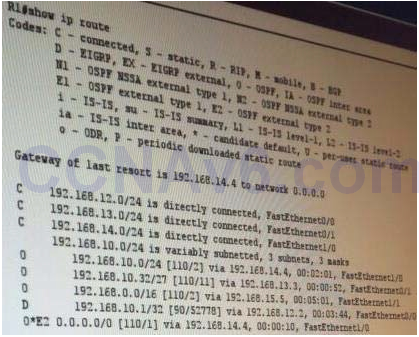 Correct
Correct
Incorrect
Hint
It can’t find the address 172.16.1.1 so it will be directed to the Gate of last resort 192.168.14.4 -
Question 239 of 417
239. Question
What is the danger of the permit any entry in a NAT access list?Correct
Incorrect
-
Question 240 of 417
240. Question
How does a DHCP server dynamically assign IP addresses to hosts?Correct
Incorrect
Hint
The DHCP lifecycle consists of the following: Release: The client may decide at any time that it no longer wishes to use the IP address it was assigned, and may terminate the lease, releasing the IP address. -
Question 241 of 417
241. Question
Refer to the exhibit. What two results would occur if the hub were to be replaced with a switch that is configured with one Ethernet VLAN? (Choose two.)Correct
Incorrect
-
Question 242 of 417
242. Question
Refer to the exhibit, you determine that Computer A cannot ping Computer Which reason for the problem is most likely true?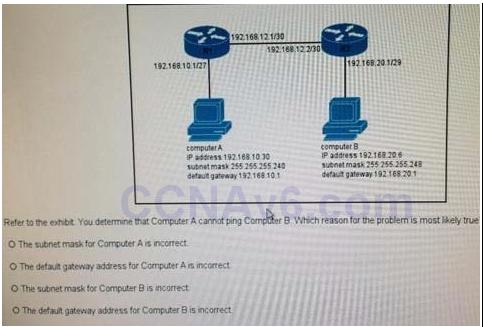 Correct
Correct
Incorrect
Hint
255.255.255.224 = /27 -
Question 243 of 417
243. Question
Which effect of the passive-interface command on R1 is true?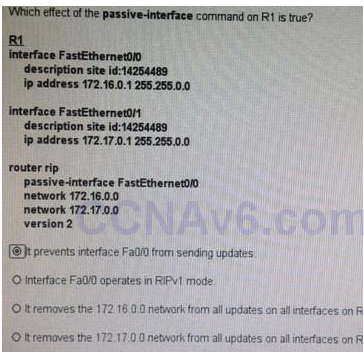 Correct
Correct
Incorrect
Hint
With most routing protocols, the passive-interface command restricts outgoing advertisements only. But, when used with Enhanced Interior Gateway Routing Protocol (EIGRP), the effect is slightly different. -
Question 244 of 417
244. Question
Which three encapsulation layers in the OSI model are combined into the TCP/IP application layer? (Choose three)Correct
Incorrect
Hint

-
Question 245 of 417
245. Question
When is the most appropriate time to escalate an issue that you troubleshooting?Correct
Incorrect
-
Question 246 of 417
246. Question
Which two command can you enter to display the current time sources statistics on devices? (Choose TWO)Correct
Incorrect
Hint
https://ccnav6.com/wp-content/uploads/2018/02/2018-02-08_104204.png -
Question 247 of 417
247. Question
When you enable PortFast on a switch port, the port immediately transitions to which state?Correct
Incorrect
Hint
PortFast causes a switch or trunk port to enter the spanning tree forwarding state immediately, bypassing the listening and learning states. You can use PortFast on switch or trunk ports that are connected to a single workstation, switch, or server to allow those devices to connect to the network immediately, instead of waiting for the port to transition from the listening and learning states to the forwarding state. -
Question 248 of 417
248. Question
Which path does a router choose when it receives a packet with multiple possible paths to the destination over different routing protocols?Correct
Incorrect
-
Question 249 of 417
249. Question
Which command is used to know the duplex speed of serial link?Correct
Incorrect
-
Question 250 of 417
250. Question
What command is used to configure a switch as authoritative NTP server?Correct
Incorrect
-
Question 251 of 417
251. Question
Which address class includes network 191.168.0.1/27?Correct
Incorrect
-
Question 252 of 417
252. Question
On which type of port can switches interconnect for multi-VLAN communication?Correct
Incorrect
-
Question 253 of 417
253. Question
Refer to the exhibit. If R1 sends traffic to 192.168.101.45 the traffic is sent through which interface?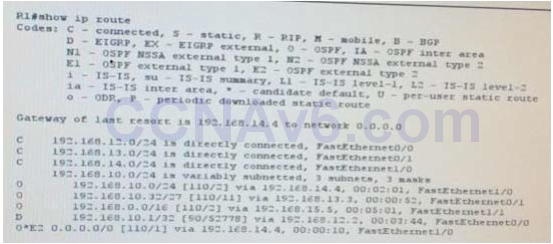 Correct
Correct
Incorrect
-
Question 254 of 417
254. Question
Which IPV6 function serves the same purpose as ARP entry verification on an IPv4 network?Correct
Incorrect
-
Question 255 of 417
255. Question
Which HSRP feature was new in HSRPv2?Correct
Incorrect
-
Question 256 of 417
256. Question
Refer to exhibit. Which command can you enter to verify link speed and duplex setting on the interface?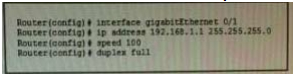 Correct
Correct
Incorrect
-
Question 257 of 417
257. Question
Which two statements about unique local IPv6 addresses are true?Correct
Incorrect
-
Question 258 of 417
258. Question
Which DTP switch port mode allows the port to create a trunk link if the neighboring port is in trunk mode, dynamic desirable mode, or desirable auto mode?Correct
Incorrect
Hint
http://bradhedlund.com/2007/11/27/switchport-configurations-explained/ -
Question 259 of 417
259. Question
When you troubleshoot an IPv4 connectivity issue on a router, which three router configuration checks you must perform?Correct
Incorrect
-
Question 260 of 417
260. Question
Configuration of which option is required on a Cisco switch for the Cisco IP phone to work?Correct
Incorrect
Hint
Configure the Switch Port to Carry Both Voice and Data TrafficWhen you connect an IP phone to a switch using a trunk link, it can cause high CPU utilization in the switches. As all the VLANs for a particular interface are trunked to the phone, it increases the number of STP instances the switch has to manage. This increases the CPU utilization. Trunking also causes unnecessary broadcast / multicast / unknown unicast traffic to hit the phone link. In order to avoid this, remove the trunk configuration and keep the voice and access VLAN configured along with Quality of Service (QoS). Technically, it is still a trunk, but it is called a Multi-VLAN Access Port (MVAP). Because voice and data traffic can travel through the same port, you should specify a different VLAN for each type of traffic. You can configure a switch port to forward voice and data traffic on different VLANs. Configure IP phone ports with a voice VLAN configuration. This configuration creates a pseudo trunk, but does not require you to manually prune the unnecessary VLANs. The voice VLAN feature enables access ports to carry IP voice traffic from an IP phone. The voice VLAN feature is disabled by default. The Port Fast feature is automatically enabled when voice VLAN is configured. When you disable voice VLAN, the Port Fast feature is not automatically disabled -
