1. Configure and verify PPP and MLPPP WAN connectivity The following describe the standard reasons for deploying WAN connectivity: enable connectivity between branch offices, data center and cloud information sharing among internal and external organizations Serial Interfaces Serial interfaces connect devices that are assigned as a DCE or …
1. Describe routing concepts Routers are primarily responsible for logical addressing and best path selection. They forward packets between different subnets, VLANs and across the WAN. They build a routing table with routes comprised of network prefix, metric and next hop address. The router selects the route based …
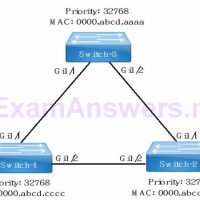
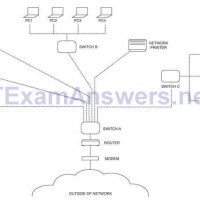
1. Describe and verify switching concepts The following is a list of network services provided by switches: switches forward data link layer traffic switches create and maintain the MAC address table switches support segmenting collision domains MAC address table Every network device is assigned a unique hardware address …
1. Compare and contrast OSI and TCP/IP models The following describe the network services at each layer of the OSI model. Each lower OSI layer provided services to the next higher layer. Effective troubleshooting should start from the physical layer and verify connectivity to the application layer. Table …
1. A network technician receives a call from a use who is experiencing network connectivity issues. The network technician questions the user and learns the user brought in a personal wired router to use multiple computers and connect to the network. Which of the following has the user …
1. Refer to the exhibit. Approximately what percentage of the physical memory is still available on this Windows system? 32% 53% 68% 90% 2. Which Windows tool can be used by a cybersecurity administrator to secure stand-alone computers that are not part of an active directory domain? Local …
Objectives Apply your knowledge of security incident handling procedures to formulate questions about given incident scenarios. Background / Scenario Computer security incident response has become a vital part of any organization. The process for handling a security incident can be complicated and involve many different groups. An organization …
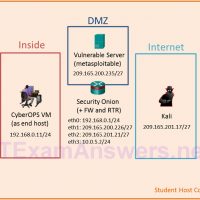
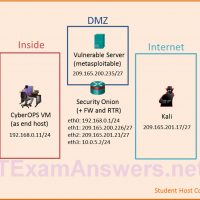
Topology Objectives In this lab, you will review logs during an exploitation of a documented vulnerability to determine the compromised hosts and file. Part 1: Prepare the Virtual Environment Part 2: Reconnaissance Part 3: Exploitation Part 4: Infiltration Part 5: Review the Logs Background / Scenario The 5-tuple …
Topology Objectives In this lab, you will review logs during an exploitation of documented HTTP and DNS vulnerabilities. Part 1: Prepare the Virtual Environment Part 2: Investigate an SQL Injection Attack Part 3: Data Exfiltration Using DNS Background / Scenario MySQL is a popular database used by numerous …
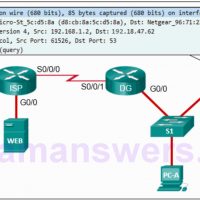
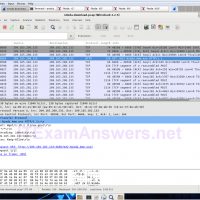
Objectives Part 1: Prepare the Virtual Environment Part 2: Analyze Pre-Captured Logs and Traffic Captures Background / Scenario Looking at logs is very important but it is also important to understand how network transactions happen at the packet level. In this lab, you will analyze the traffic in …