Category: CCNA Security 2.0 Labs
1.2.4.12 Lab – Social Engineering (Instructor Version) Instructor Note: Red font color or Gray highlights indicate text that appears in the instructor copy only. Objective In this lab, you will research examples of social engineering and identify ways to recognize and prevent it. Resources Computer with Internet Access …
0.0.0.0 Lab – Instructor Lab Using ASA 5506-X (Instructor Version) Note: ISR G1 devices use FastEthernet interfaces instead of GigabitEthernet interfaces. IP Addressing Table Device Interface IP Address Subnet Mask Default Gateway Switch Port R1 G0/0 209.165.200.225 255.255.255.248 N/A ASA G1/1 R1 S0/0/0 (DCE) 10.1.1.1 255.255.255.252 N/A N/A …
0.0.0.0 Lab – Instructor Lab Using ASA 5505 (Instructor Version) Topology Note: ISR G1 devices use FastEthernet interfaces instead of GigabitEthernet interfaces. IP Addressing Table Device Interface IP Address Subnet Mask Default Gateway Switch Port R1 G0/0 209.165.200.225 255.255.255.248 N/A ASA E0/0 S0/0/0 (DCE) 10.1.1.1 255.255.255.252 N/A N/A R2 …
Packet Tracer – Skills Integration Challenge Topology Addressing Table Objectives • Configure basic router security • Configure basic switch security • Configure AAA local authentication • Configure SSH • Secure against login attacks • Configure site-to-site IPsec VPNs • Configure firewall and IPS settings • Configure ASA …
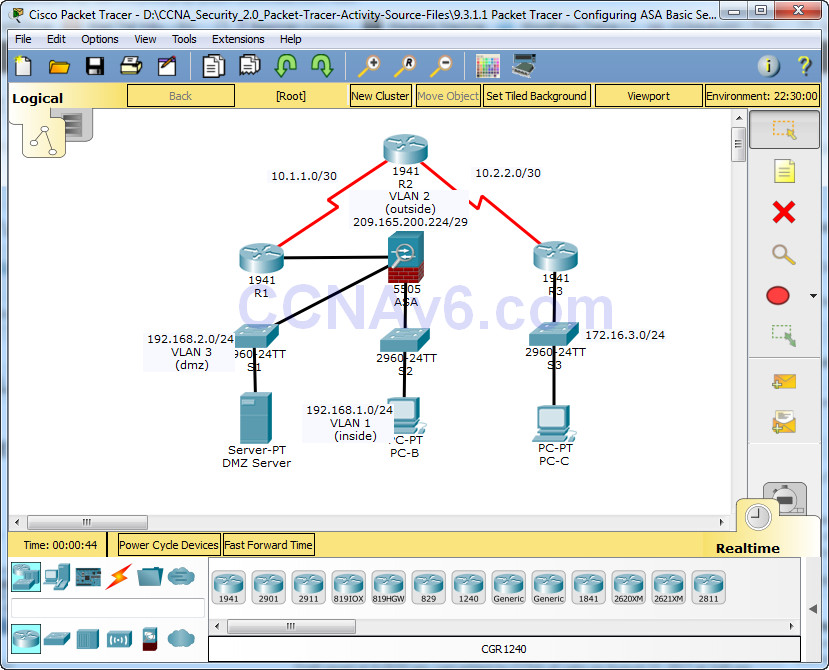
Packet Tracer – Configuring ASA Basic Settings and Firewall Using CLI Topology IP Addressing Table Objectives • Verify connectivity and explore the ASA • Configure basic ASA settings and interface security levels using CLI • Configure routing, address translation, and inspection policy using CLI • Configure DHCP, …
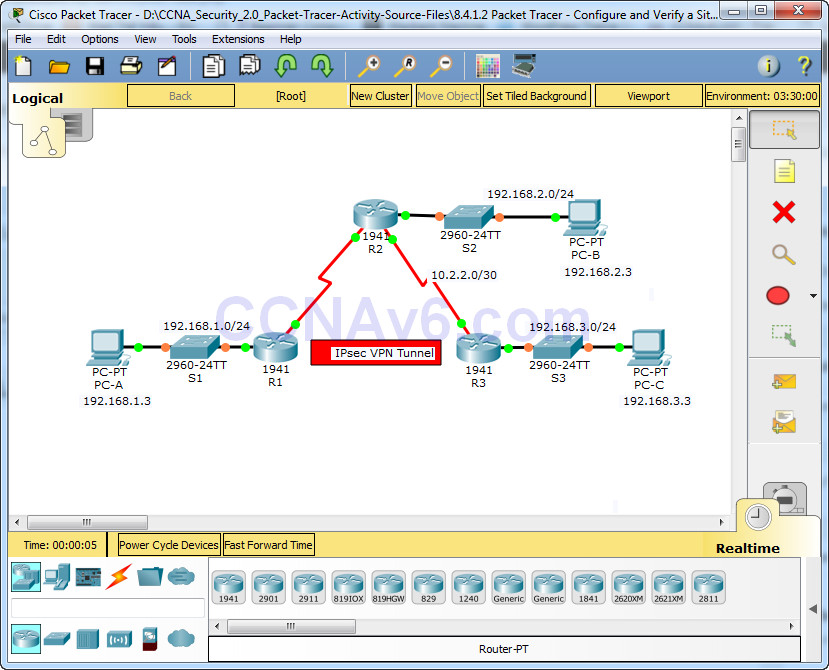
Packet Tracer – Configure and Verify a Site-to-Site IPsec VPN Using CLI Topology Addressing Table Objectives • Verify connectivity throughout the network. • Configure R1 to support a site-to-site IPsec VPN with R3. Background / Scenario The network topology shows three routers. Your task is to configure …
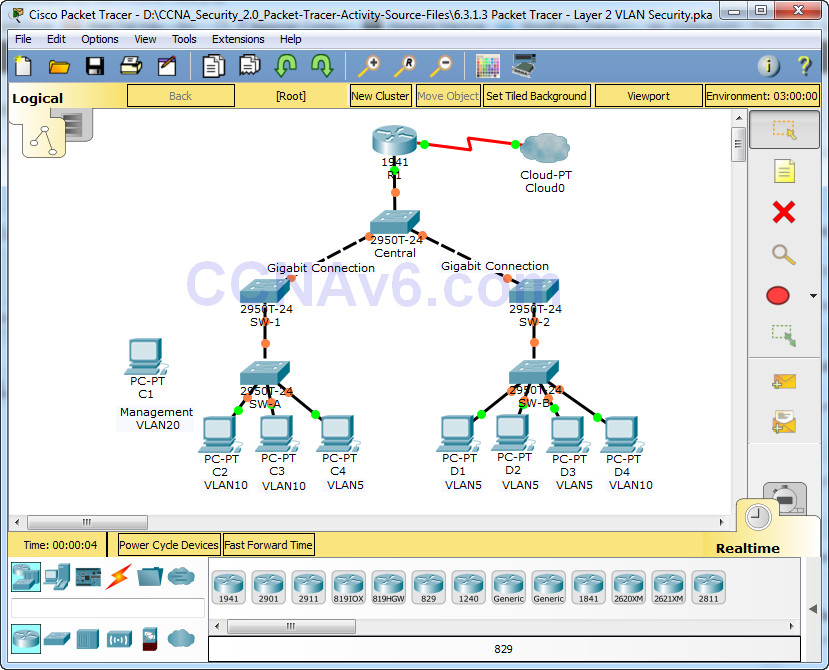
Packet Tracer – Layer 2 VLAN Security Topology Objectives • Connect a new redundant link between SW-1 and SW-2. • Enable trunking and configure security on the new trunk link between SW-1 and SW-2. • Create a new management VLAN (VLAN 20) and attach a management PC …