Question 261 of 417
261. Question
Which method does a connected trunk port use to tag VLAN traffic?Correct
Incorrect
-
Question 262 of 417
262. Question
Which RFC was created to alleviate the depletion of IPv4 public addresses?Correct
Incorrect
-
Question 263 of 417
263. Question
What is the default lease time for a DHCP binding?Correct
Incorrect
Hint
By default, each IP address assigned by a DHCP Server comes with a one- day lease, which is the amount of time that the address is valid. To change the lease value for an IP address, use the following command in DHCP pool configuration mode: -
Question 264 of 417
264. Question
Which NAT type is used to translate a single inside address to a single outside address?Correct
Incorrect
Hint
Network address translation (NAT) is the process of modifying IP address information in IP packet headers while in transit across a traffic routing device. There are two different types of NAT: NAT PAT -
Question 265 of 417
265. Question
Which network topology allows all traffic to flow through a central hub?Correct
Incorrect
-
Question 266 of 417
266. Question
Which statement about a router on a stick is true?Correct
Incorrect
Hint
https://www.freeccnaworkbook.com/workbooks/ccna/configuring-inter-vlan-routing-router-on-a-stick -
Question 267 of 417
267. Question
By default, how many MAC addresses are permitted to be learned on a switch port with port security enabled?Correct
Incorrect
-
Question 268 of 417
268. Question
Which device allows users to connect to the network using a single or double radio?Correct
Incorrect
-
Question 269 of 417
269. Question
When enabled, which feature prevents routing protocols from sending hello messages on an interface?Correct
Incorrect
Hint
You can use the passive-interface command in order to control the advertisement of routing information. The command enables the suppression of routing updates over some interfaces while it allows updates to be exchanged normally over other interfaces. With most routing protocols, the passive-interface command restricts outgoing advertisements only. But, when used with Enhanced Interior Gateway Routing Protocol (EIGRP), the effect is slightly different. This document demonstrates that use of the passive-interface command in EIGRP suppresses the exchange of hello packets between two routers, which results in the loss of their neighbor relationship. This stops not only routing updates from being advertised, but it also suppresses incoming routing updates. This document also discusses the configuration required in order to allow the suppression of outgoing routing updates, while it also allows incoming routing updates to be learned normally from the neighbor -
Question 270 of 417
270. Question
Refer to the exhibit. Which statement describes the effect of this configuration?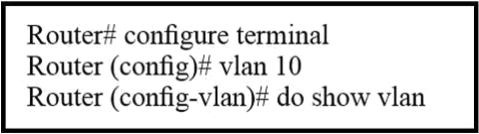 Correct
Correct
Incorrect
-
Question 271 of 417
271. Question
Which route source code represents the routing protocol with a default administrative distance of 90 in the routing table?Correct
Incorrect
Hint
Default Administrative distance of EIGRP protocol is 90 then answer is C. -
Question 272 of 417
272. Question
Which statement about native VLAN traffic is true?Correct
Incorrect
-
Question 273 of 417
273. Question
Which statement about unicast frame forwarding on a switch is true?Correct
Incorrect
-
Question 274 of 417
274. Question
Which component of the routing table ranks routing protocols according to their preferences?Correct
Incorrect
Hint
Administrative distance – This is the measure of trustworthiness of the source of the route. If a router learns about a destination from more than one routing protocol, administrative distance is compared and the preference is given to the routes with lower administrative distance. In other words, it is the believability of the source of the route -
Question 275 of 417
275. Question
Which switch would STP choose to become the root bridge in the selection process?Correct
Incorrect
-
Question 276 of 417
276. Question
Refer to the graphic. R1 is unable to establish an OSPF neighbor relationship with R3. What are possible reasons for this problem? (Choose two.)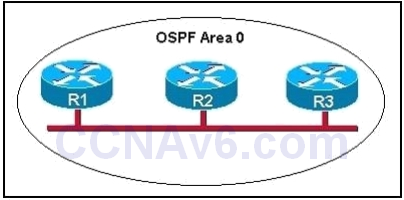 Correct
Correct
Incorrect
-
Question 277 of 417
277. Question
For what two purposes does the Ethernet protocol use physical addresses? (Choose two.)Correct
Incorrect
-
Question 278 of 417
278. Question
2 authentication type of MLPPPCorrect
Incorrect
-
Question 279 of 417
279. Question
What is the effect of the overload keyword in a static NAT translation configuration?Correct
Incorrect
Hint
http://www.firewall.cx/networking-topics/network-address-translation-nat/233-nat-overload-part-1.html -
