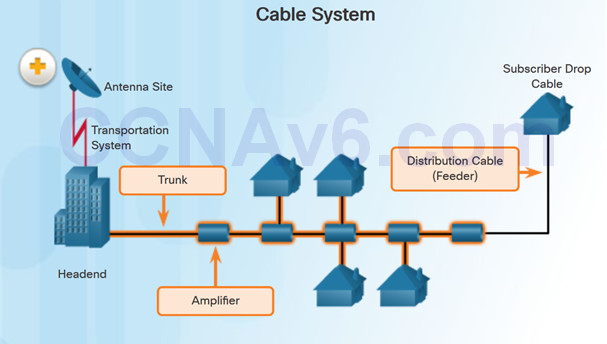
Instructor Planning Guide
Activities
What activities are associated with this chapter?
Assessment
Students should complete Chapter 3, “Assessment” after completing Chapter 3.
Quizzes, labs, Packet Tracers and other activities can be used to informally assess student progress.
Sections & Objectives
3.1 Remote Access Connections
Select broadband remote access technologies to support business requirements.
Compare remote access broadband connection options for small to medium-sized businesses.
Select an appropriate broadband connection for a given network requirement.
3.2 PPPoE
Configure a Cisco router with PPPoE.
Explain how PPPoE operates.
Implement a basic PPPoE connection on a client router.
3.3 VPNs
Explain how VPNs secure site-to-site and remote access connectivity.
Describe benefits of VPN technology.
Describe site-to-site and remote access VPNs.
3.4 GRE
Implement a GRE tunnel.
Explain the purpose and benefits of GRE tunnels.
Troubleshoot a site-to-site GRE tunnel.
3.5 eBGP
Implement eBGP in a single-homed remote access network.
Describe basic BGP features.
Explain BGP design considerations.
Configure an eBGP branch connection.
Chapter 3: Branch Connections
3.1 – Remote Access Connections
3.1.1 – Broadband Connections
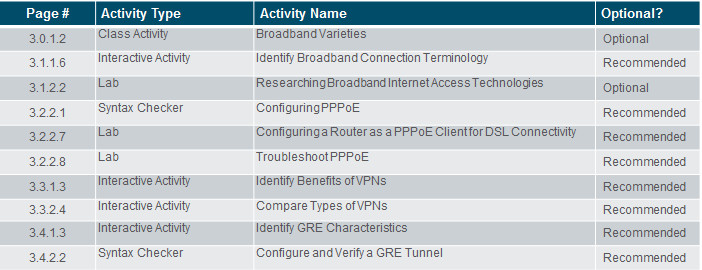
3.1.1.1 – What is a Cable System?
Cable system uses a coaxial cable that carries radio frequency (RF) signals across the network.
Cable systems provide high-speed Internet access, digital cable television, and residential telephone service.
Use hybrid fiber-coaxial (HFC) networks to enable high-speed transmission of data.
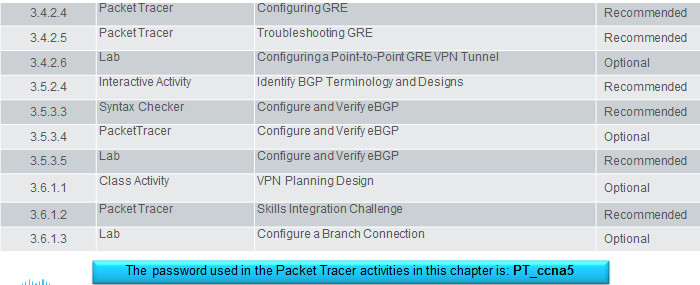
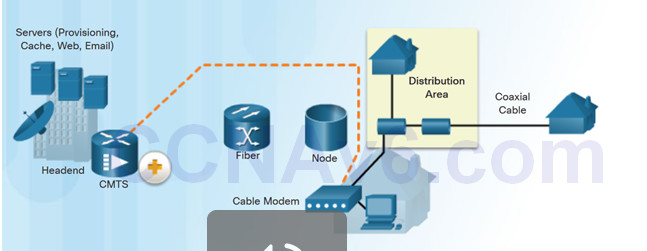
3.1.1.2 – Cable Components
Two types of equipment are required to send signals upstream and downstream on a cable system:
- Cable Modem Termination System (CMTS) at the headend of the cable operator. The headend is a router with databases for providing Internet services to cable subscribers.
- Cable Modem (CM) on the subscriber end.
3.1.1.3 – What is DSL?
- Digital Subscriber Line (DSL) is a means of providing high-speed connections over installed copper wires.
- Asymmetric DSL (ADSL) provides higher downstream bandwidth to the user than upload bandwidth.
- Symmetric DSL (SDSL) provides the same capacity in both directions.
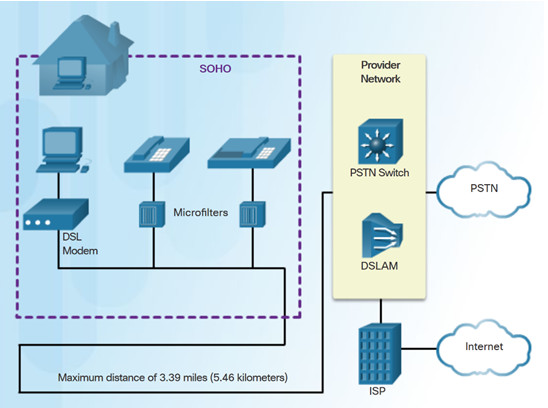
- For satisfactory ADSL service, the local loop length must be less than 3.39 miles (5.46 km).
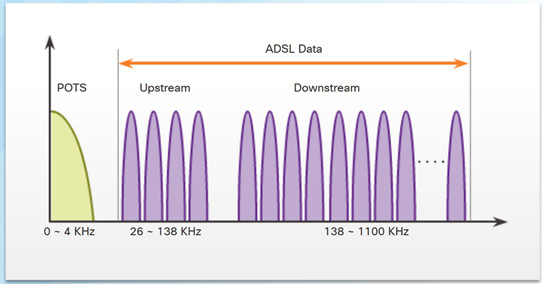
The figure shows a representation of bandwidth space allocation on a copper wire for ADSL. POTS (Plain Old Telephone System) identifies the frequency range used by the voice-grade telephone service. The area labeled ADSL represents the frequency space used by the upstream and downstream DSL signals.
3.1.1.4 – DSL Connections
The DSL connection is set up between the customer premises equipment (CPE) and the DSL access multiplexer (DSLAM) device located at the Central Office (CO).
Key components in the DSL connection:
- Transceiver – Usually a modem in a router which connects the computer of the teleworker to the DSL.
