8.3.3 Quiz – Performing Post-Exploitation Techniques Answers
1. Which resource is a Windows utility that combines the old CMD functionality with a new scripting/cmdlet instruction set with built-in system administration functionality?
- Socat
- Wsc2
- PowerShell
- Twittor
Explanation: Windows PowerShell is a newer Microsoft shell that combines the old command prompt (CMD) functionality with a new scripting/cmdlet instruction set with built-in system administration functionality. PowerShell cmdlets allow users and administrators to automate complicated tasks with reusable scripts. Socat, wsc2, and Twittor are Command and Control (C2) utilities.
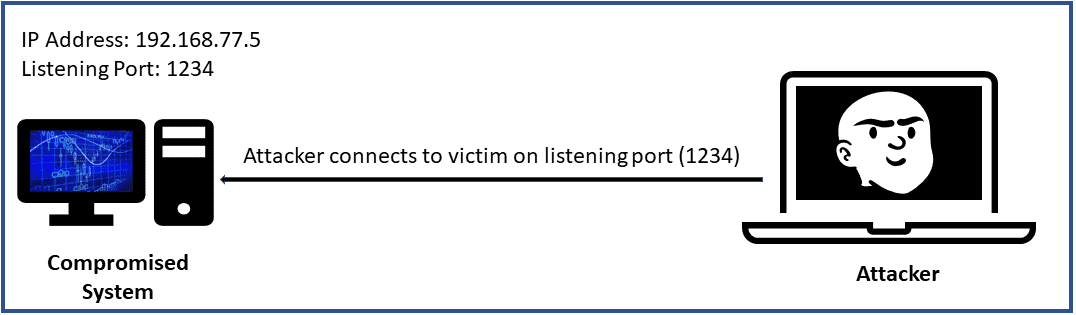
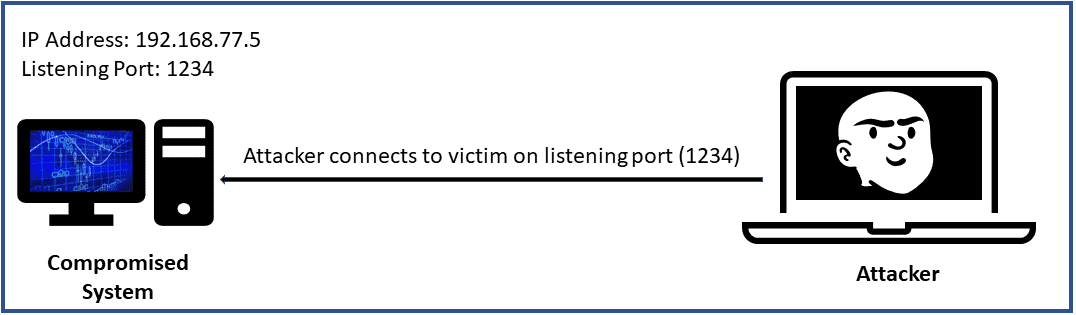
2. Refer to the exhibit. An attacker opens a port or a listener on the compromised system and waits for a connection. The goal is to connect to the victim from any system, execute commands, and further manipulate the victim. What type of malicious activity is being performed?
- reverse shell
- horizontal privilege escalation
- bind shell
- vertical privilege escalation
Explanation: With a bind shell, an attacker opens a port or a listener on the compromised system and waits for a connection. This is done to connect to the victim from any system, execute commands, and further manipulate the victim. In this case, the attacker opens port 1234 on the compromised system with an IP address 192.168.77.5.
3. Which resource is a lightweight and portable tool that allows the creation of bind and reverse shells from a compromised host?
- WMImplant
- WSC2
- BloodHound
- Netcat
Explanation: Many tools allow the creation of bind and reverse shells from a compromised host. One of the most popular is Netcat. Netcat is one of the best and most versatile pen test tools because it is lightweight and very portable. WMImplant is a PowerShell-based tool that leverages WMI to create a command and control channel. Wsc2 is a Python-based command and control utility that uses WebSockets. BloodHound is a single-page JavaScript web application that uses graph theory to reveal the hidden relationships in a Windows Active Directory environment.
4. A cybersecurity student is learning about Netcat commands that could be used in a penetration testing engagement. Which Netcat command is used to connect to a TCP port?
- nc -nv
- nc -lvp
- nc -z
- nc -nv
Explanation: Several Netcat commands can be used in a penetration testing engagement. Some of them are the following:
- nc -nv – to connect to a TCP port
- nc -lvp – to listen on a given TCP port
- nc -lvp 1234 > output.txt (receiving system) and nc -nv nc -z – to be used as a port scanner
5. Which Meterpreter command is used to execute Meterpreter commands that are listed inside a text file and also to help accelerate the actions taken on the victim system?