Question 280 of 417
280. Question
What are the requirements for running VTP (choose two)Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3560/software/release/12-2_52_se/configuration/guide/3560scg/swvtp.html ” Follow these guidelines when deciding which VTP version to implement: •All switches in a VTP domain must have the same domain name, but they do not need to run the same VTP version. •A VTP version 2-capable switch can operate in the same VTP domain as a switch running VTP version 1 if version 2 is disabled on the version 2-capable switch (version 2 is disabled by default). “ -
Question 281 of 417
281. Question
What is the use of IPv4 private space (choose two)Correct
Incorrect
-
Question 282 of 417
282. Question
Assuming a subnet mask of 255.255.248.0, three of the following addresses are valid host addresses. Which are these addresses? (Choose three.)Correct
Incorrect
-
Question 283 of 417
283. Question
Which type does a port become when it receives the best BPDU on a bridge?Correct
Incorrect
-
Question 284 of 417
284. Question
Which value can you modify to configure a specific interface as the preferred forwarding interface?Correct
Incorrect
-
Question 285 of 417
285. Question
Which statement about VLAN configuration is true?Correct
Incorrect
-
Question 286 of 417
286. Question
Refer to the exhibit. Which switch provides the spanning-tree designated port role for the network segment that services the printers?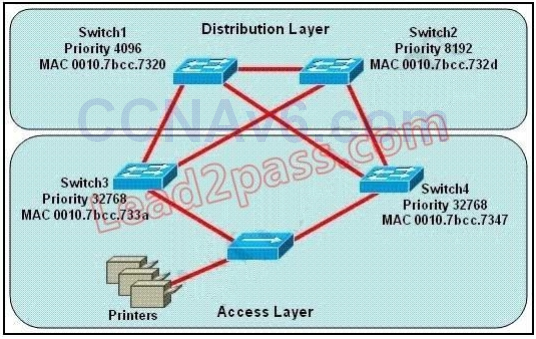 Correct
Correct
Incorrect
-
Question 287 of 417
287. Question
In which two situations should you use out-of-band management?Correct
Incorrect
-
Question 288 of 417
288. Question
Which command can you enter to configure a local username with an encrypted password and EXEC mode user privileges?Correct
Incorrect
-
Question 289 of 417
289. Question
What happens when an 802.11a node broadcasts within the range of an 802.11g access point?Correct
Incorrect
-
Question 290 of 417
290. Question
Which value is indicated by the next hop in a routing table?Correct
Incorrect
-
Question 291 of 417
291. Question
Which statement about the inside interface configuration in a NAT deployment is true?Correct
Incorrect
-
Question 292 of 417
292. Question
Which option is the default switch port port-security violation mode?Correct
Incorrect
-
Question 293 of 417
293. Question
Which entity assigns IPv6 addresses to end users?Correct
Incorrect
-
Question 294 of 417
294. Question
which value indicate the distance from the ntp authoritative time source?Correct
Incorrect
-
Question 295 of 417
295. Question
Which NTP type designates a router without an external reference clock as an authoritative time source?Correct
Incorrect
-
Question 296 of 417
296. Question
Which 3 feature are represented by A letter in AAA? (Choose Three)Correct
Incorrect
-
Question 297 of 417
297. Question
Which of the following are the valid numbers of standard ACL (choosse 2)Correct
Incorrect
-
Question 298 of 417
298. Question
When you deploy multilink PPP on your network, where must you configure the group IP Address on each device?Correct
Incorrect
-
Question 299 of 417
299. Question
What are two statement for SSH?Correct
Incorrect
-
Question 300 of 417
300. Question
If a route is not present in the routing table for a particular destination, what would the router do?Correct
Incorrect
-
Question 301 of 417
301. Question
Host is able to ping a web server but it is not able to do HTTP request.Correct
Incorrect
-
Question 302 of 417
302. Question
Which NTP command configures the local devices as an NTP reference clock source?Correct
Incorrect
-
Question 303 of 417
303. Question
Which item represents the standard IP ACL?Correct
Incorrect
-
Question 304 of 417
304. Question
Which item represents the standard IP ACL?Correct
Incorrect
-
Question 305 of 417
305. Question
Which command can you enter to verify that a 128-bit address is live and responding?Correct
Incorrect
-
Question 306 of 417
306. Question
Where information about untrusted hosts are stored?Correct
Incorrect
Hint
Builds and maintains the DHCP snooping binding database, which contains information about untrusted hosts with leased IP addresses. -
Question 307 of 417
307. Question
What is one benefit of PVST+?Correct
Incorrect
Hint
The PVST+ provides Layer 2 load-balancing for the VLAN on which it runs. You can create different logical topologies by using the VLANs on your network to ensure that all of your links are used but that no one link is oversubscribed. Each instance of PVST+ on a VLAN has a single root switch. This root switch propagates the spanning-tree information associated with that VLAN to all other switches in the network. Because each switch has the same information about the network, this process ensures that the network topology is maintained and optimized per VLAN. -
Question 308 of 417
308. Question
Which statement about VLAN operation on Cisco Catalyst switches is true?Correct
Incorrect
Hint
Each VLAN resides in its own broadcast domain, so incoming frames with unknown destinations are only transmitted to ports that reside in the same VLAN as the incoming frame. -
Question 309 of 417
309. Question
Three switches are connected to one another via trunk ports. Assuming the default switch configuration, which switch is elected as the root bridge for the spanning-tree instance of VLAN 1?Correct
