Networking Devices and Initial Configuration Course Final Exam Answers
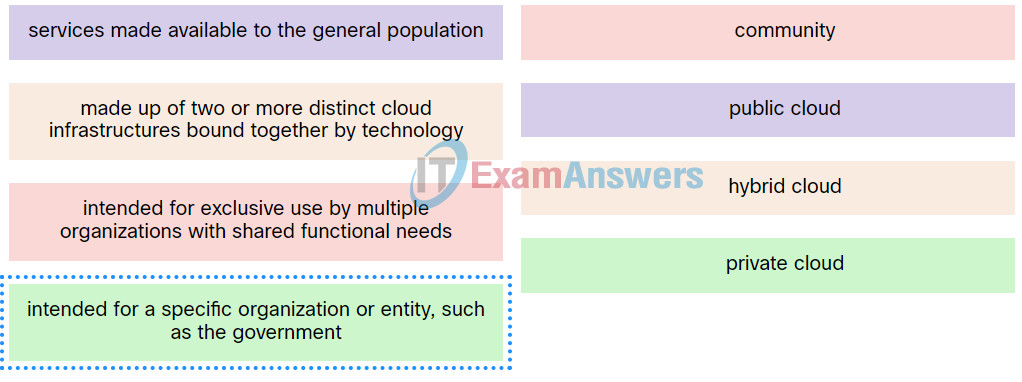
1. Match the definition to the type of cloud.
2. A data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?
- maintaining communication integrity
- online collaboration
- virtualization
- BYOD
3. What is an example of cloud computing?
- a service that offers on-demand access to shared resources
- a network infrastructure that spans a large geographic area
- an architectural style of the World Wide Web
- a continuous interaction between people, processes, data, and things
4. Which two scenarios would benefit the user the most by adding quality of service (QoS) to the network? (Choose two.)
- Students are updating information about their sport activities on the class Facebook page.
- A student is sending emails to a friend.
- A student is communicating via Skype with a friend in another country.
- Students are watching a lecture from a YouTube site.
5. An employee of a large corporation remotely logs into the company using the appropriate username and password. The employee is attending an important video conference with a customer concerning a large sale. It is important for the video quality to be excellent during the meeting. The employee is unaware that after a successful login, the connection to the company ISP failed. The secondary connection, however, activated within seconds. The disruption was not noticed by the employee or other employees.
What three network characteristics are described in this scenario? (Choose three.)
- scalability
- security
- integrity
- fault tolerance
- quality of service
- powerline networking
6. Which three statements describe the functions of the Cisco hierarchical network design model? (Choose three.)
- The goal of the core layer is maximizing throughput.
- The distribution layer distributes network traffic directly to end users.
- The distribution layer is responsible for traffic filtering and isolating failures from the core.
- The access layer provides a means of connecting end devices to the network.
- Route summarization is not necessary at the core and distribution layers.
- The core layer usually employs a star topology.
7. What is the key difference between a type 1 hypervisor and a type 2 hypervisor?
- A type 1 hypervisor runs directly on the system hardware and a type 2 hypervisor requires a host OS to run.
- A type 1 hypervisor supports server virtualizations and a type 2 hypervisor only supports workstation virtualization.
- A type 1 hypervisor supports all server OS virtualization and a type 2 hypervisor supports Linux and Mac virtualization.
- A type 1 hypervisor runs on specialized systems and a type 2 hypervisor runs on desktop computers.
8. Refer to the exhibit. Host A has sent a packet to host B. What will be the source MAC and IP addresses on the packet when it arrives at host B?
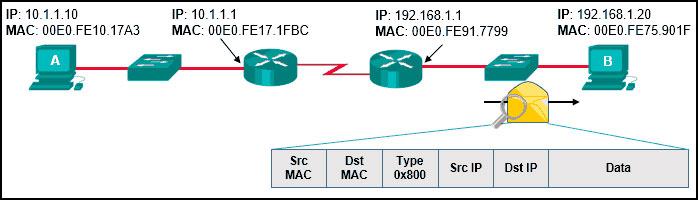
Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.10
Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.1
Source MAC: 00E0.FE10.17A3
Source IP: 10.1.1.10
Source MAC: 00E0.FE91.7799
Source IP: 192.168.1.1
Source MAC: 00E0.FE10.17A3
Source IP: 192.168.1.1
9. Which two statements are correct in a comparison of IPv4 and IPv6 packet headers? (Choose two.)
- The Time-to-Live field from IPv4 has been replaced by the Hop Limit field in IPv6.
- The Version field from IPv4 is not kept in IPv6.
- The Destination Address field is new in IPv6.