- DSLAM – Located at the CO of the carrier, it combines individual DSL connections from users into one high-capacity link to an ISP.
Advantage of DSL over cable technology is that DSL is not a shared medium. Each user has a separate direct connection to the DSLAM.
3.1.1.5 – Wireless Connection
Three main broadband wireless technologies:
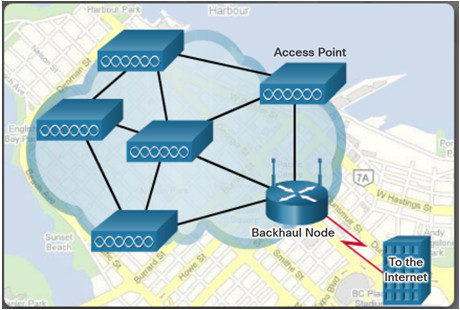
- Municipal Wi-Fi – Most municipal wireless networks use a mesh of interconnected access points as shown in figure.
- Cellular/mobile – Mobile phones use radio waves to communicate through nearby cell towers. Cellular speeds continue to increase. LTE Category 10 supports up to 450 Mb/s download and 100 Mb/s upload.
- Satellite Internet – Used in locations where land-based Internet access is not available. Primary installation requirement is for the antenna to have a clear view toward the equator.
Note: WiMAX has largely been replaced by LTE for mobile access, and cable or DSL for fixed access.
3.1.2 – Select a Broadband Connection
3.1.2.1 – Comparing Broadband Solutions
Factors to consider in selecting a broadband solution:
- Cable – Bandwidth shared by many users, slow data rates during high-usage hours.
- DSL – Limited bandwidth that is distance sensitive (in relation to the ISP’s central office).
- Fiber-to-the-Home – Requires fiber installation directly to the home.
- Cellular/Mobile – Coverage is often an issue.
- Wi-Fi Mesh – Most municipalities do not have a mesh network deployed.
- Satellite – Expensive, limited capacity per subscriber

3.1.2.2 – Lab – Researching Broadband Internet Access Technologies
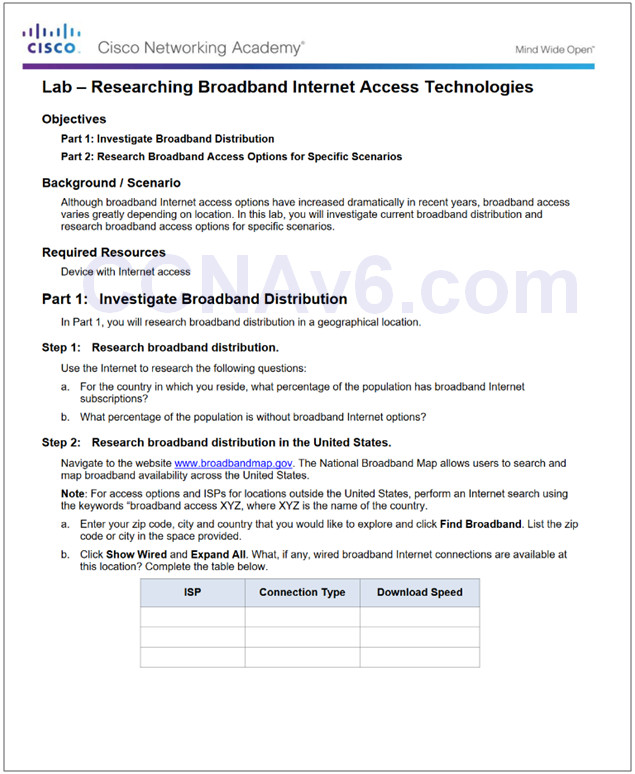
3.1.2.2 Lab – Researching Broadband Internet Access Technologies
3.2 – PPPoE
3.2.1 – PPPoE Overview
3.2.1.1 – PPPoE Motivation
PPP can be used on all serial links including those links created with dial-up analog and ISDN modems.
ISPs often use PPP as the data link protocol over broadband connections.
- ISPs can use PPP to assign each customer one public IPv4 address.
- PPP supports CHAP authentication.
Ethernet links do not natively support PPP.
- PPP over Ethernet (PPPoE) provides a solution to this problem.
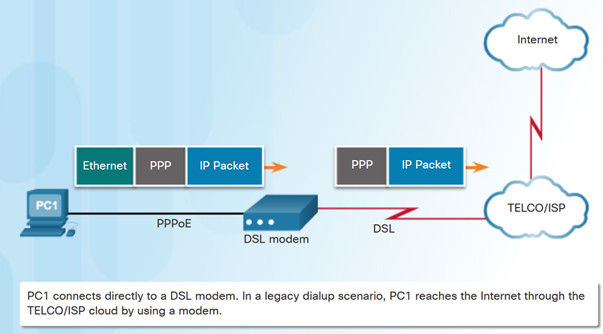
PPP Frames Over An Ethernet Connection
3.2.1.2 – PPPoE Concepts
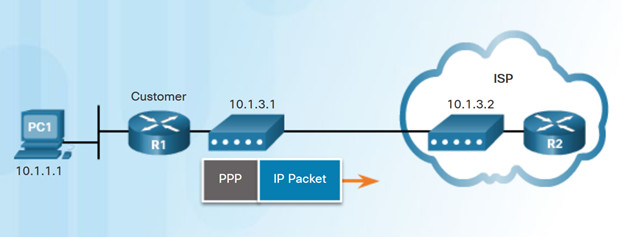
PPPoE creates a PPP tunnel over an Ethernet connection.
This allows PPP frames to be sent across the Ethernet cable to the ISP from the customer’s router.
3.2.2 – Implement PPPoE
3.2.2.1 – PPPoE Configuration
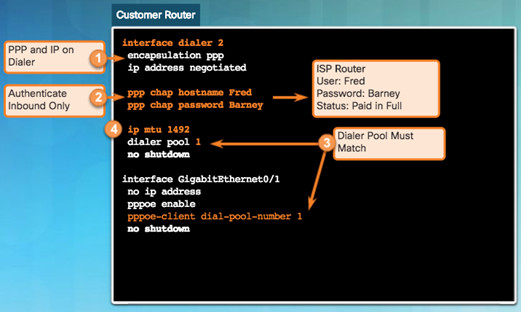
To create the PPP tunnel a dialer interface is configured.
- Use interface dialer number command
The PPP CHAP is then configured. Use ppp chap hostname name and ppp chap password password.
The physical Ethernet interface connected to the DSL modem is enabled with the command pppoe enable interface configuration command.