- search
- execute
- resource
- shell
Explanation: Some of the most common Meterpreter commands are the following:
- resource – used to execute Meterpreter commands listed inside a text file, which can help accelerate the actions taken on the victim system
- search – used to locate files on the victim system
- shell – used to go into a standard shell on the victim system
- execute – used to run commands on the victim system
6. Which two resources are C2 utilities? (Choose two.)
- Socat
- Empire
- BloodHound
- Netcat
- Twittor
Explanation: Many different utilities can be used to create a C2, such as socat, a C2 utility that can be used to create multiple reverse shells, and Twittor, a C2 utility that uses Twitter direct messages for command and control. Netcat is a simple unix utility that reads and writes data across network connections using TCP or UDP. BloodHound is a single-page JavaScript web application that uses graph theory to reveal the hidden relationships in a Windows Active Directory environment. Empire is an open-source framework that includes a PowerShell Windows agent and a Python Linux agent.
7. What kind of channel is created by a C2 with a system that has been compromised?
- wireless channel
- encrypted channel
- covert channel
- command channel
Explanation: A C2 creates a covert channel with the compromised system. A covert channel is an adversarial technique that allows the attacker to transfer information objects between processes or systems that, according to a security policy, are not supposed to be allowed to communicate.
8. Which living-off-the-land post-exploitation technique can get directory listings, copy and move files, get a list of running processes, and perform administrative tasks?
- PowerShell
- Sysinternals
- WMI
- BloodHound
Explanation: PowerShell can get directory listings, copy and move files, get a list of running processes, and perform administrative tasks. Sysinternals is a suite of tools that allows administrators to control Windows-based computers from a remote terminal. BloodHound is a single-page JavaScript web application that uses graph theory to reveal the hidden relationships in a Windows Active Directory environment. WMI is used to manage data and operations on Windows operating systems.
9. Which resource is an open-source framework that allows rapid deployment of post-exploitation modules, including keyloggers, bind and reverse shells, and adaptable communication to evade detection?
- BloodHound
- Sysinternals
- WMI
- Empire
Explanation: Empire is an open-source framework that includes a PowerShell Windows agent and Python Linux agent. It allows rapid deployment of post-exploitation modules, including keyloggers, bind and reverse shells, Mimikatz, and adaptable communication to evade detection. BloodHound is a single-page JavaScript web application that uses graph theory to reveal the hidden relationships in a Windows Active Directory environment. Sysinternals is a suite of tools that allows administrators to control Windows-based computers from a remote terminal. WMI is used to manage data and operations on Windows operating systems.
10. Which resource is a single-page JavaScript web application that can be used to find complex attack paths in Microsoft Azure?
- Empire
- Netcat
- BloodHound
- Sysinternals
Explanation: BloodHound is a single-page JavaScript web application that uses graph theory to reveal the hidden relationships in a Windows Active Directory environment. An attacker can use it to identify numerous attack paths. Similarly, an incident response team can use BloodHound to detect and eliminate those same attack paths. It can also be used to find complex attack paths in Microsoft Azure.
11. Which utility can be used to write scripts or applications to automate administrative tasks on remote computers and can also be used by malware to perform different activities in a compromised system?
- WMI
- PowerShell
- Empire
- BloodHound
Explanation: Windows Management Instrumentation (WMI) manages data and operations on Windows operating systems. WMI scripts or applications can be written to automate administrative tasks on remote computers. Malware can use WMI to perform different activities in a compromised system. For example, the Nyeta ransonware used WMI to perform administrative tasks.
12. Which Sysinternals tool is used by penetration testers to modify Windows registry values and connect a compromised system to another system?
- PsInfo
- PsLoggedOn
- PsGetSid
- PsExec
Explanation: PsExec is one of the most powerful Sysinternals tools. It can remotely execute anything that can run on a Windows command prompt. PsExec can also modify Windows registry values, execute scripts, and connect a compromised system to another system.
13. Which three tools are living-off-the-land post-exploitation techniques? (Choose three.)
- Twittor
- PowerSploit
- Socat
- WMImplant
- WinRM
- Empire
Explanation: Some examples of living-off-the-land post-exploitation techniques are Empire, WMI, BloodHound, PowerShell, Sysinternals, WinRM, and PowerSploit. WMImplant, Twittor, and socat are C2 utilities. Mimikatz is a tool for credential attacks.
14. An attacker wants to allow further connections to a compromised system and maintain persistent access. The attacker uses the Windows system command Enable-PSRemoting -SkipNetworkProfileCheck – Force. What tool is being enabled using this command?
- WinRM
- BloodHound
- PsExec
- WMImplant
Explanation: WinRM can be useful for post-exploitation activities. An attacker could enable WinRM to allow further connections to the compromised systems. It can easily be enabled on a Windows system by using the Enable-PSRemoting -SkipNetworkProfileCheck – Force command. This command configures the WinRM service to start automatically and sets up a firewall rule to allow inbound connections to the compromised system.
15. What kind of malicious activity is performed by a lower-privileged user who accesses functions reserved for higher-privileged users?
- horizontal privilege escalation
- steganography
- bind shell
- vertical privilege escalation
Explanation: Privilege escalation is gaining access to resources that normally would be protected from an application or a user. With vertical privilege escalation, lower-privileged users access functions reserved for higher-privileged users, such as root or administrator access.
