CCNA 1 Chapter 3 v5.0 Exam Answers 2015 (100%) PDF Download 1. A computer in a given network is communicating with a specific group of computers. What type of communication is this? broadcast multicast unicast ARP HTTP 2. What method can be used by two computers to ensure …
1. Convert the decimal number 231 into its binary equivalent. Select the correct answer from the list below. 11110010 11011011 11110110 11100111 11100101 11101110 2. Convert the binary number 10111010 into its hexadecimal equivalent. Select the correct answer from the list below. 85 90 BA A1 B3 1C …
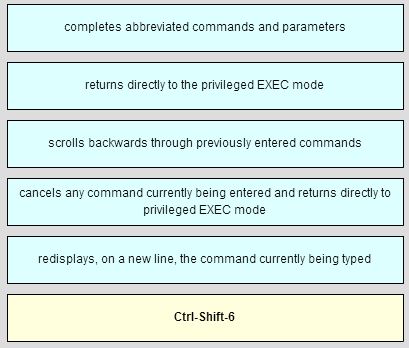
CCNA 1 Chapter 2 v5.0 Exam Answers 2015 100% PDF Download 1. Which two features are characteristics of flash memory? (Choose two.) Flash provides nonvolatile storage. Flash receives a copy of the IOS from RAM when a device is powered on. The contents of flash may be lost …
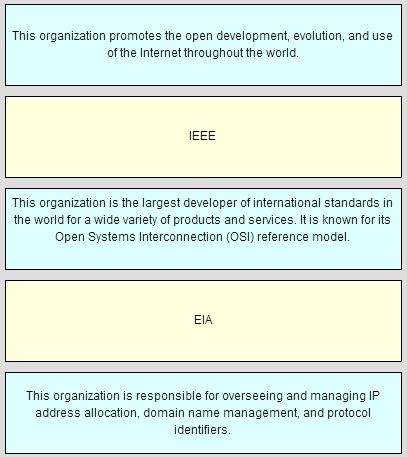
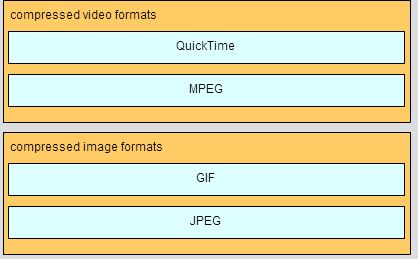
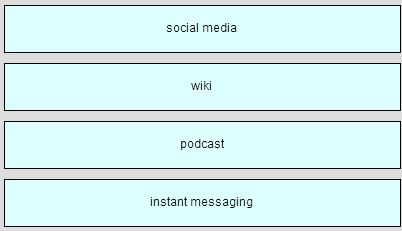
CCNA 1 Chapter 1 v5.0 Exam Answers 2015 (100%) PDF Download 1. What two criteria are used to help select network media? (Choose two.) the types of data that need to be prioritized the cost of the end devices utilized in the network the distance the media can …
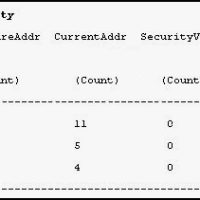
1. Refer to the exhibit. Which statement is true about port Fa5/1? When a violation is detected, the port will log the information to a syslog server. When a violation is detected, the port will go into err-disable mod There have been 11 security violations since the last …
1. What can be found at the enterprise edge? Internet, VPN, and WAN modules Internet, PSTN, and WAN services server farms and network management campus infrastructure, including access layer devices 2. In which functional area of the Cisco Enterprise Architecture should IDS and IPS be located to detect …
1. A company is developing an Internet store for its website. Which protocol should be used to transfer credit card information from customers to the company web server? FTPS HTTP HTTPS WEP2 TFTP 2. Refer to the exhibit. A new branch office has been added to the corporate …
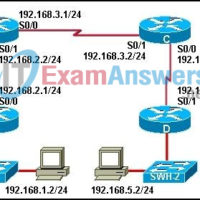
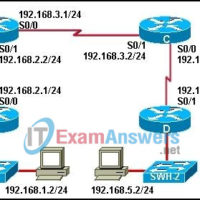
1. A network administrator is asked to design a system to allow simultaneous access to the Internet for 250 users. The ISP for this network can only supply five public IPs. What can be used to accomplish this task? static translation port address translation routable translation dynamic translation …
1. Which AAA service reduces IT operating costs by providing detailed reporting and monitoring of network user behavior, and also by keeping a record of every access connection and device configuration change across the network? accreditation authentication accounting authorization 2. A hacker has gained access to sensitive network …
1. Refer to the exhibit. Which two statements are true about this file? (Choose two.) If the gateway address changes, the file will be updated dynamically. The command ping fileserv will use IP address 172.16.5.10. If the ping www.cisco.com command is issued, the file will be checked for the …