Dialer interface is linked to the Ethernet interface with the dialer pool and pppoe-client interface configuration commands.
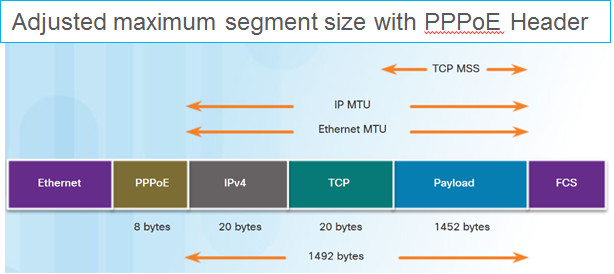
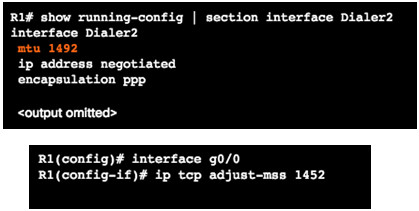
The MTU should be set to 1492 to accommodate PPPoE headers.
3.2.2.2 – PPPoE Verification
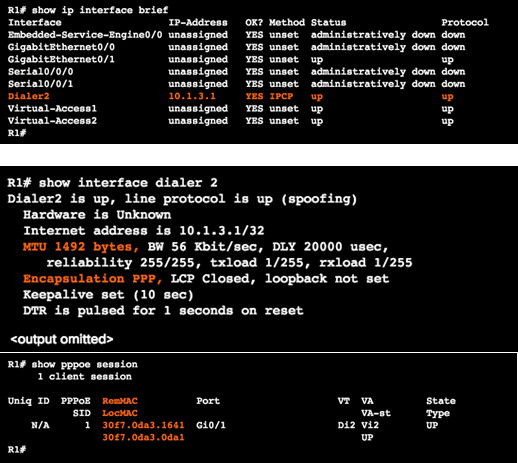
Use the following commands to verify PPPoE:
- show ip interface brief – verify the IPv4 address automatically assigned.
- show interface dialer – verifies the MTU and PPP encapsulation.
- show ip route
- show pppoe session – displays information about currently active PPPoE sessions.
3.2.2.3 – PPPoE Troubleshooting
The following are possible causes of problems with PPPoE:
- Failure in the PPP negotiation process
- Failure in the PPP authentication process
- Failure to adjust the TCP maximum segment size

3.2.2.4 – PPPoE Negotiation
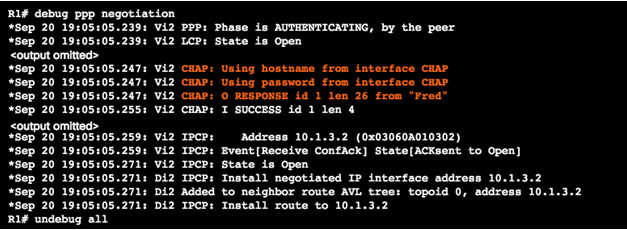
Use the debug ppp negotiation command to verify PPP negotiation.
Four possible points of failure in PPP negotiation:
- No response from the remote device.
- Link Control Protocol (LCP) not open.
- Authentication failure.
- IP Control Protocol (IPCP) failure.
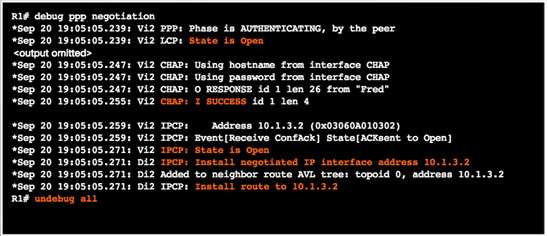
3.2.2.5 – PPPoE Authentication
Verify that the CHAP username and password are correct using debug ppp negotiation command.
3.2.2.6 – PPPoE MTU Size
PPPoE supports an MTU of only 1492 bytes in order to accommodate the additional 8-byte PPPoE header.
Use show running-config command to verify PPPoE MTU.
The ip tcp adjust-mss max-segment-size interface command prevents TCP sessions from being dropped by adjusting the MSS value during the TCP 3-way handshake.
3.2.2.7 – Lab – Configuring a Router as a PPPoE Client for DSL Connectivity
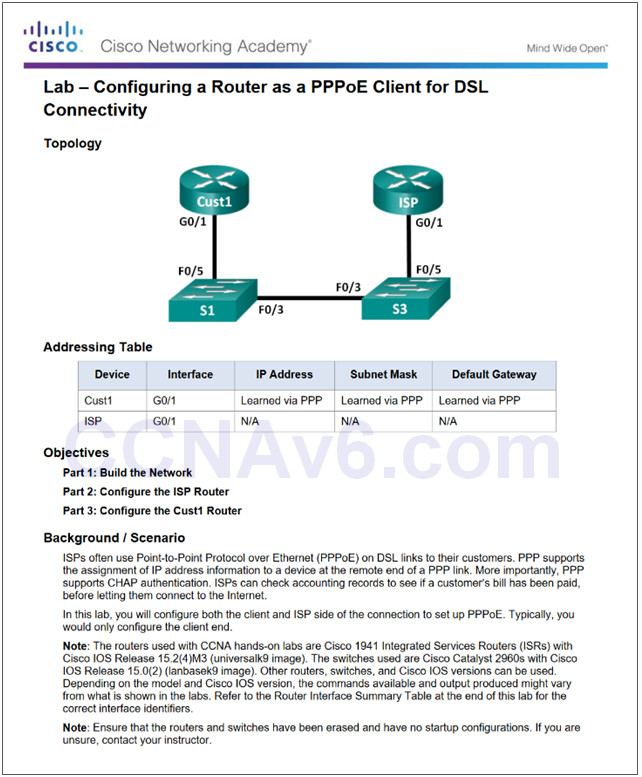
3.2.2.7 Lab – Configuring a Router as a PPPoE Client for DSL Connectivity
3.2.2.8 – Lab – Troubleshoot PPPoE
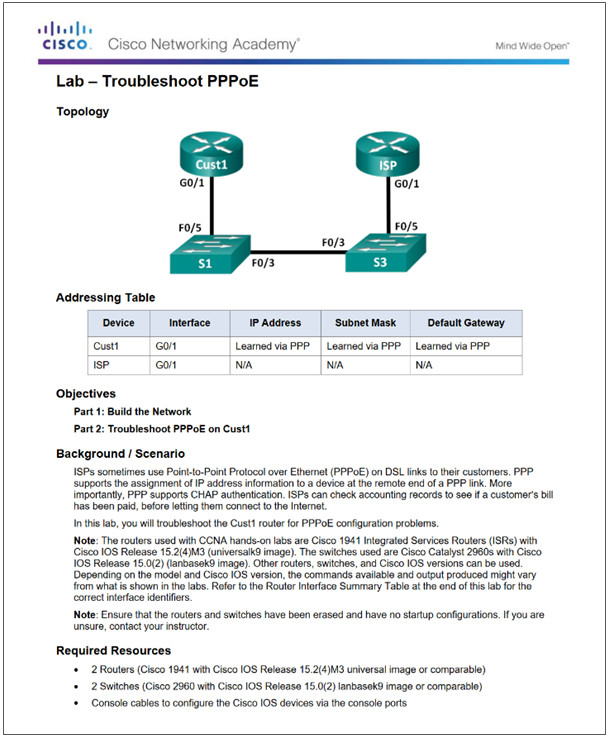
3.2.2.8 Lab – Troubleshoot PPPoE
3.3 – VPNs
3.3.1 – Fundamentals of VPNs
3.3.1.1 – Introducing VPNs
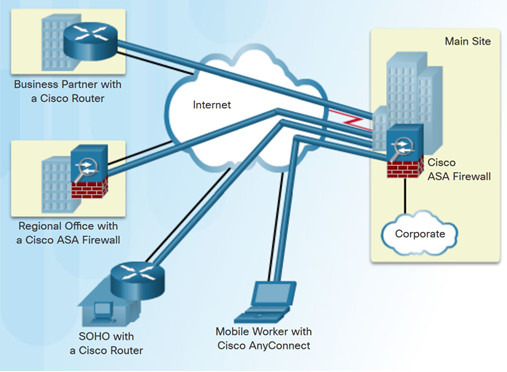
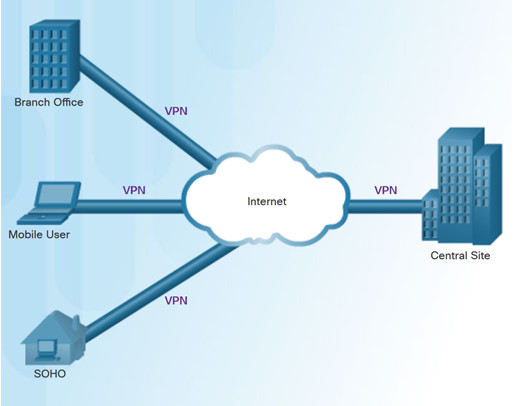
A VPN is a private network created via tunneling over a public network, usually the Internet.
A secure implementation of VPN with encryption, such as IPsec VPNs, is what is usually meant by virtual private networking.
To implement VPNs, a VPN gateway is necessary – could be a router, a firewall, or a Cisco Adaptive Security Appliance (ASA).
