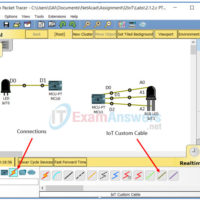
5.1.2.6 Packet Tracer – Configure Wireless Security Answers Objectives •Create a home network with a secure wireless router Introduction In this activity, you will configure a wireless router to: Modify the default password. Modify the default SSID and do not broadcast Use WPA2 Personal as security method. Rely …
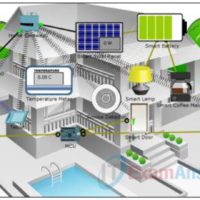
4.1.1.6 Packet Tracer – Explore the Smart Home Answers Topology Objectives Explore the Smart Home Analyze The Usage of Fog Computing in the Smart Home Background / Scenario In this activity, you will explore the smart home example. Depending on the application, some data is best processed close …
2.1.2.3 Lab – Blinking an LED Using Blockly Objectives Answers Part 1: Open Packet Tracer and Examine Blockly Program for LED Blinking Part 2: Control a RGB LED using Blockly Background Blockly is a visual programming language that lets users create programs by connecting blocks, that represent different …
1.2.2.3 Packet Tracer – Connect and Monitor IoT Devices Answers The Smart Home Network Objectives Part 1: Add Home Gateway to the Network Part 2: Connect IoT Devices to the Wireless Network Part 3: Add End User Device to the Network Background / Scenario In this activity you …
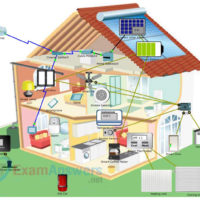
1.2.2.1 Packet Tracer – Adding IoT Devices to a Smart Home Answers The Smart Home Network Objectives Part 1: Explore the Existing Smart Home Network Part 2: Add Wired IoT Devices to the Smart Home Network Part 3: Add Wireless IoT Devices to the Smart Home Network Background …
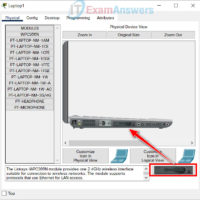
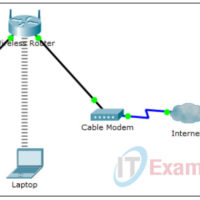
1.1.2.5 Packet Tracer – Create a Simple Network Using Packet Tracer Answers Topology Addressing Table Device Interface IP Address Subnet Mask Default Gateway PC Ethernet0 DHCP 192.168.0.1 Wireless Router WRT300N LAN 192.168.0.1 255.255.255.0 Internet DHCP Cisco.com Server Ethernet0 208.67.220.220 255.255.255.0 Laptop Wireless0 DHCP Objectives Part 1: Build a …
1. What are two roles of the transport layer in data communication on a network? (Choose two.) tracking the individual communication between applications on the source and destination hosts performing a cyclic redundancy check on the frame for errors identifying the proper application for each communication stream providing …
1. A host is transmitting a broadcast. Which host or hosts will receive it? the closest neighbor on the same network all hosts on the Internet all hosts in the same network a specially defined group of hosts 2. Which statement describes a characteristic of cloud computing? A …
1. What is indicated by a successful ping to the ::1 IPv6 address? All hosts on the local link are available. The link-local address is correctly configured. The default gateway address is correctly configured. IP is properly installed on the host. The host is cabled properly. 2. A …
1. Which two characteristics describe Ethernet technology? (Choose two.) It typically uses an average of 16 Mb/s for data transfer rates. It uses a ring topology. It uses the CSMA/CD access control method. It is supported by IEEE 802.3 standards. It is supported by IEEE 802.5 standards. 2. …