25.0 Introduction 25.0.1 Why Should I Take this Module? What types of data are necessary to perform security monitoring? What type of logging will be needed in order to capture the data that is necessary for security monitoring? What type of information is included in the various log …
24.0 Introduction 24.0.1 Why Should I Take this Module? Good protocols can have bad uses. Sometimes the protocols that we use daily can be turned against us. There are many different protocols that are used in the day-to-day operations of a network. This module will explain how these …
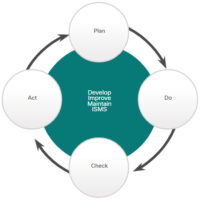
23.0 Introduction 23.0.1 Why Should I Take this Module? How much money should an organization spend on network security and cyberoperations? How does an organization know how much effort and resources to put into keeping the network and data safe? These questions can be answered through the assessment …
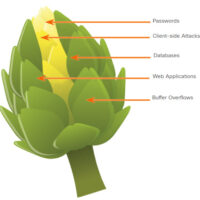
22.0 Introduction 22.0.1 Why Should I Take this Module? Endpoints are any device that communicates with any other device on a network. This includes the thousands of PCs, printers, servers, and other devices that are found in a large network. Each endpoint is vulnerable to attack. How can …
21.0 Introduction 21.0.1 Why Should I Take this module? What do you know about cryptography? What is it and how can it be implemented? In order to secure data as it travels across links, you need to have an understanding of how to protect that data and maintain …
20.0 Introduction 20.0.1 Why Should I Take this Module? It is important for you to keep up with the latest information when it comes to cybersecurity. How do you do that? Read this module to learn about information sources and threat intelligence services. 20.0.2 What Will I Learn …
19.0 Introduction 19.0.1 Why Should I Take this Module? How can you restrict access within your network? Will you allow all employees access to everything? Or will it be designed to allow users access based on their role in the company? How can you track what the user …
18.0 Introduction 18.0.1 Why Should I Take this Module? Protecting our networks will continue to be a challenge. Millions of new devices are joining our networks every year as the Internet of Things (IoT) continues to expand and individuals need to connect their own devices to the network. …
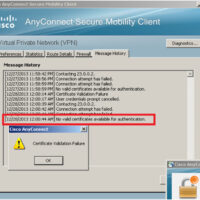
17.0 Introduction 17.0.1 Why Should I Take this Module? The foundations of the network must be secured, but that is not enough to fully protect your network. The protocols that are used to conduct the day-to-day business of the organization must be protected as well. In addition, protocols …
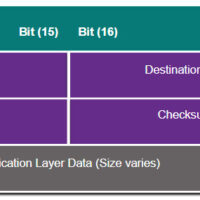
16.0 Introduction 16.0.1 Why Should I Take this Module? Protocols are the foundation of data communications. For this reason they have been a target of threat actors for a very long time. Cybersecurity analysts must understand how threat actors use features of common protocols in cyberattacks. This module …