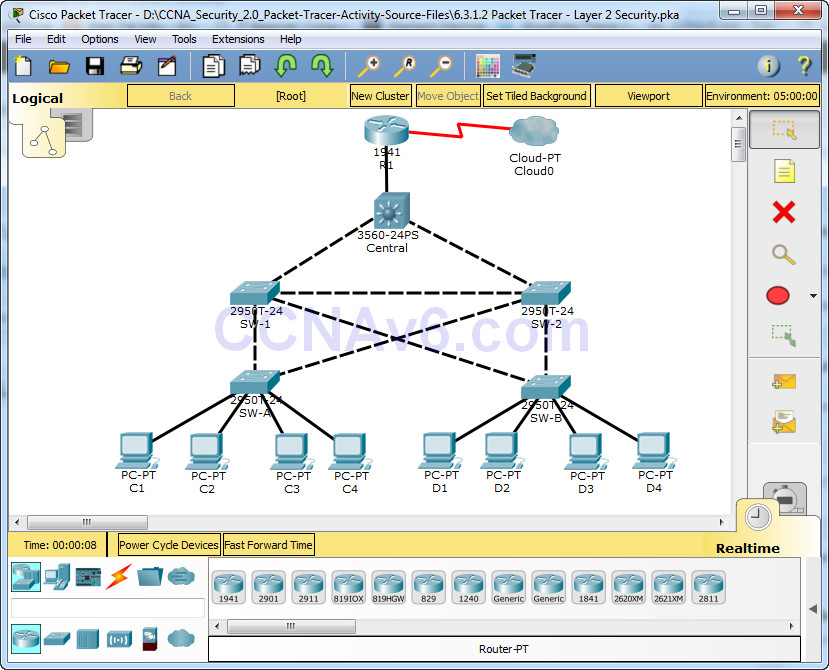
Packet Tracer – Layer 2 Security Topology Objectives • Assign the Central switch as the root bridge. • Secure spanning-tree parameters to prevent STP manipulation attacks. • Enable port security to prevent CAM table overflow attacks. Background / Scenario There have been a number of attacks on …
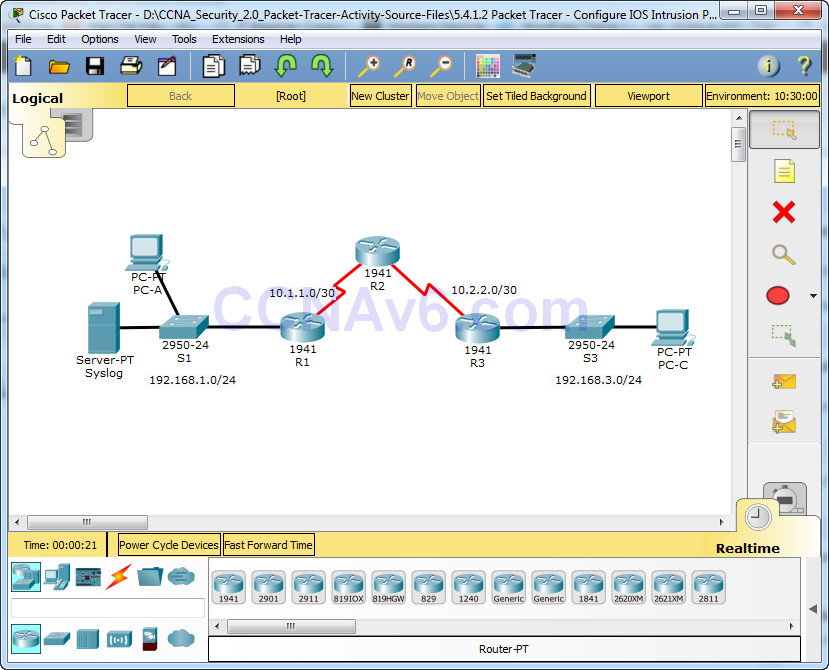
Packet Tracer – Configure IOS Intrusion Prevention System (IPS) Using the CLI Topology Addressing Table Objectives • Enable IOS IPS. • Configure logging. • Modify an IPS signature. • Verify IPS. Background / Scenario Your task is to enable IPS on R1 to scan traffic entering the …
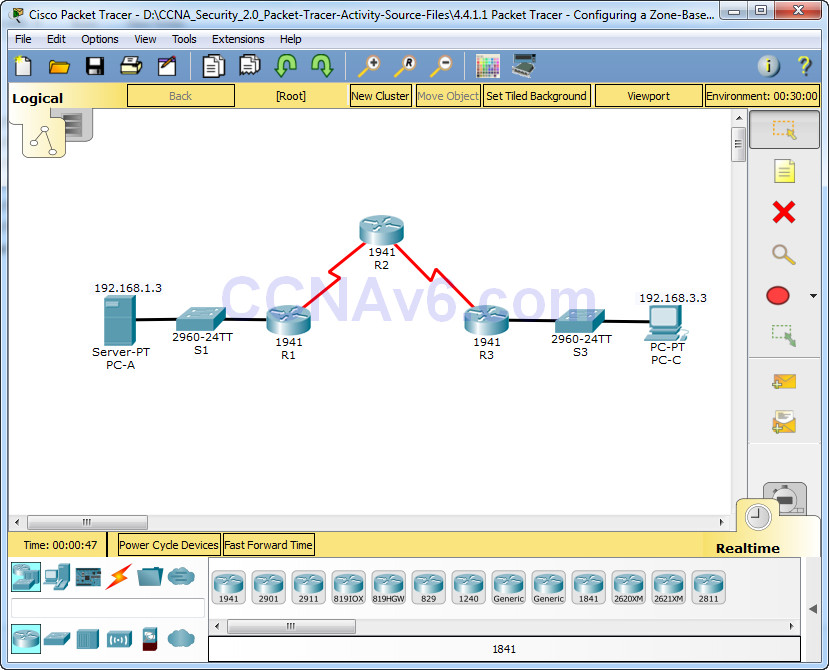
Packet Tracer – Configuring a Zone-Based Policy Firewall (ZPF) Topology Addressing Table Objectives • Verify connectivity among devices before firewall configuration. • Configure a zone-based policy (ZPF) firewall on R3. • Verify ZPF firewall functionality using ping, SSH, and a web browser. Background/Scenario ZPFs are the latest …