3.3.1.2 – Benefits of VPNs
The benefits of a VPN include the following:
- Cost savings – VPNs enable organizations to use cost-effective, high-bandwidth technologies, such as DSL to connect remote offices and remote users to the main site.
- Scalability – Organizations are able to add large amounts of capacity without adding significant infrastructure.
- Compatibility with broadband technology – Allow mobile workers and telecommuters to take advantage of high-speed, broadband connectivity.
- Security – VPNs can use advanced encryption and authentication protocols.
3.3.2 –Types of VPNs
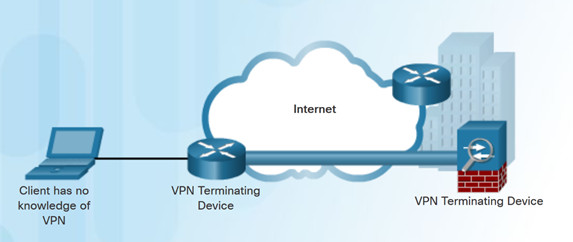
3.3.2.1 – Site-to-Site VPNs
Site-to-site VPNs connect entire networks to each other, for example, connecting a branch office network to a company headquarters network.
In a site-to-site VPN, end hosts send and receive normal TCP/IP traffic through a VPN “gateway”.
The VPN gateway is responsible for encapsulating and encrypting outbound traffic.
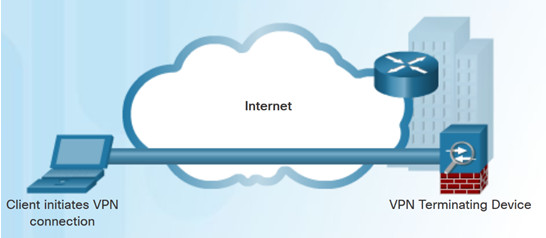
3.3.2.2 – Remote Access VPNs
A remote-access VPN supports the needs of telecommuters, mobile users, and extranet traffic.
Allows for dynamically changing information, and can be enabled and disabled.
Used to connect individual hosts that must access their company network securely over the Internet.
VPN client software may need to be installed on the mobile user’s end device.
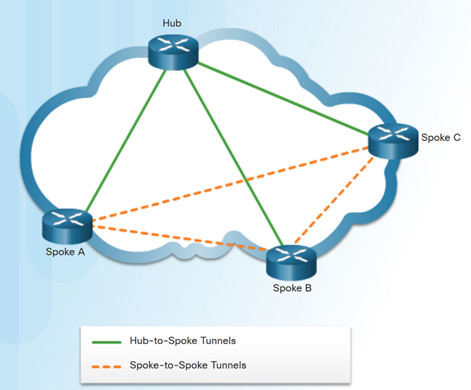
3.3.2.3 – DMVPN
Dynamic Multipoint VPN (DMVPN) is a Cisco software solution for building multiple VPNs.
DMVPN is built using the following technologies:
- Next Hop Resolution Protocol (NHRP) – NHRP creates a distributed mapping database of public IP addresses for all tunnel spokes.
- Multipoint Generic Routing Encapsulation (mGRE) tunnels – An mGRE tunnel interface allows a single GRE interface to support multiple IPsec tunnels.
- IP Security (IPsec) encryption – provides secure transport of private information over public networks.
3.4 – GRE
3.4.1 –GRE Overview
3.4.1.1 – GRE Introduction
Generic Routing Encapsulation (GRE) is a non-secure, site-to-site VPN tunneling protocol.
Developed by Cisco.
GRE manages the transportation of multiprotocol and IP multicast traffic between two or more sites
A tunnel interface supports a header for each of the following:
- An encapsulated protocol – or passenger protocol, such as IPv4, IPv6.
- An encapsulation protocol – or carrier protocol, such as GRE.
- A transport delivery protocol, such as IP.