Incorrect
Hint
Each switch in your network will have a Bridge ID Priority value, more commonly referred to as a BID. This BID is a combination of a default priority value and the switch’s MAC address, with the priority value listed first. The lowest BID will win the election process. For example, if a Cisco switch has the default priority value of 32,768 and a MAC address of 11-22-33- 44-55-66, the BID would be 32768:11-22-33-44-55-66. Therefore, if the switch priority is left at the default, the MAC address is the deciding factor in the root bridge election. -
Question 310 of 417
310. Question
Which two options are primary responsibilities of the APlC-EM controller? (Choose two.)Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/products/cloud-systems-management/application-policy-infrastructure-controller-enterprise-module/index.html Automate network configuration and setup Deploy network devices faster Automate device deployment and provisioning across the enterprise. Provide a programmable network Enable developers to create new applications that use the network to fuel business growth. -
Question 311 of 417
311. Question
Which command can be used from a PC to verify the connectivity between hosts that connect through a switch in the same LAN?Correct
Incorrect
Hint
ICMP pings are used to verify connectivity between two IP hosts. Traceroute is used to verify the router hop path traffic will take but in this case since the hosts are in the same LAN there will be no router hops involved. -
Question 312 of 417
312. Question
Refer to the exhibit. Which two statements are true about interVLAN routing in the topology that is shown in the exhibit? (Choose two.)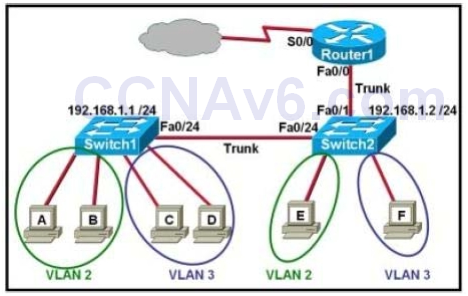 Correct
Correct
Incorrect
Hint
In order for multiple VLANs to connect to a single physical interface on a Cisco router, subinterfaces must be used, one for each VLAN. This is known as the router on a stick configuration. Also, for any trunk to be formed, both ends of the trunk must agree on the encapsulation type, so each one must be configured for 802.1q or ISL. -
Question 313 of 417
313. Question
What value is primarily used to determine which port becomes the root port on each nonroot switch in a spanning-tree topology?Correct
Incorrect
Hint
The path cost to the root bridge is the most important value to determine which port will become the root port on each non-root switch. In particular, the port with lowest cost to the root bridge will become root port (on non-root switch). -
Question 314 of 417
314. Question
Refer to the exhibit. lf RTRO1 as configured as shown, which three addresses will be received by other routers that are running ElGRP on the network? (Choose three.)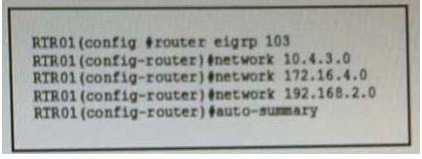 Correct
Correct
Incorrect
-
Question 315 of 417
315. Question
Which two statements about TACACS+ are true? (Choose two.)Correct
Incorrect
Hint
http://tacacs.net/docs/TACACS_Advantages.pdf Many IT departments choose to use AAA (Authentication, Authorization and Accounting) protocols RADIUS or TACACS+ to address these issues. http://www.cisco.com/c/en/us/support/docs/security-vpn/terminal-access-controller-access-control-system-tacacs-/13865-tacplus.pdf This document describes how to configure a Cisco router for authentication with the TACACS+ that runs on UNIX. TACACS+ does not offer as many features as the commercially available Cisco Secure ACS for Windows or Cisco Secure ACS UNIX. TACACS+ software previously provided by Cisco Systems has been discontinued and is no longer supported by Cisco Systems. -
Question 316 of 417
316. Question
Which command enables RSTP on a switch?Correct
Incorrect
Hint
Rapid Spanning Tree Protocol (RSTP) is an enhancement of the original STP 802.1D protocol. The RSTP 802.1w protocol is an IEEE open implementation. Cisco has its own proprietary implementation of RSTP, that includes the benefits of its Per-VLAN spanning tree protocols, called Rapid-PVST+. To activate the Rapid-PVST+ protocol: switch(config)#spanning-tree mode rapid-pvst -
Question 317 of 417
317. Question
A switch is configured with all ports assigned to VLAN 2 with full duplex FastEthernet to segment existing departmental traffic. What is the effect of adding switch ports to a new VLAN on the switch?Correct
Incorrect
-
Question 318 of 417
318. Question
VLAN 3 is not yet configured on your switch. What happens if you set the switchport access vlan 3 command in interface configuration mode?Correct
Incorrect
Hint
The “switchport access vlan 3″will put that interface as belonging to VLAN 3 while also updated the VLAN database automatically to include VLAN 3. -
Question 319 of 417
319. Question
Cisco Catalyst switches CAT1 and CAT2 have a connection between them using ports FA0/13. An 802.1Q trunk is configured between the two switches. On CAT1, VLAN 10 is chosen as native, but on CAT2 the native VLAN is not specified. What will happen in this scenario?Correct
Incorrect
Hint
A “native VLAN mismatch” error will appear by CDP if there is a native VLAN mismatch on an 802.1Q link. “VLAN mismatch” can cause traffic from one vlan to leak into another vlan. -
Question 320 of 417
320. Question