- The Source Address field name from IPv4 is kept in IPv6.
- The Header Checksum field name from IPv4 is kept in IPv6.
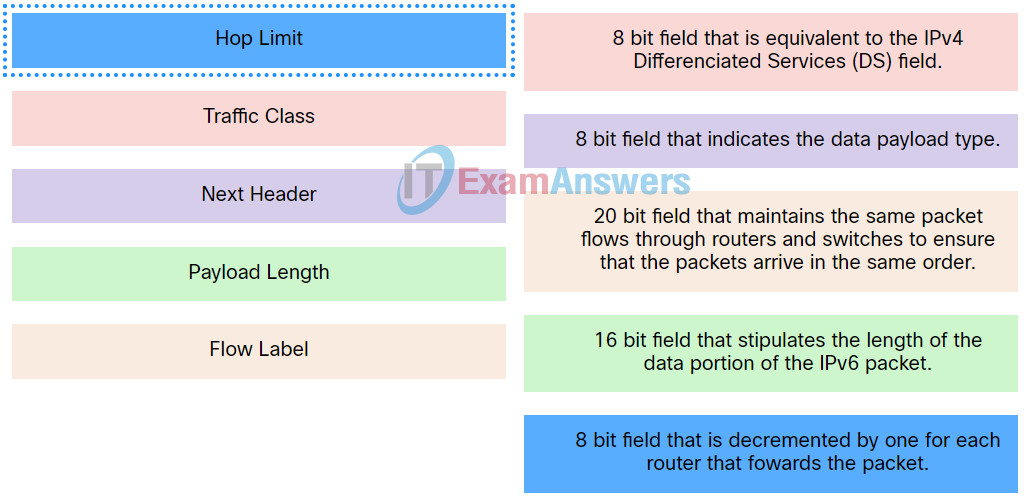
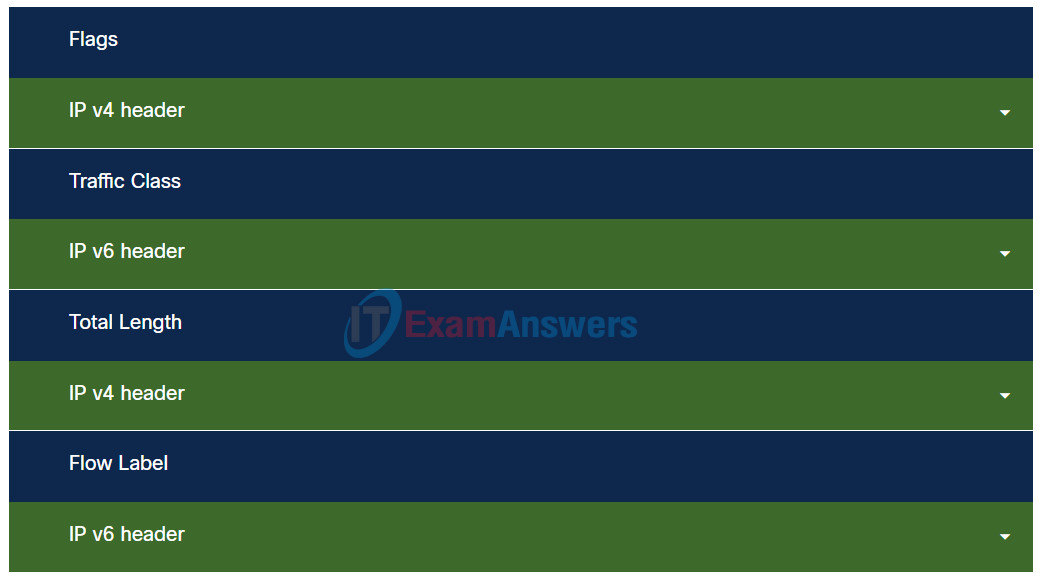
10. Match the IPv6 packet header field with the description.
11. Which three IPv4 header fields have no equivalent in an IPv6 header? (Choose three.)
- protocol
- fragment offset
- TTL
- version
- identification
- flag
12. Refer to the exhibit. A ping to PC2 is issued from PC0, PC1, and PC3 in this exact order. Which MAC addresses will be contained in the S1 MAC address table that is associated with the Fa0/1 port?