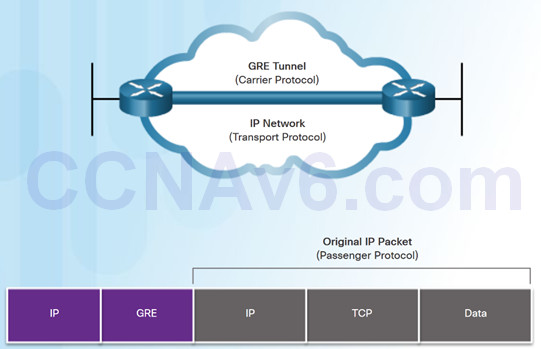
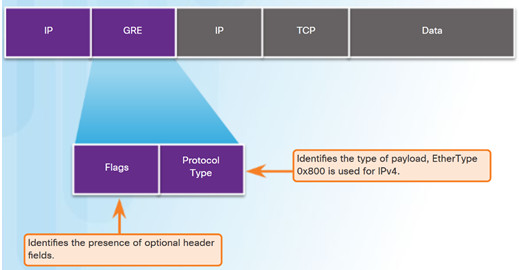
3.4.1.2 – GRE Characteristics
- GRE is defined as an IETF standard (RFC 2784).
- In the outer IP header, 47 is used in the protocol field.
- GRE encapsulation uses a protocol type field in the GRE header to support the encapsulation of any OSI Layer 3 protocol.
- GRE is stateless.
- GRE does not include any strong security mechanisms.
- GRE header, together with the tunneling IP header, creates at least 24 bytes of additional overhead for tunneled packets.
3.4.2 –Implement GRE
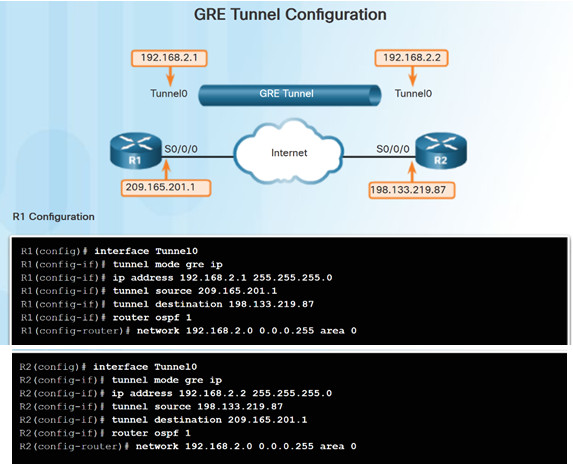
3.4.2.1 – Configure GRE
Five steps to configuring a GRE tunnel:
- Step 1. Create a tunnel interface using the interface tunnel number command.
- Step 2. Configure an IP address for the tunnel interface. (Usually a private address)
- Step3. Specify the tunnel source IP address.
- Step 4. Specify the tunnel destination IP address.
- Step 5. (Optional) Specify GRE tunnel mode as the tunnel interface mode.
Note: The tunnel source and tunnel destination commands reference the IP addresses of the preconfigured physical interfaces.
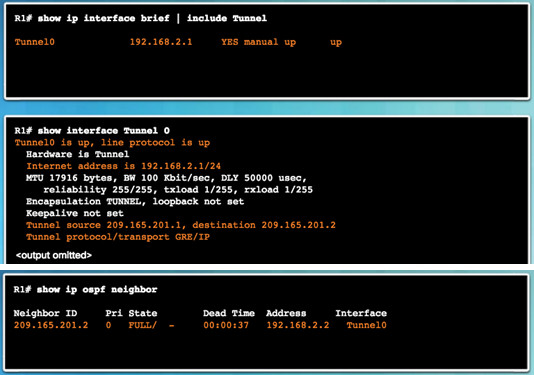
3.4.2.2 – Verify GRE
- Use the show ip interface brief command to verify that the tunnel interface is up.
- Use the show interface tunnel command to verify the state of the tunnel.
- Use the show ip ospf neighbor command to verify that an OSPF adjacency has been established over the tunnel interface.
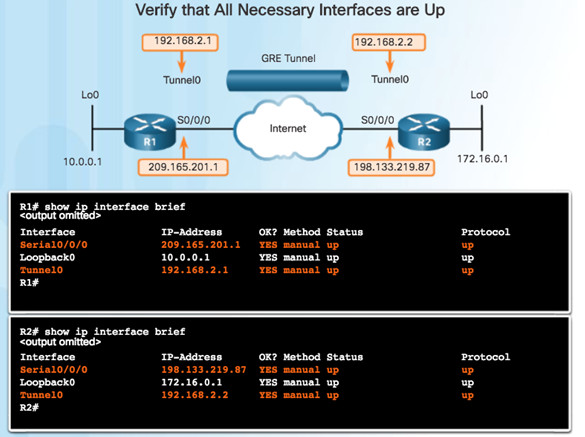
3.4.2.3 – Troubleshoot GRE
Issues with GRE are usually due to one or more of the following:
- The tunnel interface IP addresses are not on the same network or the subnet masks do not match. Use the show ip interface brief command.
- The interfaces for the tunnel source and/or destination are not configured with the correct IP address or are down. Use the show ip interface brief command.
- Static or dynamic routing is not properly configured. Use show ip route or show ip ospf neighbor.