Refer to the exhibit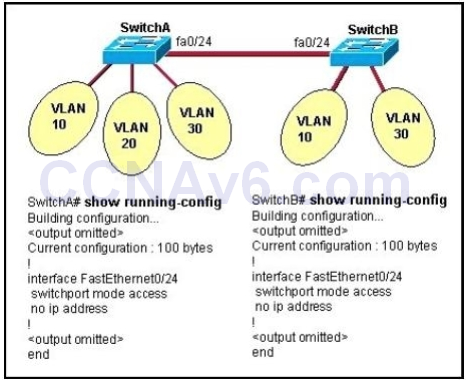 All switch ports are assigned to the correct VLANs, but none of the hosts connected to SwitchA can communicate with hosts in the same VLAN connected to SwitchB. Based on the output shown, what is the most likely problem? Correct
All switch ports are assigned to the correct VLANs, but none of the hosts connected to SwitchA can communicate with hosts in the same VLAN connected to SwitchB. Based on the output shown, what is the most likely problem? Correct
Incorrect
Hint
In order to pass traffic from VLANs on different switches, the connections between the switches must be configured as trunk ports. -
Question 321 of 417
321. Question
What is the function of the command switchport trunk native vlan 999 on a Cisco Catalyst switch?Correct
Incorrect
Hint
Configuring the Native VLAN for Untagged Traffic A trunk port configured with 802.1Q tagging can receive both tagged and untagged traffic. By default, the switch forwards untagged traffic in the native VLAN configured for the port. The native VLAN is VLAN 1 by default. -
Question 322 of 417
322. Question
Which parameter or parameters are used to calculate OSPF cost in Cisco routers?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/ip/open-shortest-path-first-ospf/7039-1.html#t6 OSPF Cost The cost (also called metric) of an interface in OSPF is an indication of the overhead required to send packets across a certain interface. The cost of an interface is inversely proportional to the bandwidth of that interface. A higher bandwidth indicates a lower cost. There is more overhead (higher cost) and time delays involved in crossing a 56k serial line than crossing a 10M ethernet line. The formula used to calculate the cost is: cost= 10000 0000/bandwith in bps For example, it will cost 10 EXP8/10 EXP7 = 10 to cross a 10M Ethernet line and will cost 10 EXP8/1544000 = 64 to cross a T1 line. By default, the cost of an interface is calculated based on the bandwidth; you can force the cost of an interface with the ip ospf costinterface subconfiguration mode command. -
Question 323 of 417
323. Question
Which command shows your active Telnet connections?Correct
Incorrect
Hint
The “show users” shows telnet/ssh connections to your router while “show sessions” shows telnet/ssh connections from your router (to other devices). The question asks about “your active Telnet connections”, meaning connections from your router -
Question 324 of 417
324. Question
Refer to the exhibit.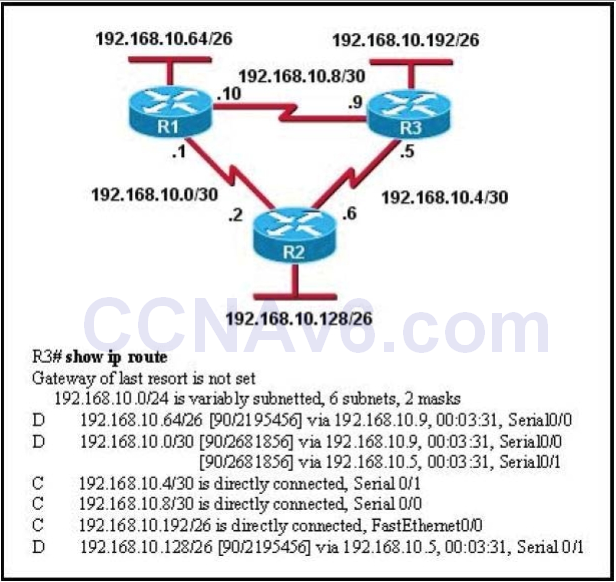 Correct
Correct
Incorrect
-
Question 325 of 417
325. Question
Refer to the exhibit. You have discovered that computers on the 192 168 10 0/24 network can ping their default gateway, but they cannot connect to any resources on a remote network. Which reason for the problem is most likely true?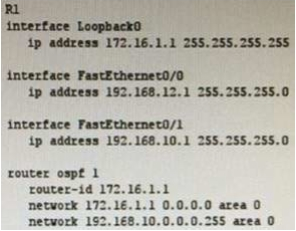 Correct
Correct
Incorrect
-
Question 326 of 417
326. Question
Which WAN topology provides a direct connection from each site to all other sites on the network?Correct
Incorrect
-
Question 327 of 417
327. Question
Which two passwords must be supplied in order to connect by Telnet to a properly secured Cisco switch and make changes to the device configuration? (Choose two.)Correct
Incorrect
-
Question 328 of 417
328. Question
Refer to the exhibit. Which user-mode password has just been set?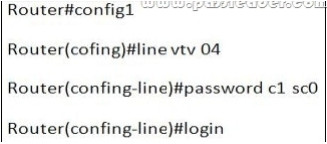 Correct
Correct
Incorrect
-
Question 329 of 417
329. Question
Which component of a routing table entry represents the subnet mask?Correct
Incorrect
Hint
IP Routing Table Entry Types An entry in the IP routing table contains the following information in the order presented: Network ID. The network ID or destination corresponding to the route. The network ID can be class- based, subnet, or supernet network ID, or an IP address for a host route. Network Mask. The mask that is used to match a destination IP address to the network ID. Next Hop. The IP address of the next hop. Interface. An indication of which network interface is used to forward the IP packet. Metric. A number used to indicate the cost of the route so the best route among possible multiple routes to the same destination can be selected. A common use of the metric is to indicate the number of hops (routers crossed) to the network ID. Routing table entries can be used to store the following types of routes: Directly Attached Network IDs. Routes for network IDs that are directly attached. For directly attached networks, the Next Hop field can be blank or contain the IP address of the interface on that network. Remote Network IDs. Routes for network IDs that are not directly attached but are available across other routers. For remote networks, the Next Hop field is the IP address of a local router in between the forwarding node and the remote network. Host Routes. A route to a specific IP address. Host routes allow routing to occur on a per-IP address ba- sis. For host routes, the network ID is the IP address of the specified host and the network mask is 255.255.255.255. Default Route. The default route is designed to be used when a more specific network ID or host route is not found. The default route network ID is 0.0.0.0 with the network mask of 0.0.0.0. -
Question 330 of 417
330. Question
How can you disable DTP on a switch port?Correct
Incorrect
-
Question 331 of 417
331. Question
How is the redundancy represented in ntp master?Correct
