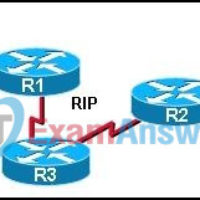
1. Refer to the exhibit. Which configuration command or commands contributed to the output that is shown? routerA(config-router)# no version 2 routerA(config)# interface fa0/0 routerA(config-if)# ip address 172.19.0.0 255.255.0.0 routerA(config-router)# network 192.168.3.0 routerA(config)# no ip default-gateway 2. Refer to the exhibit. What is the maximum number of RIP …
1. Refer to the exhibit. Which three sets of commands are required to enable administrators to connect to the Switch1 console over Telnet for configuration and management? (Choose three.) Switch1(config)# interface fa0/1 Switch1(config-if)# ip address 192.168.2.64 255.255.255.192 Switch1(config)# interface fa0/1 Switch1(config-if)# ip address 192.168.2.66 255.255.255.192 Switch1(config)# interface vlan …
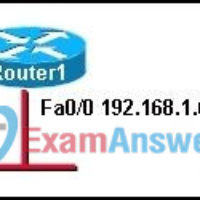
1. Refer to the exhibit. Host A is connected to the LAN, but it cannot get access to any resources on the Internet. The configuration of the host is shown in the exhibit. What could be the cause of the problem? The host subnet mask is incorrect. The …
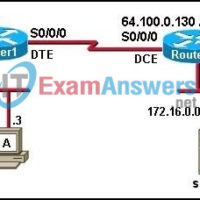
1. Refer to the exhibit. Which type of twisted pair cable is used between each device? A=console, B=straight, C=crossover, D= crossover, E=straight A=straight, B=straight, C=straight, D=crossover, E=console A=crossover, B=straight, C=straight, D=crossover, E=crossover A=console, B=straight, C=straight, D=crossover, E=crossover A=console, B=crossover, C=crossover, D=straight, E=straight 2. Which three issues should be noted …
1. Which two functions are provided by the upper layers of the OSI model? (Choose two.) placing electrical signals on the medium for transmission initiating the network communication process encrypting and compressing data for transmission segmenting and identifying data for reassembly at the destination choosing the appropriate path …
1. Which network support services team is responsible for testing a new customer connection and for monitoring the ongoing operation of the link? customer service network operations help desk on-site installation 2. Which two things can be determined by using the ping command? (Choose two.) the number of …
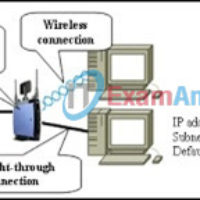
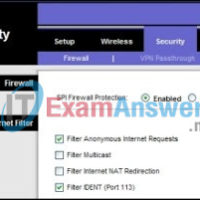
1. A wireless DHCP client cannot connect to the Internet through a Linksys integrated router. When you type ipconfig on the host, no IP address, subnet mask, or default gateway shows. What are two of the first things you will check? (Choose two.) SSID the cable between client …
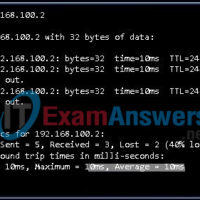
1. Refer to the exhibit. A host is having problems maintaining a connection to a server at 192.168.100.2. Which statement best describes the output of the ping command? The server is shut down. The server has no route back to the host. Two routers along the path are …
1. What should a network administrator do first after receiving a call from a user who cannot access the company web server? Reboot the web server. Replace the NIC of the computer. Ask the user to log off and log on again. Ask the user what URL has …
1. Identify three techniques used in social engineering. (Choose three.) fishing vishing phishing spamming pretexting junk mailing 2. During a pretexting event, how is a target typically contacted? by e-mail by phone in person through another person 3. While surfing the Internet, a user notices a box claiming …