3.4.2.4 – Packet Tracer – Configuring GRE
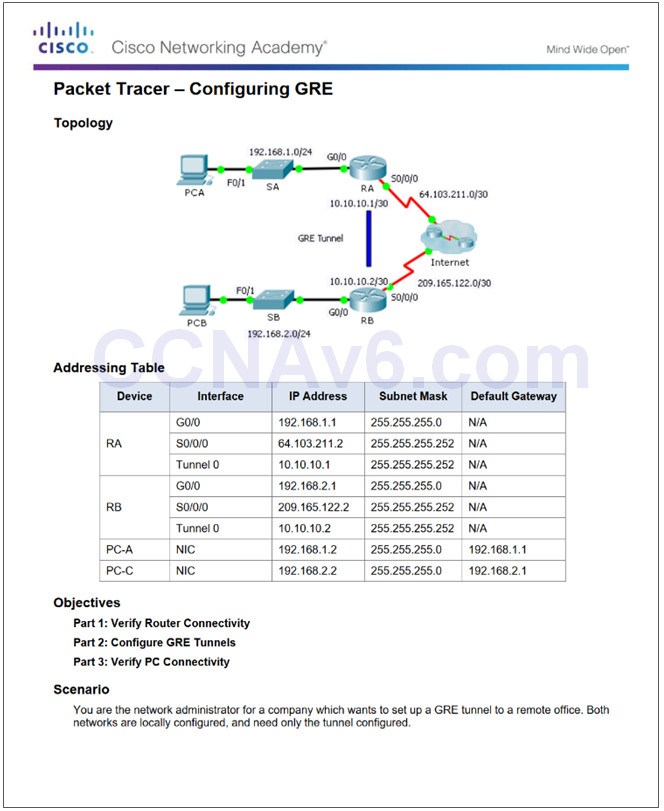
3.4.2.4 Packet Tracer – Configuring GRE
3.4.2.5 – Packet Tracer – Troubleshooting GRE
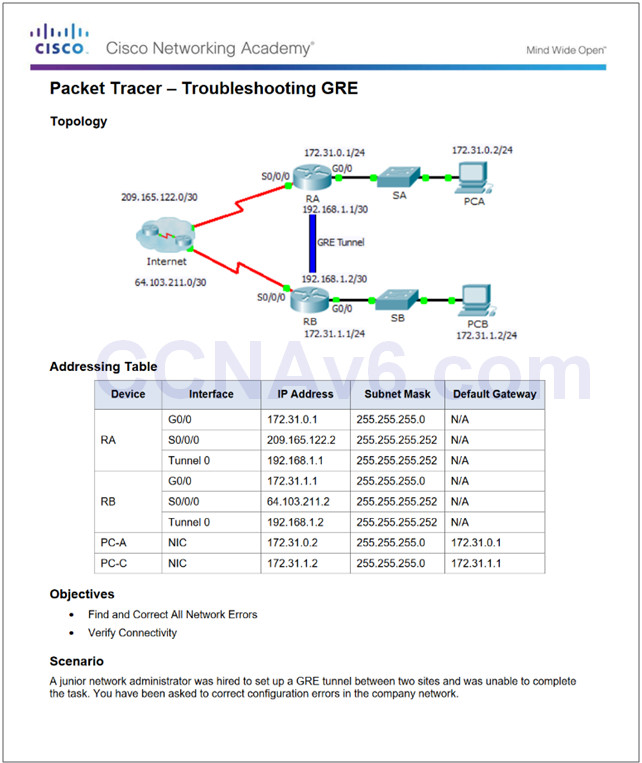
3.4.2.5 Packet Tracer – Troubleshooting GRE
3.4.2.6 – Lab – Configuring a Point-to-Point GRE VPN Tunnel
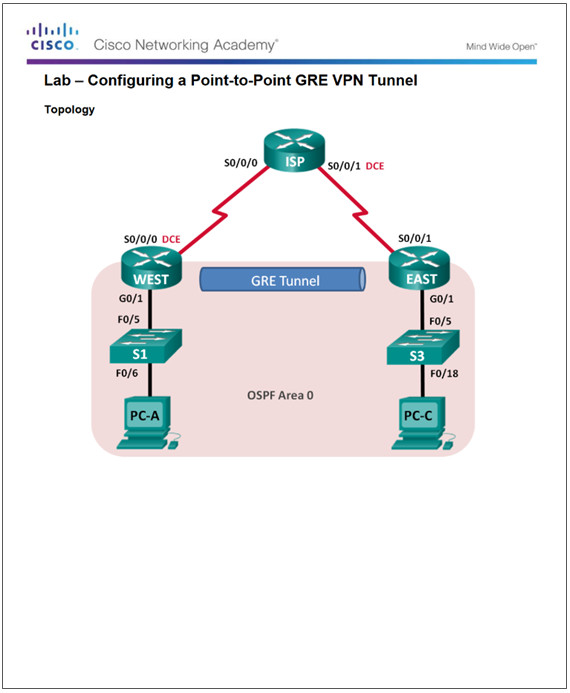
3.4.2.6 Lab – Configuring a Point-to-Point GRE VPN Tunnel
3.5 – eBGP
3.5.1 –BGP Overview
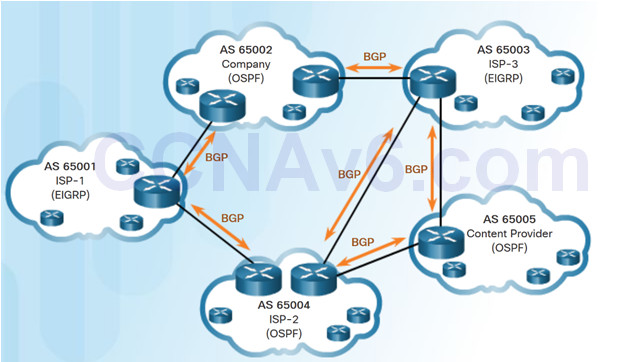
3.5.1.1 – IGP and EGP Routing Protocols
IGPs are used to exchange routing information within a company network or an autonomous system (AS).
An Exterior Gateway Protocol (EGP) is used for the exchange of routing information between autonomous systems, such as ISPs.
Border Gateway Protocol (BGP) is an Exterior Gateway Protocol (EGP).
- Every AS is assigned a unique 16-bit or 32-bit AS number which uniquely identifies it on the Internet.
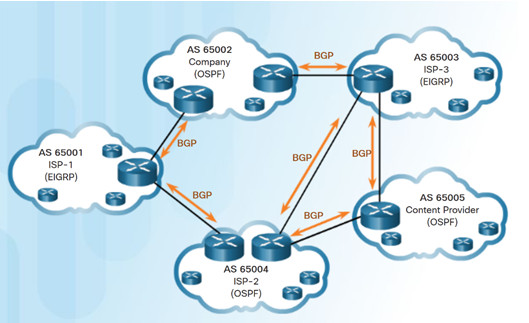
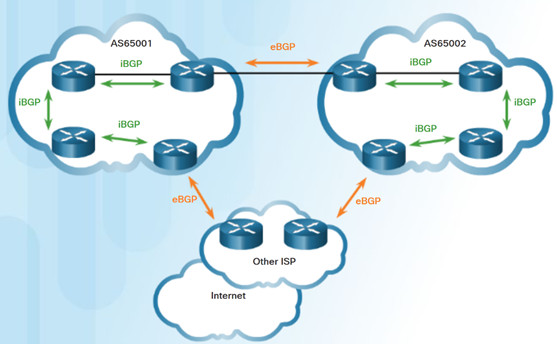
3.5.1.2 – eBGP and iBGP
External BGP (eBGP) – External BGP is the routing protocol used between routers in different autonomous systems.
Internal BGP (iBGP) – Internal BGP is the routing protocol used between routers in the same AS.