Incorrect
Hint
NTP redundancy http://sflanders.net/2015/02/09/time-hard-proper-ntp-configuration/ -
Question 332 of 417
332. Question
Which command you enter on a switch to display the ip address associated with connected devices?Correct
Incorrect
-
Question 333 of 417
333. Question
Which technology can enable multiple vlan to communicate with one another?Correct
Incorrect
-
Question 334 of 417
334. Question
Which protocol is a Cisco proprietary implementation of STP?Correct
Incorrect
-
Question 335 of 417
335. Question
Which Type of ipv6 unicast ip address is reachable across the internet?Correct
Incorrect
-
Question 336 of 417
336. Question
interface Loopback0 ip address 172.16.1.33 255.255.255.224 router bgp 999 neighbor 10.1.5.2 remote-as 65001 Refer to the exhibit . Which Command do you enter so that R1 advertises the loopback0 interface to the BGP Peers?Correct
Incorrect
-
Question 337 of 417
337. Question
Which networking Technology is currently recognized as the standard for computer networking?Correct
Incorrect
-
Question 338 of 417
338. Question
Which two are advantages of static routing when compared to dynamic routing? (Choose two.)Correct
Incorrect
Hint
Explanation: Since static routing is a manual process, it can be argued that it is more secure (and more prone to human errors) since the network administrator will need to make changes to the routing table directly. Also, in stub networks where there is only a single uplink connection, the load is reduced as stub routers just need a single static default route, instead of many routes that all have the same next hop IP address. -
Question 339 of 417
339. Question
Refer to the exhibit.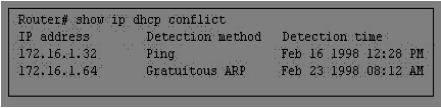 Which rule does the DHCP server use when there is an IP address conflict? Correct
Which rule does the DHCP server use when there is an IP address conflict? Correct
Incorrect
Hint
Explanation: An address conflict occurs when two hosts use the same IP address. During address assignment, DHCP checks for conflicts using ping and gratuitous ARP. If a conflict is detected, the address is removed from the pool. The address will not be assigned until the administrator resolves the conflict. -
Question 340 of 417
340. Question
Which two tasks does the Dynamic Host Configuration Protocol perform? (Choose two.)Correct
Incorrect
Hint
Explanation: The Dynamic Host Configuration Protocol (DHCP) is a network protocol used to configure devices that are connected to a network (known as hosts) so they can communicate on that network using the Internet Protocol (IP). It involves clients and a server operating in a client-server model. DHCP servers assigns IP addresses from a pool of addresses and also assigns other parameters such as DNS and default gateways to hosts. -
Question 341 of 417
341. Question
Which definition of default route is true?Correct
Incorrect
-
Question 342 of 417
342. Question
Which value must the device send as its username when using CHAP to authenticate with the remote peer site id:17604704 over a PPP link?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/wan/point-to-point-protocol-ppp/10241-ppp-callin-hostname.html -
Question 343 of 417
343. Question
Which two options are the best reasons to use an IPV4 private IP space? (Choose two)Correct
Incorrect
-
Question 344 of 417
344. Question
Which three statements about DWDM are true? (Choose three)Correct
Incorrect
Hint
thx to @green aple who provide the correct answer the correct answer is ABD. i saw it about dwdm in netacad course. this is the statement i copy from netacad for ensure. pecifically, DWDM: – Enables bidirectional communications over one strand of fiber. – Can multiplex more than 80 different channels of data (i.e., wavelengths) onto a single fiber. – Each channel is capable of carrying a 10 Gb/s multiplexed signal. – Assigns incoming optical signals to specific wavelengths of light (i.e., frequencies). – Can amplify these wavelengths to boost the signal strength. – Supports SONET and SDH standards. – DWDM circuits are used in all modern submarine communications cable systems and other longhaul circuit -
Question 345 of 417
345. Question
Which tunneling mechanism embeds an IPv4 address within an IPv6 address?Correct
Incorrect
Hint
https://tools.ietf.org/html/rfc6052#section-2 -
Question 346 of 417
346. Question
If two OSPF neighbors have formed complete adjacency and are exchanging link-state advertisements, which state have they reached?Correct
Incorrect
Hint
https://www.google.com/search?q=state+ospf&source=lnms&tbm=isch&sa=X&ved=0ahUKEwjg7ebX jtLVAhXJAsAKHXoyATQQ_AUIDCgD&biw=1536&bih=735#imgrc=99-F38FQ0gZgVM: -
Question 347 of 417
347. Question
Which three statements about IPv6 address fd14:920b:f83d:4079::/64 are true? (Choose three)Correct
Incorrect
Hint
https://www.ripe.net/participate/member-support/lir-basics/ipv6_reference_card.pdf -
Question 348 of 417
348. Question
Which functionality does an SVI provide?Correct
Incorrect
-
Question 349 of 417
349. Question
Which three commands are required to enable NTP authentication on a Cisco router? (Choose three)Correct
Incorrect
Hint
http://blog.ine.com/2007/12/28/how-does-ntp-authentication-work/ -
Question 350 of 417
350. Question
Which statement about DHCP snooping is true?Correct
Incorrect
-
Question 351 of 417