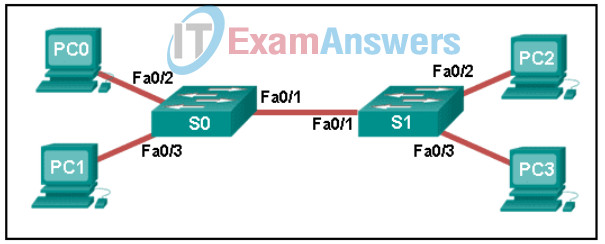
Networking Devices and Initial Configuration Course Final Exam 12
- just the PC1 MAC address
- just PC0 and PC1 MAC addresses
- just the PC0 MAC address
- PC0, PC1, and PC2 MAC addresses
- just the PC2 MAC address
13. Match field names to the IP header where they would be found.
14. What is the dotted decimal representation of the IPv4 address
11001011.00000000.01110001.11010011?
- 203.0.113.211
- 209.165.201.223
- 198.51.100.201
- 192.0.2.199
15. Which two items are used by a host device when performing an ANDing operation to determine if a destination address is on the same local network? (Choose two.)
- network number
- destination IP address
- source MAC address
- destination MAC address
- subnet mask
16. A home network has both wired and wireless connectivity. From a laptop computer, the user issues a ping to the wireless printer located in another room. The first two echo requests fail, but the last two succeed. Additional pings are all successful. Why do the first two echo requests fail?
- The computer and the printer must join the wireless network first and that process takes time.
- The distance between the computer and the printer causes delay on the first two pings.
- The wireless printer must be activated and that takes time.
- The computer must use ARP to obtain the MAC address of the printer and this process takes time.
17. Which statement is true regarding the UDP client process during a session with a server?
- A session must be established before datagrams can be exchanged.
- Datagrams that arrive in a different order than that in which they were sent are not placed in order.
- Application servers have to use port numbers above 1024 in order to be UDP capable.
- A three-way handshake takes place before the transmission of data begins.
18. Match each DHCP message type with its description.
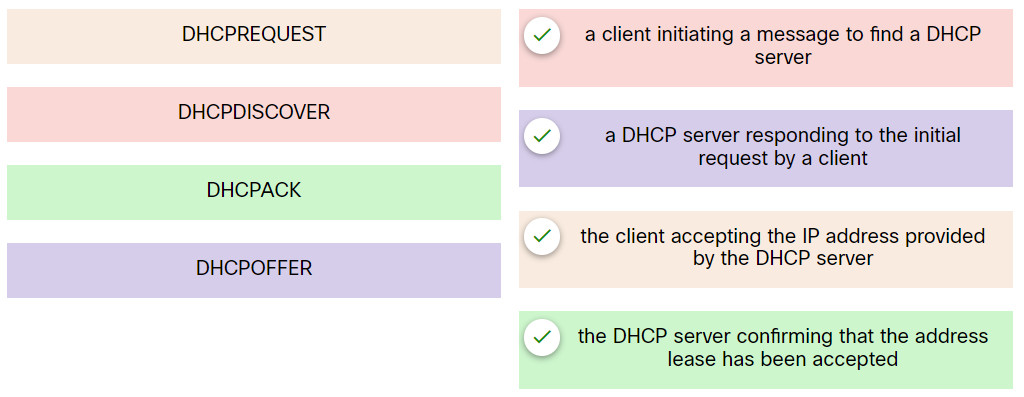
Networking Devices and Initial Configuration Course Final Exam 18
19. Refer to the exhibit. Which protocol was responsible for building the table that is shown?
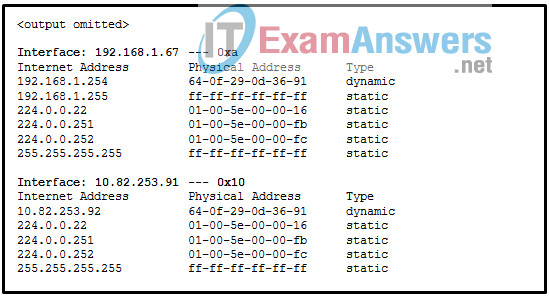
- ARP
- DHCP
- ICMP
- DNS
20. Refer to the exhibit. A web designer calls to report that the web server web-s1.cisco.com is not reachable through a web browser. The technician uses command line utilities to verify the problem and to begin the troubleshooting process. Which two things can be determined about the problem? (Choose two.)
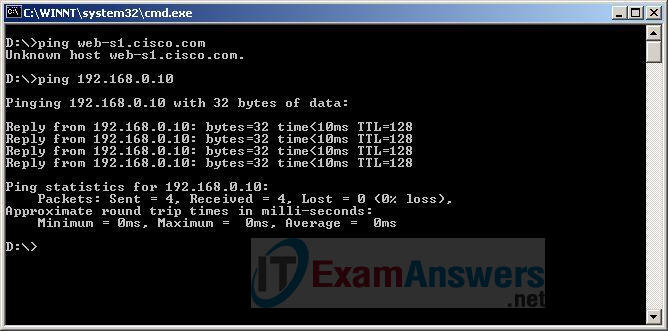
- A router is down between the source host and the server web-s1.cisco.com.