16. What task can be accomplished with the steghide tool?
- to modify Windows registry values and to connect a compromised system to another system
- to find complex attack paths in Microsoft Azure
- to obfuscate, to evade and to cover the attacker tracks
- to allow administrators to control a Windows-based computer from a remote terminal
Explanation: Attackers can use steganography to obfuscate, evade, and cover the tracks. Steganography involves hiding a message or any other content inside an image or a video file. To accomplish this task, tools such as steghide can be used.
17. After compromising a system during a penetration testing engagement, all penetration work should be cleaned up, including extra files, system changes, and modified logs. The media sanitation methodology should be discussed with the client and the owner of the affected systems. What document guides media sanitation?
- NIST SP 800-88
- OWASP ZAP
- OSSTMM
- PCI DSS
Explanation: After a penetration testing engagement is complete, all the systems should be cleaned up. Logs should be suppressed, user accounts deleted, and any files that were created as well. A secure deletion method may be preferred. NIST Special Publication 800-88, Revision 1: “Guidelines for Media Sanitization,” guides media sanitation. This methodology should be discussed with the client and the owner of the affected systems.
18. What procedure should be deployed to protect the network against lateral movement?
- Database backups
- VPNs
- Strong passwords for user accounts
- VLANs
Explanation: Lateral movement involves scanning a network for other systems, exploiting vulnerabilities in other systems, compromising credentials, and collecting sensitive information for exfiltration. Lateral movement is possible if an organization does not segment the network properly. The organization might have deployed virtual or physical firewalls, VLANs, or access control policies for segmentation.
19. What is the main advantage of Remote Desktop over Sysinternals?
- It can upload, execute, and interact with executables on compromised hosts.
- It can run commands revealing information about running processes, and services can be killed and stopped.
- It can use PsExec to remotely execute anything that can run on a Windows command prompt.
- It gives a full, interactive GUI of the remote compromised computer.
Explanation: The main advantage of Remote Desktop over other tools, like Sysinternals, is that it gives a full, interactive graphical user interface (GUI) of the remote compromised computer. The other three options describe the characteristics of Sysinternals.
20. An attacking system has a listener (port open), and the victim initiates a connection back to the attacking system. What type of vulnerability does this situation describe?
- reverse shell
- horizontal privilege escalation
- bind shell
- vertical privilege escalation
Explanation: A reverse shell is a vulnerability in which an attacking system has a listener (port open), and the victim initiates a connection back to the attacking system. With a bind shell, an attacker opens a port or a listener on the compromised system and waits for a connection. With horizontal privilege escalation, a regular user accesses functions or content reserved for other non-root or non-admin users. With vertical privilege escalation, a lower-privileged user accesses functions reserved for higher-privileged users, such as root or administrator access.
21. A cybersecurity student is learning about Netcat commands that could be used in a penetration testing engagement. The student wants to use Netcat as a port scanner. What command should be used?
- nc -nv
- nc -lvp
- nc -z
- nc -nv
Explanation: Several Netcat commands can be used in a penetration testing engagement. Some of them are the following:
- nc -nv – to connect to a TCP port
- nc -lvp – to listen on a given TCP port
- nc -lvp 1234 > output.txt (receiving system) and nc -nv nc -z – to be used as a port scanner
22. Which C2 utility is a PowerShell-based tool that leverages WMI to create a C2 channel?
- Socat
- WMImplant
- WSC2
- TrevorC2
Explanation: Many different techniques and utilities can be used to create a C2. Some examples are the following:
- WMImplant – a PowerShell-based tool that leverages WMI to create a C2 channel
- socat – a C2 utility that can be used to create multiple reverse shells
- wsc2 – a Python-based C2 utility that uses WebSockets
- TrevorC2 – a Python-based C2 utility
23. Which two C2 utilities are Python-based? (Choose two.)
- TrevorC2
- Socat
- DNSCat2
- Wsc2
- Twittor
Explanation: C2 utilities are useful software tools. Examples include Twittor, wsc2, DNSCat2, socat, and TrevorC2. Python-based C2 utilities are wsc2 and TrevorC2.
24. After the exploitation phase, it is necessary to maintain a foothold in a compromised system to perform additional tasks. Which way could maintain persistence?
- performing ARP scans and ping sweeps
- performing additional enumeration of users, groups, forests, sensitive data, and unencrypted files
- creating a bind or reverse shell
- using local system tools
Explanation: After the exploitation phase, it is necessary to maintain a foothold in a compromised system to perform additional tasks, such as installing and modifying services to connect back to the compromised system. The persistence of a compromised system can be maintained in several ways, including the following:
- creating a bind or reverse shell
- creating and manipulating scheduled jobs and tasks
- creating custom daemons and processes
- creating new users
25. Which two commands are the same in Meterpreter and Linux or Unix-based systems? (Choose two.)
- pwd
- hashdump
- clearev
- resource
- cat
Explanation: The Meterpreter commands that are the same as the ones in Linux or Unix-based systems are cat, cd, pwd, and ls.

1. Which resource is a Windows utility that combines the old CMD functionality with a new scripting/cmdlet instruction set with built-in system administration functionality?
1. Which resource is a Windows utility that combines the old CMD functionality with a new scripting/cmdlet instruction set with built-in system administration functionality?
Answer: Powershell