Category: CCNA Exploration 4.0
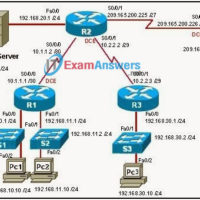
10.1.1.4 Packet Tracer – Map a Network Using CDP (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Topology Addressing Table Device Interface IP Address Subnet Mask Local Interface and Connected Neighbor Edge1 G0/0 192.168.1.1 255.255.255.0 G0/1 – …
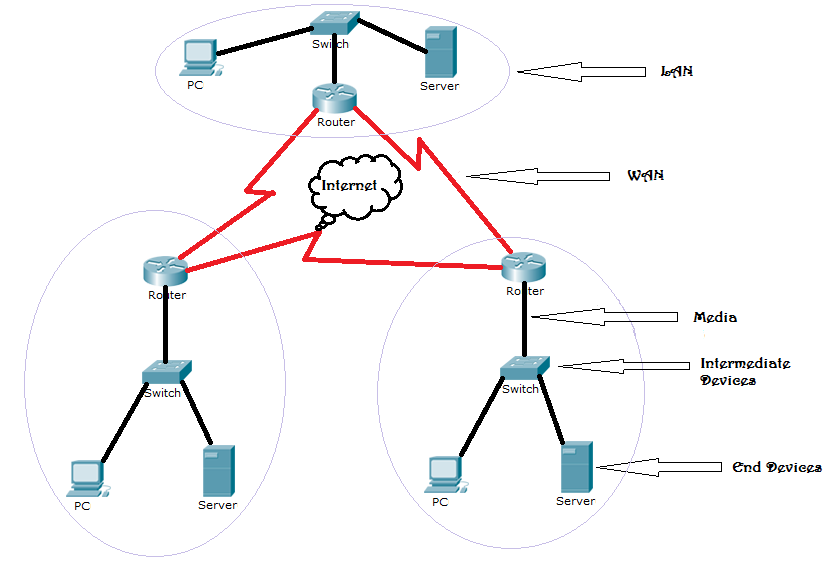
Draw Your Concept of the Internet Now Objectives Identify the common components of a network. In this activity, you will illustrate how concepts from Chapter 1 are applied to show how network devices connect to and throughout the Internet. After reflecting on your home or small-business topology, you …
Assessment ESwitching Practice Final – CCNA 3 Exploration: LAN Switching and Wireless (Version 4.0) 1. Refer to the exhibit. After receiving a console notification on Switch2, the network administrator begins to troubleshoot the trunk link between Switch1 and Switch2. Which configuration change can be made to correct the …
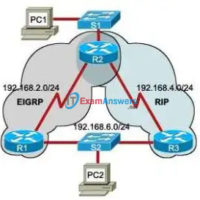
Assessment ERouting Practice Final – CCNA 2 Exploration: Routing Protocols and Concepts (Version 4.0) 1. Refer to exhibit. The network is using the RIPv2 routing protocol. If network 10.0.0.0 goes down, what mechanism will prevent Router1 from advertisting false routing information back to Router2? triggered updates poison reverse …
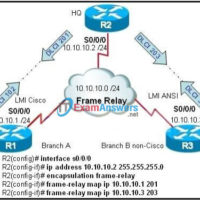
Assessment EWAN Final – CCNA 4 Exploration: Accessing the WAN (Version 4.0) 1. Which two statements are true about creating and applying access lists? (Choose two.) There is an implicit deny at the end of all access lists. One access list per port, per protocol, per direction is …
Assessment EWAN Practice Final – CCNA 4 Exploration: Accessing the WAN (Version 4.0) 1. What are two characteristics of DSL technology? (Choose two.) Uploads typically offer larger transfer rates than downloads. Service providers deploy DSL in the local loop of the telephone network. DSL download rates are reduced …
Assessment EWAN Chapter 8 – CCNA 4 Exploration: Accessing the WAN (Version 4.0) 1. What combination of IP address and wildcard mask should be used to specify only the last 8 addresses in the subnet 192.168.3.32/28? 192.168.3.32 0.0.0.7 192.168.3.32 0.0.0.15 192.168.3.40 0.0.0.7 192.168.3.40 0.0.0.15 2. Excessive broadcasts are …
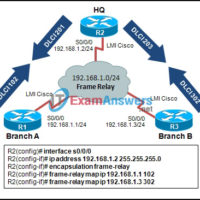
Assessment EWAN Chapter 7 – CCNA 4 Exploration: Accessing the WAN (Version 4.0) 1. Refer to the exhibit. Traffic exiting R1 is failing translation. What part of the configuration is most likely incorrect? ip nat pool statement access-list statement ip nat inside is on the wrong interface interface …
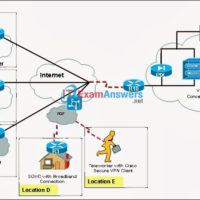
1. Which two protocols can be used to encapsulate traffic that is traversing a VPN tunnel? (Choose two.) ATM CHAP IPsec IPX MPLS PPTP 2. What are the three main functions of a secure VPN? (Choose three.) accounting authentication authorization data availability data confidentiality data integrity 3. Data …
1. The following commands were entered on a router: Router(config)# access-list 2 deny 172.16.5.24 Router(config)# access-list 2 permit any The ACL is correctly applied to an interface. What can be concluded about this set of commands? The wildcard mask 0.0.0.0 is assumed. The access list statements are misconfigured. …