Two routers exchanging BGP routing information are known as BGP peers
3.5.2 –BGP Design Considerations
3.5.2.1 – When to use BGP
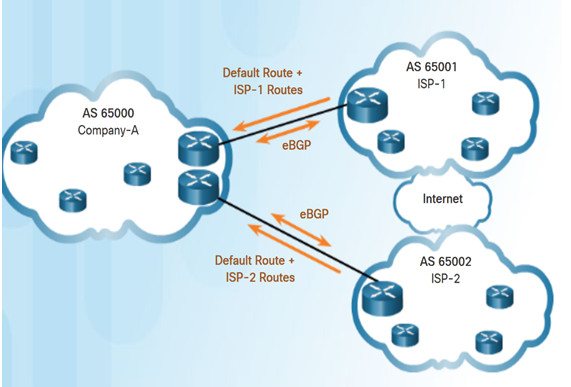
- BGP is used when an AS has connections to multiple autonomous systems. This is known as multi-homed.
- A misconfiguration of a BGP router could have negative effects throughout the Internet.
3.5.2.2 – When not to use BGP
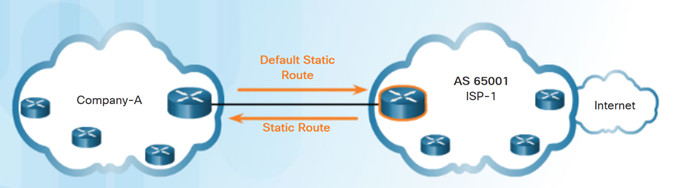
BGP should not be used when one of the following conditions exist:
- There is a single connection to the Internet or another AS. Known as single-homed.
- When there is a limited understanding of BGP.
Note: Although it is recommended only in unusual situations, for the purposes of this course, you will configure single-homed BGP.
3.5.2.3 – BGP Options
Three common ways an organization can implement BGP in a multi-homed environment:
- Default Route Only
- Default Route and ISP Routes
- All Internet Routes (this would include
routes to over 550,000 networks)
3.5.3 –eBGP Branch Configuration
3.5.3.1 – Steps to Configure eBGP
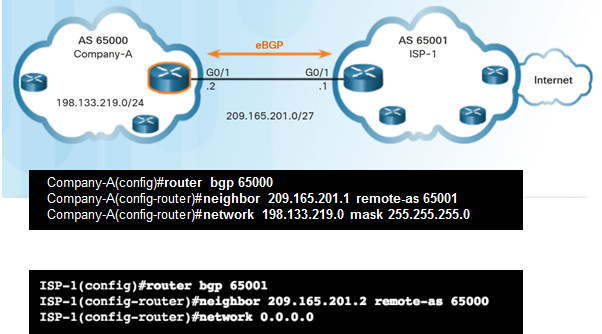
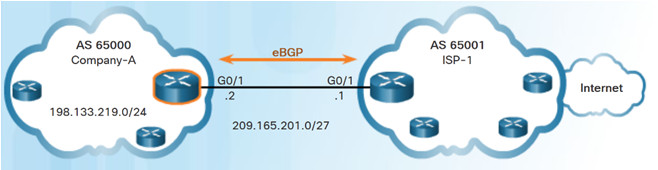
To implement eBGP:
- Enable BGP routing.
- Configure BGP neighbor(s) (peering)
- Advertise network(s) originating from this AS.
3.5.3.2 – BGP Sample Configuration
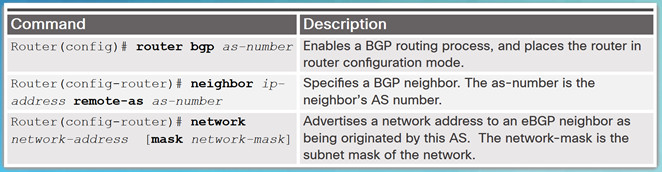
- The router bgp as–number global configuration command enables BGP and identifies the AS number.
- The neighbor ip-address remote-as as-number router configuration command identifies the BGP peer and its AS number.
- The network network-address [mask network-mask] router configuration command enters the network-address into the local BGP table.
Note: The network-address used in the network command does not have to be a directly connected network.
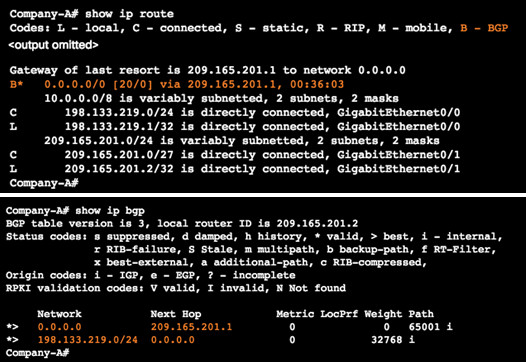
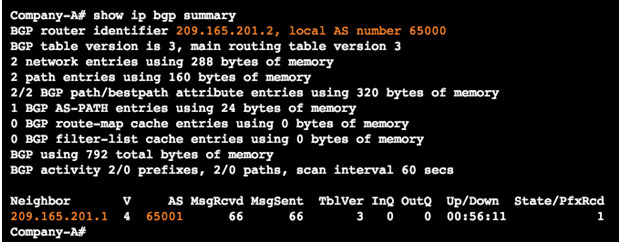
3.5.3.3 – Verify eBGP
Three commands to verify eBGP:
- show ip route
- show ip bgp
- show ip bgp summary
3.5.3.4 – Packet Tracer – Configure and Verify eBGP