- The web server at 192.168.0.10 is reachable from the source host.
- The default gateway between the source host and the server at 192.168.0.10 is down.
- DNS cannot resolve the IP address for the server web-s1.cisco.com.
- There is a problem with the web server software on web-s1.cisco.com.
21. What are two potential network problems that can result from ARP operation? (Choose two.)
- Multiple ARP replies result in the switch MAC address table containing entries that match the MAC addresses of hosts that are connected to the relevant switch port.
- Network attackers could manipulate MAC address and IP address mappings in ARP messages with the intent of intercepting network traffic.
- On large networks with low bandwidth, multiple ARP broadcasts could cause data communication delays.
- Manually configuring static ARP associations could facilitate ARP poisoning or MAC address spoofing.
- Large numbers of ARP request broadcasts could cause the host MAC address table to overflow and prevent the host from communicating on the network.
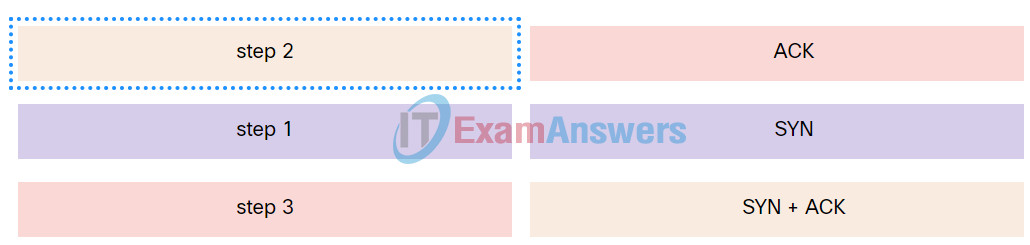
22. Match the TCP flag to the correct step in the session establishment sequence.
23. What is the difference between the terms keyword and argument in the IOS command structure?
- A keyword is entered with a predefined length. An argument can be any length.
- A keyword always appears directly after a command. An argument does not.
- A keyword is required to complete a command. An argument is not.
- A keyword is a specific parameter. An argument is not a predefined variable.
24. Which three commands are used to set up secure access to a router through a connection to the console interface? (Choose three.)
- line vty 0 4
- password cisco
- interface fastethernet 0/0
- line console 0
- enable secret cisco
- login
25. What three configuration steps must be performed to implement SSH access to a router? (Choose three.)
- a unique hostname
- a password on the console line
- an IP domain name
- a user account
- an enable mode password
- an encrypted password
26. Refer to the exhibit. What is the maximum TTL value that is used to reach the destination www.cisco.com?
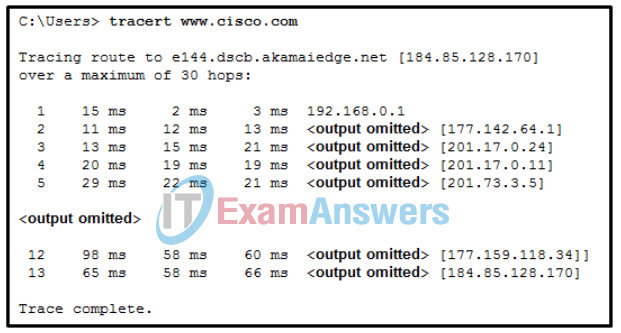
Networking Devices and Initial Configuration Course Final Exam 26
- 12
- 13
- 11
- 14
27. Which protocol is used by IPv4 and IPv6 to provide error messaging?
- NDP
- ARP
- ICMP
- DHCP
28. The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch can be remotely managed from a host on another network.
- The switch will have a management interface with the address 172.16.100.1.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
29. Match the router prompt to the configuration task.
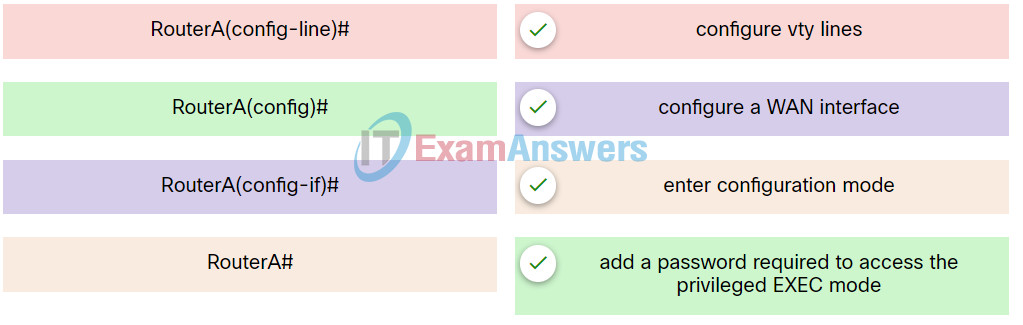
Networking Devices and Initial Configuration Course Final Exam 29
30. While troubleshooting a network problem, a network administrator issues the show version command on a router. What information can be found by using this command?