351. Question
Which type of cable must you use to connect two device with mdi interfaces ?Correct
Incorrect
-
Question 352 of 417
352. Question
which port security violation mode allows traffic from valid mac address to pass but block traffic from invalid mac address?Correct
Incorrect
-
Question 353 of 417
353. Question
Which type of routing protocol operates by exchanging the entire routing information ?Correct
Incorrect
-
Question 354 of 417
354. Question
Which statements is true about Router on Stick.Correct
Incorrect
-
Question 355 of 417
355. Question
Refer to the exhibit. Given the output from the show ip eigrp topology command, which router is the feasible successor? router# show ip eigrp topology 10.0.0.5 255.255.255.255 IP-EIGRP topology entry for 10.0.0.5/32 State is Passive, Query origin flag is 1, 1 Successor(s), FD is 41152000Correct
Incorrect
-
Question 356 of 417
356. Question
Which IPsec security protocol should be used when confidentiality is required?Correct
Incorrect
-
Question 357 of 417
357. Question
Which IPv6 routing protocol uses multicast group FF02::9 to send updates?Correct
Incorrect
-
Question 358 of 417
358. Question
Which of the port is not part of STP protocol. (Question is not accurate but its sounds something like this)Correct
Incorrect
-
Question 359 of 417
359. Question
which definition of a host route is true?Correct
Incorrect
-
Question 360 of 417
360. Question
which statement about upgrading a cisco IOS device with TFTP server?Correct
Incorrect
-
Question 361 of 417
361. Question
What is a valid HSRP virtual MAC address? (old question)Correct
Incorrect
-
Question 362 of 417
362. Question
which command do use we to see SNMP versionCorrect
Incorrect
Hint
https://www.cisco.com/c/en/us/td/docs/ios/12_2/configfun/command/reference/ffun_r/frf014.htm l#wp1053304 -
Question 363 of 417
363. Question
Which command can you enter on a switch to determine the current SNMP security model?Correct
Incorrect
Hint
https://www.cisco.com/c/en/us/td/docs/ios/12_2/configfun/command/reference/ffun_r/frf014.htm l#wp1053304 -
Question 364 of 417
364. Question
When troubleshooting Ethernet connectivity issues, how can you verify that an IP address is known to a router?Correct
Incorrect
-
Question 365 of 417
365. Question
After you apply the given configuration to a router, the DHCP clients behind the device cannot communicate with hosts outside of their subnet. Which action is most likely to correct the problem?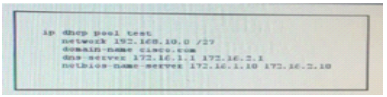 Correct
Correct
Incorrect
-
Question 366 of 417
366. Question
Refer to the exhibit. What set of commands was configured on interface Fa0/3 to produce the given the output? Correct
Correct
Incorrect
-
Question 367 of 417
367. Question
While troubleshooting a DCHP client that is behaving erratically, you discover that the client has been assigned the same IP address as a printer that is a static IP address. Which option is the best way to resolve the problem?Correct
Incorrect
-
Question 368 of 417
368. Question
Refer to the exhibit: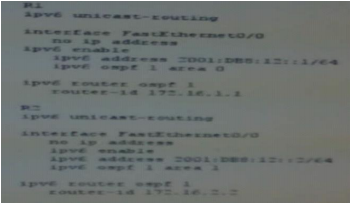 after you apply the give configurations to R1 and R2 you notice that OSPFv3 fails to start. Which reason for the problem is most likely true ? Correct
after you apply the give configurations to R1 and R2 you notice that OSPFv3 fails to start. Which reason for the problem is most likely true ? Correct
Incorrect
-
Question 369 of 417
369. Question
Which two statements about IPv6 address 2002:ab10:beef::/48 are true? (Choose two.)Correct
Incorrect
-
Question 370 of 417
370. Question
While troubleshooting a connection problem on a computer, you determined that the computer can ping a specific web server but it cannot connect to TCP port 80 on that server. Which reason for the problem is most likely ture?Correct
Incorrect
-
Question 371 of 417
371. Question
Which two steps must you perform on each device that is configured for IPv4 routing before you implement OSPFv3? (Choose two.)Correct
Incorrect
-
Question 372 of 417
372. Question
Which option is the main function of congestion management?Correct
Incorrect
-
Question 373 of 417
373. Question
Which command must you enter to enable OSPFV2 in an IPV4 network?Correct
Incorrect
-
Question 374 of 417
374. Question
Which three statements about the features of SNMPv2 and SNMPv3 are true? (Choose three.)Correct
Incorrect
-
Question 375 of 417
375. Question
Why do large OSPF networks use a hierarchical design? (choose three)Correct
Incorrect
-
Question 376 of 417
376. Question
Assuming the default switch configuration which vlan range can be added modified and removed on a Cisco switch?Correct
Incorrect
-
Question 377 of 417
377. Question
Which of the following is true about spanning-tree root-bridge election?Correct
Incorrect
-
Question 378 of 417
378. Question
What is the most efficient subnet mask for a point to point ipv6 connection?Correct
Incorrect
Hint
https://tools.ietf.org/html/rfc6164 -
Question 379 of 417
379. Question
Which protocol does ipv6 use to discover other ipv6 nodes on the same segment?Correct
Incorrect
Hint
https://tools.ietf.org/html/rfc4861 -
Question 380 of 417
380. Question
which technology supports multiple dynamic secure connections an unsecure transport network ?Correct
Incorrect
-
Question 381 of 417
381. Question