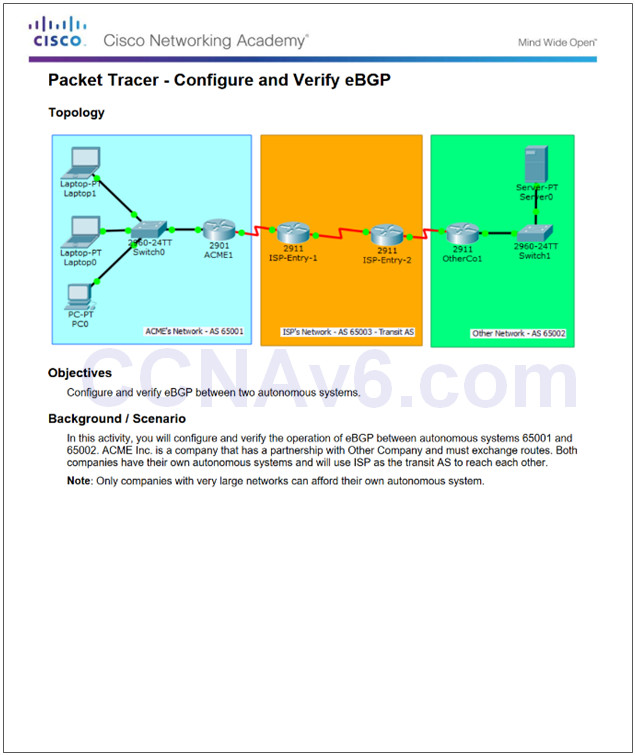
3.5.3.4 Packet Tracer – Configure and Verify eBGP
3.5.3.5 – Lab – Configure and Verify eBGP
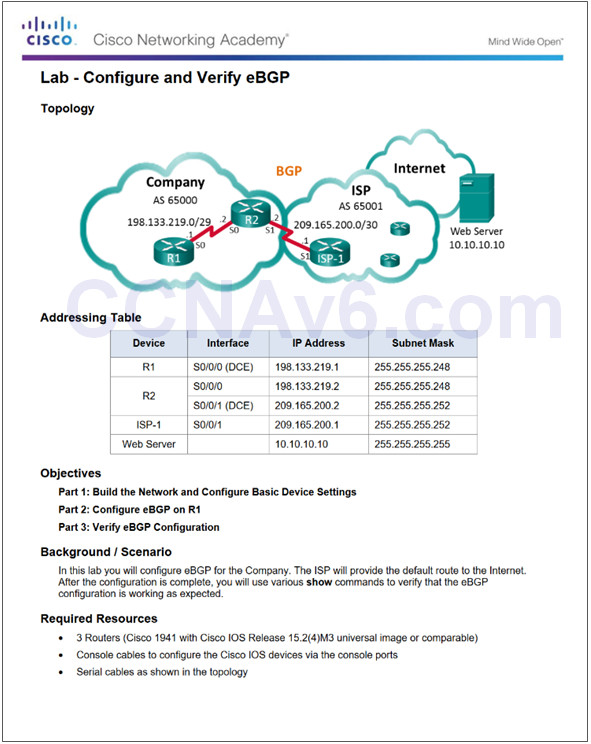
3.5.3.5 Lab – Configure and Verify eBGP
3.6 – Summary
3.6.1 – Conclusion
3.6.1.1 Class Actvity – VPN Planning Design
3.6.1.1 Class Actvity – VPN Planning Design
3.6.1.2 – Packet Tracer – Skills Integration Challenge
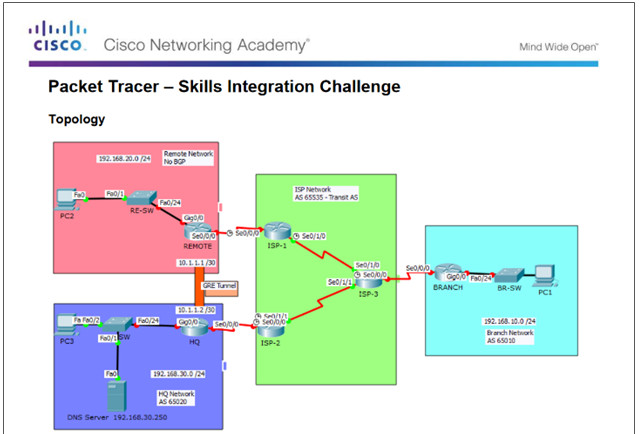
3.6.1.2 Packet Tracer – Skills Integration Challenge
3.6.1.3 – Lab – Configure a Branch Connection
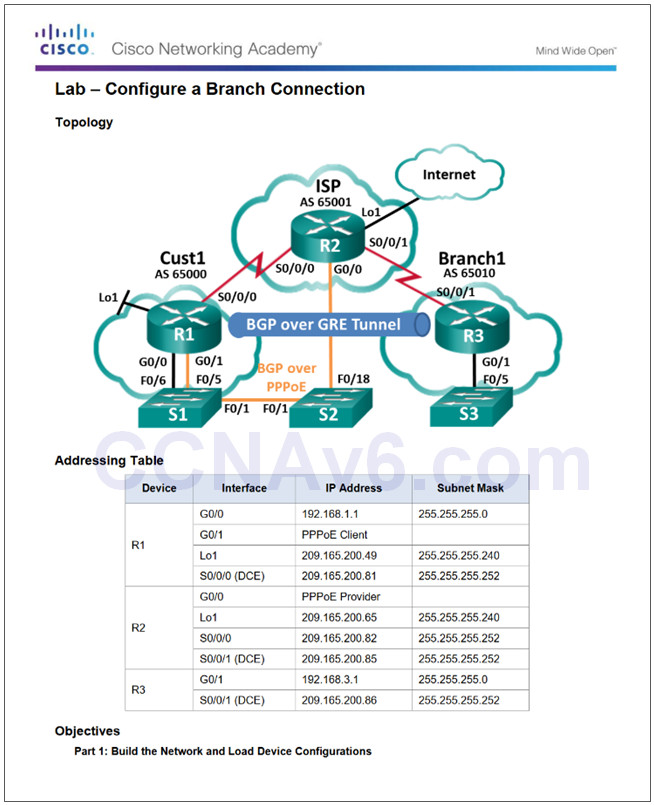
3.6.1.3 Lab – Configure a Branch Connection
3.6.1.4 – Chapter 3: Branch Connections
- Select broadband remote access technologies to support business requirements.
- Configure a Cisco router with PPPoE.
- Explain how VPNs secure site-to-site and remote access connectivity.
- Implement a GRE tunnel.
- Implement eBGP in a single-homed remote access network.
New Terms and Commands
| •PPP over Ethernet (PPPoE)
•Internet Protocol Security (IPsec) •Border Gateway Protocol (BGP) •radio frequency (RF) •hybrid fiber-coaxial (HFC) •Data over Cable Service Interface Specification (DOCSIS) •Antenna Site •Transportation Network •distribution network •central office (co) •Amplifier •Subscriber Drop •Node •downstream |
•upstream
•Asymmetric DSL (ADSL) •symmetric DSL (SDSL) •DSL Transceiver •DSL micro filter •Cellular/mobile •dialer interface •maximum transmission unit (MTU) •maximum segment size (MSS) •VPN gateway •telecommuters •VPN client software •Cisco AnyConnect Secure Mobility Client •Dynamic Multipoint VPN (DMVPN) •Next Hop Resolution Protocol (NHRP) |
| •Next Hop Server (NHS)
•Next Hop Clients (NHCs) •spoke-to-spoke •Multipoint Generic Routing Encapsulation (mGRE) •Passenger protocol •Carrier protocol •Transport protocol •Secure Sockets Layer (SSL) •AS number (ASN) •path vector routing protocol •External BGP (eBGP) •Internal BGP (iBGP) |
•multi-homed
•single-homed •BGP peers •Network Address Translation (NAT) |