- the amount of NVRAM, DRAM, and flash memory installed on the router
- the bandwidth, encapsulation, and I/O statistics on the interfaces
- differences between the backup configuration and the current running configuration
- the version of the routing protocol that is running on the router
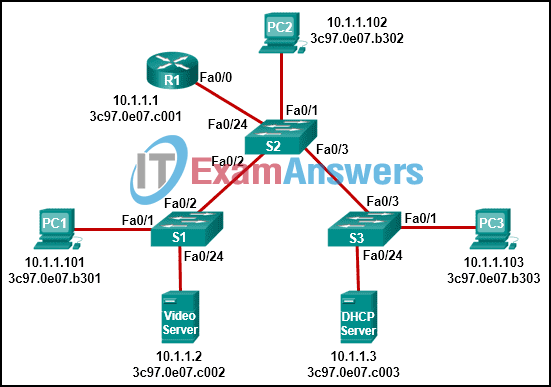
31. Refer to the exhibit. PC1 sends a frame with the destination MAC address 3c97.0e07.a1b2. Switch S1 looks up the destination MAC address in its CAM table but the address is not there. What will the switch do?
- It willl add the destination MAC address to the CAM table.
- It will forward the frame out all ports except Fa0/1.
- It will send a destination unreachable message back to PC1.
- The switch will drop the frame.
- It will forward the frame out port Fa0/2 towards the router.
32. Which forwarding action does a switch take when the destination MAC address of an Ethernet frame is an unknown unicast?
- The switch forwards the frame to the default gateway.
- The switch forwards the frame the same way it does for broadcast and multicast MAC addresses.
- The switch drops the frame.
- The switch forwards the frame out a specified port for this type of address.
33. Refer to the exhibit. An administrator is troubleshooting connectivity on the office network. PC1 is able to send print jobs to Printer1, but is unable to access File Server1. Which action would correct the problem?
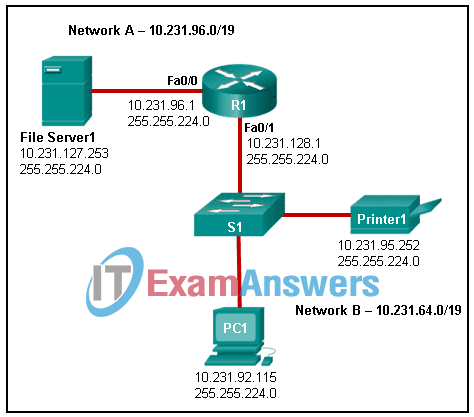
- Change the R1 Fa0/1 interface IP address to 10.231.64.1.
- Change the R1 Fa0/0 interface subnet mask to 255.255.0.0.
- Change the File Server1 IP address to 10.231.96.253.
- Change the PC1 IP address to 10.231.64.115.
34. Match the characteristic to the protocol category.

35. The ARP table in a switch maps which two types of address together?
- Layer 3 address to a Layer 4 address
- Layer 4 address to a Layer 2 address
- Layer 2 address to a Layer 4 address
- Layer 3 address to a Layer 2 address
36. A network administrator issues the Switch# show running-config command on a Cisco switch. Which term is used to describe the part “running-config” in the command?
- command
- argument
- hot key
- keyword
37. The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch can be remotely managed from a host on another network.
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch will have a management interface with the address 172.16.100.1.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
38. What is the purpose of the MAC address which is added to an e-mail message that is sent from a teacher to a student?
- It identifies the network to which the sending computer belongs.
- It identifies the computer on the Internet.
- It identifies the TCP/IP network application to which the reply can be sent.
- It identifies the computer on the LAN.
39. What is the purpose of assigning an IP address to the VLAN1 interface on a Cisco Layer 2 switch?
- to enable remote access to the switch to manage it
- to permit IP packets to be forwarded by the switch
- to create a new IP local network on the switch
- to enable the switch to route packets between networks
40. Which command should be used to test connectivity to the loopback interface?
- ping 255.255.255.255
- ping 0.0.0.0
- ping 127.0.0.1
- ping loopback