To enable router on a stick on a router subinterface, which two steps must you perform ? choose twoCorrect
Incorrect
-
Question 382 of 417
382. Question
Which feature can you use to restrict SNMP queries to a specific OID tree?Correct
Incorrect
-
Question 383 of 417
383. Question
Which two options are fields in an Ethernet frame? (choose two)Correct
Incorrect
-
Question 384 of 417
384. Question
Refer to the exhibit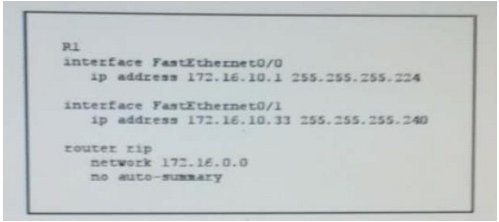 fter you apply the given configuration to R1, you determine that it is failing to advertise the 172.16.10.32/27 network. Which action most likely to correct the problem. Correct
fter you apply the given configuration to R1, you determine that it is failing to advertise the 172.16.10.32/27 network. Which action most likely to correct the problem. Correct
Incorrect
-
Question 385 of 417
385. Question
Which type of secure MAC address must be configured manually?Correct
Incorrect
-
Question 386 of 417
386. Question
What are types of IPv6 static routes? (Choose Three)Correct
Incorrect
-
Question 387 of 417
387. Question
Which option is the industry-standard protocol for ether channelCorrect
Incorrect
-
Question 388 of 417
388. Question
Router R1 has a static router that is configured to a destination network. A directly connected inference is configured with an ip address in the same destination network. which statement about R1 is trueCorrect
Incorrect
-
Question 389 of 417
389. Question
Where does a switch maintain DHCP snooping information?Correct
Incorrect
-
Question 390 of 417
390. Question
When is a routing table entry identified as directly connected?Correct
Incorrect
-
Question 391 of 417
391. Question
which command can you enter in a network switch configuration so that learned mac addresses are saved in configuration as they connect?Correct
Incorrect
-
Question 392 of 417
392. Question
If Computer A is sending traffic to computer B, which option is the source ip address when a packet leaves R1 on interface F0/1?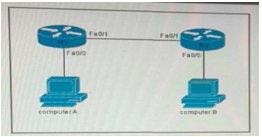 Correct
Correct
Incorrect
-
Question 393 of 417
393. Question
Which three options are the major components of a network virtualization architecture? (Choose three.)Correct
Incorrect
-
Question 394 of 417
394. Question
Which RPVST+ port state is excluded from all STP operations?Correct
Incorrect
-
Question 395 of 417
395. Question
Which command can you enter to block HTTPS traffic from the whole class A private network range to a host?Correct
Incorrect
-
Question 396 of 417
396. Question
For which two reasons was RFC 1918 address space define (Choose two)Correct
Incorrect
-
Question 397 of 417
397. Question
Which two statements about RIPv2 are true? (Choose two)Correct
Incorrect
-
Question 398 of 417
398. Question
In which CLI configuration mode can you configure the hostname of a device?Correct
Incorrect
-
Question 399 of 417
399. Question
In which two circumstances are private IPv4 addresses appropriate? (Choose two)Correct
Incorrect
-
Question 400 of 417
400. Question
related to BPDU need to choose 2Correct
Incorrect
-
Question 401 of 417
401. Question
Which two statements about eBGP neighbor relationships are true? (Choose two)Correct
Incorrect
-
Question 402 of 417
402. Question
Which two pieces of information can be shared with LLDP TLVs? (Choose two)Correct
Incorrect
-
Question 403 of 417
403. Question
Which two statements about UDP are true? (Choose two)Correct
Incorrect
-
Question 404 of 417
404. Question
Which two statements about access points are true? (Choose Two)Correct
Incorrect
-
Question 405 of 417
405. Question
For which two protocols can PortFast alleviate potential host startup is-sues? (Choose two.)Correct
Incorrect
-
Question 406 of 417
406. Question
What does it take for BGP to establish connection. (Choose 2) Given answers wereCorrect
Incorrect
Hint
router bgp AS LOCAL neighbor xxxx remote-as AS number on remote router -
Question 407 of 417
407. Question
On which layer tcp/ip is ACL Apic-EM pathCorrect
Incorrect
-
Question 408 of 417
408. Question
how is MPLS implemented (like this) :Correct
Incorrect
-
Question 409 of 417
409. Question
Question about HTTP API :Correct
Incorrect
-
Question 410 of 417
410. Question
Which cloud service is typically used to provide DNS and DHCP services to an enterprise?Correct
Incorrect
-
Question 411 of 417
411. Question
how to configure pppoe choose 2Correct
Incorrect
-
Question 412 of 417
412. Question
how router will advertise dhcpoffer to its other interface :Correct
Incorrect
-
Question 413 of 417
413. Question
What two state that lacp forwarding (something like this)Correct
Incorrect
-
Question 414 of 417
414. Question
whats benefit of dual homed vs single homod :Correct
Incorrect
-
Question 415 of 417
415. Question
Which is true about switch stacking something like thatCorrect
Incorrect
-
Question 416 of 417
416. Question
when ebgp it used (like this)Correct
Incorrect
-
Question 417 of 417
417. Question
What statements are true for multicast mac address directions?Correct
Incorrect
Hint
Amm because of lack information about Drag and Drop and Simulation , I will provide some information and complete some option shared in 9TUT

Why put the “Check” button so close to the “NEXT ARTICLE” button. This made me waste so much time restarting the quizz. :(
Why do you have to restart the quizz?